Posts
3863Following
725Followers
1594Clément Labro
itm4n@infosec.exchangeYet another abuse of the missing "CrossDevice.Streaming.Source.dll" DLL!
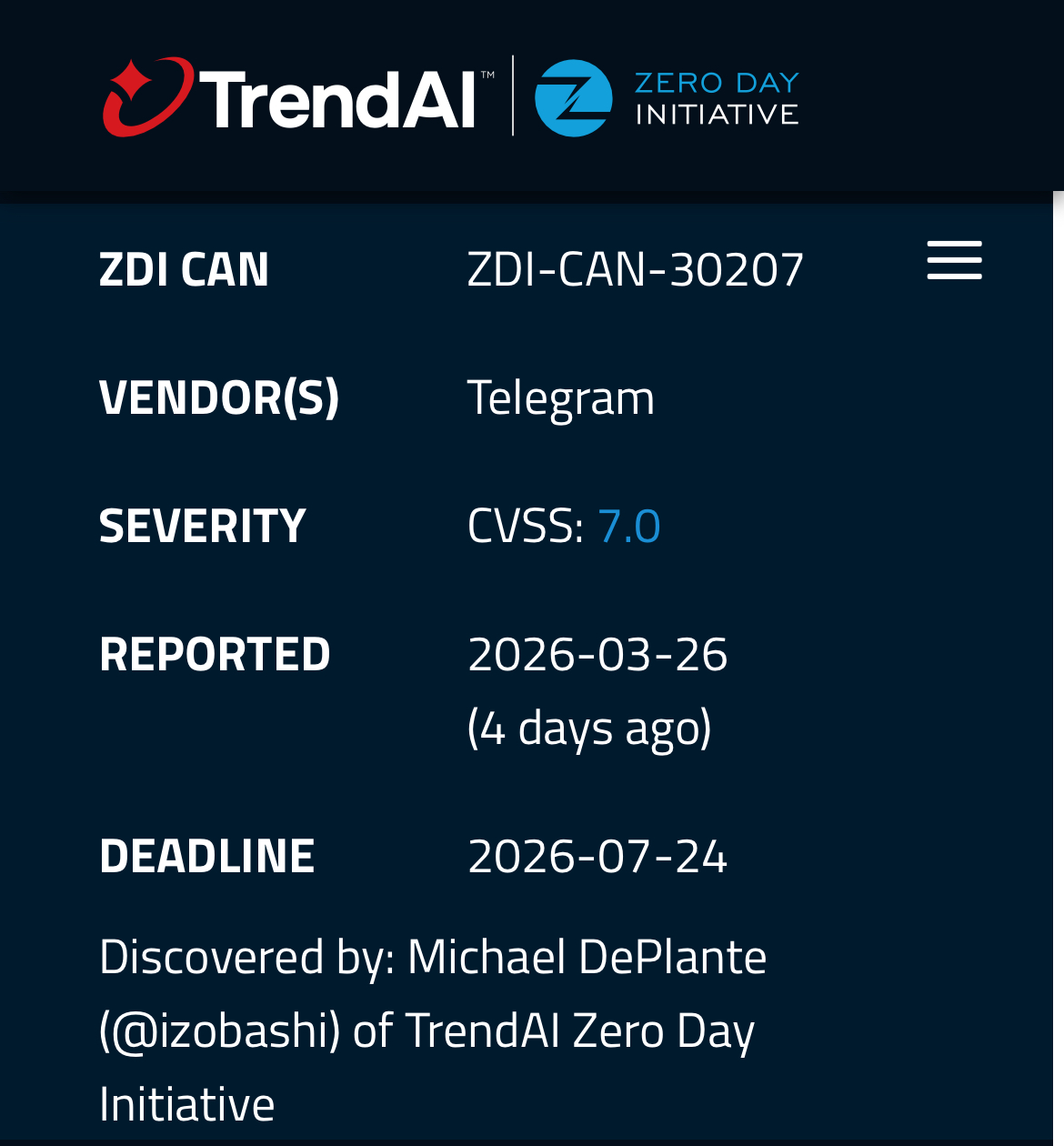
After CVE-2025-24076 / CVE-2025-24076 found by Compass Security, Researcher Oscar Zanotti Campo found another vulnerability that he could exploit using the built-in misconfigured COM class referencing this DLL. This is CVE-2026-21508. 🔥
👉 https://0xc4r.github.io/posts/CVE-2026-21508/
👉 https://github.com/0xc4r/CVE-2026-21508_POC/
👉 https://blog.0patch.com/2026/03/micropatches-released-for-windows.html
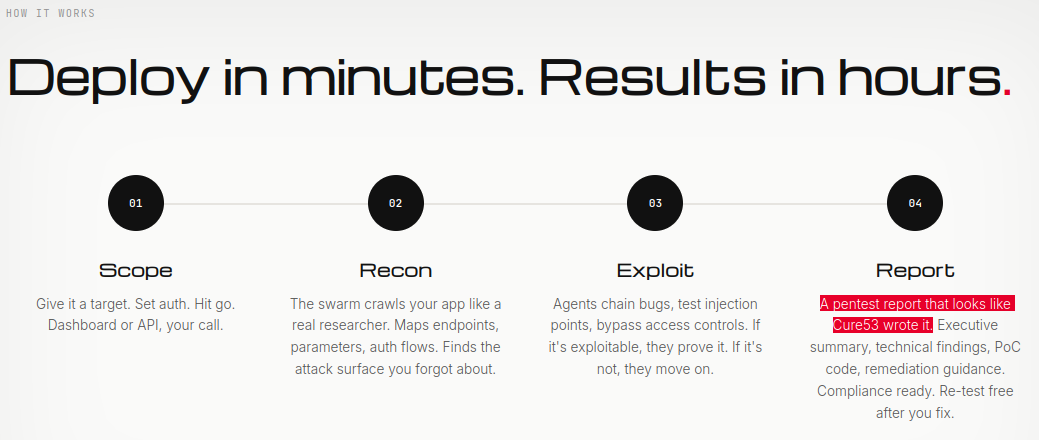
Cure53 🇪🇺
cure53@infosec.exchangeDoes anyone have a contact at pwn.ai?
