Posts
3865Following
725Followers
1594buherator
buherator#Citrix should do CTF challenges instead of security appliances, really.
https://labs.watchtowr.com/the-sequels-are-never-as-good-but-were-still-in-pain-citrix-netscaler-cve-2026-3055-memory-overread/
/r/netsec
_r_netsec@infosec.exchangeThe Sequels Are Never As Good, But We're Still In Pain (Citrix NetScaler CVE-2026-3055 Memory Overread) - watchTowr Labs https://labs.watchtowr.com/the-sequels-are-never-as-good-but-were-still-in-pain-citrix-netscaler-cve-2026-3055-memory-overread/
watchTowr
watchTowr@infosec.exchangewhile we’re eating our best writing crayons and using finger paint to finish our latest research, we’ve decided to take this opportunity to share research from the archives with new followers 🙂
happy Friday… for now 🥹
https://labs.watchtowr.com/we-spent-20-to-achieve-rce-and-accidentally-became-the-admins-of-mobi/
(Yes this is not new don’t @ us)
buherator
buheratorhttps://qriousec.github.io/post/cve-2025-14325/
Simple Sabotage Field Manual
simple_sabotage@mastodon.socialCry and sob hysterically at every occasion, especially when confronted by government clerks.
buherator
buheratorhttps://blog.talosintelligence.com/tp-link-canva-hikvision-vulnerabilities/
buherator
buheratorEinstein obviously didn't have to work with LLMs
Caitlin Condon
catc0n@bird.makeupA hefty root cause analysis of #Cisco Secure Firewall Management Center (FMC) RCE CVE-2026-20079 out now from our exploit dev team. The bug's a CVSS 10, but there are significant prerequisites for exploitation that limit real-world exploitability https://www.vulncheck.com/blog/cisco-fmc-auth-bypass-cve-2026-20079
hanno
hanno@mastodon.socialAI, a few thoughts, observations about AI & security vulns.
My standard line about AI is "there's a lot I'm uncertain about". But let's be clear, there's a lot I don't like & I'm probably biased towards the "here's how spectacularly AI failed once again" news (of which there are plenty) or at least the "it's not as impressive as it may look".
Yet, I don't want to close my eyes if I see things that clearly don't fit my biases. And I know a thing or two about security vulnerabilities.🧵
buherator
buheratorhttps://addons.mozilla.org/en-US/firefox/addon/sidebery/
Right click on tab -> Configure site
Ian Campbell 🏴
neurovagrant@masto.deoan.orgUS or EU, Remote - Wiz - Threat Intelligence Researcher (Cloud)
Wiz has been doing some great work around TeamPCP lately, among other things.
According to LinkedIn ( https://www.linkedin.com/posts/benjamin-read-41817121_im-continuing-to-build-the-threat-intel-share-7442969734645608448-Gu-n?utm_source=share&utm_medium=member_desktop&rcm=ACoAABIZhqYBjXCQuV7JX7N_3xlpxZY6alHZ77o ) it's posted for US but open to EU. They're looking for two roles, one Cyber Crime and one Cyber Espionage.
(I am not affiliated with Wiz or at all involved in this hiring process.)
https://www.wiz.io/careers/job/4658917006/threat-intelligence-researcher-cloud
Fi 🏳️⚧️
munin@infosec.exchangeyou know
multiple people now have said that the thing they like about LLMs is that they don't have to deal with feeling embarrassed or humiliated by bringing questions to others that the others will judge them for.
which like
y'all.
this is a classic "solving a people problem with tech and having horrible side effects as a result" situation
and perhaps y'all ought to be less fucking toxic and judgemental to your coworkers.
fuck.
Rust Language
rust@social.rust-lang.orgRust 1.94.1 has been released.
This point release fixes a few regressions that slipped into in Rust 1.94.0: an internal compiler error in Clippy, a small security issue in Cargo, and two issues in the standard library.
See the blog post for details: https://blog.rust-lang.org/2026/03/26/1.94.1-release/
buherator
buheratorAny recommendations?
