Posts
2536Following
640Followers
1435buherator
buheratorhttps://github.com/google/security-research/security/advisories/GHSA-qx2m-rcpc-v43v
buherator
buheratorAchievement unlocked: featured in exploits.club newsletter \o/
https://blog.exploits.club/exploits-club-weekly-newsletter-72-windows-on-windows-coreaudio-fuzzing-virtualbox-escapes-and-more/
Trend Zero Day Initiative
thezdi@infosec.exchangeWrapping up Day Two of #Pwn2Own Berlin 2025. We’ve awarded $695,000 for 20 unique 0-days, with one more day to go!
Jan Wildeboer 😷
jwildeboer@social.wildeboer.net
Dear #Letsencrypt, you helped secure millions and millions of servers, not just web servers. But your announcement at https://letsencrypt.org/2025/05/14/ending-tls-client-authentication/ about ending Ending TLS Client Authentication Certificate Support in 2026 because Google changes their requirements would result in your certificates being unusable for SMTP servers. You are literally risking an email collapse for many mailserver owners just to please Google? Please think again. Please.
Hanno Zulla
hzulla@infosec.exchangeThe cool thing about software development is that the computer is doing exactly what you tell it to do.
The cool thing about debugging is slowly learning what you actually told the computer to do.
Trend Zero Day Initiative
thezdi@infosec.exchangeConfirmed!! Dinh Ho Anh Khoa of Viettel Cyber Security combined an auth bypass and an insecure deserialization bug to exploit #Microsoft SharePoint. He earns $100,000 and 10 Master of Pwn points. #Pwn2Own #P2OBerlin
Peter Schaar
PWS_1@mastodon.social#Microsoft has blocked its services to the International Criminal Court by order of Donald #Trump. The #ICC prosecutor doesn’t have access to his #email. Source:AP
https://apnews.com/article/icc-trump-sanctions-karim-khan-court-a4b4c02751ab84c09718b1b95cbd5db3
Virus Bulletin
VirusBulletin@infosec.exchangeG DATA's Karsten Hahn details how software downloads for the printer company Procolored were infected with XRed backdoor for half a year. https://www.gdatasoftware.com/blog/2025/05/38200-printer-infected-software-downloads
Dr. Christopher Kunz
christopherkunz@chaos.socialCISA is changing the way they publizice alerts, including the KEV (known exploited vulnerabilities). These will no longer be shown on the "Alerts" overview, but must be subscribed to via GovAlert (or just scrape the JSON...).
The first vulnerability that is *not* being published as an alert is...drumroll... CVE-2025-47729. "The TeleMessage archiving backend through 2025-05-05 holds cleartext copies of messages from TM SGNL app users"
Isn't that a funny coincidence?
Jan Wildeboer 😷
jwildeboer@social.wildeboer.net
I am totally sure (sarcasm included) that #Google has totally overseen that their planned changes to their root program requirements will cause a lot of problems for mailserver owners like me who in future might run into weird problems with #Letsencrypt certificates for SMTP. I am sure that Google is absolutely not trying to make running your own mailserver even more complicated just to protect their gmail business. That would be totally not how Google thinks, amirite? https://letsencrypt.org/2025/05/14/ending-tls-client-authentication/
daniel:// stenberg://
bagder@mastodon.socialDetecting malicious Unicode in #curl
https://daniel.haxx.se/blog/2025/05/16/detecting-malicious-unicode/
Sam Stepanyan  🐘
🐘
securestep9@infosec.exchange
CISA Warns of #Google Chromium #ZeroDay Vulnerability CVE-2025-4664 Actively Exploited in the Wild affecting #Chrome, MS #Edge and Opera – Make sure to update your browser to the latest version today!
👇
https://cybersecuritynews.com/cisa-warns-of-google-chromium-vulnerability-actively-exploited-in-the-wild/
那个饺子🦆(JJ)
thatjiaozi@bird.makeupI wanted to end last year with a vm escape, took me a bit longer but I want to present you my latest public research:
A VM escape in Oracle VirtualBox using only one integer overflow bug!
