Posts
3908Following
728Followers
1600Did anyone got that alleged Vim RCE PoC working? MacOS doesn't seem vulnerable, Ubuntu 22/24, Debian 13, the same... Advisory says <9.2.0272 but doesn't seem like it?
Smells like AI slop hype? Yeah, kinda because most distros don't seem to ship vim with +tabpanel feature. HYPEEEEEEEEEEEEEEEEE
⠠⠵ avuko
avuko@infosec.exchangeInstead of using an LLM to write me some boilerplate and basic functionality, frontend etc, why isn’t there a library where I can find all of these?
You know, something structured and shared, again, like a library, for specific purposes, and specific languages, with educational hints from development pros on the best way to do things and maybe some constructive feedback and improvements from other people?
And why were we left to deal with stackexchange instead?
Could this have been, dare I say it: gatekeeping?
Alexandre Dulaunoy
adulau@infosec.exchangeIf someone comes to me today preaching about “post-quantum” security issues, I’ll remind them of the current state of security: the npm ecosystem gets abused daily, CI pipelines run left and right with full access to cloud services, so-called security devices like F5 and Ivanti are exposed (and compromised) to the internet, mailboxes get compromised just to change an IBAN in a PDF, and a simple phone call is still enough to get someone to hand over an MFA code.
But yes, by all means, let’s focus on post-quantum threats while handing AI tools SSH access like it’s a feature, not a confession.
Taggart 
mttaggart@infosec.exchange
This is a big deal. Already seeing evidence of this by way of OpenClaw installations.
buherator
buheratorHD Moore
hdm@infosec.exchangeTom Ptacek posted a great writeup titled "Vulnerability Research Is Cooked", covering the state of vulndev and its rapidly accelerating future:
https://sockpuppet.org/blog/2026/03/30/vulnerability-research-is-cooked/
buherator
buheratorhttps://martinvol.pe/blog/2026/03/30/how-the-ai-bubble-bursts/
raptor 
raptor@infosec.exchange
Anyone knows anything more about this #Tunnelblick #vulnerability?
"CVE-2026-31893 describes a serious Tunnelblick vulnerability.
