Posts
3146Following
707Followers
1555Trail of Bits
trailofbits@infosec.exchangeWe've completed a comparative security assessment of authorization policy languages: Cedar, Rego, and the OpenFGA modeling language.
If you are a language designer or a software developer, our AWS-sponsored assessment also provides recommendations for improving policy language design and for securing systems that use policy languages.
https://buff.ly/4cSO63s
DCoder 🇱🇹❤🇺🇦
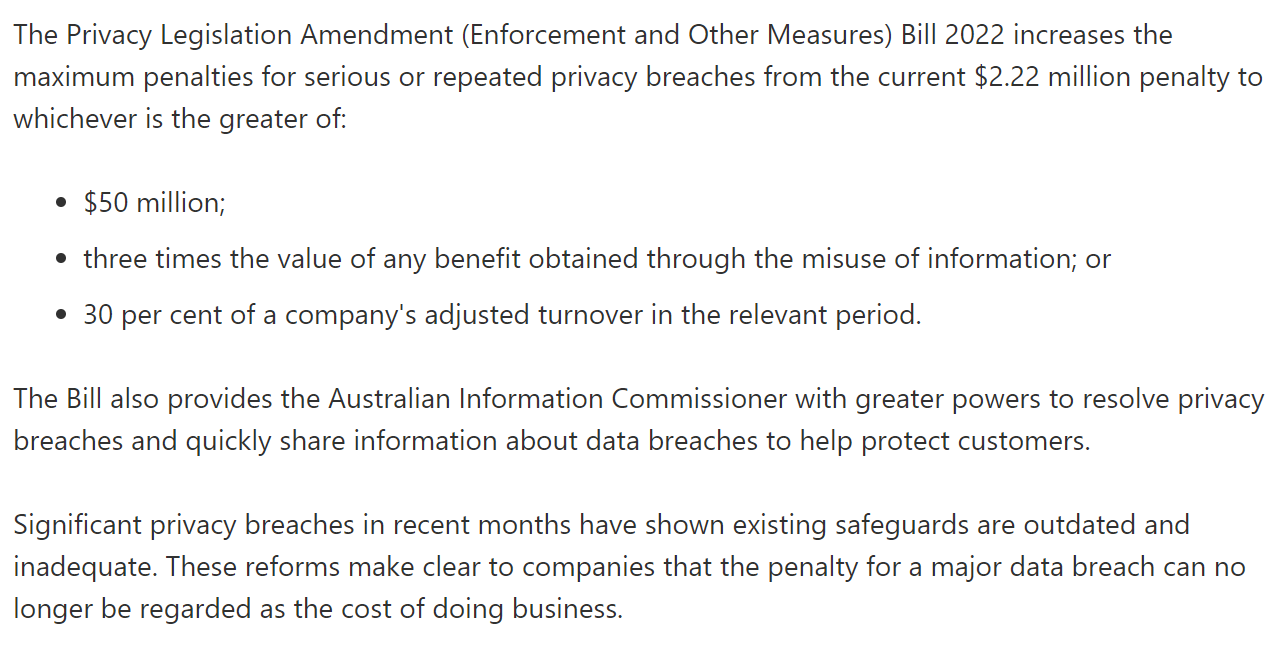
dcoderlt@ohai.socialAustralia really looked at GDPR and said “those fines are rookie numbers, mate”.
(from https://twitter.com/troyhunt/status/1597841957526568966 )
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgAs @echo_pbreyer reminded us, EU member states have revived their effort to force-install a child pornography scanner on our phones again. This idea was rejected twice before, but they'll keep trying. Here's an English transcript of what I said about this in Dutch parliament last year: https://berthub.eu/articles/posts/client-side-scanning-dutch-parliament/
Piotr Bazydło
chudypb@infosec.exchangeMy SharePoint RCE got fixed: CVE-2024-38018. Site Member privs should be enough to exploit.
I also found a DoS vuln that got patched today: CVE-2024-43466.
