Posts
3165Following
706Followers
1560Baldur Bjarnason
baldur@toot.cafeTrusting your own judgement on 'AI' is a huge risk: https://www.baldurbjarnason.com/2025/trusting-your-own-judgement-on-ai/
buherator
buheratorI'm only thinking about basic Git commands for linear version tracking, he'll learn about branching and merging as he gains some experience.
#parenting
Ned Batchelder
nedbat@hachyderm.io39 years ago today....
https://nedbatchelder.com/blog/202506/digital_equipment_corporation_no_more.html
buherator
buheratorbuherator
buheratorhttps://www.joindns4.eu/for-public#resolver-options
buherator
buheratorhttps://medium.com/@cy1337/spotting-cve-2025-23016-with-ghidra-533a084dac42
Allele Security Intelligence
alleleintel@infosec.exchangeWe wrote a blog post about a Linux kernel vulnerability we reported to Red Hat in July 2024. The vulnerability had been fixed upstream a year before, but Red Hat and derivatives distributions didn't backport the patch. It was assigned the CVE-2023-52922 after we reported it.
The vulnerability is a use-after-free read. We could abuse it to leak the encoded freelist pointer of an object. This allows an attacker to craft an encoded freelist pointer that decodes to an arbitrary address.
It also allows an attacker to leak the addresses of objects from the kernel heap, defeating physmap/heap address randomization.These primitives facilitate exploitation of the system by providing the attacker with useful primitives.
