Posts
4015Following
731Followers
1614OffensiveCon
offensivecon@mastodon.socialOffensivecon's talks are now available on our YouTube channel!
🔗 https://youtube.com/playlist?list=PLYvhPWR_XYJkIP2X-uGDsAMIKnhdSauaM
Phrack
phrack@haunted.computerSubmissions are still open!
If you've been sitting on a bug, technique, war story, weird research rabbit hole, or beautifully cursed idea: now is the time.
Write something worth archiving.
Phrack CFP closes June 30.
More details on how to submit at https://phrack.org/news
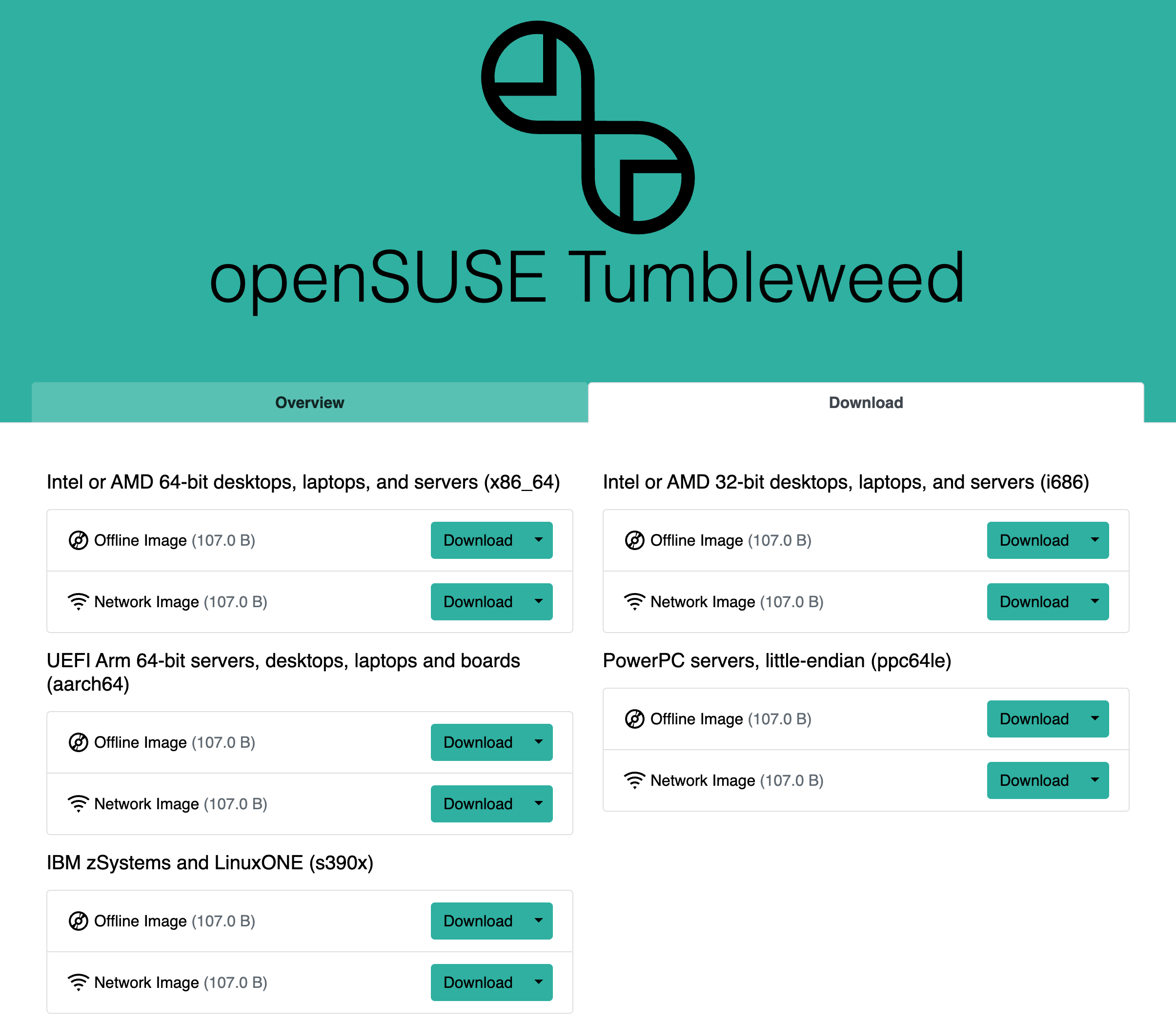
Will Dormann
wdormann@infosec.exchangeThe openSUSE peeps have figured out some crazy compression, it seems. 107.0 B for everything!
buherator
buheratorYou can write this and the compiler will just figure out all the generics for you:
`let baz = Foo::new(Bar::new());`
But if you want to write:
`return Foo::new(Bar::new());`
... it seems you have to make your function generic, even though the compiler knows exactly what will be returned.