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38018
screaminggoat
screaminggoat@infosec.exchangeHappy #PatchTuesday from Microsoft: 79 new CVEs, 4 NEW EXPLOITED ZERO DAYS:
- CVE-2024-43491 (9.8 critical) Microsoft Windows Update Remote Code Execution Vulnerability (EXPLOITED)
- CVE-2024-38226 (7.3 high) Microsoft Publisher Security Feature Bypass Vulnerability (EXPLOITED)
- CVE-2024-38217 (5.4 medium) Windows Mark of the Web Security Feature Bypass Vulnerability (EXPLOITED and PUBLICLY DISCLOSED)
- CVE-2024-38014 (7.8 high) Windows Installer Elevation of Privilege Vulnerability (EXPLOITED)
EDIT: @BleepingComputer has mentioned that CVE-2024-38217 was marked publicly disclosed. Updated this to reflect it. See related reporting Microsoft September 2024 Patch Tuesday fixes 4 zero-days, 79 flaws
#microsoft #vulnerability #zeroday #eitw #activeexploitation #cve
Anderson Nascimento
andersonc0d3@infosec.exchangeMeasuring non-determinism in the Linux kernel
https://shape-of-code.com/2024/09/08/measuring-non-determinism-in-the-linux-kernel/
screaminggoat
screaminggoat@infosec.exchangeCitrix security advisory: Citrix Workspace app for Windows Security Bulletin CVE-2024-7889 and CVE-2024-7890
Happy #PatchTuesday from Citrix.
- CVE-2024-7889 (CVSSv4: 7.0 high) LPE
- CVE-2024-7890 (CVSSv4: 5.4 medium) LPE
Fixed in Citrix Workspace app for Windows 2405 and later versions, Citrix Workspace app for Windows 2402 CU1 LTSR and later versions. No mention of exploitation.
screaminggoat
screaminggoat@infosec.exchangeIvanti security advisory: September 2024 Security Update
Happy #PatchTuesday from Ivanti. There are some serious vulnerabilities. I want to emphasize that Ivanti stated they "have no evidence of these vulnerabilities being exploited in the wild." See the following advisories:
- Security Advisory EPM September 2024 for EPM 2024 and EPM 2022
- Security Advisory Ivanti Cloud Service Appliance (CSA) (CVE-2024-8190)
- Security Advisory Ivanti Workspace Control (IWC)
The big ones:
- CVE-2024-29847 (perfect 10.0 critical 🥳 cc: @cR0w) deserialization in the agent portal of Ivanti EPM before 2022 SU6/September 2024 update allows unauth RCE