V4bel
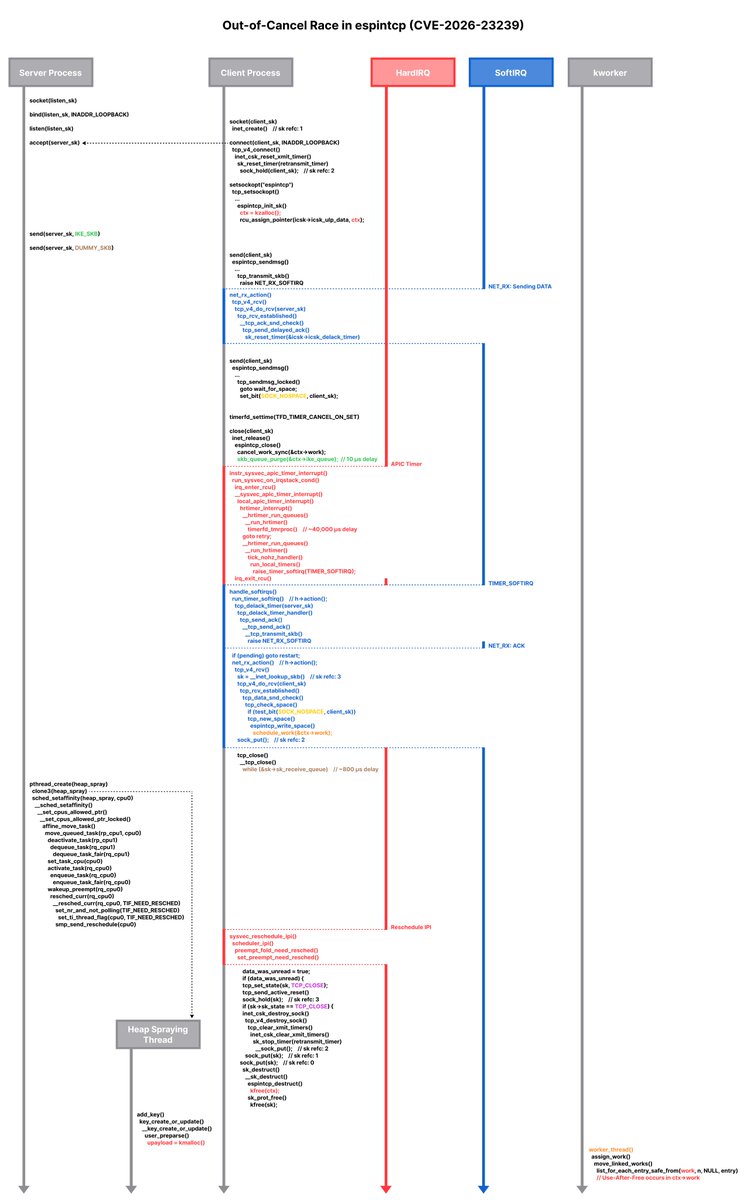
v4bel@bird.makeupI discovered a race-based vulnerability class in the Linux kernel: "Out-of-Cancel"
A structural flaw where cancel_work_sync() is used as a barrier for object lifetime management, causing UAF across multiple networking subsystems.
I wrote an exploit for CVE-2026-23239 (espintcp). It interleaves Delayed ACK timers, NET_RX softirqs, timerfd hardirqs, workqueue scheduling, and CFS scheduler manipulation to hit a ~Xµs race window.
Blog: https://v4bel.github.io/linux/2026/03/23/ooc.html
This is the race scenario diagram 😁:
Lorenzo Franceschi-Bicchierai
lorenzofb@infosec.exchangeNEW: Here's everything you need to know about the new iPhone hacking tool DarkSword.
What is DarkSword? How does it work? Where did it come from? How did it leak online? What can you do about it?
We break it all down in this explainer.
David Gerard
davidgerard@circumstances.runVibe Security Radar: Real CVEs where AI-generated code introduced the vulnerability.
https://vibe-radar-ten.vercel.app/
EDIT: forget that, it's slop:
> If the primary model fails, a Claude Agent SDK fallback with independent repository access retries the investigation.
sigh