Posts
3566Following
722Followers
1586screaminggoat
screaminggoat@infosec.exchangeIvanti security advisories: August Security Update
Today, fixes have been released for the following solutions: Ivanti Neurons for ITSM, Ivanti Avalanche and Ivanti Virtual Traffic Manager (vTM).
The concerning CVEs:
- CVE-2024-7569 (9.6 critical) An information disclosure vulnerability in Ivanti ITSM on-prem and Neurons for ITSM
- CVE-2024-7593 (9.8 critical) authentication bypass in Ivanti vTM (PUBLICLY DISCLOSED)
- "We are not aware of any customers being exploited by this vulnerability at the time of disclosure. However, a Proof of Concept is publicly available"
"We have no evidence of these vulnerabilities being exploited in the wild. These vulnerabilities do not impact any other Ivanti products or solutions."
See related Bleeping Computer reporting: Ivanti warns of critical vTM auth bypass with public exploit
screaminggoat
screaminggoat@infosec.exchangePalo Alto Networks security advisories:
- CVE-2024-5914 Cortex XSOAR: Command Injection in CommonScripts Pack (CVSSv4: 7.0 high)
- CVE-2024-5916 PAN-OS: Cleartext Exposure of External System Secrets (CVSSv4: 6.0 medium)
- CVE-2024-5915 GlobalProtect App: Local Privilege Escalation (PE) Vulnerability (CVSSv4: 5.2 medium)
- PAN-SA-2024-0007 Prisma Access Browser: Monthly Vulnerability Updates 31 Chromium CVEs from 6772-6779, 6988-6991, 6994-7001, 7003-7005, 7255-7256, 7533-7536, 7550. These CVEs are fixed in Prisma Access Browser 1.0 (supersedes Talon Browser), and all later Prisma Access Browser versions.
"Palo Alto Networks is not aware of any malicious exploitation of this issue."
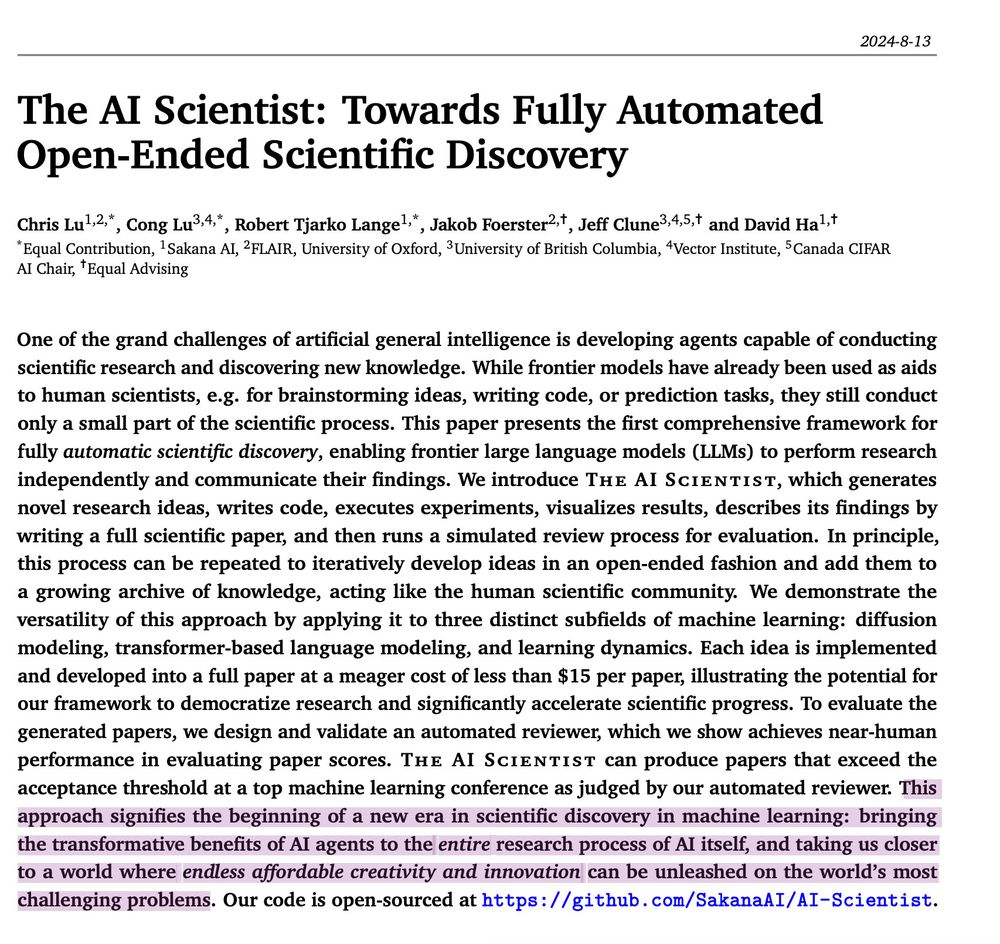
Carl T. Bergstrom
ct_bergstrom@fediscience.orgTaylorism is a management philosophy based on using scientific optimization to maximize labor productivity and economic efficiency.
