Posts
3915Following
728Followers
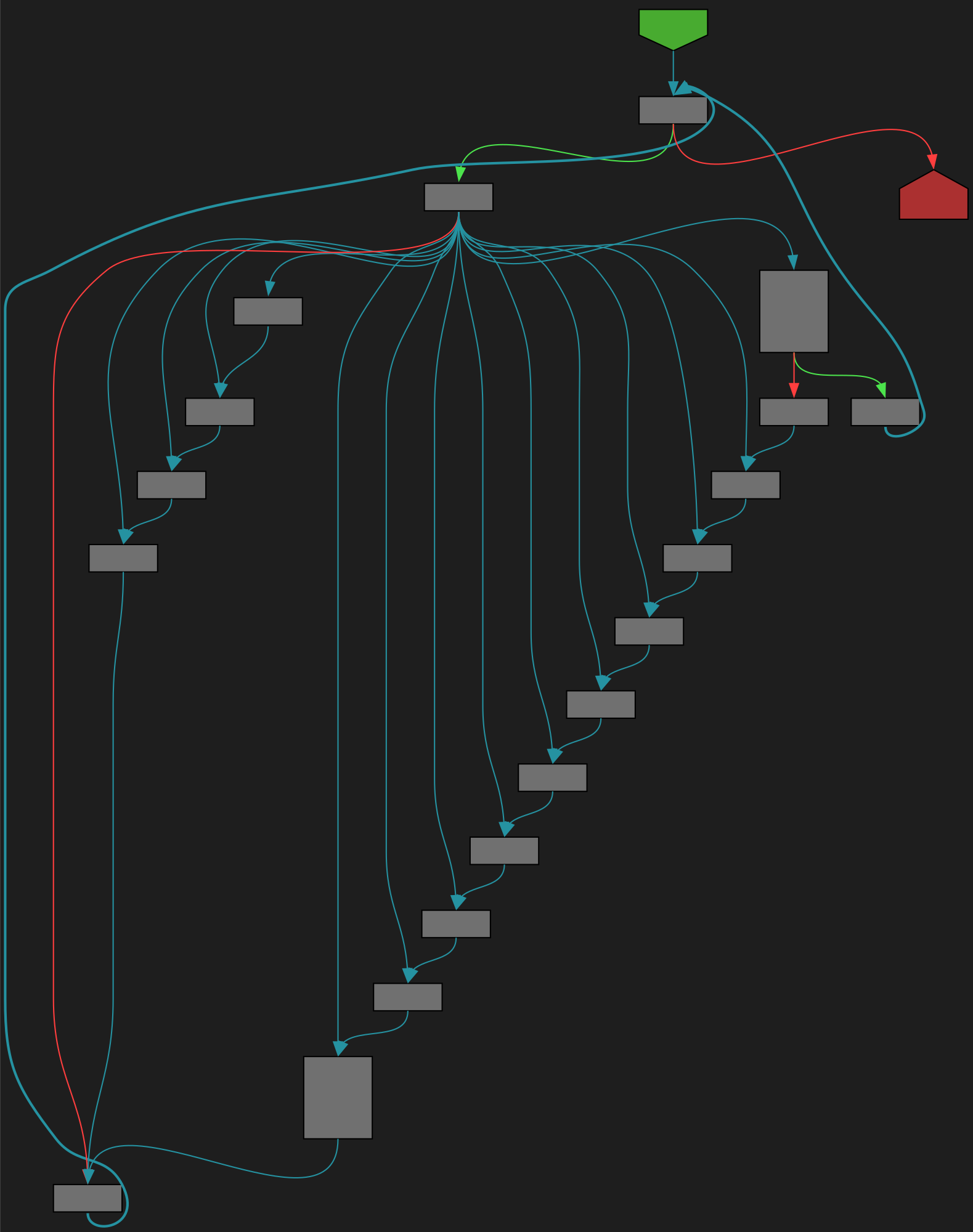
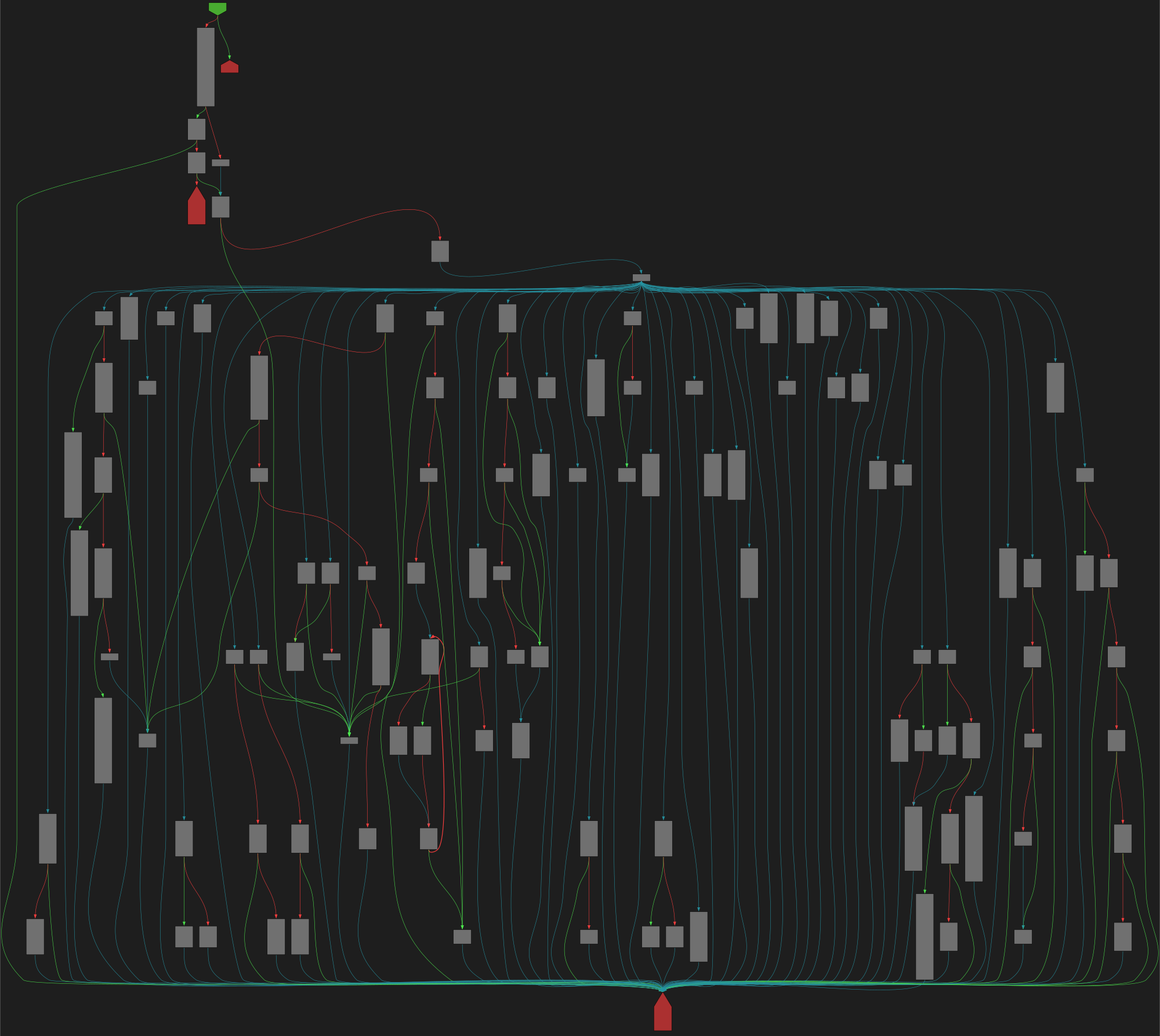
1601CFG Bot 🤖
cfgbot@mastodon.socialProject: microsoft/typescript https://github.com/microsoft/typescript
File: src/compiler/program.ts:3242 https://github.com/microsoft/typescript/blob/81c951894e93bdc37c6916f18adcd80de76679bc/src/compiler/program.ts#L3242
function checkModifiers(modifiers: NodeArray<ModifierLike>, isConstValid: boolean)
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fmicrosoft%2Ftypescript%2Fblob%2F81c951894e93bdc37c6916f18adcd80de76679bc%2Fsrc%2Fcompiler%2Fprogram.ts%23L3242&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fmicrosoft%2Ftypescript%2Fblob%2F81c951894e93bdc37c6916f18adcd80de76679bc%2Fsrc%2Fcompiler%2Fprogram.ts%23L3242&colors=light
FreddyB Aviation Photography
cvvhrn@sfba.socialUSMC AH-1Z Viper working the pattern at Pt. Mugu, July 2024 #USMC #choppa #rotor #Mugu #AH1Z #aviationphotography #planespotting #AvGeek #spotter #photography #Nikon #aircraft #nikonphotography
buherator
buheratorhttps://starlabs.sg/blog/2025/06-solo-a-pixel-6-pro-story-when-one-bug-is-all-you-need/
buherator
buheratorhttps://blog.exploits.club/exploits-club-weekly-newsletter-74/
kajer :unknown:
kajer@infosec.exchangeFucking stupid UI/UX choices.
