Posts
3144Following
707Followers
1555Lukas Beran
lukasberancz@infosec.exchangeYou asked, and we delivered! Check out the new Microsoft Incident Response Ninja Hub for a compilation of the research and guides that the Microsoft IR team has developed over the years on threat hunting, case studies, and more.
gergelykalman
gergelykalman@infosec.exchangeFor those of you who might like it: Here are the slides from my Alligatorcon talk:
https://gergelykalman.com/the-forgotten-art-of-filesystem-magic-alligatorcon-2024-slides.html
Ryan Baumann
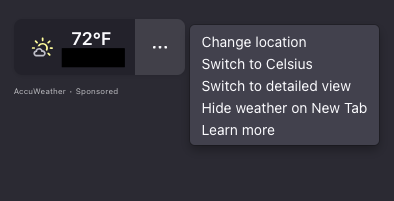
ryanfb@digipres.clubMozilla, reading the room extremely well, seemingly just recently flipped the switch to enable-by-default sponsored weather results from AccuWeather in every new Firefox tab you open. Clicking "Learn more" takes you here, with zero information on if your location is sent to AccuWeather every time you open a new tab: https://support.mozilla.org/en-US/kb/customize-items-on-firefox-new-tab-page
Probably only noticed because I normally have a blank new tab page but this showed up after updating Firefox!
buherator
buheratorhttps://www.crowdfense.com/windows-wi-fi-driver-rce-vulnerability-cve-2024-30078/
buherator
buheratorhttps://blogs.windows.com/windowsexperience/2024/09/12/taking-steps-that-drive-resiliency-and-security-for-windows-customers/?s=09
screaminggoat
screaminggoat@infosec.exchangeCISA: Vulnerability Summary for the Week of September 2, 2024
Sometimes I check the summary for hidden gems. This time, five of the Mozilla Firefox CVEs are CVSSv3.1: 9.8 critical
- CVE-2024-8381 type confusion
- CVE-2024-8384 memory corruption
- CVE-2024-8385 type confusion
- CVE-2024-8387 memory corruption
- CVE-2024-8389 memory corruption
At a glance, they're obviously high severity. It's just that you won't have that sense of urgency at the time of announcement because you didn't see the CVSS score, or understand the impact.
Let's not forget to mention Hall of Shame Progress Software for having LoadMaster vulnerability CVE-2024-7591 with a perfect 10.0 🥳
Jerry 🦙💝🦙
jerry@infosec.exchange@phil I think this one is pretty fresh: https://www.bleepingcomputer.com/news/security/fortinet-confirms-data-breach-after-hacker-claims-to-steal-440gb-of-files/
Talos Vulnerability Reports
talosvulnsMicrosoft High Definition Audio Bus Driver HDAudBus_DMA multiple irp complete requests vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2024-2008
Trend Zero Day Initiative
thezdi@infosec.exchangeIn part 2 of his #Exchange series, @chudypb describes the ApprovedApplicationCollection gadget. He also covers a path traversal in the Windows utility extrac32.exe, which allowed him to complete the chain for a full RCE in Exchange and remains unpatched.
https://www.zerodayinitiative.com/blog/2024/9/11/exploiting-exchange-powershell-after-proxynotshell-part-2-approvedapplicationcollection
buherator
buheratorhttps://bughunters.google.com/blog/6220757425586176/cvr-the-mines-of-kakad-m
Pretty sure I posted the OffensiveCon talk before, but it%27s always nice to have things written up
buherator
buheratorhttps://x41-dsec.de/lab/advisories/x41-2024-003-chilkat-asn1/
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20240911-00/?p=110247
buherator
buheratorhttps://blog.deeb.ch/posts/avred-update/
buherator
buheratorhttps://cyberscoop.com/wordpress-two-factor-authentication-supply-chain/
buherator
buheratorI ordered it through Blackwell's, that is a UK company but ships @nostarch books to EU too, so you can avoid dealing with customs yourself. Order tracking needs improvement.
https://blackwells.co.uk/bookshop/product/Windows-Security-Internals-by-James-Forshaw/9781718501980
Sarah Jamie Lewis
sarahjamielewis@mastodon.socialI really try to like Firefox, but the last 5 minutes really captures the kind of papercut that happens often:
- I open a new tab and firefox informs me it has updated itself and needs to restart and won't allow any further operations until it does so.
- Fine, I close and restart.
- I reopen Firefox to find a brand new sponsored weather widget on my otherwise blank new tab page - from a source I would never otherwise visit.
Thanks for breaking my flow and the privacy breach, I guess.
Matthew Garrett
mjg59@nondeterministic.computerThe promised writeup of how I discovered that the Feeld dating app was protecting private data by doing client-side filtering: https://mjg59.dreamwidth.org/70061.html
screaminggoat
screaminggoat@infosec.exchangeBleeping Computer: Adobe fixes Acrobat Reader zero-day with public PoC exploit
References:
- APSB24-70 Security update available for Adobe Acrobat and Reader (10 September 2024)
- APSB24-57 Security update available for Adobe Acrobat and Reader (13 August 2024)
Okay I already have an EXPMON thread here (see parent toots above) so I'll orphan the original Adobe September 2024 Patch Tuesday toot. It should be noted that CVE-2024-41869 (7.8 high) UAF to arbitrary code execution in Adobe Acrobat and Reader is a Zero Day (Proof of Concept exploit in the wild exists before the vulnerability was patched, unknown if actually exploited). Apparently the August patch wasn't sufficient for the vulnerability CVE-2024-39383 (7.8 high, which should also be considered a zero-day). Haifei Li wrote on the Bad Place: "We tested the (exactly the same) sample on the "patched" Adobe Reader version, it displayed additional dialogs, but if the user clicked/closed those dialogs, the app still crashed! Same UAF bug!"
In yesterday's Adobe Reader security advisory, Adobe didn't call attention to the fact that a Proof of Concept exploit exists in the wild, or however they would normally word it.
#expmon #adobe #proofofconcept #zeroday #vulnerability #CVE_2024_41869 #CVE_2024_39383