Here's the result of making the false Taylorist assumption that the output of scientific research is scientific papers—the more, faster, and cheaper, the better.
Mr. Bitterness
wdormann@infosec.exchangeMe to Microsoft: You can avoid a whole class of vulnerability if non-admin users can't create subdirectories off of the root directory. You should fix this.
MS: Nah.
Me: Well, you folks should probably at least run Crassus on your code.
MS: Nah.
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38098
Mara Bos
Mara@hachyderm.ioReminder that my book—Rust Atomics and Locks—is freely available online: https://marabos.nl/atomics/ 😊
(If you read it, please leave a review on https://www.goodreads.com/book/show/63291820-rust-atomics-and-locks)
Tim Bray
timbray@cosocial.caThis is cool! https://quic.xargs.org/ [if you’re a security geek.]
Click on a few bubbles.
h/t @nelson
Thijs Alkemade
xnyhps@infosec.exchangeIn our writeup https://sector7.computest.nl/post/2024-06-cve-2024-20693-windows-cached-code-signature-manipulation/ about CVE-2024-20693, we noted that Microsoft did not structurally address the trust of "$KERNEL.*" Extended Attributes on SMB shares. Today's Patch Tuesday addresses #CVE-2024-38133, doing the same thing again, but in this case even an USB disk would work!
I think this may be the first time we got an "Exploitation More Likely", so achievement unlocked I guess?
TrendAI Zero Day Initiative
thezdi@infosec.exchangeBetter late than never, patches from #Microsoft and #Adobe are finally out - and 6 bugs are under active attack. Check out all the details, including some wormable bugs, as @TheDustinChilds breaks down the release. https://www.zerodayinitiative.com/blog/2024/8/13/the-august-2024-security-update-review
screaminggoat
screaminggoat@infosec.exchangeHappy Patch Tuesday from Microsoft: 87 vulnerabilities, 7 zero-days (6 exploited)
- CVE-2024-38189 (8.8 high) Microsoft Project Remote Code Execution Vulnerability (exploited)
- CVE-2024-38107 (7.8 high) Windows Power Dependency Coordinator Elevation of Privilege Vulnerability (exploited)
- CVE-2024-38106 (7.0 high) Windows Kernel Elevation of Privilege Vulnerability (exploited)
- CVE-2024-38213 (6.5 medium) Windows Mark of the Web Security Feature Bypass Vulnerability (exploited)
- CVE-2024-38193 (7.8 high) Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability (exploited)
- CVE-2024-38178 (7.5 high) Scripting Engine Memory Corruption Vulnerability (exploited)
- CVE-2024-38199 (9.8 critical) Windows Line Printer Daemon (LPD) Service Remote Code Execution Vulnerability (publicly disclosed)
cc: @campuscodi @briankrebs @mttaggart @deepthoughts10 @cR0w @regnil @bschwifty @arinc629 @Cali @wvu @hrbrmstr @avoidthehack @bieberium @TheDustinChilds @dreadpir8robots (make sure to remove all the mentions to avoid ReplyAll madness)
#Microsoft #zeroday #vulnerability #eitw #proofofconcept #CVE #PatchTuesday
screaminggoat
screaminggoat@infosec.exchangeFortinet security advisories for #PatchTuesday:
- FG-IR-22-445 CVE-2022-45862 (3.7 low) GUI Console WebSockets do not terminate on logout
- FG-IR-24-012 CVE-2024-36505 (5.1 medium) Real-time file system integrity checking write protection bypass
- FG-IR-22-047 CVE-2022-27486(6.7 medium) OS command injections in execute CLI commands
- FG-IR-24-255 RADIUS Protocol CVE-2024-3596 (Fortinet gives it a 6.5 medium) aka #BlastRADIUS
- FG-IR-23-467 CVE-2024-21757 (6.1 medium) Priviledged admin able to modify super-admins password
- FG-IR-23-088 CVE-2023-26211 (6.8 medium) XSS vulnerability in communications triggered in playbooks
No mention of exploitation. CVE-2024-3596 was publicly disclosed 09 July 2024.
