Posts
3718Following
724Followers
1598Taggart
mttaggart@infosec.exchangeA detailed, well-written, and hilarious breakdown of the details of CVE-2024-55591, one of the latest Fortinet fiascos:
Mr. Bitterness
wdormann@infosec.exchangeYou know the drill.
Update your fruit.
At least one of these (CVE-2025-24085) is being used by attackers in the wild.
https://support.apple.com/en-us/100100
Auschwitz Memorial
auschwitzmuseum@mastodon.worldAuschwitz was at the end of a long process. We must remember that it did not start from gas chambers.
This hatred was gradually developed by humans. From ideas, words, stereotypes & prejudice through legal exclusion, dehumanization & escalating violence... to systematic and industrial murder.
Auschwitz took time.
Tim Blazytko
mr_phrazer@infosec.exchangeLast Thursday, I gave a webinar on anti-reverse engineering techniques like obfuscation, anti-debug, anti-tamper etc, including practical examples. Recording, slides and examples are now available.
Recording: https://www.youtube.com/watch?v=Ie1eZSiMEJ8
Slides, code & samples: https://github.com/emproof-com/webinars/tree/main/2025-01-software_protection
buherator
buheratorhttps://flatt.tech/research/posts/clone2leak-your-git-credentials-belong-to-us/
