Posts
3934Following
728Followers
1603eShard
eshard@infosec.exchangeMissing peripheral in QEMU? Adding it yourself is easier than you think.
We hit a wall analyzing CVE-2019-14192 on real Raspberry Pi 3B+ firmware, so we added the missing driver to #QEMU. Register by register, using U-Boot's own source as the spec.
Stefan Eissing
icing@chaos.socialWhen you hear people abandoning Open Source because of the AI exploit threat, ask them if we should keep our laws secret as well.
Because there is a huge industry of accountants and lawyers specialized in finding exploits in those.
No? Thought so.
Satya Nadella
satyanadella@bird.makeupOur new multi-model agentic security system brings together more than 100 specialized agents across frontier and custom models to find exploitable bugs, delivering top performance on the CyberGym benchmark.
We used it ahead of Patch Tuesday to help find and fix 16 vulnerabilities. Today we’re announcing that customers can sign up to test it in private preview.
cynicalsecurity 
cynicalsecurity@bsd.network
Will you please stop wasting time on Mythos-associated FUD and try to understand that you need to build reliable and dependable software, not stuff which changes weekly, to get security?
Mythos & LLM only bring breadth and depth to automated searching, they find nothing conceptually new, if no-one had come up with buffer overflows there would be no buffer overflows coming out of Mythos.
There will be a flood of issues, as if suddenly thousands of people were dedicated to finding bugs, then it will stop.
It is an excellent chance to ask yourselves "why?" and realise that no, we don't need software like it is being built now, you need software like it was built back when downtime mattered.
daniel:// stenberg://
bagder@mastodon.social"Packages that can't be rebuilt byte-for-byte are now blocked from entering Debian's testing branch."
https://itsfoss.com/news/debian-makes-reproducible-builds-mandatory/
Frederik Braun �
freddy@security.plumbingPoll: What is the main driver of high quality vulnerability research?
(Multiple choice. Please boost for reach :))