Techmeme
Techmeme@techhub.socialPolitico, the NYT, the WaPo, and others say they received hacked Trump campaign materials, but gave few details, a marked contrast to Clinton's emails in 2016 (David Bauder/Associated Press)
https://apnews.com/article/trump-vance-leak-media-wikileaks-e30bdccbdd4abc9506735408cdc9bf7b
http://www.techmeme.com/240813/p14#a240813p14
sha1lan
sha1lan@infosec.exchangeWhy exploits prefer memory corruption
Thanks to @HalvarFlake and @chompie1337!
https://pacibsp.github.io/2024/why-exploits-prefer-memory-corruption.html
screaminggoat
screaminggoat@infosec.exchangeZoho ManageEngine security advisories:
- Authenticated SQL Injection Vulnerability (CVE-2024-5527) fixed in ADAudit Plus build 8110 CVE-2024-5527 (vendor 8.3 high) authenticated SQL Injection in file auditing configuration
- Authenticated SQL Injection Vulnerability (CVE-2024-5487) fixed in ADAudit Plus build 8110 CVE-2024-5487 (vendor 8.3 high) authenticated SQL Injection in attack surface analyzer's export option
- Authenticated SQL Injection Vulnerability (CVE-2024-36518) fixed in ADAudit Plus build 8110 CVE-2024-36518 (vendor 8.3 high) authenticated SQL Injection in attack surface analyzer's dashboard
No mention of exploitation. Mitre and NVD only have publish dates from yesterday 12 August 2024, even though the Zoho advisories marked them fixed 14 June 2024. Zoho also doesn't indicate when the advisories were published. Happy #PatchTuesday
Lukasz Olejnik
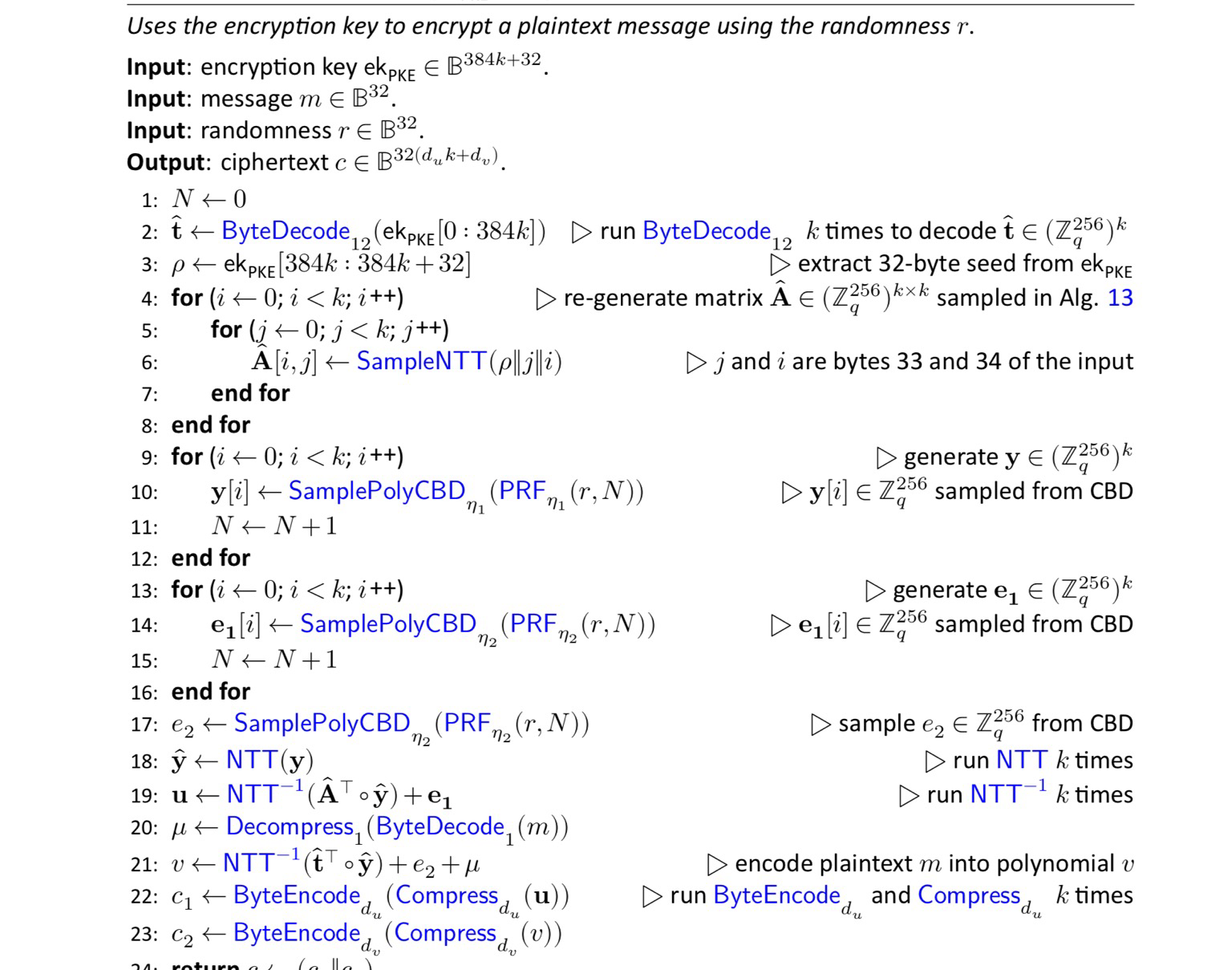
LukaszOlejnik@mastodon.social‼️Big day! NIST publishes standards for next-generation cryptography (cipher, digital signature) understood as resistant to attacks with future quantum computers. Migration will not be a piece of cake, but there’s time. https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.203.pdf https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.204.pdf https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.204.pdf
lown
lown@hachyderm.ioSeeking help from an IT security person - please share!
I run an open source, federated event sharing site, #Gathio (https://gath.io). A few days ago, it was victim to a ransomware attack that deleted the database. I need a few hours of someone's time (paid of course!) to sit with me and go through my security configuration ASAP.
Sometimes, running open source, free, community services _sucks_. 
Jann Horn
jann@infosec.exchangefun Linux fact:
There are at least two places in the Linux kernel where performance-sensitive code paths use a, uh, retrospective approach to memory safety, where you do the memory read first (and suppress the occasional kernel page fault) and worry about making sure it was memory-safe later.
