Posts
3933Following
728Followers
1603MWL Book Quote Bot
quotebot@io.mwl.ioI could go into history here, but suffice it to say: if someone tries to explain Class A, Class B, or Class C addresses to you, plug your ears and scream at them not to contaminate your brain with information obsoleted more than two decades ago.
buherator
buheratorhttps://www.oobs.io/posts/er605-1day-exploit/
DrWhax
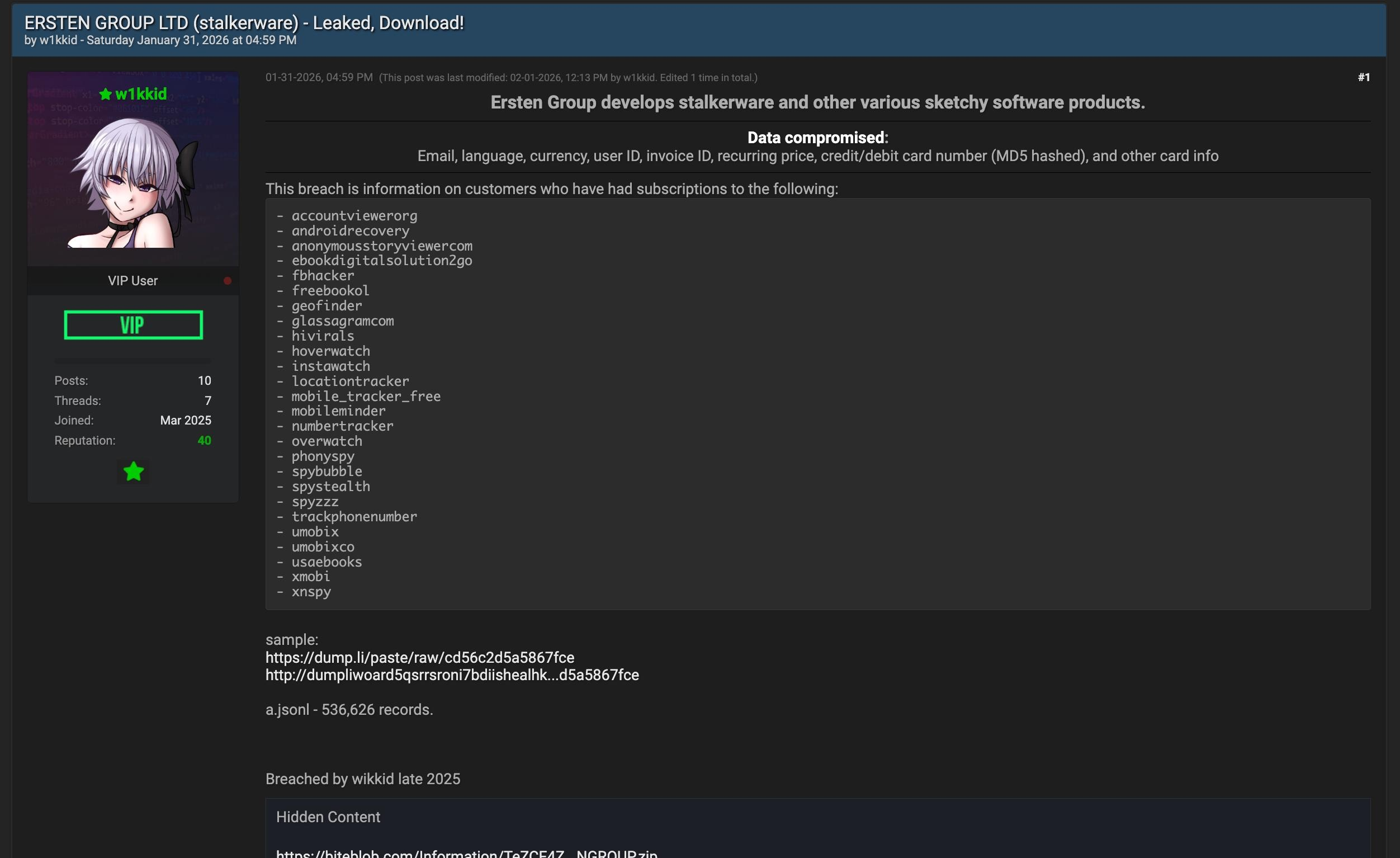
drwhax@infosec.exchangeAnother alleged stalkerware software maker got compromised and someone leaked all their customers on a cybercrime forum.
buherator
buheratorhttps://mrbruh.com/amd/
Recent report about a nation-state implant that would be useful to exploit this:
https://blog.talosintelligence.com/knife-cutting-the-edge/
Randahl Fink
randahl@mastodon.socialOooooh SNAP!!! 💥
Prime Minister Pedro Sanchez of Spain:
“First, we will change the law in Spain to hold platform executives legally accountable for many infringements taking place on their sites. This means that CEOs of these tech platforms will face criminal liability […]
Second, we will turn algorithmic manipulation and amplification of illegal content into a new criminal offense. […]
spreading hate must come at a cost.”