Additionally, we highlighted a typical pattern in the subsystem, as two similar vulnerabilities had been discovered. However, before publishing the blog post, we noticed that the patch for this vulnerability doesn't fix it. We could still trigger the use-after-free issue.
This finding confirms the point raised by the blog post. Furthermore, we discovered another vulnerability in the subsystem. An out-of-bounds read. We've reported them, and these two new vulnerabilities were already patched. A new blog post about them will be written.
Use-after-free vulnerability in CAN BCM subsystem leading to information disclosure (CVE-2023-52922)
Programming Quotes
programming_quotes@mastodon.socialA human being should be able to change a diaper, plan an invasion, butcher a hog, conn a ship, design a building, write a sonnet, balance accounts, build a wall, set a bone, comfort the dying, take orders, give orders, cooperate, act alone, solve equations, analyze a new problem, pitch manure, program a computer, cook a tasty meal, fight efficiently, die gallantly. Specialization is for insects.
— Robert A. Heinlein
eShard
eshard@infosec.exchangeWinDBG vs esReverse: same concept (time travel debugging), very different scope.
We break down the differences in our blog: https://eshard.com/posts/difference-between-windbg-and-esreverse
buherator
buheratorhttps://aoli.al/blogs/jdk-bug/
CFG Bot 🤖
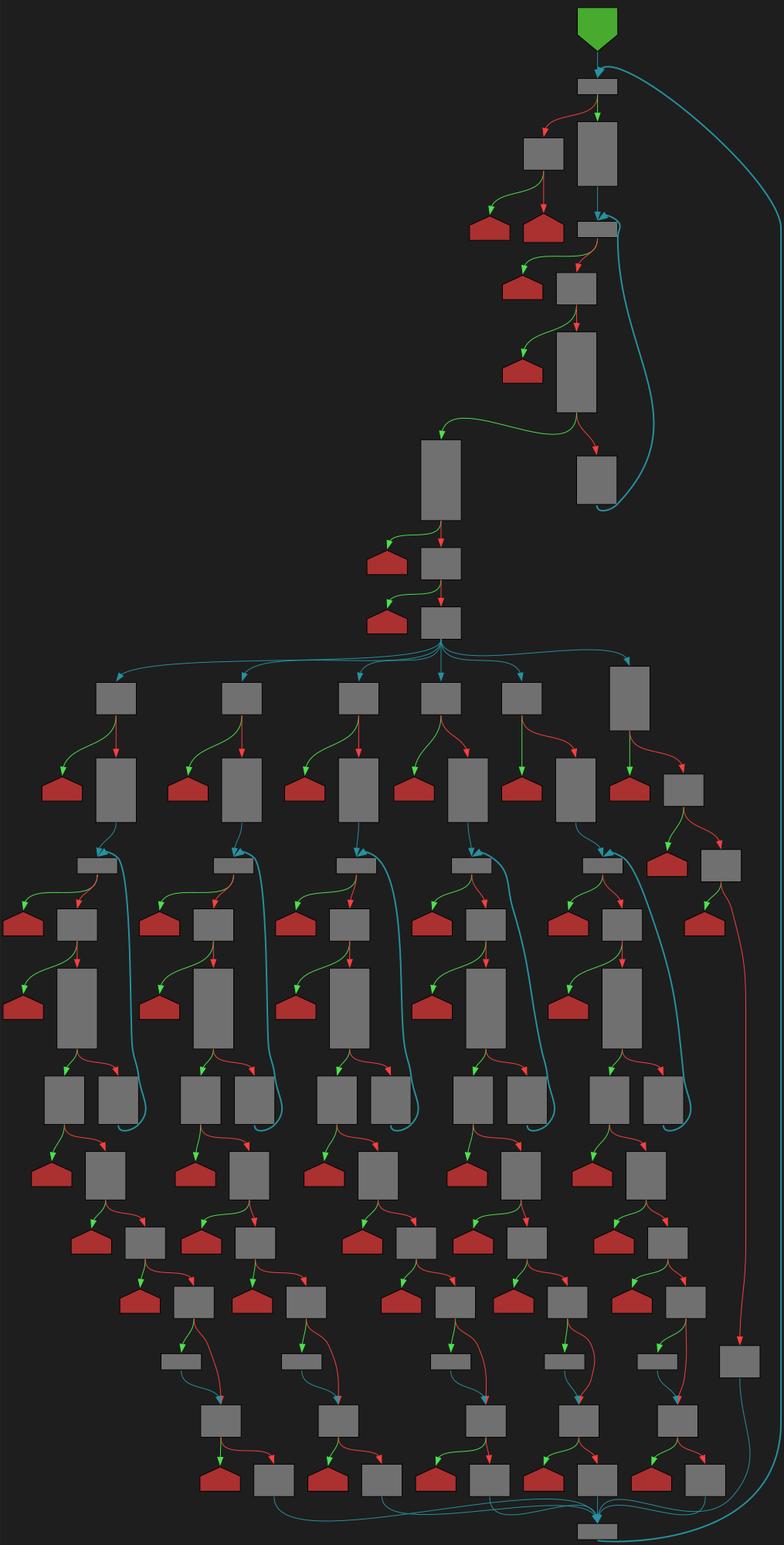
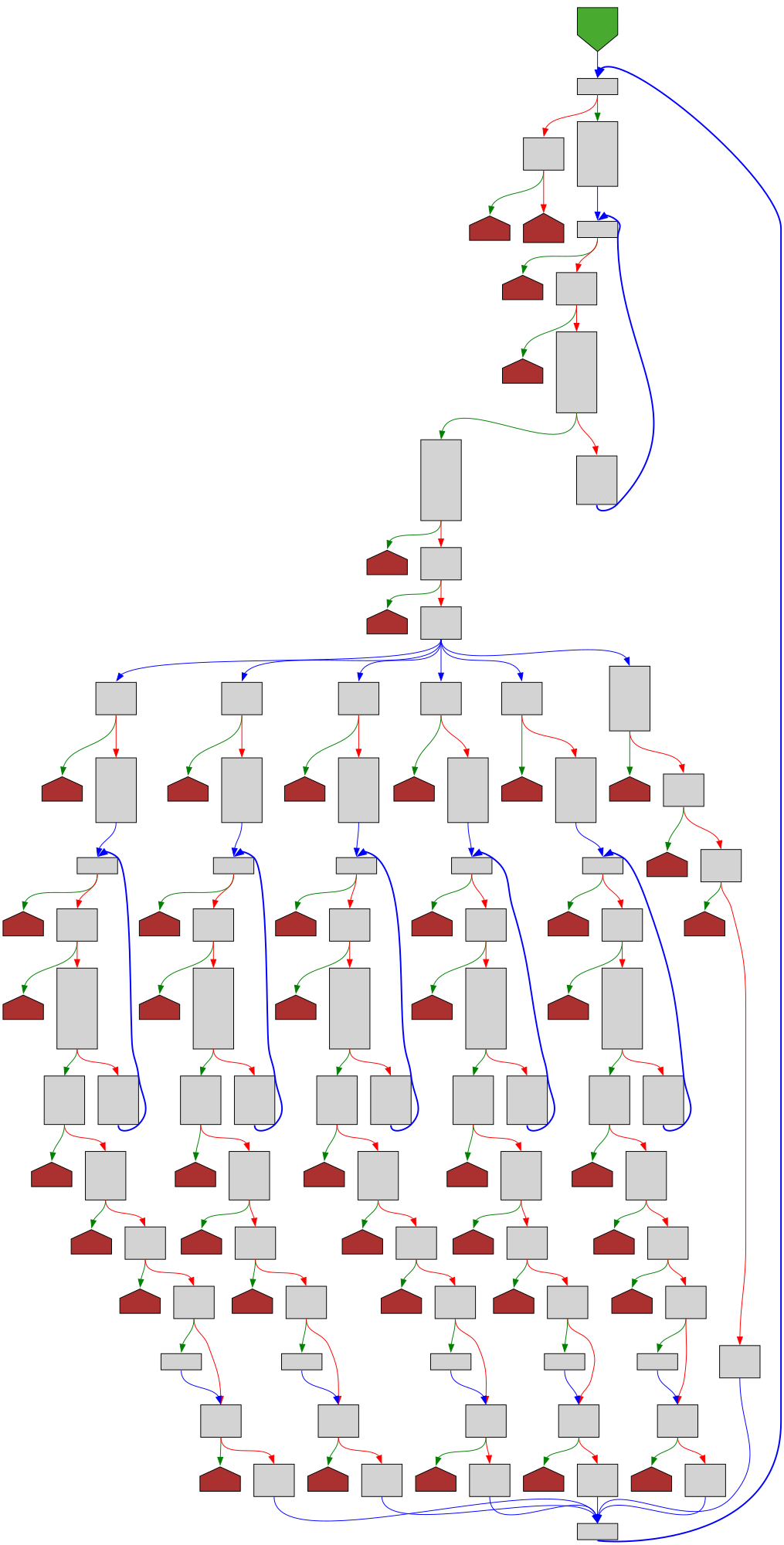
cfgbot@mastodon.socialProject: kubernetes/kubernetes https://github.com/kubernetes/kubernetes