One of the two is in the SLUB allocator's lockless allocation fastpath: https://elixir.bootlin.com/linux/v6.10.4/source/mm/slub.c#L544
It (1) first loads the pointer to the current top freelist element, then (2) reads the next freelist pointer out of that element, and (3) does a double-wide atomic compare-exchange to check if it raced and replace the freelist head. The read in step (2) can return garbage or fault if someone else concurrently modified the freelist (basically it can be UAF), but in that case step (3) that uses the result of the read is guaranteed to fail, so it's fine.
The other one is in the Virtual File System layer, used for printing pathnames (like for getcwd()):
https://elixir.bootlin.com/linux/v6.10.4/source/fs/d_path.c#L50
As the comment there explains:
* The source of the prepend data can be an optimistic load
* of a dentry name and length. And because we don't hold any
* locks, the length and the pointer to the name may not be
* in sync if a concurrent rename happens, and the kernel
* copy might fault as a result.
*
* The end result will correct itself when we check the
* rename sequence count, but we need to be able to handle
* the fault gracefully.
So this one can race so that OOB memory is copied into the path buffer, but the kernel will afterwards notice that the "how many rename operations have happened" counter has gone up (or that the "we are currently in the middle of a rename" bit is set), discard the result, and try again.
quarkslab
quarkslab@infosec.exchangeWireless hacking doesn't have to be a mess of dongles and ad-hoc code anymore.
Yesterday @virtualabs from Quarkslab and @rcayre from EURECOM released WHAD, a set of open source tools, libraries and firmware to make wireless security research easier.
WHAD implements 6 protocols (BLE, ZigBee, RF4CE, Unifying, ESB, LoRaWAN) and supports 11 different hardware devices, including 4 embedding our custom firmwares to extend their capabilities.
It can be used to sniff various protocols (BLE, 802.15.4, ZigBee, RF4CE, Enhanced Shockburst, Logitech Unifying and even unknown ones via its PHY support), packet injection, MITM attacks, device emulation, device sharing over TCP, and a number of other features and capabilities.
See the code repository here https://github.com/whad-team/whad-client
abadidea
0xabad1dea@infosec.exchangeif AI wants to be useful, it can read the build instructions of a github readme and tell me which seventeen packages the author forgot to mention I need to install first
Max "Buzzworthy" Eddy
maxeddy@infosec.exchangeLosing my mind at this. Google says that cellsite simulators are being used to send SMS spam.
https://security.googleblog.com/2024/08/keeping-your-android-device-safe-from.html