This vulnerability is present in all versions of all Tunnelblick versions 3.3beta26 through 9.0beta01.
Tunnelblick 8.0.1 and 9.0beta02 contain fixes for the vulnerability.
The CVE is expected to be published and this page updated on or before 2026-03-27."
0patch
0patch@infosec.exchangeMicropatches released for Arbitrary Registry Key Delete As Local System With Consolidator Scheduled Task (CVE-2025-59512) https://blog.0patch.com/2026/03/micropatches-released-for-arbitrary.html
Frédéric Jacobs
fj@mastodon.socialRE: https://social.heise.de/@heiseonlineenglish/116316847500488516
“Oh, we murdered 100 kids? Oh, that's unfortunate.
We just had some stale data in our Palantir Project Maven data lake that was used by our ‘highly accelerated, software-supported targeting process’. We'll clear the cache sometimes.”
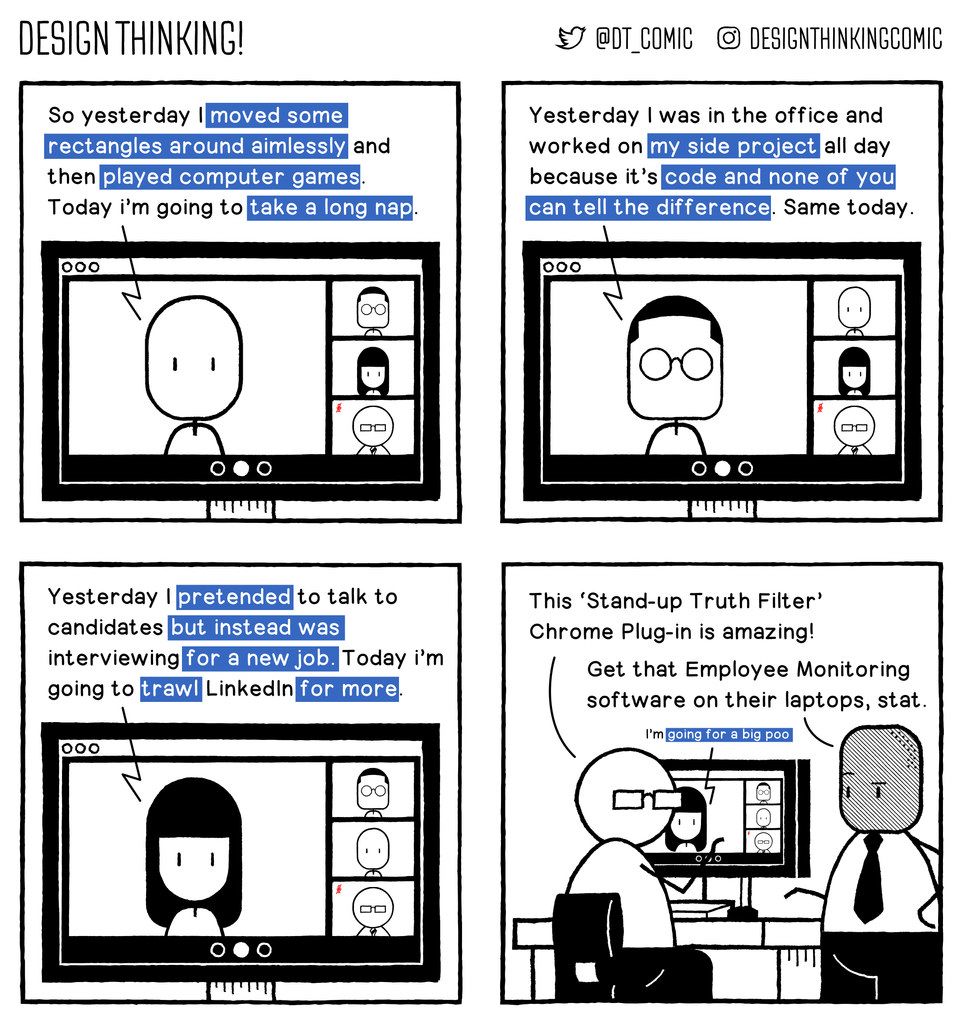
DT! Comic HAS MOVED
designthinkingcomic@mastodon.cloudHonesty is not policy.
#webcomics #comics
 radare
radare 
radareorg@infosec.exchange
“Reverse Engineering the ITE 8910 Keyboard RGB Protocol for OpenRGB” with #radare2 https://chocapikk.com/posts/2026/reverse-engineering-ite8910-keyboard-rgb/
buherator
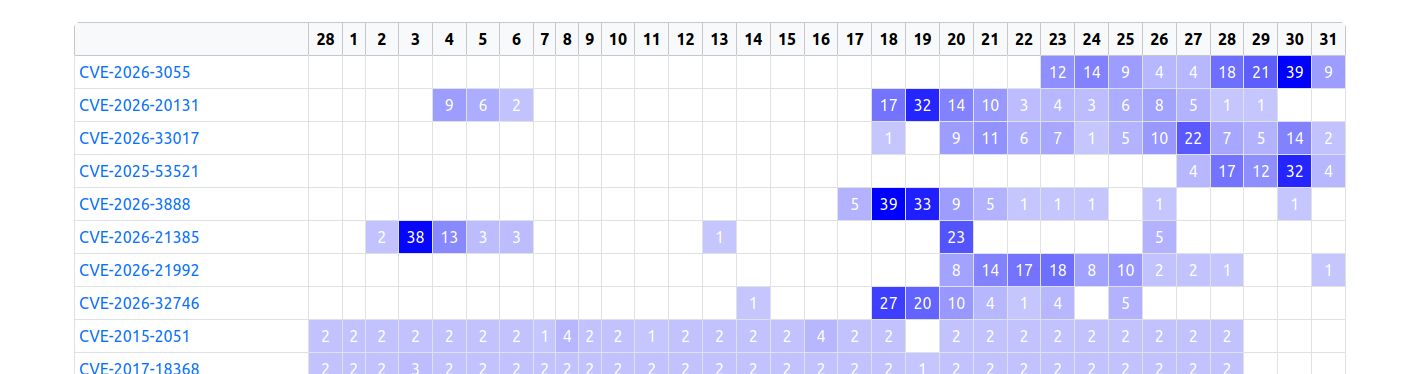
buheratorhttps://labs.watchtowr.com/please-we-beg-just-one-weekend-free-of-appliances-citrix-netscaler-cve-2026-3055-memory-overread-part-2/
dragosr
dragosr@chaos.socialA walkthrough on patching Dell UEFI firmware at the SPI flash level to disable pre-boot DMA protection — bypassing the BIOS password entirely. The interesting part: the UEFI UI still reports the setting as enabled, and TPM measured boot doesn't detect the NVRAM change, so BitLocker unlocks normally. The patch also persists through official Dell BIOS updates. From there it's DMAReaper to kill IOMMU + PCILeech for a SYSTEM shell. Significant measured boot policy gap. https://www.mdsec.co.uk/2026/03/disabling-security-features-in-a-locked-bios/
abadidea
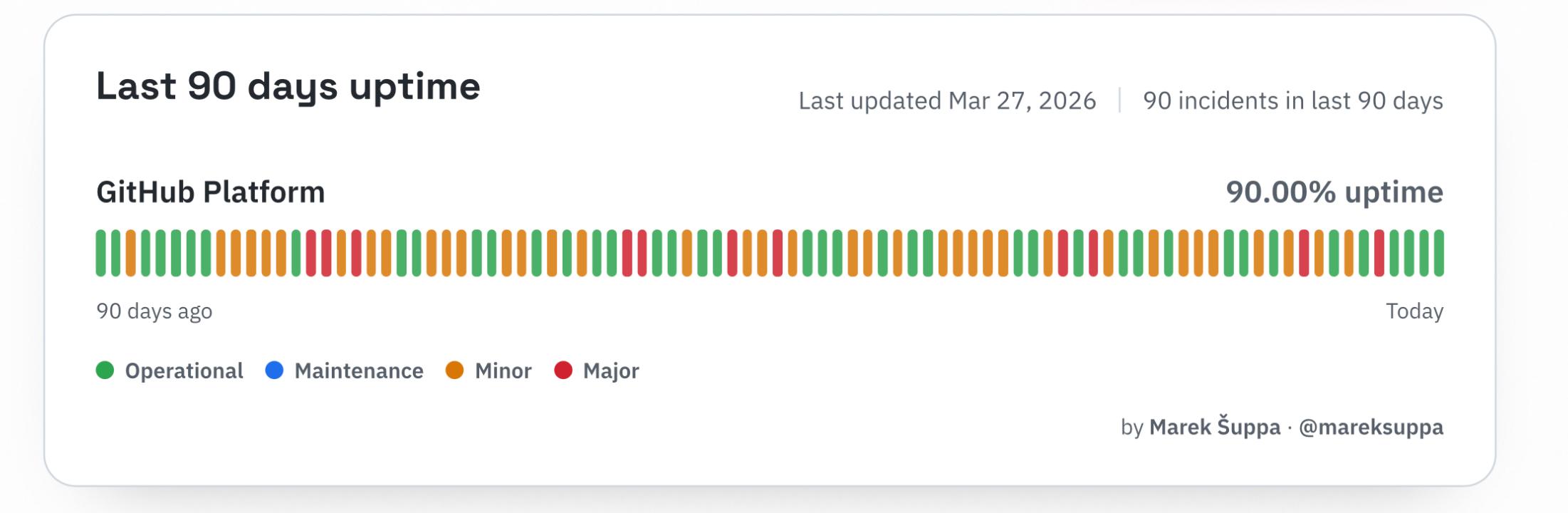
0xabad1dea@infosec.exchangeNINETY DAYS
NINETY INCIDENTS
NINETY PERCENT
YOU PAID FOR ALL FIVE NINES BUT YOU’LL ONLY NEED THE EDGE
