Posts
3275Following
709Followers
1570Soatok Dreamseeker
soatok@furry.engineerHorrible idea:
Disclose vulns in the speech bubbles of furry porn commissions
buherator
buheratorDr. Zalka Csenge Virág
TarkabarkaHolgy@ohai.socialThey know what's in your house.
They know who your friends are.
They know what you say about people behind their back.
They know what you eat.
They know where you sleep.
They know when you're on your period.
They know when you fart.
They are not the NSA.
They are not the CIA.
They are your child's kindergarden teachers.
Daring Fireball
daringfireball@mastodon.socialTim Cook Wrote a Memo on the ‘Events in Minneapolis’
https://daringfireball.net/linked/2026/01/28/tim-cook-memo
Caitlin Condon
catc0n@infosec.exchangeThe VulnCheck research team found an unauth RCE vuln in SmarterMail that at least three other researchers discovered independently. VulnCheck canaries are also detecting in-the-wild exploitation of CVE-2026-24423. Lots of sudden attention on this software from researchers and adversaries.
https://www.vulncheck.com/blog/smartermail-connecttohub-rce-cve-2026-24423
buherator
buheratorhttps://blog.0patch.com/2026/01/micropatches-released-for-microsoft.html
Nina Kalinina
nina_kali_nina@tech.lgbtBuild systems suck, all of them. They try to solve a real problem but fundamentally the only way to win this game is not to play.
*ducks*
buherator
buheratorbuherator
buheratorbuherator
buheratorhttps://blog.synology.com/the-efforts-synology-made-in-pursuit-of-data-security
This is a more technical analysis from the attackers view:
https://drive.google.com/file/d/1MYCNVKkNETkqS-cLJsqHE43Sfm4LZbCO/view?pli=1
In short: they took significant steps forward during the past years, they probably ignored active network attacks (on LANs this may make sense, for Internet comms not so much).
buherator
buheratorbuherator
buheratorThe V Programming Language
vlang@mas.toV now has SSA, SSA => x64/arm64 backends, a linker built in V and a code signer.
As the result, a 2000 line test program is compiled in 8ms!
It's work in progress, self hosting is not possible yet. But once it is, it's going to be awesome!
buherator
buheratorRE: https://bird.makeup/users/lauriewired/statuses/2015880031227281872
Jan Schaumann
jschauma@mstdn.socialOpenSSL Security Advisory
https://openssl-library.org/news/secadv/20260127.txt
One high, one medium, and 9 low severity issues.
The high severity is a stack buffer overflow in CMS AuthEnvelopedData parsing (CVE-2025-15467): attacker provides an oversized IV, leading to buffer overflow prior to authentication, possibly leading to remote code execution if you're parsing untrusted CMS or PKCS#7 content with AEAD (e.g., AES-GCM).
buherator
buheratorhttps://www.linaro.org/blog/reproducible-linux-kernel-bisection/
Jonah Aragon
jonah@neat.computerRE: https://mastodon.thenewoil.org/@thenewoil/115971195227745876
Next up will be a VPN ban. Many tech-y people will see that and think “lol yeah well that’s not going to stop *me* from using a VPN”
A VPN ban isn’t really meant stop you from using one. It means when they catch you doing so, they’ll use the fact you’re using this harmless technology itself as a *pretense* to lock you up without needing to do any “hard work” (i.e. an investigator’s job) like actually confirming whether you committed a real crime.
Don’t think you won’t be impacted just because you know how to outsmart an ISP filter! This is not a plan to protect children or stop you from consuming adult media. It is a ploy to eventually eliminate ALL freedom of expression and free access to information in the UK.
