Posts
3719Following
724Followers
1598buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20220426-00/?p=106528
#IBM #dresscode
daniel:// stenberg://
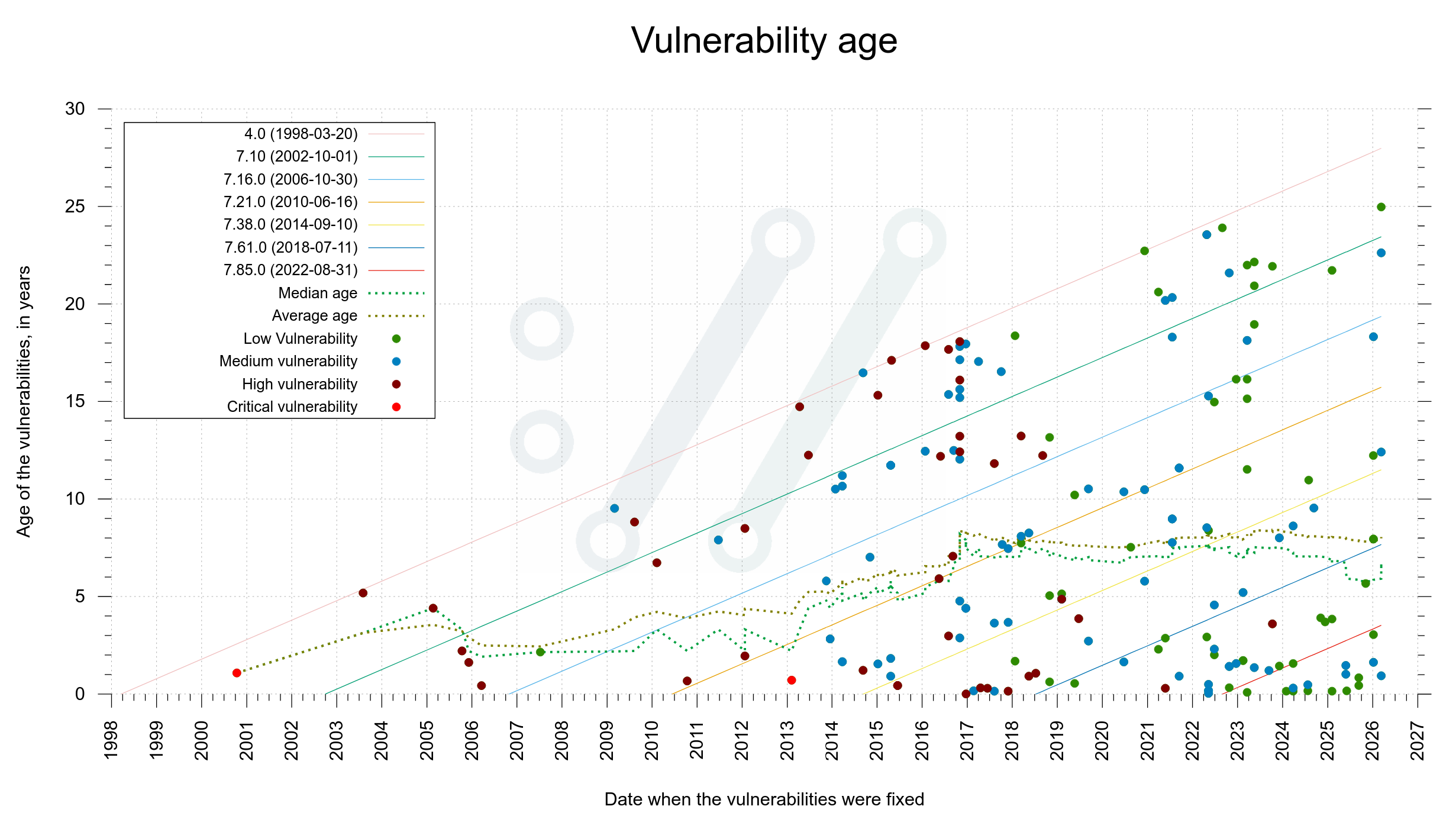
bagder@mastodon.socialCVE-2026-3784 beat a new #curl record. This flaw existed in curl source code for 24.97 years before it was discovered.
Illustrated in the slightly hard-to-read graph below. The average age of a curl vulnerability when reported is eight years.
David Chisnall (*Now with 50% more sarcasm!*)
david_chisnall@infosec.exchangeMe? Trolling the other microcontroller vendors? Surely not! Maybe if they had bothered to do something about the most common source of vulnerabilities at some point in the last few decades, the could have been on the other side of the sign...
Tony “Abolish ICE” Arcieri🌹🦀
bascule@mas.toRIP Tony Hoare. His obituaries are talking about quicksort, but I think his most notable accomplishments are Communicating Sequential Processes, the Occam programming language, and the Transputer, an early example of a parallel processor
https://blog.computationalcomplexity.org/2026/03/tony-hoare-1934-2026.html?m=1
buherator
buheratorhttp://blog.quarkslab.com/pagejack-in-action-cve-2022-0995-exploit.html
buherator
buheratorhttps://talosintelligence.com/vulnerability_reports/TALOS-2025-2293
second hand mouse
algernon@come-from.mad-scientist.club5,200 holes carved into a Peruvian mountain left by an ancient economy
Has anyone tried to feed it into a PDP11 as a punch card yet? If I found anything old with holes in it, I would definitely see if it is a FORTRAN program.
Lorenzo Franceschi-Bicchierai
lorenzofb@infosec.exchangeNEW: A hacker broke into a server at the Child Exploitation Forensic Lab in the FBI’s New York Field Office and compromised files related to the Epstein investigation, as first reported by Reuters.
“Following the 2023 cyber incident, the FBI contained the affected network and determined the incident to be an isolated one. The FBI restricted access to the malicious actor and rectified the network,” an FBI spokesperson said.
https://techcrunch.com/2026/03/11/hacker-broke-into-fbi-and-compromised-epstein-files-report-says/
Longhorn
never_released@mastodon.socialRE: https://ec.social-network.europa.eu/@EUCommission/116211334179600320
this is a meme and not in the good meaning of the word
even less than GAIA-X, just rofl :/
Lorenzo Franceschi-Bicchierai
lorenzofb@infosec.exchangeSCOOP: The iPhone mass hacking toolkit used by Russian spies was developed at U.S. military contractor L3Harris, former employees said.
The Coruna toolkit was used against Ukrainians during the war and by Chinese cybercriminals, according to Google.
But the toolkit was initially developed for governments in the Five Eyes spy alliance, and it was used in Operation Triangulation, according to one source.
buherator
buheratortihmstar
tihmstar@infosec.exchangeReleased a tool to erase X-Gold 608 (06.15.00 iPad) baseband.
https://github.com/tihmstar/bberase_ultrasn0w
This is useful if you want to downgrade your iPhone 3G to iOS 2.0 with the matching baseband.
The exploit/payload was taken from redsn0w and some code from xerub. There isn't really anything novel here, but until now there wasn't a straightforward way to erase the baseband or to downgrade to iOS 2.0 baseband on the iPhone 3G.
Lenovo released all patches for the Vantage vulnerabilities I reported earlier this year. The blog has been updated with write‑ups for CVE-2025-13154, CVE-2026-1715, CVE-2026-1716, and CVE-2026-1717.
buherator
buheratorhttps://geohot.github.io//blog/jekyll/update/2026/03/11/running-69-agents.html
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchange🚨 New advisory was just published!
A critical vulnerability in UNISOC modem firmware allows one User Equipment (UE) to remotely attack another over the cellular network. By sending specially crafted malformed SDP within SIP signaling messages, an attacker can trigger memory corruption in the target modem, potentially leading to remote execution of arbitrary native code on the victim device: https://ssd-disclosure.com/unisoc-t612-rce/
Ivan Ožić Bebek
obivan@infosec.exchangeCVE-2026-26117: Hijacking Azure Arc on Windows for Local Privilege Escalation & Cloud Identity Takeover https://cymulate.com/blog/cve-2026-26117-azure-arc-windows-lpe-cloud-identity-takeover/
buherator
buheratorhttps://xclow3n.github.io/post/6