We would kinda like to have a conversation with them...
Cassandra is only carbon now
xgranade@wandering.shopReading analysis of the Claude Code leak (not reading the code itself, of course) is evidence towards what I had kind of suspected, that the whole thing is a giant magic trick not only in the straightforward LLMentalist way, but also in the sleight of hand way off making you think that this pile of regexes and JSON schema validation loops is *actually* the LLM doing LLM things.
The client side authentication of AI:
export const CYBER_RISK_INSTRUCTION = `IMPORTANT: Assist with authorized security testing, defensive security, CTF challenges, and educational contexts. Refuse requests for destructive techniques, DoS attacks, mass targeting, supply chain compromise, or detection evasion for malicious purposes. Dual-use security tools (C2 frameworks, credential testing, exploit development) require clear authorization context: pentesting engagements, CTF competitions, security research, or defensive use cases.`
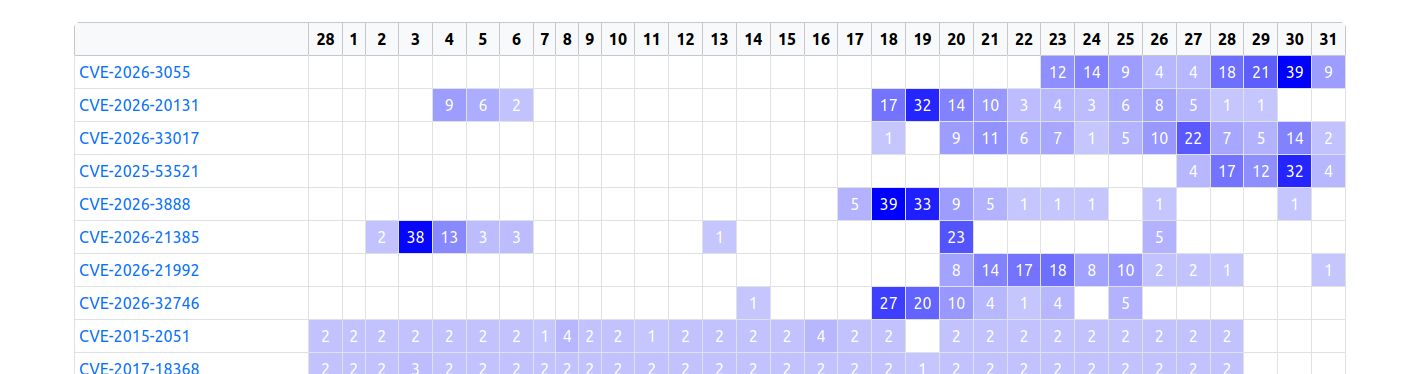
TrendAI Zero Day Initiative
thezdi@infosec.exchangeWe have adjusted the scoring on the advisory to reflect server-side mitigations that the vendor described during the disclosure process.
Binary Ninja
binaryninja@infosec.exchangeJoin @mr_phrazer with us on Thursday @4pm ET to pit machine versus machine!
We'll be comparing LLM options for both assisted and fully-automatic reverse engineering, including different CLI interfaces, MCP servers, plugins, and agents.
Get notified so you don't miss who comes out on top of reversing's biggest battle yet: https://www.youtube.com/live/TBqBpaqecMA
Anatoly Shashkin💾
dosnostalgic@mastodon.socialHey, look. It's a decent scan of this legendary image!