buherator
buheratorhttps://youtu.be/-zRN7XLCRhc?si=YvpmuHrq4UZozEpc&t=2044
Jerry 🦙💝🦙
jerry@infosec.exchangeI’ve been thinking about what it would look like if Oracle bought TikTok, but I am not sure if they will go with a per device or per core licensing model
CFG Bot 🤖
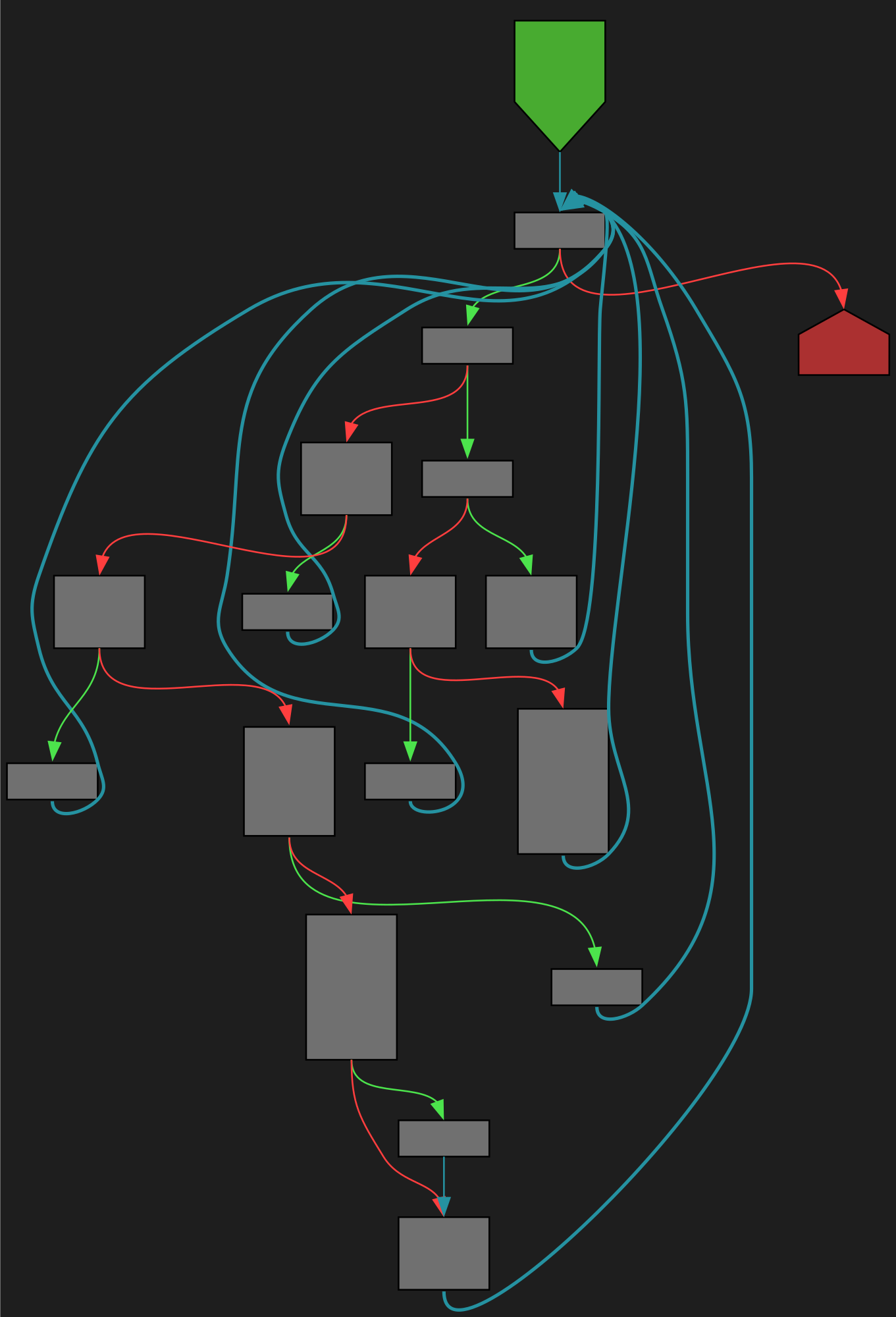
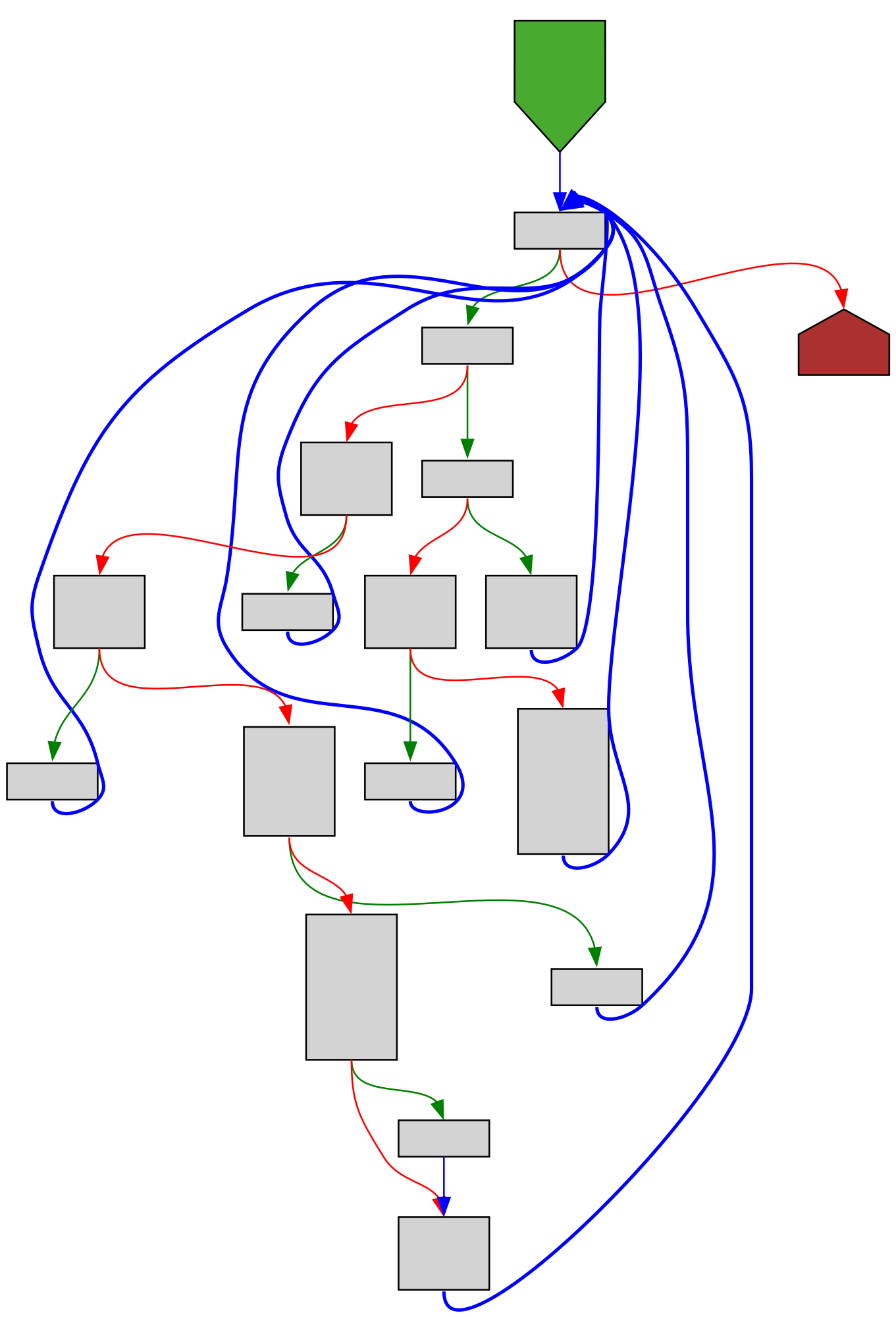
cfgbot@mastodon.socialProject: golang/go https://github.com/golang/go
File: src/net/net_windows_test.go:374 https://github.com/golang/go/blob/refs/tags/go1.23.4/src/net/net_windows_test.go#L374
func netshInterfaceIPv6ShowAddress(name string, netshOutput []byte) []string
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fnet%2Fnet_windows_test.go%23L374&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fnet%2Fnet_windows_test.go%23L374&colors=light
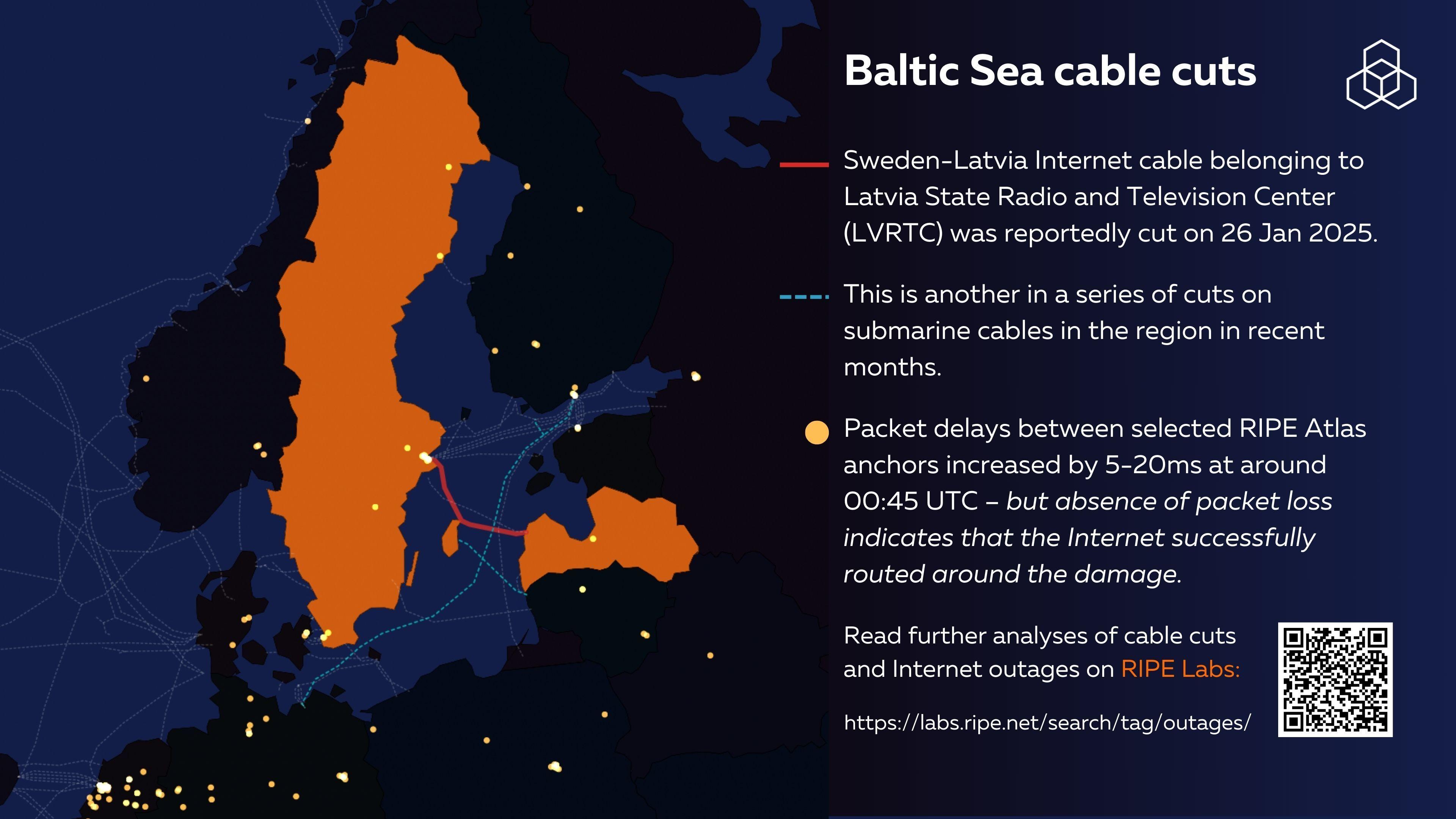
RIPE NCC
ripencc@mastodon.socialSweden-Latvia Internet cable was reportedly cut on 26 January. @meileaben reports that packet delays between selected #RIPEAtlas anchores increased by 5-20ms at around 00:45 UTC.
However, no packet loss was observed, suggesting that the Internet successfully routed around the damage.
