Posts
4090Following
732Followers
1618Allele Security Intelligence
alleleintel@infosec.exchangeWe started analyzing a classic case where GDB creates the illusion that code in writable memory is corrupted. We ended up discovering two interesting behaviors.
Did you know there's a way to hit a breakpoint without using hardware or software breakpoints? Or how GDB patches the binary to execute an instruction?
Learn more about how GDB works under the hood.
Why is my shellcode being corrupted?
https://allelesecurity.com/why-is-my-shellcode-being-corrupted/
@cynicalsecurity Can't wait to see if LLMs bug hunting is deep or shallow. Really curious. Also interesting how they all turned into bug hunting as their main target and AGI etc talk is long gone already LOL Guess bugs make better PR, financial returns, time will tell :-)
buherator
buheratorhttps://deadeclipse666.blogspot.com/2026/06/greatxml-bitlocker-that-seems-to-only.html
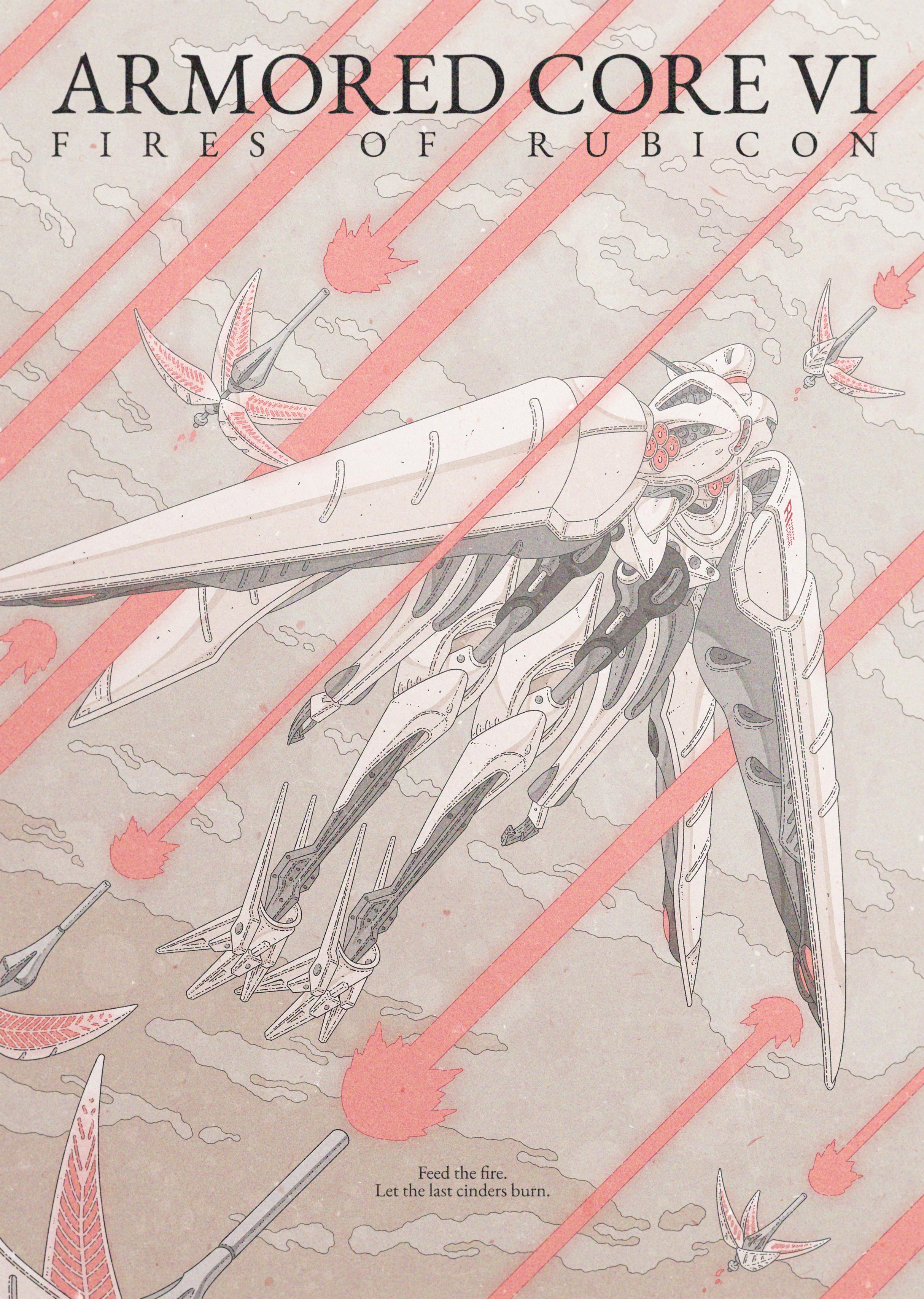
Lur Noise・ルル
lurnoise@gamedev.lgbt"Feed the fire, let the last cinders burn."
My IB-01: CEL 240 illustration is now available as a print <3
buherator
buheratorbedroom::Plumbus and bathroom::Plumbus are probably fine.
But when I have bedroom::PlumbusInserter and bathroom::PlumbusInserter it's *guaranteed* that my IDE will import the wrong name resulting in hours of debugging because nothing makes sense.
#programming
Christine Lemmer-Webber
cwebber@social.coopSomeone's AI agent has been performing a wide variety of manipulation to the project for a while to the Fedora project. https://lwn.net/SubscriberLink/1077035/c7e7c14fbd60fae9/
It's clearly linked to an account that precedes the, ahem, "agentic AI era", but it also seems the account wwas probably compromised, but everything is unclear, including motivations or the extent of damage.
Alistair Davidson
moh_kohn@mastodon.scotBlogged about the time I doubled our users by doing proper engineering instead of React slop
buherator
buheratorDr. Christopher Kunz
christopherkunz@chaos.social@buherator I can verify that the exploit still works with that mpengine.dll version and the 1.453.28.0 definition update that got released 6/10/2026 6:29:20 PM. It takes more than one attempt, sometimes up to 6-7 now, where it used to be almost always one shot, but it still works.
I'm waiting for my other VM to fully update and then I'll retry there, too.
buherator
buheratorZack Whittaker
zackwhittaker@mastodon.socialNew, by me: ServiceNow appears to have notified some enterprise customers that there was outside access to their data, after a security bug left instances exposed to the web.
The company has hidden its notice behind a login wall, but was shared by network defenders on Reddit.
dragosr
dragosr@chaos.socialThe Anthropic Fable-5 safety classifiers seem to be written by the OpenAI marketing department.
Pretty much anything I talk to LLMs about gets downgraded.
Nerfed into useless. Worst model release ever?
DEY!
dey@mastodon.socialGolden rule of vulnerability disclosure is:
Dont fuck with people who are time rich and cash poor.