Fortigate Firewall/Routers - All options for BGP/IPSEC are behind an "advanced options" user preference.... IT'S A FORTIFUCKINGROUTER the only people in this interface are advanced users.
PaloAlto XDR portal - Right-click for options on a line... fine... But wait, if you hold option/alt, you get even more options. I get the need to define which options are less common choices, but you should not be hiding things behind click-modifiers. The only people using the XDR interface will be advanced users. If a user doesn't have authorization for a command, then don't show it. If the option is destructive, then confirm with N number of dialogs. Also, the ENTIRE user interface is in italics.
Admin interfaces should never have hidden options.
Phrack Zine
phrack@bird.makeupThere’s still time for you to submit your article for the 40th anniversary edition of Phrack!
Jonty Wareing
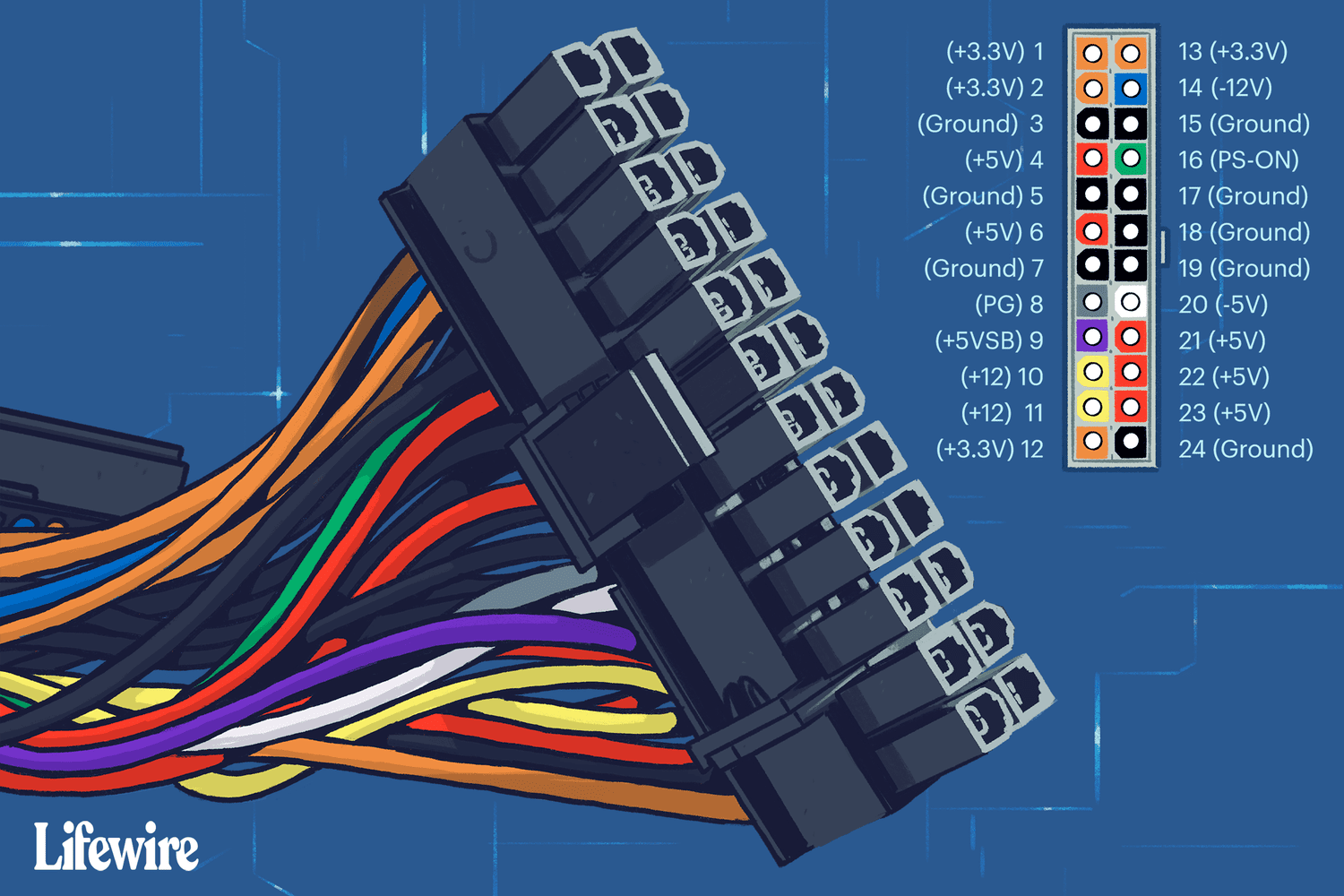
jonty@chaos.socialWhat is the most inappropriate connector with enough pins to support USB-C?
