Posts
3906Following
728Followers
1600
Jeff Hall - PCIGuru 
jbhall56@infosec.exchange
Markus Vervier 👾
marver@mastodon.socialHere's the full writeup of CVE-2025-53773 - Visual Studio & Copilot – Wormable Command Execution via Prompt Injection: https://www.persistent-security.net/post/part-iii-vscode-copilot-wormable-command-execution-via-prompt-injection
Patch now!
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@eupolicy.socialI had a great time at the most excellent #why2025 camp! Here a write-up of my own #DNA talks (with links to video & annotated slides), some observations on the tremendously terrible state of security & regulation, and what we could do about it, plus some nice photos!
https://berthub.eu/articles/posts/dna-talks-and-why2025/
buherator
buheratorShow content
https://amylandthesniffers.bandcamp.com/
buherator
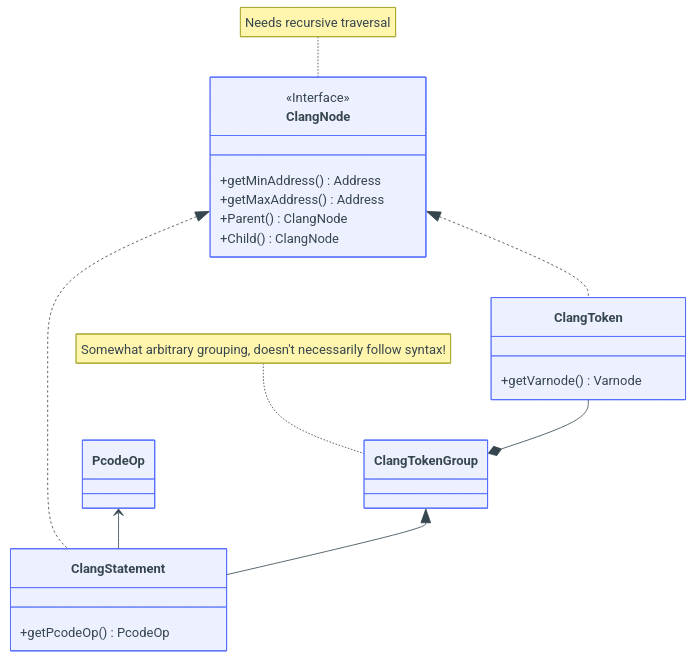
buheratorhttps://scrapco.de/ghidra-cheat-sheet/
PR's and suggestions are most welcome!
buherator
buheratorRE: https://chaos.social/@weirdunits/115020402704312177
buherator
buheratorhttps://seclists.org/fulldisclosure/2025/Aug/3
"PlayReady Activation service does not implement real authentication, but
some form of obfuscated identification scheme [...] Arbitrary PlayReady identity can be requested by the client through public API" and more...
Viss
Viss@mastodon.socialthis is uh.
something.
perplexity is offering twice its valuation to buy chrome off google?
strong "run the fuck away" vibes
https://arstechnica.com/gadgets/2025/08/perplexity-offers-more-than-twice-its-total-valuation-to-buy-chrome-from-google/
Richard Johnson
richinseattle@bird.makeupProud moment. The 40th anniversary @phrack release was a full success. We gave away 12,000 full color 150pg printed zines for free across three different conferences and did the final main stage talk before closing. l covered the history of phrack and did some panel questions.
/r/netsec
_r_netsec@infosec.exchangeFortMajeure: Authentication Bypass in FortiWeb (CVE-2025-52970) https://pwner.gg/blog/2025-08-13-fortiweb-cve-2025-52970
Julia Evans
b0rk@jvns.cahas anyone ever made a man page viewer which shows you a table of contents for the man page so you can easily navigate through the sections?
(please do not tell me about `info`)
CISA KEV Tracker
cisakevtracker@mastodon.socialCVE ID: CVE-2025-8088
Vendor: RARLAB
Product: WinRAR
Date Added: 2025-08-12
Notes: https://www.win-rar.com/singlenewsview.html?&L=0&tx_ttnews%5Btt_news%5D=283&cHash=a64b4a8f662d3639dec8d65f47bc93c5 ; https://nvd.nist.gov/vuln/detail/CVE-2025-8088
CVE URL: https://nvd.nist.gov/vuln/detail/CVE-2025-8088
TrendAI Zero Day Initiative
thezdi@infosec.exchangeWe've managed to make it through hacker summer camp, and #Microsoft and #Adobe survived enough to deliver their latest security patches. Join @TheDustinChilds as he breaks down another large Patch Tuesday release. https://www.zerodayinitiative.com/blog/2025/8/12/the-august-2025-security-update-review
Lorenzo Franceschi-Bicchierai
lorenzofb@infosec.exchangeNEW: Two hackers broke into the computer of a hacker allegedly working for the North Korean spy group known as "Kimsuky."
The hackers then leaked a treasure trove of stolen data, exposing a North Korean spy operation against South Korean targets.
“Kimsuky, you’re not a hacker. You are driven by financial greed, to enrich your leaders, and to fulfill their political agenda. You steal from others and favour your own. You value yourself above the others: You are morally perverted,” the two wrote in their Phrack magazine article. “You hack for all the wrong reasons.”
https://techcrunch.com/2025/08/12/hackers-breach-and-expose-a-major-north-korean-spying-operation/
RE//verse Conference
REverseConf@infosec.exchangeJust under three weeks until CFP opens for RE//verse 2026! Submissions open September 1st: https://sessionize.com/reverse-2026
And while you’re at it, snag your ticket early before prices go up: https://shop.binary.ninja/collections/re-verse-admissions-requires-sales-tax/products/re-verse-2026-admission
buherator
buherator(now that file is a sacred artifact that must be protected by all costs)