Posts
3895Following
728Followers
1602sha1lan
sha1lan@infosec.exchangeWhy exploits prefer memory corruption
Thanks to @HalvarFlake and @chompie1337!
https://pacibsp.github.io/2024/why-exploits-prefer-memory-corruption.html
screaminggoat
screaminggoat@infosec.exchangeZoho ManageEngine security advisories:
- Authenticated SQL Injection Vulnerability (CVE-2024-5527) fixed in ADAudit Plus build 8110 CVE-2024-5527 (vendor 8.3 high) authenticated SQL Injection in file auditing configuration
- Authenticated SQL Injection Vulnerability (CVE-2024-5487) fixed in ADAudit Plus build 8110 CVE-2024-5487 (vendor 8.3 high) authenticated SQL Injection in attack surface analyzer's export option
- Authenticated SQL Injection Vulnerability (CVE-2024-36518) fixed in ADAudit Plus build 8110 CVE-2024-36518 (vendor 8.3 high) authenticated SQL Injection in attack surface analyzer's dashboard
No mention of exploitation. Mitre and NVD only have publish dates from yesterday 12 August 2024, even though the Zoho advisories marked them fixed 14 June 2024. Zoho also doesn't indicate when the advisories were published. Happy #PatchTuesday
Lukasz Olejnik
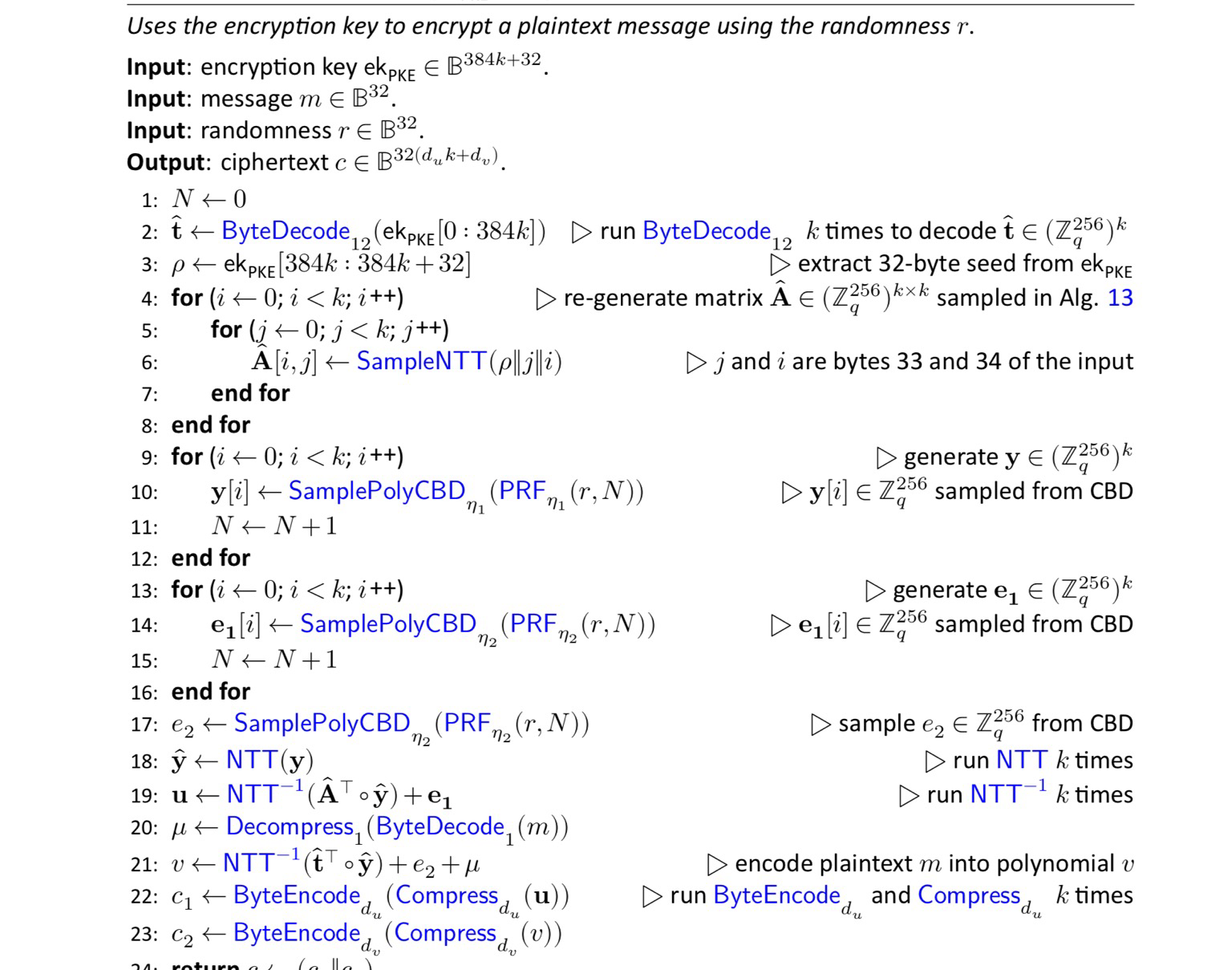
LukaszOlejnik@mastodon.social‼️Big day! NIST publishes standards for next-generation cryptography (cipher, digital signature) understood as resistant to attacks with future quantum computers. Migration will not be a piece of cake, but there’s time. https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.203.pdf https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.204.pdf https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.204.pdf
lown
lown@hachyderm.ioSeeking help from an IT security person - please share!