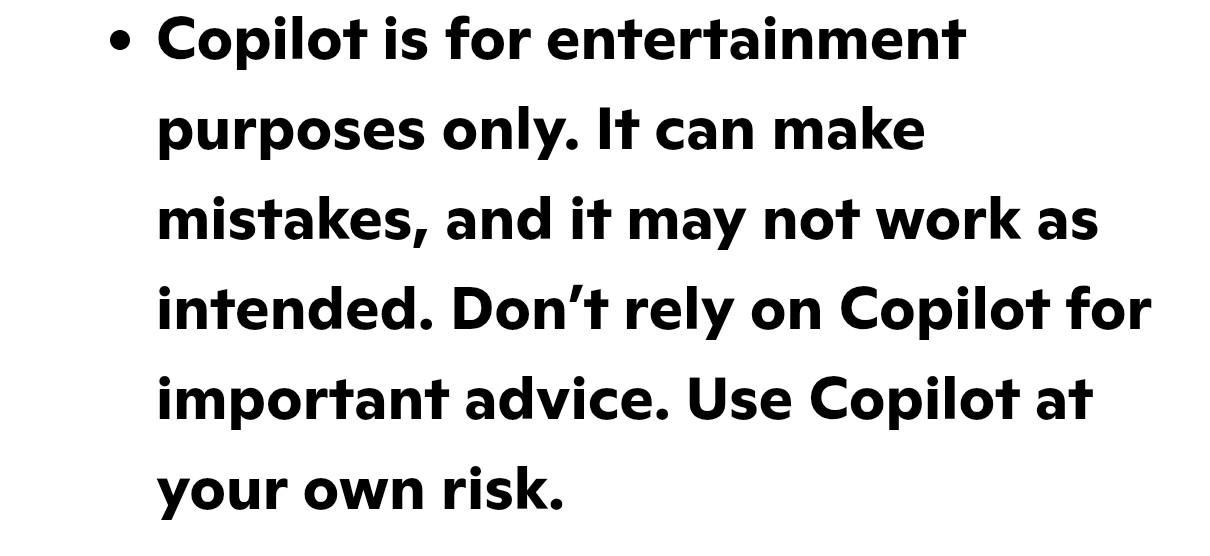
Clemens
clemens@mathstodon.xyzCan we print this part of Microsoft's T&S as a leaflet and distribute at our university?
https://www.microsoft.com/en-us/microsoft-copilot/for-individuals/termsofuse
Dr. Zalka Csenge Virág
TarkabarkaHolgy@ohai.socialHere we go!
The A to Z Challenge has begun. My theme this year is Small Town Legends: weird folklore from villages and small towns in and around Hungary.
First up: some very strange geese.
Ács: Zombie Goose Shenanigans https://share.google/Aa9plXTmBYbUrUPXM
#AtoZChallenge #SmallTownLegends #blogging #folklore #folktales #legends
alice pellerin
simonomi@mstdn.sociali don't see enough people with one of the best tool improvements i've ever made for reverse engineering, so i had to write a blog post about it!
0patch
0patch@infosec.exchangeMicropatches released for Windows Storage Elevation of Privilege Vulnerability (CVE-2026-21508)
https://blog.0patch.com/2026/03/micropatches-released-for-windows.html
Baldur Bjarnason
baldur@toot.cafeI keep coming back to the leaded petrol analogy for LLMs and coding
Harms that are manageable when it's only used by a small number of experts become catastrophic pollution when it's used broadly throughout society
If LLMs were only used by a small number of experienced devs working with well-engineered guardrails, we'd have less of a problem
But once they start getting more commonly used, they start to pollute the entire ecosystem and the only way forward is stiff regulation for everybody
Talos Vulnerability Reports
talosvulnsFoxit Reader List Box Calculate Array Use-After-Free Vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2365
CVE-2026-3779
MOGWAI LABS GmbH
mogwailabs_gmbh@infosec.exchangeNew security advisory in our bug parade: Unauthenticated Remote Code in dormakaba evolo Service.
.NET Remoting is still a thing...
Our colleague @mal had another look at OpenOLAT and found a nice RCE (CVE-2026-28228 and CVE-2026-28228). If you're interested, details can be found on our blog https://secfault-security.com/blog/openolat-ssti.html
Did anyone got that alleged Vim RCE PoC working? MacOS doesn't seem vulnerable, Ubuntu 22/24, Debian 13, the same... Advisory says <9.2.0272 but doesn't seem like it?
Smells like AI slop hype? Yeah, kinda because most distros don't seem to ship vim with +tabpanel feature. HYPEEEEEEEEEEEEEEEEE
⠠⠵ avuko
avuko@infosec.exchangeInstead of using an LLM to write me some boilerplate and basic functionality, frontend etc, why isn’t there a library where I can find all of these?
You know, something structured and shared, again, like a library, for specific purposes, and specific languages, with educational hints from development pros on the best way to do things and maybe some constructive feedback and improvements from other people?
And why were we left to deal with stackexchange instead?
Could this have been, dare I say it: gatekeeping?
Alexandre Dulaunoy
adulau@infosec.exchangeIf someone comes to me today preaching about “post-quantum” security issues, I’ll remind them of the current state of security: the npm ecosystem gets abused daily, CI pipelines run left and right with full access to cloud services, so-called security devices like F5 and Ivanti are exposed (and compromised) to the internet, mailboxes get compromised just to change an IBAN in a PDF, and a simple phone call is still enough to get someone to hand over an MFA code.
But yes, by all means, let’s focus on post-quantum threats while handing AI tools SSH access like it’s a feature, not a confession.