Posts
3887Following
728Followers
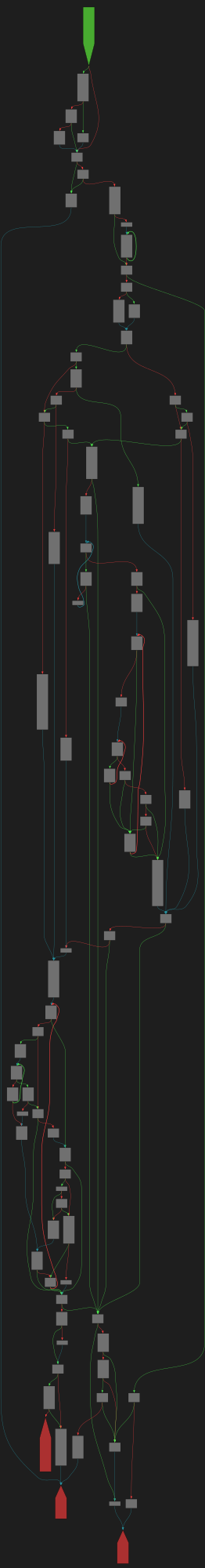
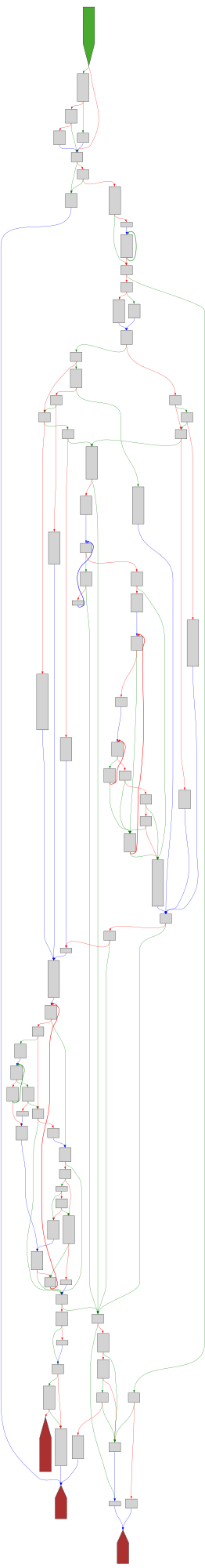
1600CFG Bot 🤖
cfgbot@mastodon.socialProject: openssl-static-gcc-dwarf 3.4.0
File: openssl
Address: 00867b00
____strtol_l_internal
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00867b00.json&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00867b00.json&colors=light
Ron Bowes
iagox86@infosec.exchangeRE: https://infosec.exchange/@BleepingComputer/115367382398075001
Another one??
daniel:// stenberg://
bagder@mastodon.socialA new breed of analyzers.
And they use AI.
https://daniel.haxx.se/blog/2025/10/10/a-new-breed-of-analyzers/
Frida
fridadotre@fosstodon.orgFrida 17.4 introduces Simmy, a new backend for Apple’s Simulators on macOS.
Spawn, attach, and instrument apps — just like on a real device. #ios #reverseengineering
daniel:// stenberg://
bagder@mastodon.socialIf you're curious, here are 158 of Joshua's reported issues on #curl to give you an idea what we talk about.
We have manually gone trough them all and dismissed or addressed them. None of them has been deemed a security problem. Not all the PRs for the valid problems have been merged yet.
https://gist.github.com/bagder/d1fff7f0471fbbe71354048a282e098e
Saar Amar
amarsaar@infosec.exchangeIt took four years, but now there is spec for lock files https://snarky.ca/why-it-took-4-years-to-get-a-lock-files-specification/
buherator
buheratorhttps://github.com/LvStrnggg/zkm-flow
buherator
buheratorhttps://spaceraccoon.dev/nokia-beacon-router-uart-command-injection/
postcardware.net
postcardware@cyber.msSent from Los Gatos, California, U.S.A. on July 16, 1995. https://postcardware.net/?id=36-67
The Hacker‘s Choice
thc@infosec.exchangeINTERVIEW of "MB" WhereWarlocksStayUpLate:
https://wherewarlocksstayuplate.com/interview/mohammed-bagha/
You have inspired many. We are fans:⚡️🌊🎠
https://wherewarlocksstayuplate.com/interview/mohammed-bagha/