I run an open source, federated event sharing site, #Gathio (https://gath.io). A few days ago, it was victim to a ransomware attack that deleted the database. I need a few hours of someone's time (paid of course!) to sit with me and go through my security configuration ASAP.
Sometimes, running open source, free, community services _sucks_. 
Jann Horn
jann@infosec.exchangefun Linux fact:
There are at least two places in the Linux kernel where performance-sensitive code paths use a, uh, retrospective approach to memory safety, where you do the memory read first (and suppress the occasional kernel page fault) and worry about making sure it was memory-safe later.
One of the two is in the SLUB allocator's lockless allocation fastpath: https://elixir.bootlin.com/linux/v6.10.4/source/mm/slub.c#L544
It (1) first loads the pointer to the current top freelist element, then (2) reads the next freelist pointer out of that element, and (3) does a double-wide atomic compare-exchange to check if it raced and replace the freelist head. The read in step (2) can return garbage or fault if someone else concurrently modified the freelist (basically it can be UAF), but in that case step (3) that uses the result of the read is guaranteed to fail, so it's fine.
The other one is in the Virtual File System layer, used for printing pathnames (like for getcwd()):
https://elixir.bootlin.com/linux/v6.10.4/source/fs/d_path.c#L50
As the comment there explains:
* The source of the prepend data can be an optimistic load
* of a dentry name and length. And because we don't hold any
* locks, the length and the pointer to the name may not be
* in sync if a concurrent rename happens, and the kernel
* copy might fault as a result.
*
* The end result will correct itself when we check the
* rename sequence count, but we need to be able to handle
* the fault gracefully.
So this one can race so that OOB memory is copied into the path buffer, but the kernel will afterwards notice that the "how many rename operations have happened" counter has gone up (or that the "we are currently in the middle of a rename" bit is set), discard the result, and try again.
quarkslab
quarkslab@infosec.exchangeWireless hacking doesn't have to be a mess of dongles and ad-hoc code anymore.
Yesterday @virtualabs from Quarkslab and @rcayre from EURECOM released WHAD, a set of open source tools, libraries and firmware to make wireless security research easier.
WHAD implements 6 protocols (BLE, ZigBee, RF4CE, Unifying, ESB, LoRaWAN) and supports 11 different hardware devices, including 4 embedding our custom firmwares to extend their capabilities.
It can be used to sniff various protocols (BLE, 802.15.4, ZigBee, RF4CE, Enhanced Shockburst, Logitech Unifying and even unknown ones via its PHY support), packet injection, MITM attacks, device emulation, device sharing over TCP, and a number of other features and capabilities.
See the code repository here https://github.com/whad-team/whad-client
abadidea
0xabad1dea@infosec.exchangeif AI wants to be useful, it can read the build instructions of a github readme and tell me which seventeen packages the author forgot to mention I need to install first
Max "Buzzworthy" Eddy
maxeddy@infosec.exchangeLosing my mind at this. Google says that cellsite simulators are being used to send SMS spam.
https://security.googleblog.com/2024/08/keeping-your-android-device-safe-from.html
TrendAI Zero Day Initiative
thezdi@infosec.exchangeWe had a lot of fun handing out our first-ever #Vanguard Awards. If you couldn't be there, we've updated our blog with all the winners. Check it out at https://www.zerodayinitiative.com/blog/2024/8/1/introducing-the-vanguard-awards
Frederik Braun �
freddy@security.plumbingLooks like we shipped Firefox 129 last week, where the address bar is defaulting to use HTTPS (and falls back to HTTP if it doesn't work). Kudos to the team for shipping! 😀 It's nice to see something happen so smoothly when on vacation
Christian Blichmann🇺🇦
AdmVonSchneider@infosec.exchangeHuh, with the new IDAlib headless mode in @HexRaysSA IDA 9.0, #BinDiff can get rid of the visible second IDA instance. Need to play around with this more.
Kamil Bojarski
lawsecnet@infosec.exchangeI very much enjoyed this talk by @thegrugq While there are many issues here worth discussing like systems' perception of the world or why is it not so easy to predict how system will fail, I particularly liked discussion on impact of policy decision.
Too often I have heard arguments how certain technical solution can overcome/solve particular issues and make them "policy-proof". In reality scope of influence available to both state and private actors, makes policy way more important factor determining outcome. You can't out-obfuscate your way out of telemetry available to major tech companies or out-encrypt government level targeted surveillance.
blasty
bl4sty@bird.makeupexcited to see my janky code being put to good use for jailbreaking flagship smartphones such as the "vtech kidizoom snap touch"
David Weston (DWIZZZLE)
dwizzzlemsft@bird.makeupInteresting paper - A Verification Methodology for the Arm® Confidential Computing Architecture: From a Secure Specification to Safe Implementations https://dl.acm.org/doi/abs/10.1145/3586040
ChanceyFleet
ChanceyFleet@mas.toAs a Blind person i never thought i would be on social media savoring photos. But the communal Mastodon alt text game is so strong that sweet, poetic or silly descriptions abound on my timeline. Thanks to legions of people who take time to write a meaningful description of the ephemera they post, i learn so much about insects, plants, buildings, memes — all dispatches from a dimension of the world that i otherwise wouldn't experience. If you're wondering whether anybody reads these things: YES.
jonpalmisc
jonpalmisc@infosec.exchange🧵 Saturday reversing thread: I was going to wait until the full release, but since the beta seems to have become more-public-than-intended, let’s look at how the official “IDA as a library” works in IDA Pro 9.0…
Longhorn
never_released@mastodon.socialMaking RSA faster on Graviton2: https://www.amazon.science/blog/formal-verification-makes-rsa-faster-and-faster-to-deploy