File: staging/src/k8s.io/api/core/v1/generated.pb.go:72936 https://github.com/kubernetes/kubernetes/blob/a62752db5110225a89a83ec844a5884413e550ff/staging/src/k8s.io/api/core/v1/generated.pb.go#L72936
func (m *VolumeProjection) Unmarshal(dAtA []byte) error
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fkubernetes%2Fkubernetes%2Fblob%2Fa62752db5110225a89a83ec844a5884413e550ff%2Fstaging%2Fsrc%2Fk8s.io%2Fapi%2Fcore%2Fv1%2Fgenerated.pb.go%23L72936&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fkubernetes%2Fkubernetes%2Fblob%2Fa62752db5110225a89a83ec844a5884413e550ff%2Fstaging%2Fsrc%2Fk8s.io%2Fapi%2Fcore%2Fv1%2Fgenerated.pb.go%23L72936&colors=light
buherator
buheratorhttps://xania.org/202506/how-compiler-explorer-works
#fromBsky
Simple Sabotage Field Manual
simple_sabotage@mastodon.socialWhen you go to the lavatory, spend a longer time there than is necessary.
Łukasz 
maldr0id@infosec.exchange
Communist Poland was exceptionally good at making fun of secret police and egomaniacal leaders.
If my American friends need some good authoritarian jokes so that they can keep their spirits up for the long run I can suggest some!
hanno
hanno@mastodon.socialIn case anyone here has connections with the Python team: can you please tell them to update their docs on XML security? The way it is is quite misleading, and it's been annoying me for a while. I raised this a while ago in their issue tracker, but it got no reaction whatsoever. https://github.com/python/cpython/issues/127502 🧵