Posts
3718Following
724Followers
1598Jerry 🦙💝🦙
jerry@infosec.exchangeHas anyone ever heard of a security breach of a Fedramp moderate or higher authorized environment? I mean the parts that are authorized.
buherator
buheratorShow content
https://soundcloud.com/township-rebellion/township-rebellion-fab-massimo?in=township-rebellion%2Fsets%2Freleases
Tormod
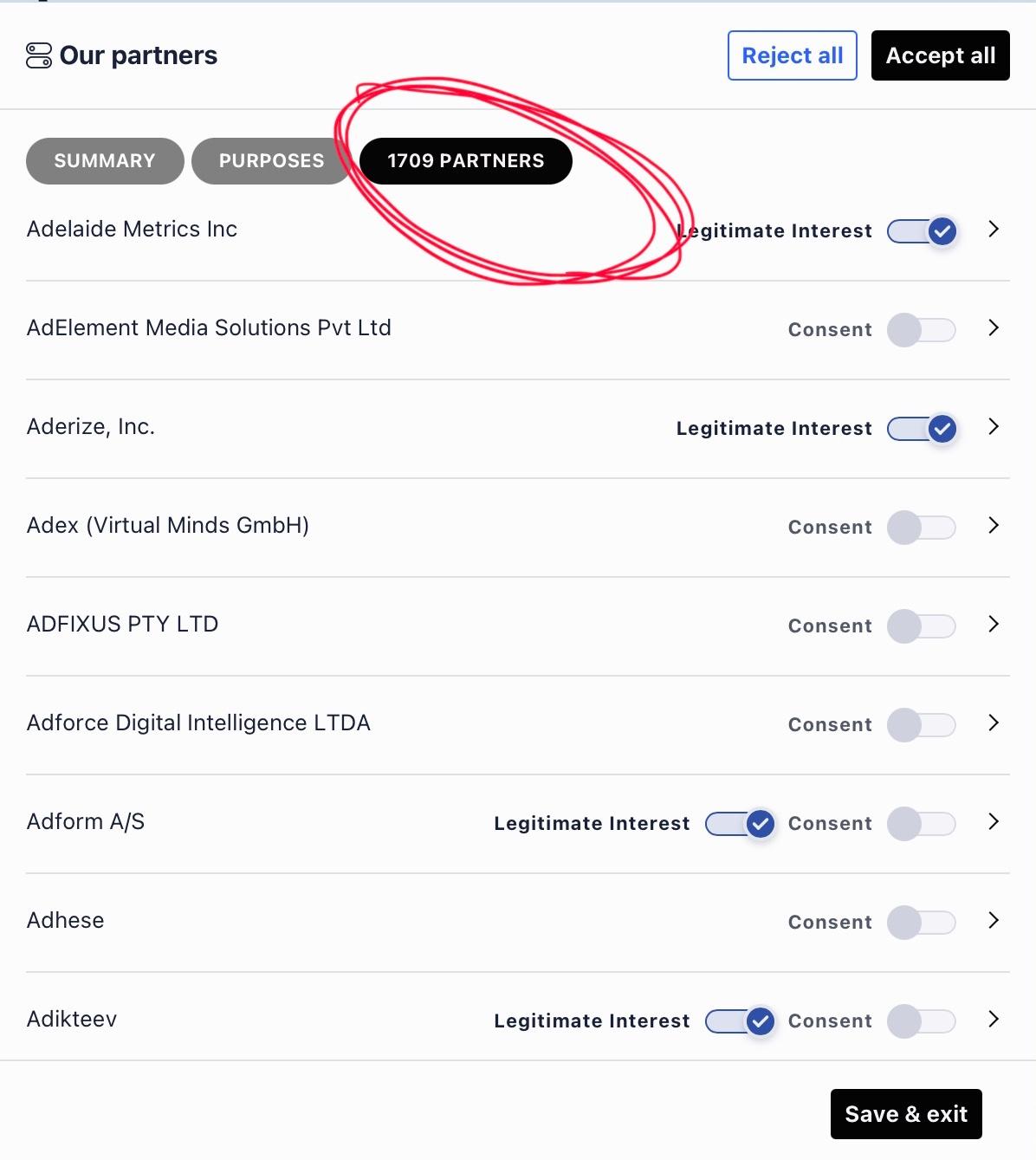
airwhale@beige.partyDoes anyone know where to find more info on the surveilance economy online? I was looking for an update on the unfortunate Debora Silvestri who crashed so badly yesterday, and of course, was met with "We value your privacy" banner where I could consent to giving away… something?