- CVE-2024-32840, CVE-2024-32842, CVE-2024-32843, CVE-2024-32845, CVE-2024-32846, CVE-2024-32848, CVE-2024-34783, CVE-2024-34785: unspecified SQL injection in Ivanti EPM before 2022 SU6/September 2024 update allow remote authenticated attacker with admin privileges to RCE
Melanie Imming ✅
meliimming@akademienl.socialIt is shocking that after moving from Google workspace to Proton as the back office for our professional email adresses etc, all the major Dutch institutions are blocking us as spam. All our contacts have to whitelist us individually. So I think we are forced to go back to Google, where we had this problem occasionally but not as massively as now. It seems the reason is that Microsoft, used by almost all institutions in NL, simply blocks all Proton mail .😈 ( DNS=OK configured)
abadidea
0xabad1dea@infosec.exchangeI would like to impress upon product managers that a code security review does not consist of me sitting down with the files in alphabetical order and reading each and every line exactly once in order and checking off whether it is or isn’t secure
hanno
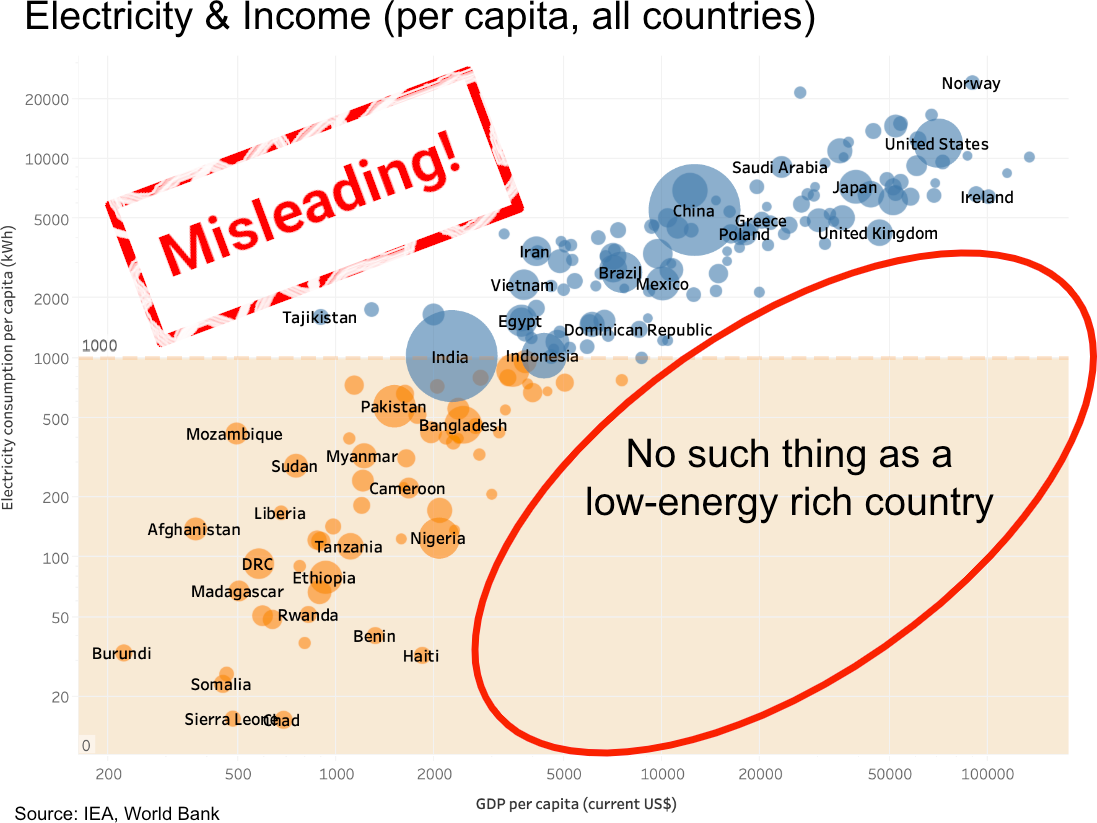
hanno@mastodon.socialThis widely shared infographic uses a trick to make its message appear much stronger than it actually is. It seems to show a strong correlation between energy consumption and the wealth of a country. By using a logarithmic scale, the correlation appears much stronger than it actually is. I covered this before in articles, and now have also uploaded a short video ⚡💸🎥 https://www.youtube.com/watch?v=2xZ6CihdKu0 🧵
Solarbird 
moira@mastodon.murkworks.net
@mcc (In short, as "AI summaries" corrupt more and more material, I think we're going to end up seeing more and more arguments where people are not reading the article, but instead are just the broken AI paraphrase, and starting fights based on what the LLM got wrong.)
Cassandra is only carbon now
xgranade@wandering.shop@mcc This, this, this. Whether or not LLMs "work" (they don't), whether or not they can be ethically trained (they can't), whether or not they can be reduced to an energy and CPU scale that's reasonable to run locally (they can't), LLMs still fundamentally invert the relationship we have with written language.