And the same goes for Chat Control and encrypted messengers, btw
#UKpol #VPNban #PornHub #ChatControl #Privacy #FreeSpeech #SocialMedia
Gwen Fisher
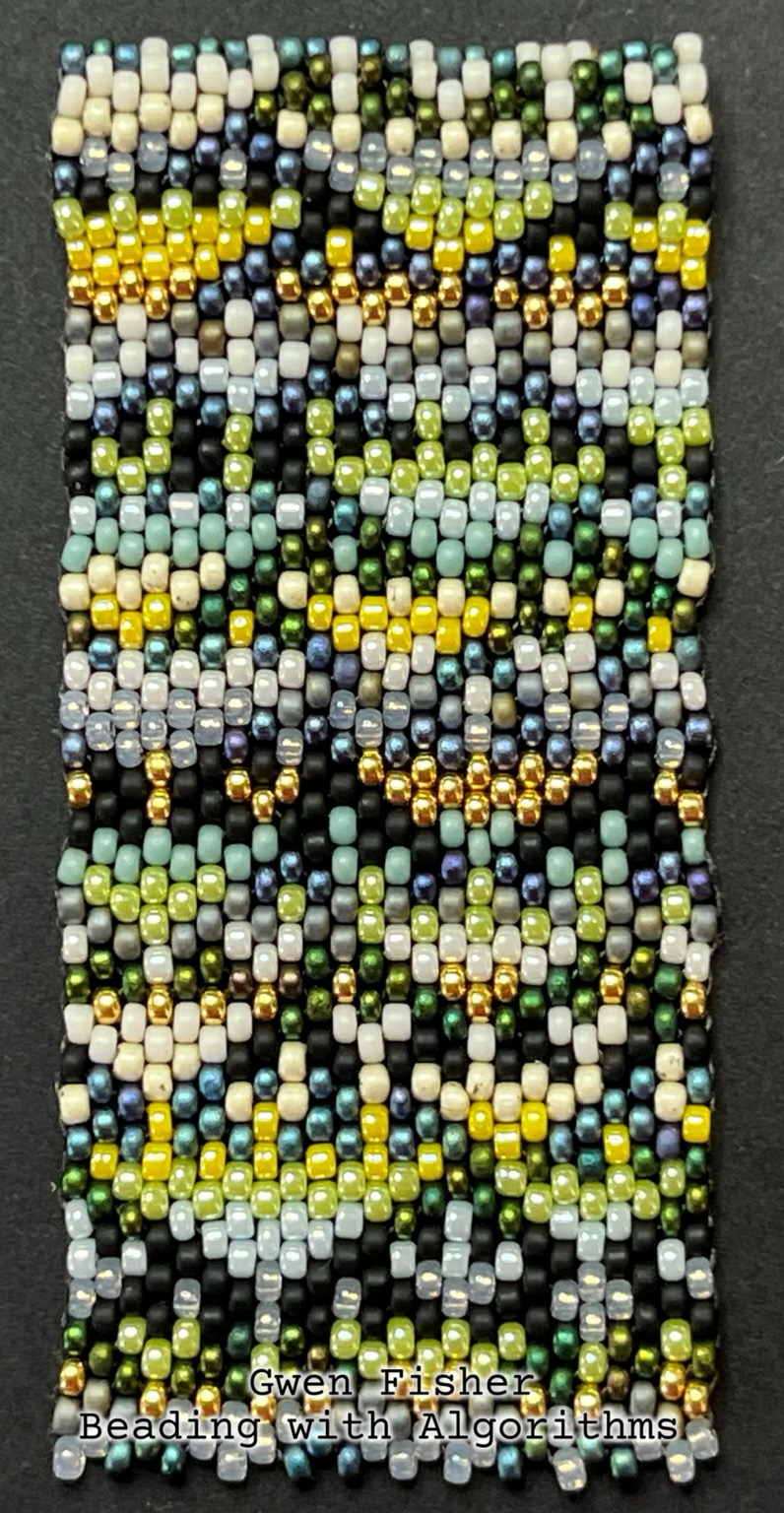
gwenbeads@mathstodon.xyzTwelve years. I started this project twelve years ago, and today I hold the result in my hand. It’s a book that combines bead weaving with math called, “Beading with Algorithms: Cellular Automata in Peyote Stitch.” With help from mathematician and artist Roger Antonsen, graphic designer Zelda Lin, a handful of talented proof readers, and the good people from World Scientific Publishing Company, my dream of combining my loves of math, art, and teaching into a book is finally a reality.
This book is the first of its kind, a recipe book of algorithms that can be used and combined to generate colorful patterns in peyote stitch beadwork in any size and shape you desire. These algorithms could also be applied to other pixelated art forms like tile laying, embroidery, crochet, and quilts. We included projects like bracelets, pill pouches, pendants, beaded beads, and key chains. We also included a bunch of different grids that you can photocopy and color with markers.
Of course I’m biased, but I think it’s a really beautiful book. We included multiple colorful images on almost every page, 172 pages in all. It was a huge layout challenge, but Zelda nailed it. My original goal was to write 128 pages on how to use algorithms to make beaded jewelry, but the more we explored the space, the more we found. Not just millions of algorithms, the space of possibilities is infinite. So of course, we couldn’t include them all. But we used math and Roger’s custom software that he wrote for this project to help us find dozens of the easiest algorithms and more than a hundred more in increasing levels of complexity. We included all of our favorites. 1/2