Posts
3275Following
709Followers
1570Cloudflare just published a vibe coded blog post claiming they implemented Matrix on cloudflare workers. They didn't, their post and README is AI generated and the code doesn't do any of the core parts of matrix that make it secure and interoperable. Instead it's littered with 'TODO: Check authorisation' and similar
https://blog.cloudflare.com/serverless-matrix-homeserver-workers/
Dio9sys
Dio9sys@haunted.computerFriends, Romans, countrymen, lend me your ear.
If you are writing about a CVE or compiling a list of CVEs and their proof of concept code, please please please mirror the original proof of concept somewhere. I don't care if it's an unformatted .py file on your server. Just put it somewhere rather than hoping that that github user in China won't get their account deleted at any point in the next 15 years.
Wayback machine is down today. Swear words have been said.
Kim Zetter
kimzetter@infosec.exchangeThe Booz Allen tech contractor behind Treasury Department's unprecedented decision yesterday to cancel all 31 of its contracts with the consulting firm, took the job with Booz Allen - much like Edward Snowden before him - specifically to get access to IRS tax records of President Trump and leak them. And not only Trump's records, he stole the tax records of more than 400,000 other individual and corporate taxpayers -- leaking some of these to the media as well. All of this contributed to the Treasury decision yesterday. https://www.zetter-zeroday.com/booz-allen-tech-contractor-took-irs-job-specifically-to-leak-trumps-tax-records/
Insinuator
Insinuator@infosec.exchangeNew post: Incident Response in GCP: Out of Scope – Ouf of Mind https://insinuator.net/2026/01/incident-response-in-gcp-out-of-scope-ouf-of-mind/
Chris John Riley 
ChrisJohnRiley@infosec.exchange
Just under a year ago I was planning to leave Google after 10 years. Since then I've been considering what's next (and doing some advisory work on the side).
I've slowly been giving more and more thought to how to give back in a sustainable way that works for me.
With that in mind, if you know of any organisations who offer security consulting/testing (pentesting) for NGOs or other worthy causes, please share 🙏
(Please re-toot for reach)
Slashdot 
slashdot@mastodon.cloud
ReactOS Celebrates 30 Years https://news.slashdot.org/story/26/01/27/0053233/reactos-celebrates-30-years?utm_source=rss1.0mainlinkanon
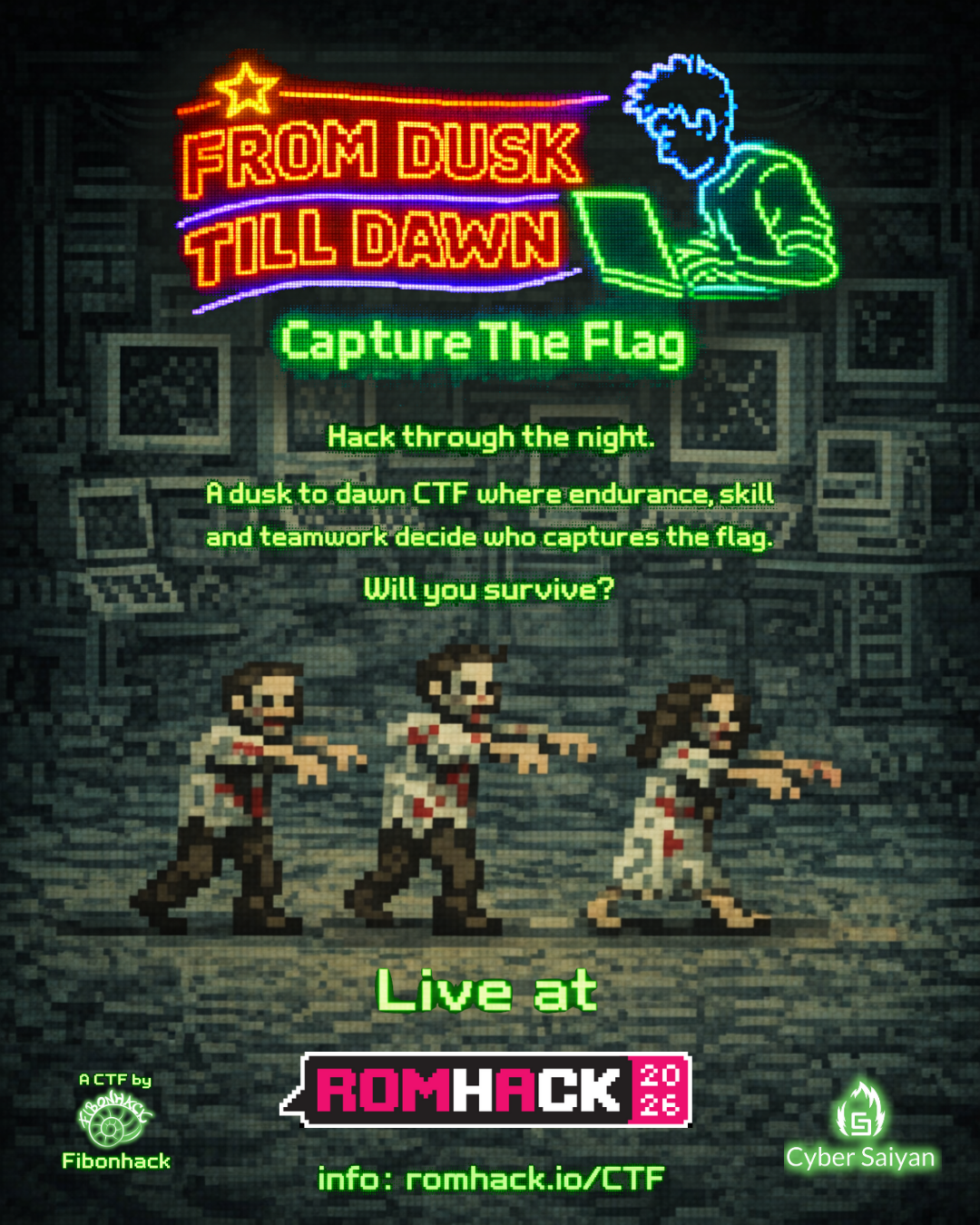
Cyber Saiyan
cybersaiyan@infosec.exchangeAre you ready to survive the night at RomHack Camp? 🌙
We believe the best hacking stories happen after midnight. That’s why for RomHack Camp 2026, we are teaming up with Fibonhack to bring you another intense competition: "From Dusk Till Dawn"
This isn’t just another CTF. It’s an on-site, 12-hour overnight marathon taking place at RomHack Camp.