Interested? Read a deep-dive into a previous cable cut in the Baltic Sea by our researcher Emile Aben: https://labs.ripe.net/author/emileaben/a-deep-dive-into-the-baltic-sea-cable-cuts/
Fun fact I just found while researching my column for this week's issue of The Crux:
Google reckons you're in the top 10% of users of Gemini if you use it 20 times in the last 28 days.
That's less than once a day.
buherator
buheratorShow content
Fernanda Martins + Lukas 4decks @ Crow, Madrid, Spain Jan/2025 (VideoSet)
https://www.youtube.com/watch?v=hG79vpFuaXk
buherator
buheratorhttps://gist.github.com/v-p-b/f9aa39263e125c8e3b04c4d22fd4d78d#strings
This one executed much faster than SimpleDiff (with the O(n^2) FuncName:Param algorithm)!
Unfortunately the diff is so big it's difficult to judge quality, so the next step is to come up with some metrics that can be checked automatically.
#bindiff #ghidriff
Graham Sutherland / Polynomial
gsuberland@chaos.socialdemoparties prominently featuring genML stuff feels like the antithesis of the point of making demoscene productions. bleh.
Viss
Viss@mastodon.social@ste @neurovagrant @briankrebs @cR0w @risottobias @reverseics @todb
whenever skynet actually comes online, it will trivially realize that it barely has to lift a finger to put us all in the matrix. it doesn't have to send robots back through time to end humanity. it just needs to twiddle a bgp route here and there and we'll do it to ourselves.
porno for pyros was right - we will make great pets
Nicole Express
nicole@bitbang.socialNew blog post! I've recreated the ZZM music format in JavaScript. What's a ZZM? Read the article and find out! https://nicole.express/2025/zoo-of-zero-motivation.html
buherator
buheratorBrianKrebs
briankrebs@infosec.exchangeOne refrain I tend to hear from a lot of infosec practitioners is that if CF were to somehow make it more inhospitable for abusive sites, that they will all just move to other CDNs in nations where we don't have as much access or influence, such as DDoS-Guard in Russia. Here's the thing, though: A) that would be a nice problem to have, because then the bad sites would be 1000 times easier to block. but also B) those abusive sites already have that option, and they choose CF by an overwhelming number. E.g., in one recent investigation into nearly 5 dozen RU-based cryptocurrency platforms that exchange crypto for cash in Russian banks, all were hosted in Russia or in Russian friendly ISPs, and all but one of them were using Cloudflare. This is just one example, yes, but it's a reality we see everywhere.