This was fixed in April 15 and assigned CVE-2025-30712.
https://github.com/google/security-research/security/advisories/GHSA-qx2m-rcpc-v43v
Trend Zero Day Initiative
thezdi@infosec.exchangeA brief summary of Day One of #Pwn2Own Berlin 2025, featuring Sina Kheirkhah, STAR Labs SG, Wongi Lee of Theori, Marcin Wiązowski and more. #P2OBerlin
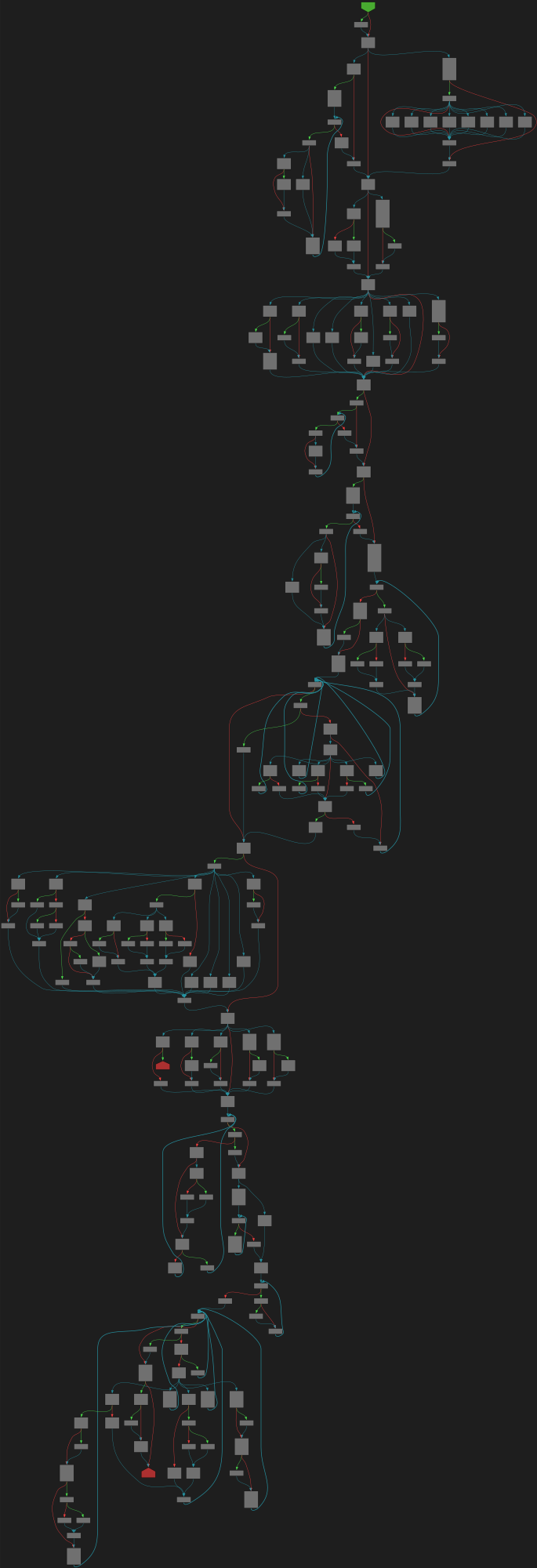
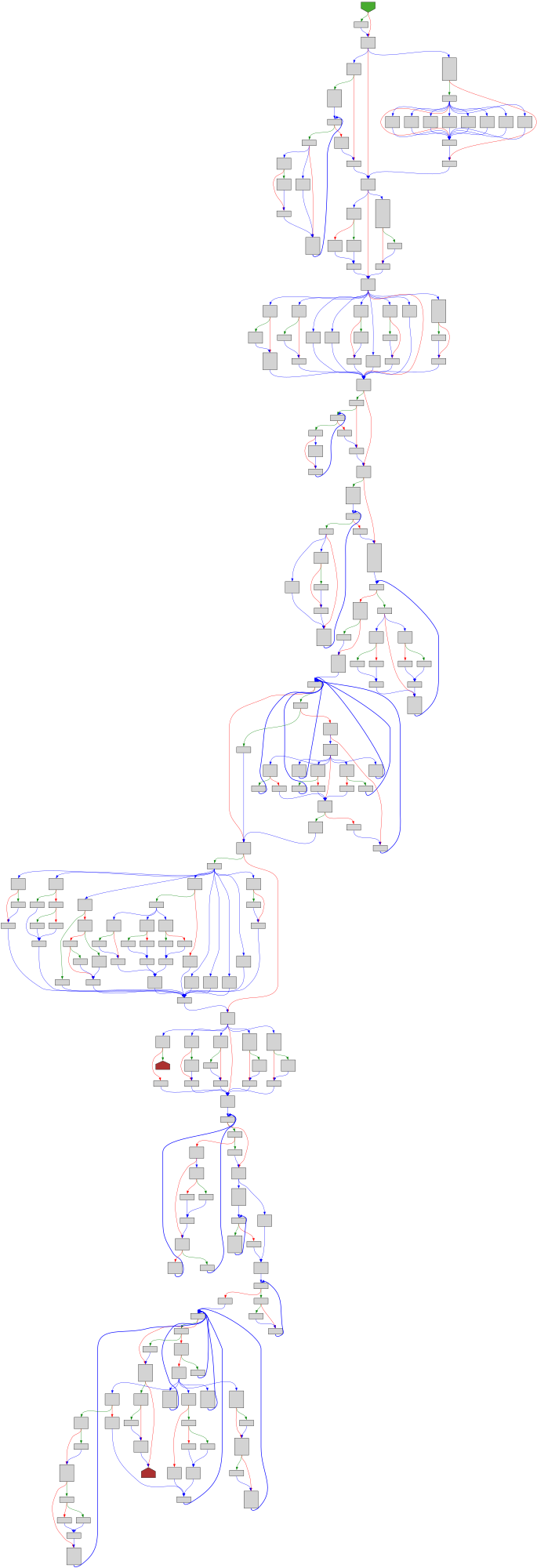
CFG Bot 🤖
cfgbot@mastodon.socialProject: golang/go https://github.com/golang/go
File: src/cmd/vendor/golang.org/x/arch/x86/x86asm/gnu.go:14 https://github.com/golang/go/blob/refs/tags/go1.23.4/src/cmd/vendor/golang.org/x/arch/x86/x86asm/gnu.go#L14
func GNUSyntax(inst Inst, pc uint64, symname SymLookup) string
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgolang.org%2Fx%2Farch%2Fx86%2Fx86asm%2Fgnu.go%23L14&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgolang.org%2Fx%2Farch%2Fx86%2Fx86asm%2Fgnu.go%23L14&colors=light
yossarian (1.3.6.1.4.1.55738)
yossarian@infosec.exchangethis ratelimiting stuff with GitHub makes me really think that MSFT might actually successfully kill their golden goose
trust arrives on foot and leaves on horseback, etc
Trend Zero Day Initiative
thezdi@infosec.exchangeConfirmed! Hyeonjin Choi of Out Of Bounds earns $15,000 for a third round win and 3 Master of Pwn Points by successfully using a type confusion bug to escalate privileges in #Windows11 #Pwn2Own #P2OBerlin
Aral Balkan
aral@mastodon.ar.alThose annoying “consent” cookie pop ups that Big Tech has been using as part of their malicious compliance efforts to convince you that data protection law in the EU is a nuisance?
Turns out they’re illegal.
#TCF #consent #data #privacy #EU #GDPR #BigTech #maliciousCompliance #SiliconValley #adtech #technoFascism
chITchat by pamoutaf
chITchat@infosec.exchangeNew podcast is now live! This podcast episode goes over the career of pinkflawd, how she got into malware reversing, advice on being in the industry, how to deal with failures, and some exciting content about some interesting piece of malware she has analyzed !
https://www.buzzsprout.com/2400544/episodes/17145918-pinkflawd-malware-reverse-engineering
https://open.spotify.com/episode/4ln1X3zd6LqM3sm6rTI527?si=eT-ERmW1Q-GN7fLaoniMSg
Thank you so much to @pinkflawd for coming on and talking about her story. Hope you enjoy 🤩