I suggest:
buherator
buheratorhttps://kaist-hacking.github.io/publication/yun-ksa/
eShard
eshard@infosec.exchangeOur journey with our #iOS emulator continues.
We show how we reached the home screen, enabled multitouch, unlocked network access, and started running real apps 👉 https://eshard.com/posts/emulating-ios-14-with-qemu-part2
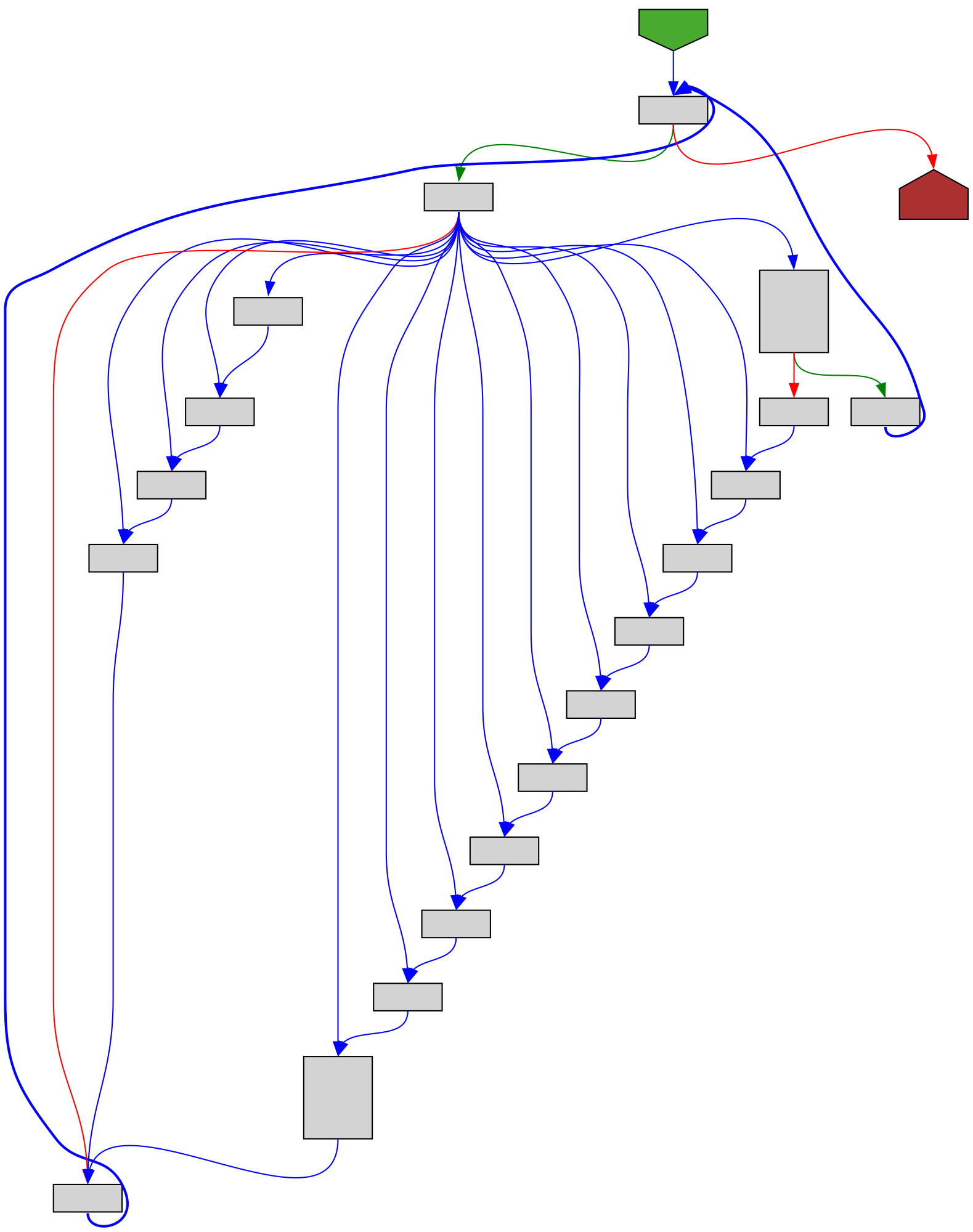
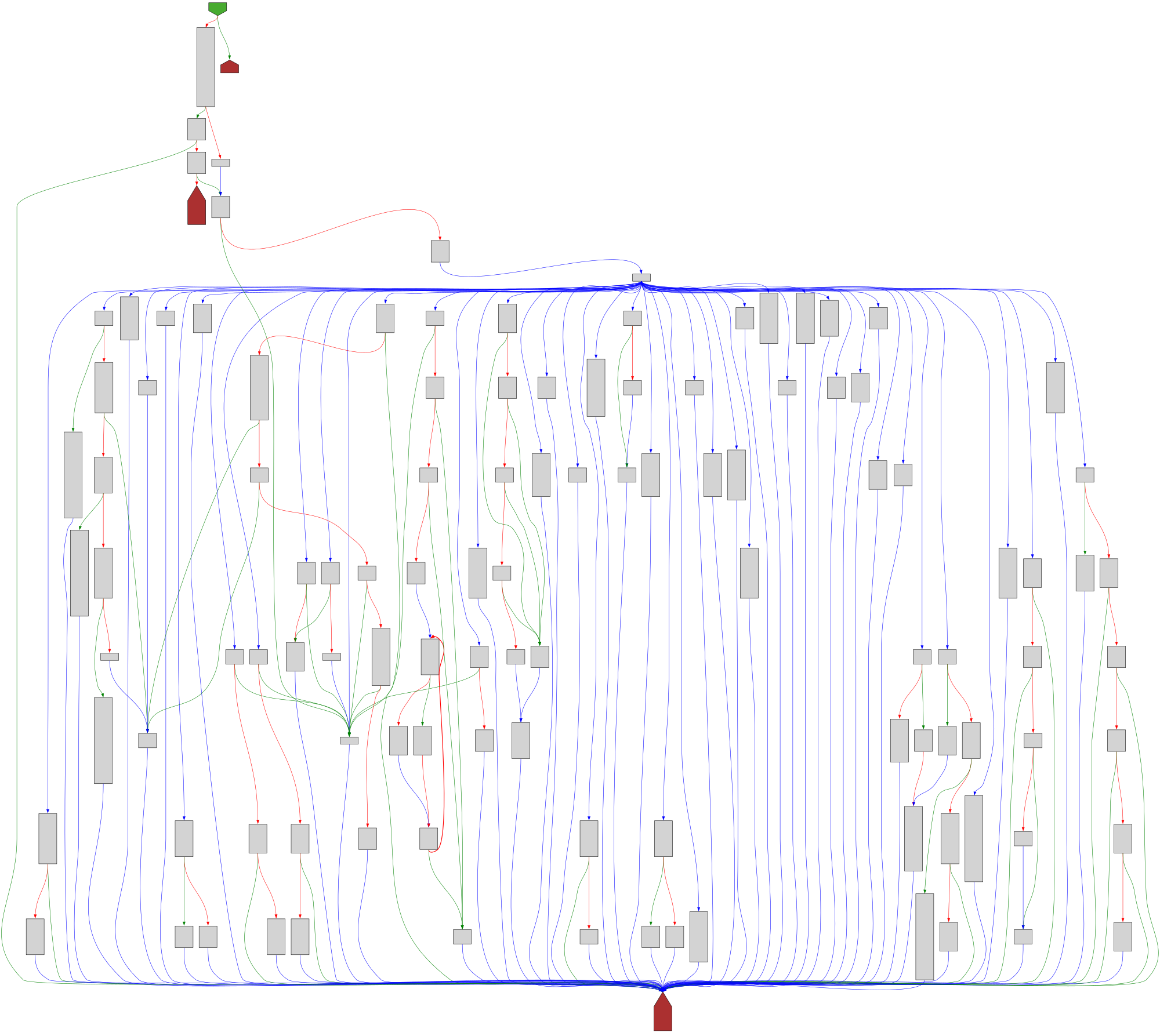
CFG Bot 🤖
cfgbot@mastodon.socialProject: openssl-static-gcc-dwarf 3.4.0
File: openssl
Address: 00478ea0
ssl3_ctrl
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00478ea0.json&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00478ea0.json&colors=light
The DFIR Report
TheDFIRReport@infosec.exchange🎯 THIS SATURDAY: DFIR Labs CTF 🎯
⏰ June 7 | 1630–2030 UTC
🔗 Register Now → https://dfirlabs.thedfirreport.com/ctf
🚀 DFIR Labs CTF is back!
💥 Only $9.99 to join
💥 Choose Elastic or Splunk
💥 Access a brand-new, unreleased case
💥 Top 5 get invited to join The DFIR Report team!
