Posts
3259Following
709Followers
1567daniel:// stenberg://
bagder@mastodon.socialCurrent #curl bug-bounty stats (since April 2019).
Reports: 475
Confirmed security issues: 73 (15%)
Identified bugs (but not security problems): 92 (19%)
Invalid: 310 (65%)
 𝚜𝚎𝚕𝚎𝚊
𝚜𝚎𝚕𝚎𝚊 
selea@social.linux.pizza
So what did I find in my EV-charger wifi-card?
Basically, it is a raspberry pi.
The SD-card contains goodies, like a private ssh-key that apparently gave me access to their jumphost (no restrictions in their shell either).
The NTP was also not configured, it also contained the entire bash-history, including all the "failed commands" and apparently a password to something.
I guess I'll spend some time on the phone tomorrow
Erik Uden 🍑
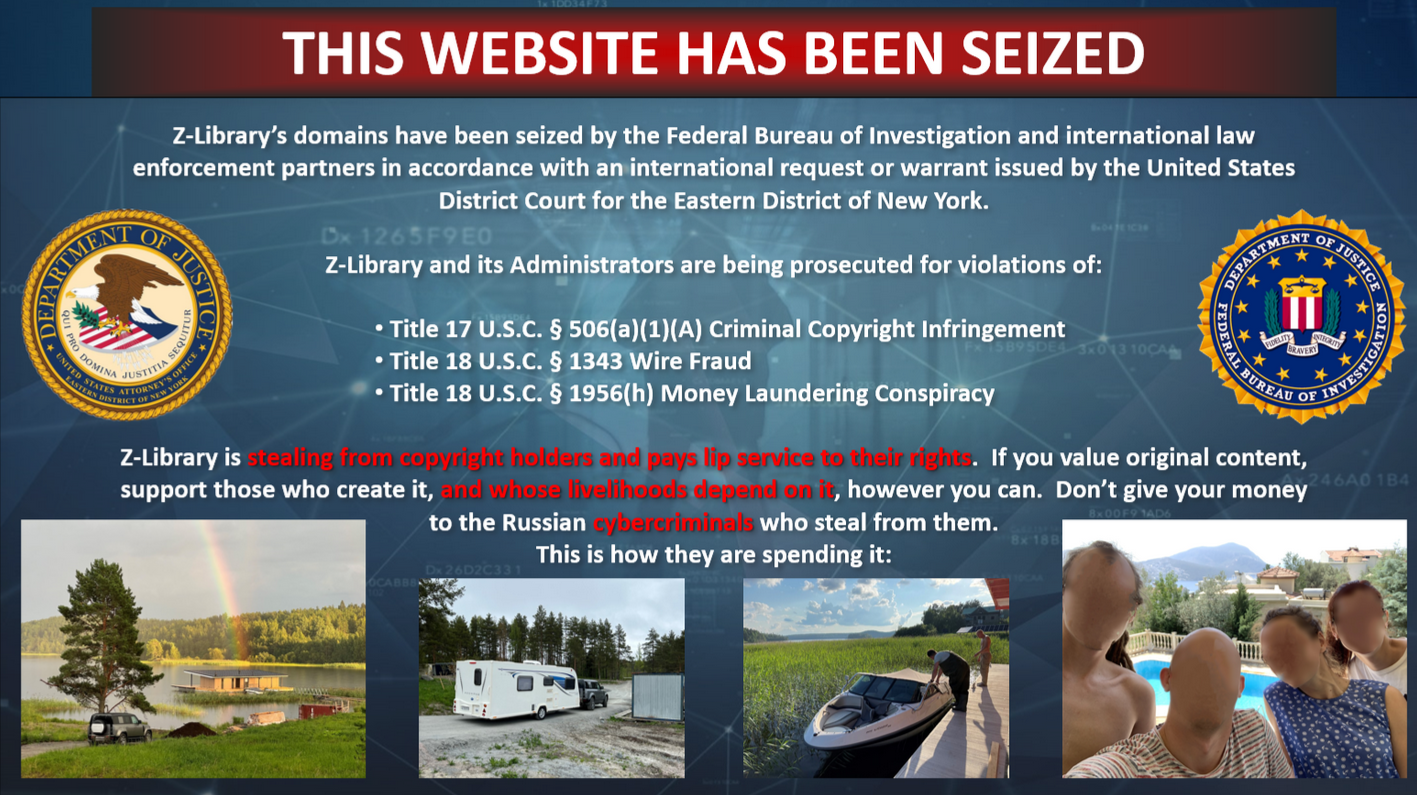
ErikUden@mastodon.delmao, the FBI is mad that the Z-Library founders are having holidays
Erik Uden 🍑
ErikUden@mastodon.deyou can check this yourself here: http://z-lib.org
I do not think these people are cybercriminals. They are the best we got to help information preservation (next to the Internet Archive) in the 21st century.
The fact they had to mention that these people are Russian also strikes me as odd. They don't even seem to be government affiliated, I'm pretty sure the FBI would've said so if there was even a slight hint of that.
While OpenAI can freely use all copyrighted material and make billions off of it, these people giving it out for free are supposed “criminals”. Aaron Schwartz didn't die for this.