The Roadmap to Glory
1️⃣ May 9-10: Open Online Qualifiers (24h)
2️⃣ The Selection: The Top 5 teams qualify for the Camp
3️⃣ Oct 2–3: The Finals. 19:00 to 07:00. On-site. No sleep. Pure skill.
From Web Security and Binary Exploitation to Cryptography and Reverse Engineering, Fibonhack is preparing a set of challenges that will push even the most seasoned researchers to their limit.
Mark your calendars. Sharpen your tools. The long night is coming.
👉 Follow Fibonhack and Cyber Saiyan for the upcoming quals registration link! 🔗 More info: https://romhack.io/ctf
#RomHackCamp #CyberSecurity #CyberSaiyan #CTF #Hacking #Rome #Fibonhack
JP Mens
jpmens@mastodon.socialLong shot: do I know anybody in Europe who can provide two dozen 12 row, 80 column punch cards, preferably punched with a specific text? (no advertising)
Background: August of this year marks 45th anniversary of a Nixdorf Computer apprenticeship, and we're meeting. I thought it would be cute to present colleagues with a punch card (which is what we first programmed on) as a souvenir.
Obviously I'd be very willing to pay for the service!
Boosts appreciated.
stefan brunthaler
sbrunthaler@mastodon.socialJust read this via repost from @HalvarFlake
https://sean.heelan.io/2026/01/18/on-the-coming-industrialisation-of-exploit-generation-with-llms/
This post from Sean Heelan is probably the most important post in that domain (being LLMs in offensive security contexts) in quite a while. We're already discussing this in my research group, and I have some initial thoughts. Exciting times!
Arne Brasseur
plexus@toot.catBit of a long shot, would anyone on here know how to get in touch with anyone from the Finnish demoscene group Future Crew, in particular Psi (Sami Tammilehto)? Are any on them on fedi? They must be in their 50's now.
I'd like to ask if he still has the Scream Tracker 3 source code, and if he would consider releasing it... It's such an important part of computing and music history. It deserves preservation.
Update: hearsay is that Psi is not interested in releasing the sources. See replies.
Synacktiv
synacktiv@bird.makeupAt #Pwn2Own Berlin 2025, a full exploit chain against VMware Workstation was demonstrated via a heap overflow in the PVSCSI controller.
Despite Windows 11 LFH mitigations, advanced heap shaping and side-channel techniques enabled a reliable exploit.
🔍 Full technical write-up 👇
https://www.synacktiv.com/en/publications/on-the-clock-escaping-vmware-workstation-at-pwn2own-berlin-2025
buherator
buheratorhttps://www.akamai.com/blog/security-research/2026/jan/cve-2026-23864-react-nextjs-denial-of-service
buherator
buheratorhttps://grahamhelton.com/blog/nodes-proxy-rce
Thread with vendor response/workaround:
https://threadreaderapp.com/thread/2015789985459212714.html
#k8s