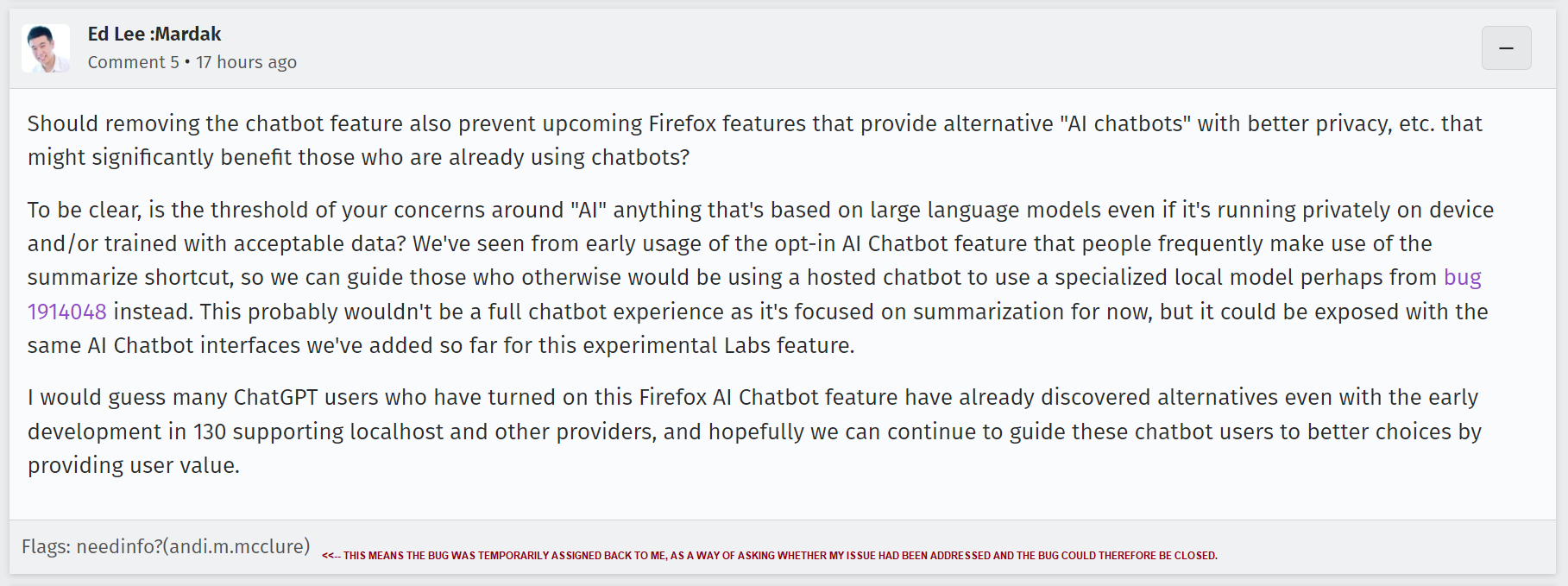
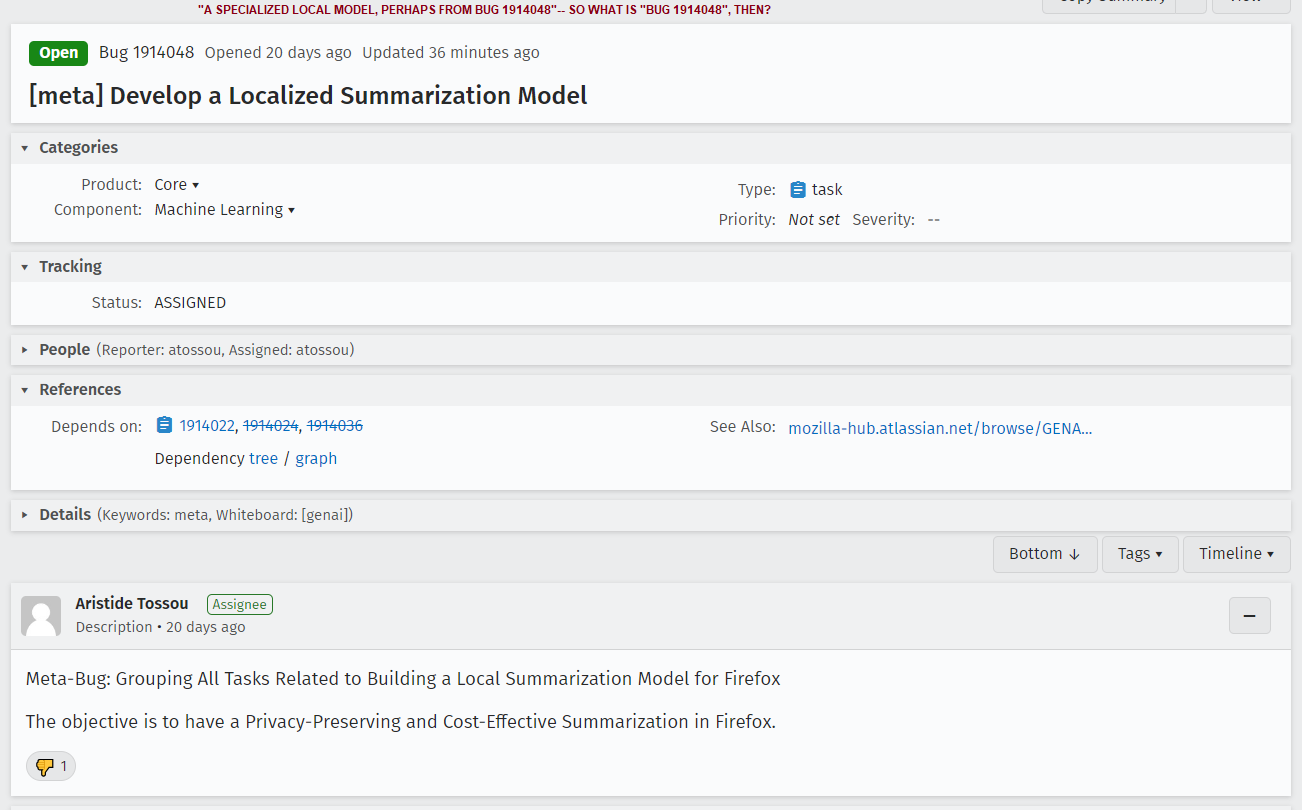
I have one contact from a Mozilla dev and a detail-free tracking issue to work from here. I can't know how this subject is being discussed within Mozilla and you should be clearly aware I'm speculating. But what I see here is, they view "summarization" as a component of the "AI chatbot" model which they can tear off and move into a local model, thus "solving" the privacy/safety problems.
Which alarms the heck out of me, as the other issues— licensing, environmental impact, and
➡️ lying ⬅️
remain.
Here is how I interpret what I see here. Mozilla, or the people within Mozilla driving the "AI chatbot" feature, view the "labs" chatbot feature as only step one of a larger plan. Their goal is to get people used to interacting with "AI" through the Mozilla sidebar, and once they're used to that, they want to encourage people to switch out OpenAI or Bing in this sidebar for Mozilla's AI (some part of which might be running locally).
In other words, Mozilla wants to be the next OpenAI.
Binary Ninja
binaryninja@infosec.exchangeThere is a known issue in the latest stable 4.1.5902 we wanted to make folks aware of. If you save a bndb while debugging, the database can get into an improper state and it may appear to lose user changes. The issue is resolved in the latest dev builds.
For those who are using the latest stable, you can either switch to dev or avoid saving during debugging (saving after debugging is unaffected). Impacted users can contact support (https://binary.ninja/support/) or see: https://github.com/Vector35/debugger/issues/612