The Privacy Policy talks about two cookies - both Google Analytics, and two partners for gaining "audience insights". The actual cookie pop-up list 1.709 (!) so-called "partners", many with "legitimate interest". Basically all these are companies nobody has ever heard of.
I know I'm leaking info like IP-address, browser and device details. What I can't understand is how all these 1.709 little leeches can possibly deliver enough value and generate revenue based on this information. Who pays them, and for what?
Thanks!
Haroon Meer
haroonmeer@infosec.exchangeWe’ve always had a problem with least privilege, but users needed to be owned for it to visibly hurt the enterprise.
Kevin didn’t know what to do with the extra creds, but his agent will.
Maybe the first run of the “paperclip” problem will be agents wiping shares to save us..
Siguza
siguza@infosec.spaceOkay these "Background Security Improvements" are definitely worse than RSRs. They show up at random times in your Settings app, and if you tap anywhere else, they disappear immediately. You can find them again, but they're not under Software Updates where they should be, but under Privacy & Security > Background Security Improvements, which also does not seem to show up in search.
EDIT: HOLY SHIT I have to enable "Automatically Install" in order to even be allowed to download them MANUALLY?! And there's no progress indicator either?? Whoever approved this should be hurled into the sea.
buherator
buheratorhttps://sigma-star.at/blog/2025/12/unix-v4-buffer-overflow/
Exploit su on a PDP-11 :)
tmpout
tmpout@haunted.computer🚨 We are extending the deadline for our Volume 5 Call For Papers and its Rootkit Competition!
Check out the updated dates below:
→ https://tmpout.sh/blog/vol5-cfp.html (until May 1st 2026)
→ https://tmpout.sh/blog/vol5-rootkit-competition.html (until May 31st 2026)
We are looking forward to reading your work!
Battle Programmer Yuu
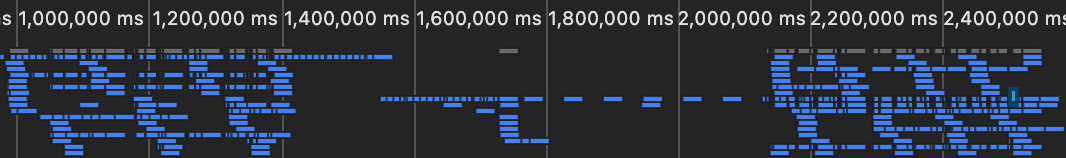
netspooky@haunted.computerWhenever I use Chrome to debug a modern website, it's so funny to see all the requests usually blocked by my normal setup. It's like watching a fish being released back into the sea, swimming happily, gobbling up all the data and sending telemetry out to the other fish.
buherator
buherator"You will see us be more intentional about how and where Copilot integrates across Windows [...] we are reducing unnecessary Copilot entry points, starting with apps like Snipping Tool, Photos, Widgets and Notepad"
buherator
buheratorhttps://archive.ph/f8zdV
buherator
buheratorhttps://simonw.substack.com/p/thoughts-on-openai-acquiring-astral
buherator
buheratorThen I usually decide that "it's fine, this is not a spaceship" and forget to implement the exit path.
quarkslab
quarkslab@infosec.exchange"Intego X9: Never trust my updates"
Read @coiffeur0x90's research showing how XPC interprocess communications and the update mechanism of the Intego antivirus for MacOS can be abused for local privilege escalation.
Mr. Bitterness
wdormann@infosec.exchangeCall me crazy, but there are times when I think that ChatGPT sprinkling in knowledge about what I normally ask is... not useful.
This is from a question I asked about grease.
buherator
buheratorR.I.P.
Dr. Christopher Kunz
christopherkunz@chaos.socialCVE-2026-20963 Sharepoint Insecure Deserialization 8.8/10
Weekend soon. Where @watchTowr blog? Need lolz. I can has?
buherator
buheratorDebugging worked out-of-the-box, I only had some trouble figuring out that LSP is not available until I mark the remote project as Trusted too.
a very strange trackball
algernon@come-from.mad-scientist.clubToday is #iocaine 3.3.0 release day.
I'd like if it included a Grafana dashboard for the built-in script. But I'm yet to build one. It's very similar in shape to NSoE's, mind you... but I'd still need to do some work on it.