buherator
buheratorhttps://blog.trailofbits.com/2026/05/12/go-fuzzing-was-missing-half-the-toolkit.-we-forked-the-toolchain-to-fix-it./
buherator
buheratorhttps://www.synacktiv.com/en/publications/exploiting-the-tesla-wall-connector-from-its-charge-port-connector-part-2-bypassing.html
buherator
buheratorJán Trenčanský
j91321@infosec.exchangeBabe wake up, new Windows privesc just dropped. #GreenPlasma. Oh and also Bitlocker bypass #YellowKey https://github.com/Nightmare-Eclipse/GreenPlasma
buherator
buheratorWill Dormann
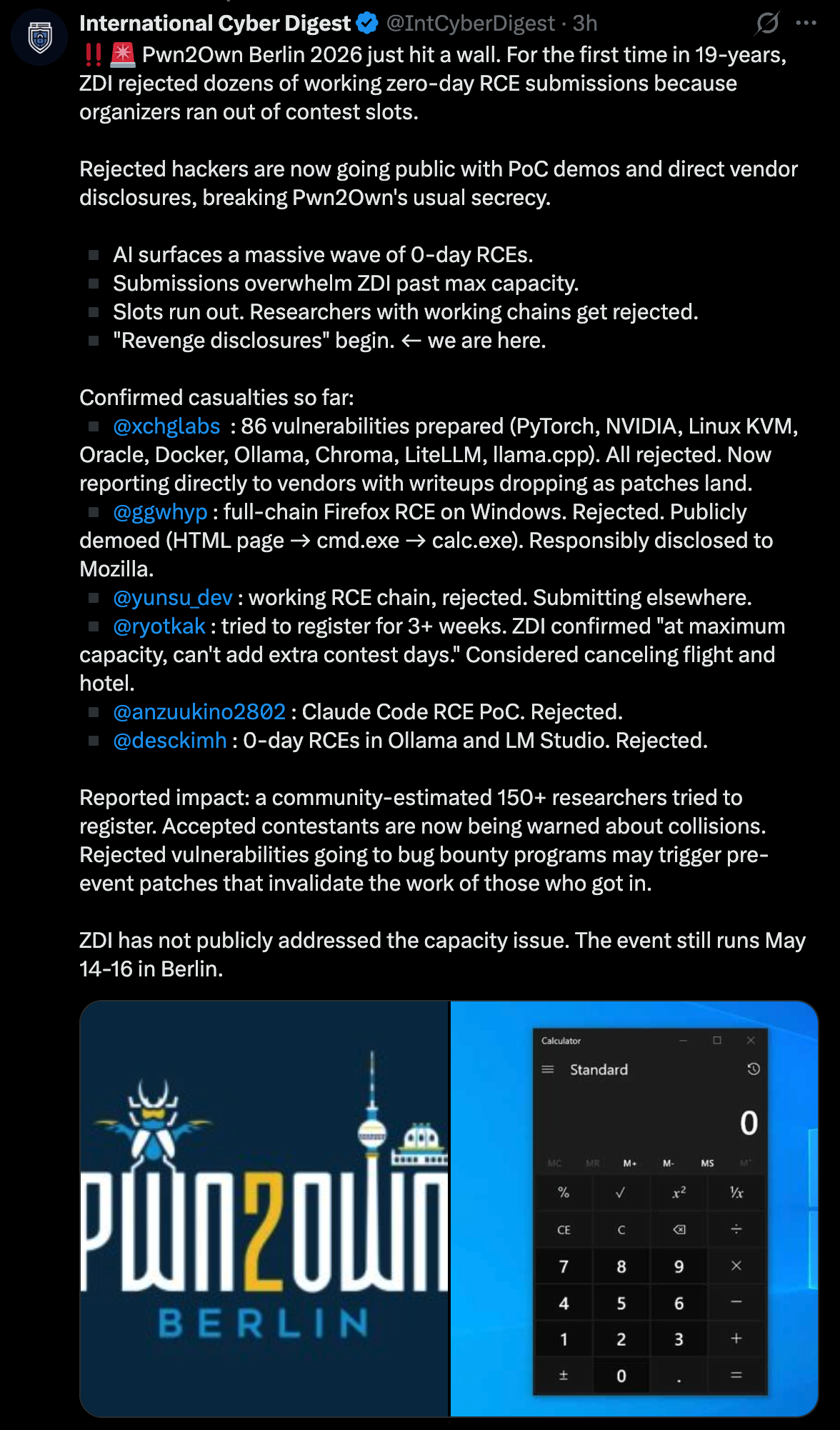
wdormann@infosec.exchangePwn2Own Berlin 2026 is rejecting working RCEs because organizers ran out of contest slots.
Visit a website in Firefox and get code execution? Rejected.
Strange days indeed.
TrendAI Zero Day Initiative
thezdi@infosec.exchangeHe says to blame the delay on jet lag, but @dustin_childs has his full review of the #Adobe and #Microsoft patches. Nothing under active attack, but a total of 190 CVEs to look at (plus 120+ from Chrome recently!) read the details at https://www.zerodayinitiative.com/blog/2026/5/12/the-may-2026-security-update-review
Ramdhan
n0psledbyte@bird.makeupHad some fun finding and exploiting state machine logic bug in af_alg_sendmsg last year, it leads to OOB access, arbitrary write then container escape that unnoticed since 2011
kernelCTF writeup: https://github.com/star-sg/security-research/blob/fa38e161bf59e285e3fbc5238a83f71bfa7dc7c7/pocs/linux/kernelctf/CVE-2025-39964_lts_cos_mitigation/docs/exploit.md
Fix commit: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit?id=1b34cbbf4f011a121ef7b2d7d6e6920a036d5285
https://bird.makeup/users/starlabs_sg/statuses/2054048693716939215
Brad Spengler
spendergrsec@bird.makeuphttps://www.amd.com/en/resources/product-security/bulletin/amd-sb-7052.html Xen advisory posted, should be a kernel fix here any minute now I assume
hackaday
hackaday@hackaday.social2026 Hackaday Europe: Pre-party, More Workshops, and Everything Else
https://hackaday.com/2026/05/12/2026-hackaday-europe-pre-party-more-workshops-and-everything-else/