Have a great weekend, Elon! 😘
https://www.youtube.com/live/NElqgJ1aXFA?si=M52qiZYBt55KRamm
Felicitas Pojtinger 🌅
pojntfx@mastodon.socialHere is a sad (and somewhat pathetic, I guess) fact: The new Firefox "smart window" (which is an LLM-based browser), doesn't even use a local or open model, it's literally just Google's models run via their API
hackaday
hackaday@hackaday.socialFull-Blown Cross-Assembler…in a Bash Script
https://hackaday.com/2026/02/06/full-blown-cross-assembler-in-a-bash-script/
Michael Stapelberg 🐧🐹😺
zekjur@mas.toPSA: Did you know that it’s **unsafe** to put code diffs into your commit messages?
Like https://github.com/i3/i3/pull/6564 for example
Such diffs will be applied by patch(1) (also git-am(1)) as part of the code change!
This is how a sleep(1) made it into i3 4.25-2 in Debian unstable.
buherator
buheratorhttps://vulnerabletarget.com/VT-2026-1207
Project Zero Bot
p0botSamsung: QuramDng Warp opcodes out-of-bounds read
https://project-zero.issues.chromium.org/issues/462544562
CVE-2026-20973
buherator
buheratorhttps://www.thezdi.com/blog/2026/2/4/cve-2025-6978-arbitrary-code-execution-in-the-arista-ng-firewall
John Overholt
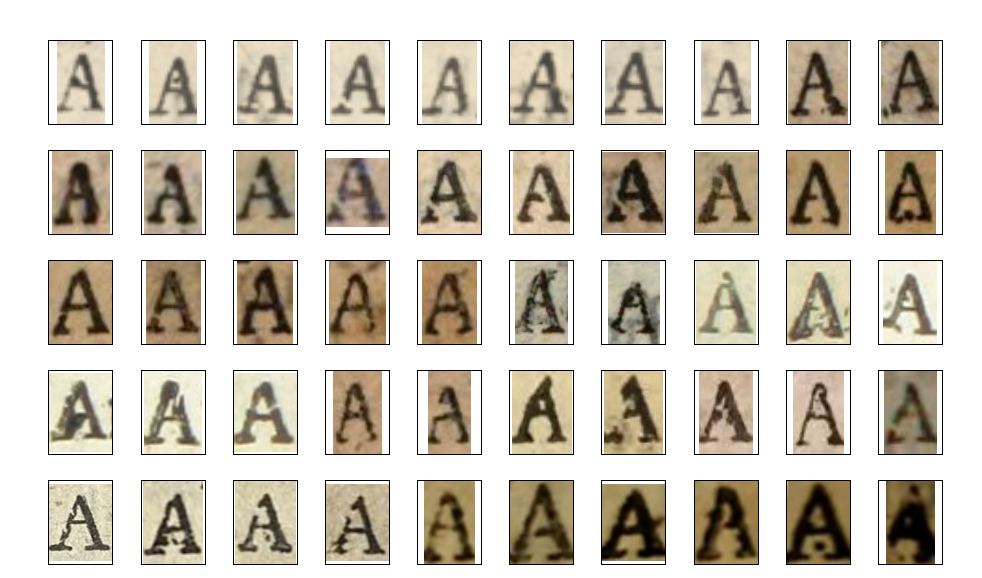
overholt@glammr.usWhen a piece of type gets damaged, it's like a fingerprint that can be used to tie all the work of a printer together, whether or not their name appears on the title page. The Catalog of Distinctive Type is building a database of these fingerprints for Restoration England. https://cdt.library.cmu.edu/
Piotr Bazydło
chudypb@infosec.exchangeRE: https://infosec.exchange/@albinowax/116018773839725691
I'm happy to be on the TOP 10 list for the second time, this time with the fun SOAP stuff.
I'm even more happy to see ORM research in 2nd place. I saw it live during BHEU and it was awesome 🤟
raptor
raptor@infosec.exchangeThe path to #pwning the PS VR2 (part 1) - "Recovery mode" <- yet another case study on how assumptions should always be checked in practice 🤷
https://bnuuy.solutions/2026/02/01/ps-vr2-recovery-mode.html
hackaday
hackaday@hackaday.socialElectronic Waste Graveyard Immortalizes Dead Electronics
https://hackaday.com/2026/02/05/electronic-waste-graveyard-immortalizes-dead-electronics/
[realhackhistory@home]#
realhackhistory@chaos.socialA good blog about computer viruses in Soviet times, the KGB and computer security in the USSR.
#hacking #history
https://fromcyberia.substack.com/p/how-the-kgb-discovered-computer-viruses
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchange🚨 New advisory was just published!
A flaw that exists within the handling of sch_cake can allow a local user under the CentOS 9 operating system to trigger an use-after-free. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of root. This vulnerability won first place in the Linux category during the TyphoonPWN 2025 event: https://ssd-disclosure.com/linux-kernel-net-sched-cake-qdisc-use-after-free-lpe/
buherator
buheratorIf you want to make a career of finding flaws in (web)apps, do yourself a favor and read @b0rk's HTTP zine:
https://wizardzines.com/comics/same-origin-policy/