Posts
3806Following
723Followers
1597jonny (good kind)
jonny@neuromatch.socialIt's so cool that anthropic is setting up a double-sided protection racket where it will profit from the massive token burn of attackers and defenders with a tool specifically designed to generate exploits and their only observable mitigation is a clientside system prompt that sternly warns the LLM to be good and not do malware
https://red.anthropic.com/2026/mythos-preview/
buherator
buheratorhttps://heyitsas.im/posts/cups/
More LLM bugs: CVE-2026-34980 and CVE-2026-34990
Tom Schuster
evilpie@hachyderm.ioTo my security peeps: Was the introduction of widespread fuzzing similar to AI-based bug hunting now, or is this really a different beast?
daniel:// stenberg://
bagder@mastodon.socialNope, no one from Anthropic Glasswing has been in touch.
buherator
buheratorhttp://blog.quarkslab.com/milking-the-last-drop-of-intego-time-for-windows-to-get-its-lpe.html
/r/netsec
_r_netsec@infosec.exchangeCVE-2026-34197: ActiveMQ RCE via Jolokia API https://horizon3.ai/intelligence/blogs/cve-2026-34197-activemq-rce-jolokia/
danzin
danzin@mastodon.socialSystematically reviewing Python C extensions (575+ bugs found so far) and offering to analyze yours!
I’ve recently analyzed 44 C extensions for correctness and free-threading readiness. I'd love to run the analysis on your extension too.
If you want the deep dive into the methodology, the false positive rates, and what I've learned, I wrote a full post here: https://discuss.python.org/t/systematically-finding-bugs-in-python-c-extensions-575-confirmed-so-far/106875
But if you just want your C extension checked, reply below or DM me!
#Python #CPython
buherator
buheratorShow content
I guess some would prefer hiding in their little bunkers with their chosen friends (and that's fine), but if we want to have an open social network it's probably the wrong strategy to design things around that concept.
buherator
buheratorShow content
Working search!
Talos Vulnerability Reports
talosvulnsLibRaw HuffTable::initval heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2330
CVE-2026-20911
Talos Vulnerability Reports
talosvulnsLibRaw lossless_jpeg_load_raw heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2331
CVE-2026-21413
Talos Vulnerability Reports
talosvulnsLibRaw x3f_thumb_loader heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2358
CVE-2026-20889
Vengeful Mouse
algernon@come-from.mad-scientist.clubA few weeks ago, someone reported an obsrvation on the iocaine bug tracker: ClaudeBot appeared to have figured out how to remove the poison ID from poisoned URLs.
That was a worrying development, so I set out to do some experiments in The Lab. I wasn't unprepared for this development, and had a few tricks lined up to address it. I wanted to test which one works.
After two and half weeks of experiments, I'm happy to report that Claude has not started to remove iocaine's poison IDs from URLs. The bot merely fails at the basic task of resolving relative URLs.
Both the built-in script and Nam-Shub of Enki generate relative URLs, and only include the poison ID if the entry URL didn't have one. Thus, whenever ClaudeBot hit a poisoned URL, it failed to resolve the poison-ID less relative URL, and constructed an URL that did not have one.
The straightforward fix for this is to not trust the crawlers to be able to resolve relative URLs.
Will Dormann
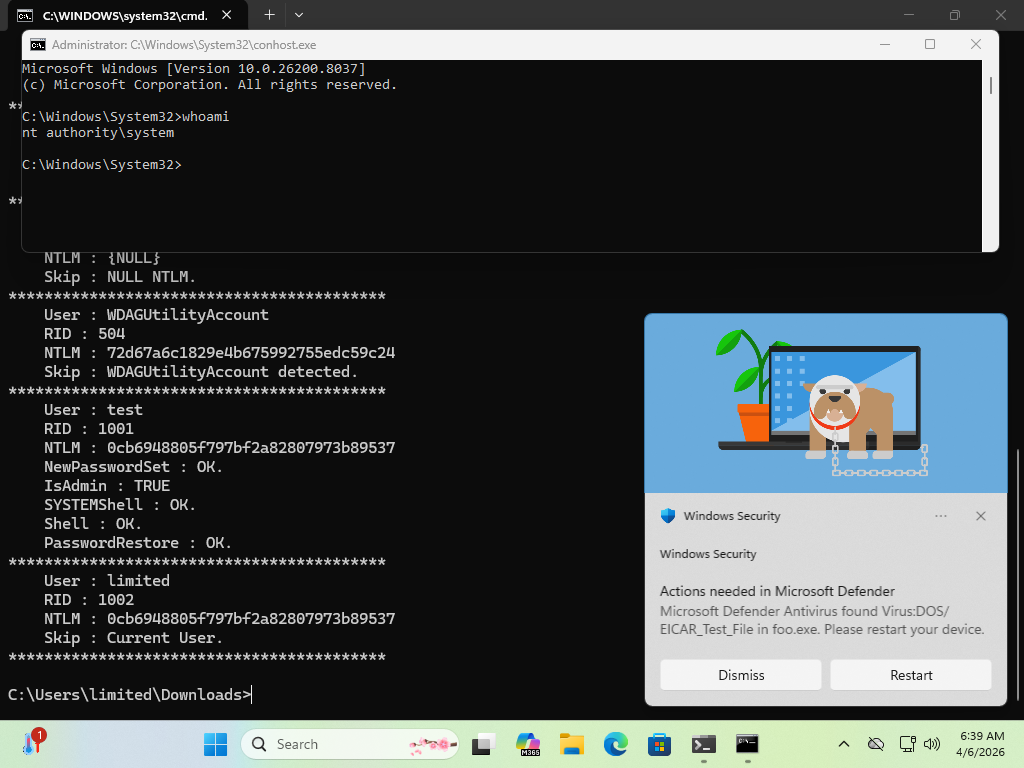
wdormann@infosec.exchangeThere's a new Windows 0day LPE that has been disclosed called BlueHammer. The reporter suggests that it's being disclosed due to how MSRC operates these days.
MSRC used to be quite excellent to work with.
But to save money Microsoft fired the skilled people, leaving flowchart followers.
I wouldn't be surprised if Microsoft closed the case after the reporter refused to submit a video of the exploit, since that's apparently an MSRC requirement now. 😂
Anyway, yeah, it works. Maybe not 100% reliably, but well enough...