buherator
buheratorMax Inden
mxinden@mastodon.social📅 Next Web Talks at Mozilla Berlin Meetup is happening Thu, June 11, 18:00 🦊
Two talks:
• Sunil Mayya on "Keep Off My LAN": Firefox's implementation of Local Network Access
• @freddy on "The Devil is in the Defaults": defending against XSS with Trusted Types and the Sanitizer API
https://www.meetup.com/de-DE/berlin-mozilla-meetup/events/314623241/
Markus Vervier 👾
marver@mastodon.socialRE: https://infosec.exchange/@x41sec/116651028731076045
Important! Using a reverse proxy might not fully protect you from BadHost / CVE-2026-48710 **also this does not only affect AI related infrastructure because FastAPI is also affected and used for various applications!**
daniel:// stenberg://
bagder@mastodon.socialPasting a huge AI generated explanation to a problem in an issue or pull-request is nothing but RUDE. Don't do it. You look stupid and the receivers of that feel insulted.
We are humans. We communicate like humans. Fine, use the tools you like, but don't insult us.
buherator
buheratorhttps://www.ibm.com/support/pages/node/7274214?myns=swgother&mynp=OCSSRQKY&mynp=OCSWG60&mync=A&cm_sp=swgother-_-OCSSRQKY-OCSWG60-_-A
13reak 
13reak@infosec.exchange
https://www.youtube.com/watch?v=xyup-362r1w
Respect, at that age such a great #punkrock song and then such current lyrics!
Well done, guys!
buherator
buheratorI wanted to define an interface with associated types to abstract away specific implementations of a component and used trait bounds (from a 3rd party lib) to provide guarantees about the associated types.
The problem was:
- 3rd party Traits forced generics on me that I didn't even use
- These generics had other bounds I needed to fulfill, which also what more bounds, etc.
- As a bonus, these two factors produce about a gazillion missing implementation errors for the first naive implementation, so you either need a really sharp debugger eye or will end up implementing one wrong solution after the other (as I did)
The solution for now is to drop the trait bound entirely (this is legal?!) and let the compiler intervene at the call site if someone doesn't implement the right trait - I complained exactly about this behavior the other day, because implementers can't figure out the bound just by looking at my trait, but at least now the code compiles and I left comments :P
#Rust
RE: https://infosec.place/objects/2c4cdbac-06e5-43bb-b070-044be09209b3
buherator
buheratorWish me luck!
buherator
buheratorhttps://youtu.be/n1E9IZfvGMA
Do these nutjobs really believe that scientific breakthroughs scale?! That it's OK to ruin the environment + economy (+ likely society), because 9 geniuses will solve that in 1 month?
#LLM
Nicolas Grégoire
agarri.fr@bsky.brid.gyI'll give a single public on-site Burp Suite Pro training session this year, and it will be in RomHack 🇮🇹 (registration link in replies) And if you're not sure this course would fit you, just give a look at this recent feedback
GitHub Security Lab
GitHubSecurityLab@infosec.exchangeProof of Concept for GHSL-2026-140 (CVE-2026-48095) in 7-Zip <= 26.00. A crafted archive shrinks a 256 MB buffer into 1 byte, overwrites a function pointer with file content, and redirects execution. Full weaponization needs an ASLR bypass. Fixed in 26.01. Read more at https://securitylab.github.com/advisories/GHSL-2026-140_7-Zip/
buherator
buheratorhttps://github.com/trusteddomainproject/OpenDMARC/issues/183#issuecomment-4556806007
See, my 768-bit key is actually large!!1
Hex-Rays SA
HexRaysSA@infosec.exchangePlugin Contest winners used it. Binarly built award-winning Rust bindings with it. BinSync added an idalib mode for headless pipeline support...
... Now it's your turn.
We're hosting a free virtual workshop on idalib — IDA as a library. Call IDA's analysis engine directly from your own code, automate workflows without launching the GUI, and integrate IDA into any toolchain you're already running.
Free. Virtual. Hands-on.
👉 https://2dgu4h.share-eu1.hsforms.com/2D4ZYPjdCRFODEGRKtMILwQ
Phrack
phrack@haunted.computerWe're looking for a cover for the next issue of Phrack!
Retro sci-fi, terminals, dystopian systems, chrome futures, hacker manuals from an alternate timeline.
Make something timeless and strange.
Send your work or idea to arts@phrack.org
Deadline June 30th
mahaloz
mahaloz@infosec.exchangeBinary hacking is something of an art, and AI has been getting significantly better at it. But do the limitations of our foundational tools, like decompilers, limit their ability to hack? Check out my talk that is now public on the topic:
https://youtu.be/ncYo6ZqSRLw?si=UnKwyKr_WqFdkDnYhttps://youtu.be/ncYo6ZqSRLw?si=UnKwyKr_WqFdkDnY