Brian Greenberg 
brian_greenberg@infosec.exchange
I teach cybersecurity. And I genuinely don't know what to tell my students after this one. Federal reviewers spent years trying to get basic encryption documentation from Microsoft for its GCC High government cloud. They couldn't get it. One reviewer called the system a "pile of spaghetti pies," with data traveling from point A to point B the way you'd get from Chicago to New York: a bus to St. Louis, a ferry to Pittsburgh, and a flight to Newark. Each leg is a potential hijacking. They knew this. They said this out loud in writing. Then they approved it anyway in December 2024, because too many agencies were already using it. 🔐 That's not a security review. That's a hostage negotiation. Two things in this story should make every CISO and CIO uncomfortable:
🧩 Microsoft built its federal cloud on top of decades of legacy code that it apparently can't fully document itself
👮 "Digital escorts" often ex-military with minimal software engineering backgrounds are the firewall between Chinese engineers working on the system and classified U.S. networks 🤦🏻♂️
The scariest line in the whole ProPublica investigation isn't the "pile of shit" quote. It's this: FedRAMP determined that refusing authorization wasn't feasible because agencies were already using the product. Read that again. The security review process reached a conclusion based on sunk cost, not risk. Ex Post Facto Fallacy
If that logic holds, the compliance framework is just documentation theater. And right now, CISA is being hollowed out, so there are fewer people left to even run the theater.
https://arstechnica.com/information-technology/2026/03/federal-cyber-experts-called-microsofts-cloud-a-pile-of-shit-approved-it-anyway/
#Cybersecurity #Microsoft #FedRAMP #Leadership #RiskManagement #security #privacy #cloud #infosec
Ken Shirriff
kenshirriff@oldbytes.spaceIn 1967, IBM introduced the System/4 Pi line of aerospace computers, packing mainframe performance into a compact box. 4 Pi computers powered everything from military aircraft to the Space Shuttle to sonar systems on submarines. Thread...