Joxean Koret (@matalaz)
joxean@mastodon.socialQuestion about IDA and Ghidra considering the latest IDA license changes, regarding #Diaphora: If a (highly integrated) Ghidra port of Diaphora appears "soon", would you...
Talos Vulnerability Reports
talosvulnsFoxit Reader checkbox Calculate use-after-free vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2024-1967
CVE-2024-28888
Dino A. Dai Zovi
dinodaizovi@bird.makeupInteresting listen (NSA's Brian Snow on risk-based security): https://t.co/MwSi8KE8kA
"Basically it boils down to the fact that it's impossible to assign a likelihood to an unknown attack.
So how on earth did risk-based security become the 'standard' way of doing things in the enterprise? What use is a risk register if high-impact, low-likelihood adverse events can't be reliably quantified?"
John Carlos Baez
johncarlosbaez@mathstodon.xyzThis undergraduate thesis by Jan Strehmel deserves a prize:
𝐀𝐛𝐬𝐭𝐫𝐚𝐜𝐭. One of the most fundamental unanswered questions that has been bothering mankind during the Anthropocene is whether the use of swearwords in open source code is positively or negatively correlated with source code quality. To investigate this profound matter we crawled and analysed over 3800 C open source code containing English swearwords and over 7600 C open source code not containing swearwords from GitHub. Subsequently, we quantified the adherence of these two distinct sets of source code to coding standards, which we deploy as a proxy for source code quality via the SoftWipe tool developed in our group. We find that open source code containing swearwords exhibit significantly better code quality than those not containing swearwords under several statistical tests. We hypothesise that the use of swearwords constitutes an indicator of a profound emotional involvement of the programmer with the code and its inherent complexities, thus yielding better code based on a thorough, critical, and dialectic code analysis process.
https://cme.h-its.org/exelixis/pubs/JanThesis.pdf
It cites some previous research:
• Yehuda Baruch et al. Swearing at work: the mixed outcomes of profanity,
Journal of Managerial Psychology 32 (Jan. 2017),149–162, https://doi.org/10.1108/JMP-04-2016-010
𝐀𝐛𝐬𝐭𝐫𝐚𝐜𝐭. In contrast to much of the incivility and social norms literatures, the authors find that male and female business executives, lawyers and doctors of all ages admit to swearing. Further, swearing can lead to positive outcomes at the individual, interpersonal and group levels, including stress-relief, communication-enrichment and socialization-enhancement
0patch
0patch@infosec.exchangeMicropatches for Windows Installer Elevation of Privilege Vulnerability (CVE-2024-38014)
https://blog.0patch.com/2024/10/micropatches-for-windows-installer.html
screaminggoat
screaminggoat@infosec.exchangeGoogle Chrome security advisory: Stable Channel Update for Desktop
New version 129.0.6668.89/.90 for Windows, Mac and 129.0.6668.89 for Linux includes 4 security fixes, 3 externally reported:
- CVE-2024-7025 (high) Integer overflow in Layout
- CVE-2024-9369 (high) Insufficient data validation in Mojo
- CVE-2024-9370 (high) Inappropriate implementation in V8
No mention of exploitation.
SIEM Shady
CDubbs@infosec.exchange@wendynather @douglevin @RGB_Lights From a performance perspective, exclusion management is important. Too many of these security tools are "expanding capability" to the point they have overlapping functions and you're chasing race conditions.
Did tool A catch the thing because it checked first, or did tool B miss it?
Is tool A misbehaving because tool B is messing with the process or locking the target?
clearbluejar
clearbluejar@infosec.exchange🚀 Taking a quick dive into Ghidra 11.2’s stack-based string handling! 🛠️
Check out the improvements from version 11.1.2 to the new release. Stack strings have been a long time coming, but Ghidra is ever improving! 👏 #Ghidra #ReverseEngineering #everydayghidra
Rob Joyce
RGB_Lights@infosec.exchangeIt’s troubling to see intrusion responses struggle due to lack of logging and visibility. Build a robust logging strategy and practice hunts to truly understand what you're monitoring and what you can trust. Incident time is a painful moment for discovery learning.
Gynvael Coldwind
gynvael@bird.makeupWe're both close to half a mil total downloads and to finalizing Issue #5 (if you want to get your article in, you have literally a few more days left to submit! there's still time, but not a lot)
Marc R
seifreed@mastodont.catToday, I'm feeling generous and giving away 2 free tickets for #r2con2024. What do you have to do?
You have to reply to this tweet saying what you like most about #radare and what you use it for. The most original comment will be the winner! @radareorg @pancake https://rada.re/con/2024/
rostiger
rostiger@merveilles.town"After decades of searching for photo-realism and performance, the soon to be over myth of perpetual growth is leaving the stage to more computationally minimal aesthetics and dispositives to refocus on the power of concept, interaction, stories and subjectivity in a scarce real-world."
From the European Permacomputing Gamejam Site:
https://itch.io/jam/europermajam
Clément Labro
itm4n@infosec.exchangeAnother cool blog post by @sploutchy (Compass Security)
"COM Cross-Session Activation"
Quick read, and straight to the point. This article provides a real-life example (Google Updater service here) showing one way to exploit a COM class for local privilege escalation on Windows. 👌
👉 https://blog.compass-security.com/2024/10/com-cross-session-activation/