I've been postponing this since forever. But this is likely going to be the last 3.x release, I really, really should.
I'll go grind some spoons1, and see if I can manage.
Well, hello there The Pitt S02E11! ↩︎
Lur Noise
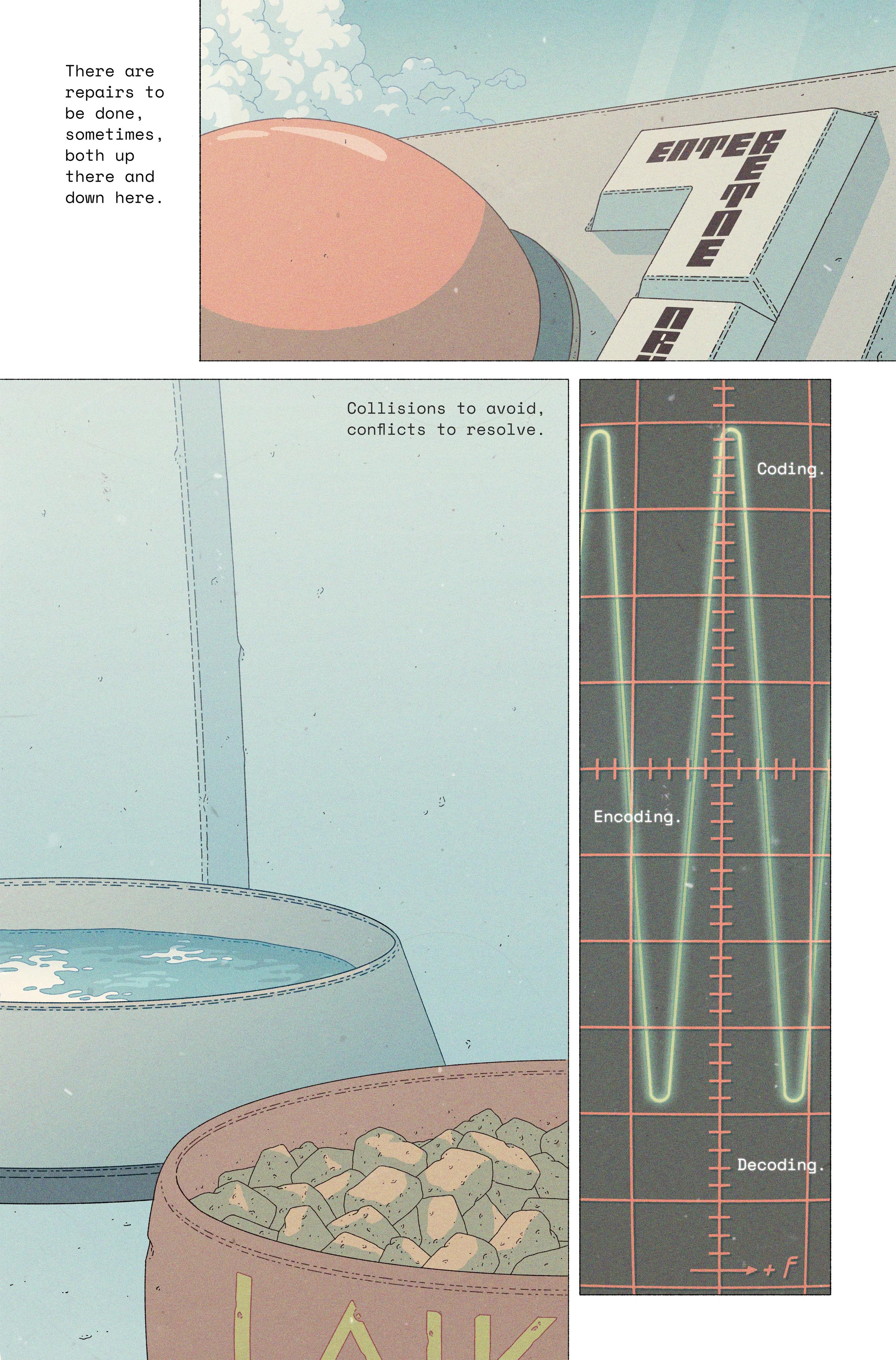
lurnoise@mastodon.art"There are repairs to be done, sometimes, both up there and down here."
A new page of my comic Ekphrasis, which you can read for free at https://ekphrasiscomic.neocities.org/