Learn Turbo Pascal - a video series originally released on VHS
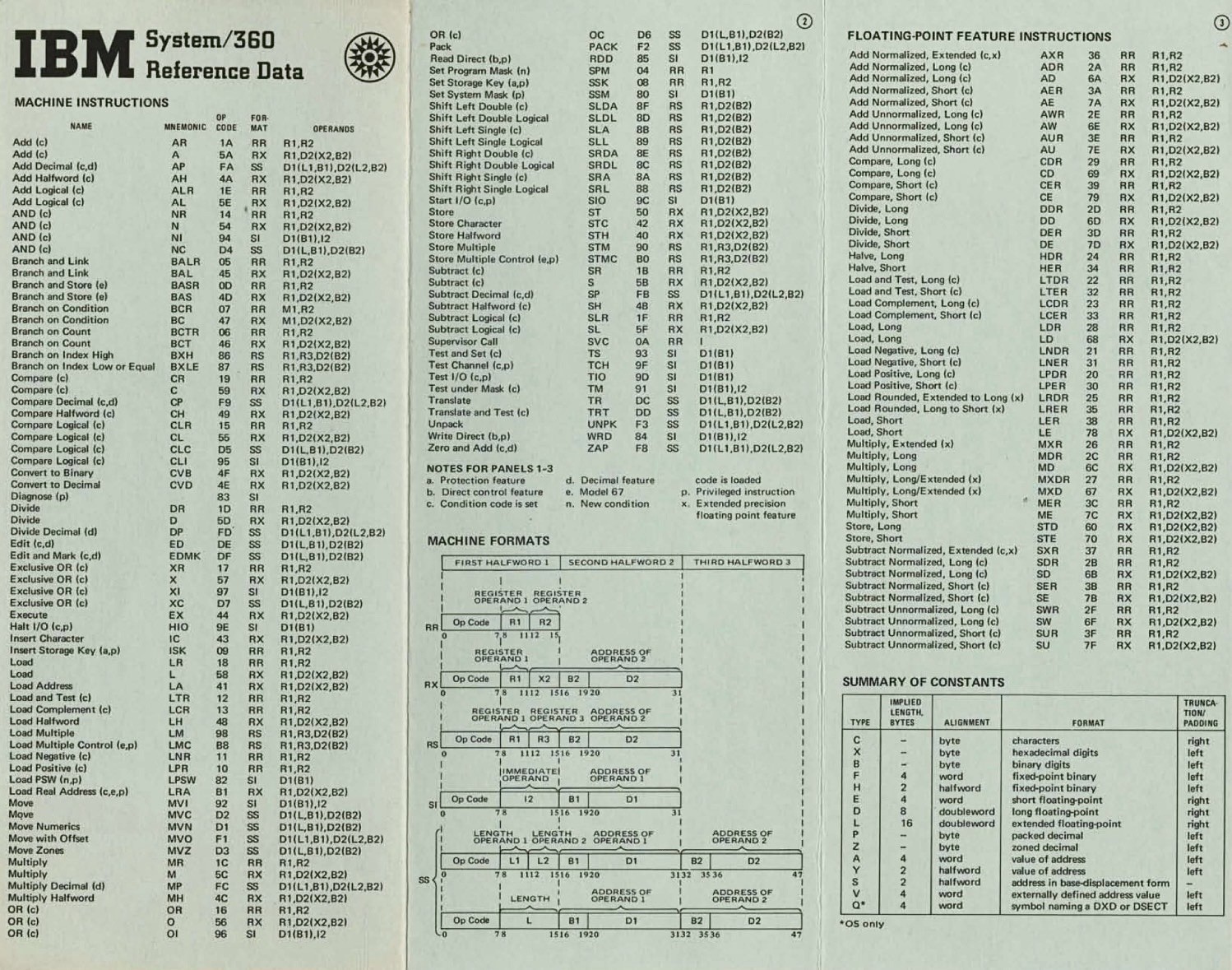
pancake 
pancake@infosec.exchange
The IBM System/360 machine instructions reference card #s360 #assembly #mainframe https://archive.computerhistory.org/resources/access/text/2010/05/102678081-05-01-acc.pdf
Where Homes Get Weird
weirdestate@eigenmagic.netYes we are all normal here in HUMANSVILLE. We are all HUMANS of course. No need to check.
kriware 
kriware@infosec.exchange
The Debugging Book
Interactive guide exploring automated debugging, testing, and program repair with Python examples for researchers and developers.
Piotr Bazydło
chudypb@infosec.exchangeFun times with Telerik UI and DoS by default (it will hit for a long time I think). Sometimes it may lead to more fun, like RCE :)
Gadgeting inspired by @pwntester Oleksandr and @stevenseeley
Blog:
buherator
buheratorhttps://momo5502.com/posts/2025-10-03-reverse-engineering-denuvo-in-hogwarts-legacy/
buherator
buheratorhttps://labs.infoguard.ch/posts/attacking_edr_part5_vulnerabilities_in_defender_for_endpoint_communication/
buherator
buheratorAny recommendations?
"You know, I couldn't do it. I couldn't reduce it to the freshman level. That means we really don't understand it." - Richard Feynman
hanno
hanno@mastodon.socialDear Infosec people who have looked at XML and XXE before: I am trying to get an understanding of Blind XXE.
Many of the descriptions I find are lacking an important detail which makes the attack much less practical. Blind XXE works by building an URL which contains content of a file, allowing to exfiltrate content. However, in all my tests, that *only* works if the file contains no newlines, as those are not allowed in URLs. Am I missing something?
🧵
Cure53🔓
cure53@infosec.exchangeDOMPurify 3.3.0 will soon be released, with this likely being the most important change in a long time: