Posts
3756Following
723Followers
1596Project Zero Bot
p0botSamsung: QuramDng Warp opcodes out-of-bounds read
https://project-zero.issues.chromium.org/issues/462544562
CVE-2026-20973
buherator
buheratorhttps://www.thezdi.com/blog/2026/2/4/cve-2025-6978-arbitrary-code-execution-in-the-arista-ng-firewall
John Overholt
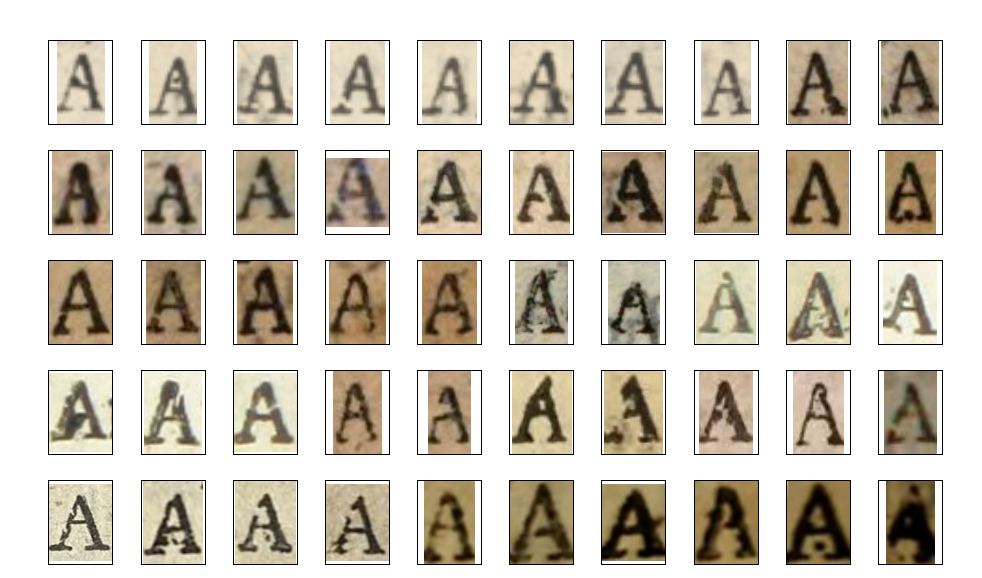
overholt@glammr.usWhen a piece of type gets damaged, it's like a fingerprint that can be used to tie all the work of a printer together, whether or not their name appears on the title page. The Catalog of Distinctive Type is building a database of these fingerprints for Restoration England. https://cdt.library.cmu.edu/
Piotr Bazydło
chudypb@infosec.exchangeRE: https://infosec.exchange/@albinowax/116018773839725691
I'm happy to be on the TOP 10 list for the second time, this time with the fun SOAP stuff.
I'm even more happy to see ORM research in 2nd place. I saw it live during BHEU and it was awesome 🤟
raptor 
raptor@infosec.exchange
The path to #pwning the PS VR2 (part 1) - "Recovery mode" <- yet another case study on how assumptions should always be checked in practice 🤷
https://bnuuy.solutions/2026/02/01/ps-vr2-recovery-mode.html
hackaday
hackaday@hackaday.socialElectronic Waste Graveyard Immortalizes Dead Electronics
https://hackaday.com/2026/02/05/electronic-waste-graveyard-immortalizes-dead-electronics/
[realhackhistory@home]#
realhackhistory@chaos.socialA good blog about computer viruses in Soviet times, the KGB and computer security in the USSR.
#hacking #history
https://fromcyberia.substack.com/p/how-the-kgb-discovered-computer-viruses
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchange🚨 New advisory was just published!
A flaw that exists within the handling of sch_cake can allow a local user under the CentOS 9 operating system to trigger an use-after-free. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of root. This vulnerability won first place in the Linux category during the TyphoonPWN 2025 event: https://ssd-disclosure.com/linux-kernel-net-sched-cake-qdisc-use-after-free-lpe/
buherator
buheratorIf you want to make a career of finding flaws in (web)apps, do yourself a favor and read @b0rk's HTTP zine:
https://wizardzines.com/comics/same-origin-policy/
raptor 
raptor@infosec.exchange
While waiting for the upcoming release of #IDAPro 9.3 by @HexRaysSA, I have made some updates and bug fixes to my idalib-based headless IDA #plugins rhabdomancer, haruspex, and augur.
Check out the changelogs for all the details and enjoy!
blacktop
blacktop@mastodon.socialHigh level diff of iOS 26.3 beta3 vs. iOS 26.3 RC 🎉
https://github.com/blacktop/ipsw-diffs/blob/main/26_3_23D5114d__vs_26_3_23D125/README.md
buherator
buheratorhttps://github.com/microsoft/terminal/issues/4750
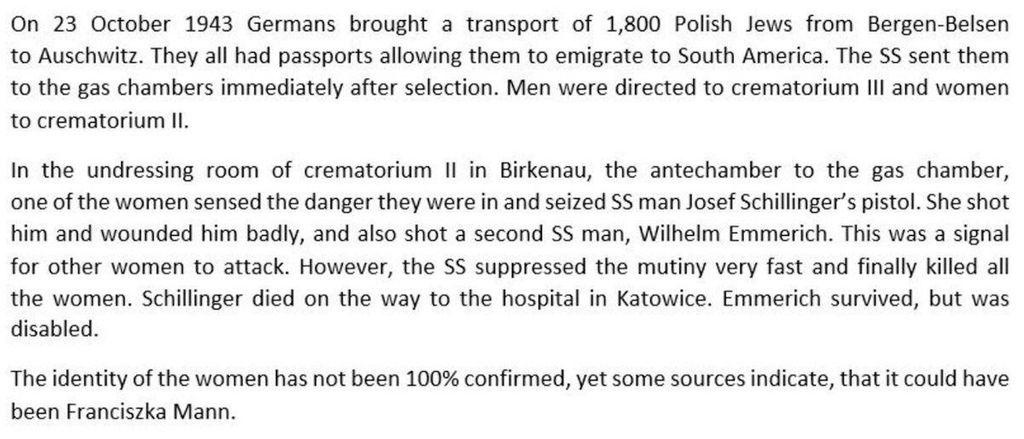
Auschwitz Memorial
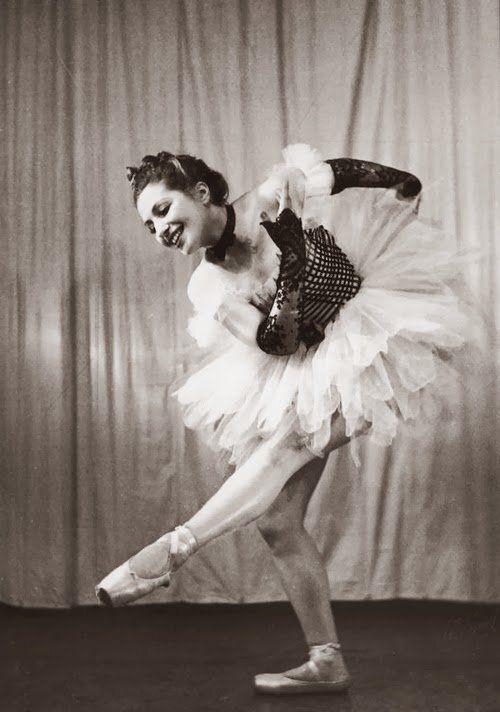
auschwitzmuseum@mastodon.world4 February 1917 | A Polish Jewish dancer Franciszka Mann was born. She was most probably the woman who on 23 October 1943, inside the undressing room of gas chamber II at Auschwitz II-Birkenau, seized SS man Josef Schillinger’s pistol, shot him & wounded SS man Wilhelm Emmerich.
---
A podcast about this and other cases of resistance at Auschwitz: https://www.auschwitz.org/en/education/e-learning/podcast/different-cases-of-organized-resistance-at-auschwitz/
daniel:// stenberg://
bagder@mastodon.socialSwitching away from Hackerone is not a guarantee... Here we go.
buherator
buheratorhttps://blog.0patch.com/2026/02/micropatches-released-for-microsoft.html
clearbluejar
clearbluejar@infosec.exchangePatch diffing + RCA for clfs.sys can take awhile.
I gave the diff + binary to a local LLM.
It mapped the UAF path, race condition, all IOCTLs in <20 min
LLMs don't replace the work, they are momentum.
New blog post following the UAF trail of CVE-2025-29824:
https://clearbluejar.github.io/posts/how-llms-feed-your-re-habit-following-the-uaf-trail-in-clfs/