screaminggoat
screaminggoat@infosec.exchangewatchTowr: Veeam Backup & Response - RCE With Auth, But Mostly Without Auth (CVE-2024-40711)
Reference: CVE-2024-40711 (9.8 critical, disclosed 04 September 2024 by Veeam) Veeam Backup & Replication: A deserialization of untrusted data vulnerability with a malicious payload can allow an unauthenticated remote code execution (RCE). This vulnerability was reported by reported by Florian Hauser @frycos with CODE WHITE Gmbh @codewhitesec.
watchTowr doing what they do best, root cause analysis of vulnerabilities and breaking it down Barney style. Veeam Backup and Replication's CVE-2024-40711 has an authenticated RCE with a 9.8? watchTowr does patch-diffing (a lot of code and rambling). They name drop James Forshaw @tiraniddo in referencing “Stupid is as Stupid Does When It Comes to .NET Remoting”
Okay in reading through this, CVE-2024-40711 is actually comprised of two separate bugs. Veeam silently patched an improper authorization bug, then the deserialisation bug 3 months later. watchTowr claims that there is a way to bypass CVE-2024-40711 (details are still under embargo). They do not release a proof of concept due to the current situation and proclivity for ransomware actors to go after Veeam backups.
#cve_2024_40711 #vulnerability #rootcauseanalysis #cve #veeam #infosec #cybersecurity
Zig Weekly
zig_discussions@mastodon.socialData-Oriented Design Revisited: Type Safety in the Zig Compiler
https://www.youtube.com/watch?v=KOZcJwGdQok
Discussions: https://discu.eu/q/https://www.youtube.com/watch?v=KOZcJwGdQok