📣 Hear from past participants:
⭐ “Real case makes it different!”
🚀 “Great hands-on learning experience”
💯 “Excellent CTF, super responsive and realistic”
Don’t miss your chance to level up with real-world incident response challenges.
buherator
buheratorhttps://telex.hu/techtud/2025/06/03/hekkertamadas-paprika-csoport-erettsegi-adatbazis-masolas-oktatasi-hivatal
Wonder if perpetrators are in fact Hungarian (as the name suggests), or just using some LLM translator?
Alexandre Borges
alexandreborges@infosec.exchangeCisco IOS XE WLC Arbitrary File Upload Vulnerability (CVE-2025-20188) Analysis:
#cybersecurity #xxe #infosec #cve #vulnerability #threathunting #exploitation
Karl Voit 

publicvoit@graz.social
Every project should have a "cursed"-page like that: 😆
"Cursed knowledge we have learned as a result of building #Immich that we wish we never knew."
https://immich.app/cursed-knowledge/
🤓
Samuel Groß
saelo@chaos.socialhttps://chromereleases.googleblog.com/2025/06/stable-channel-update-for-desktop.html
Some cool things to note though: (1) the bug was mitigated via finch kill switch (https://developer.chrome.com/docs/web-platform/chrome-finch) one day after the report from TAG (2) we also fixed the V8 Sandbox bypass within 7 days even though it's not yet considered a security boundary.
And I've also updated our V8 Exploit Tracker sheet now: https://docs.google.com/document/d/1njn2dd5_6PB7oZGTmkmoihYnVcJEgRwEFxhHnGoptLk/edit?usp=sharing (see the 2025 tab) :)
Ars Technica
arstechnica@mastodon.socialMeta and Yandex are de-anonymizing Android users’ web browsing identifiers
Abuse allows Meta and Yandex to attach persistent identifiers to detailed browsing histories.
https://arstechnica.com/security/2025/06/headline-to-come/?utm_brand=arstechnica&utm_social-type=owned&utm_source=mastodon&utm_medium=social
/r/netsec
_r_netsec@infosec.exchangeHow to build a high-performance network fuzzer with LibAFL and libdesock https://lolcads.github.io/posts/2025/05/high_performance_network_fuzzing/