Posts
3915Following
728Followers
1601TrendAI Zero Day Initiative
thezdi@bird.makeupAll of the gear needed for #Pwn2Own Berlin is on its way. Next stop - Germany!
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgIn 15 minutes Europe will hopefully launch its next climate satellite. The launch can however only be watched via YouTube since we apparently can’t do that ourselves and have to put our government info next to the antivax promo. https://www.esa.int/ESA_Multimedia/ESA_Web_TV
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250428-00/?p=111121
Jesko Hüttenhain
rattle@infosec.exchangeFYSA; #BinaryRefinery has switched from pefile to LIEF:
https://github.com/binref/refinery/pull/84
It shouldn't change anything, but if it does, please let me know.
I wrote a book on Linux Memory Management, published by @nostarch - it's a comprehensive 1300 page exploration of Linux 6.0's memory management code, depth-first, diving into the code and REALLY explaining how things work.
The idea is to avoid hand waving as much as possible and literally explore what the kernel _actually_ does.
It's full of diagrams and careful explanations of logic including a ton of stuff you just can't find anywhere else.
It's currently available in its entirety in draft form via early access when you pre-order.
It's available at https://nostarch.com/linux-memory-manager
:)
Tib3rius 
tib3rius@infosec.exchange
Thanks Forbes, I was confused what password spraying...sorry, "sparaying" attacks looked like. 🫠
buherator
buheratorShow content
https://risingnemesisrecords.bandcamp.com/track/a-new-god-of-wrath
Daring Fireball
daringfireball@mastodon.social★ Another Periodic Suggestion to Try, Just Try, Switching to Kagi for Search
https://daringfireball.net/2025/04/try_switching_to_kagi
Michał "rysiek" Woźniak · 🇺🇦
rysiek@mstdn.socialApparently #PerplexityAI CEO is annoyed that people are sharing that article where he is quoted saying that their browser will track everything users do to sell more ads.
> “That’s kind of one of the other reasons we wanted to build a browser, is we want to get data even outside the app to better understand you,” Srinivas said.
This is that article, in case you'd like to share it:
https://techcrunch.com/2025/04/24/perplexity-ceo-says-its-browser-will-track-everything-users-do-online-to-sell-hyper-personalized-ads/
Receipt:
https://xcancel.com/AravSrinivas/status/1915812398470205461#m
st1nger  🏴☠️
🏴☠️ 

st1nger@infosec.exchange
"In the coming day(s), pretty much every #Kali system out there will fail to update. [..] This is not only you, this is for everyone, and this is entirely our fault. We lost access to the signing key of the repository, so we had to create a new one," https://www.kali.org/blog/new-kali-archive-signing-key/
CISA KEV Tracker
cisakevtracker@mastodon.socialCVE ID: CVE-2025-1976
Vendor: Broadcom
Product: Brocade Fabric OS
Date Added: 2025-04-28
Vulnerability: Broadcom Brocade Fabric OS Code Injection Vulnerability
Notes: https://support.broadcom.com/web/ecx/support-content-notification/-/external/content/SecurityAdvisories/0/25602 ; https://nvd.nist.gov/vuln/detail/CVE-2025-1976
CVE URL: https://nvd.nist.gov/vuln/detail/CVE-2025-1976
Linux Kernel Security
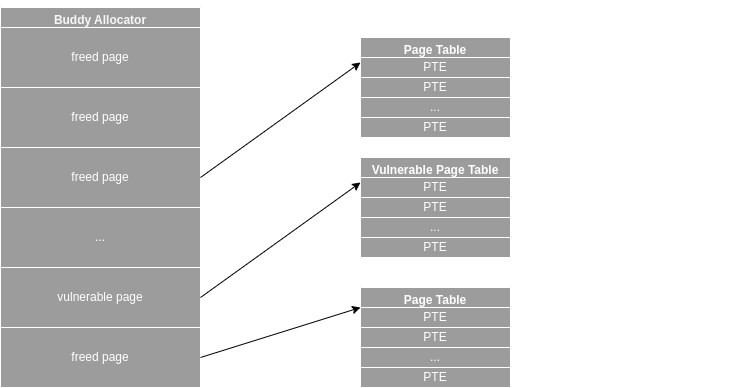
linkersec@infosec.exchangeExploiting CVE-2024-0582 via the Dirty Pagetable Method
Kuzey Arda Bulut posted an article about exploiting CVE-2024-0582 in io_uring using the Dirty Pagetable technique.
https://kuzey.rs/posts/Dirty_Page_Table/
This bug was previously reported by @jann and exploited by Oriol Castejón.
https://project-zero.issues.chromium.org/issues/42451653
https://blog.exodusintel.com/2024/03/27/mind-the-patch-gap-exploiting-an-io_uring-vulnerability-in-ubuntu/
buherator
buheratorclearbluejar
clearbluejar@infosec.exchangeNew #ghidriff release! v0.9.0
- Set custom analysis options
- Set custom base address (bootloaders, etc)
https://github.com/clearbluejar/ghidriff/releases/tag/v0.9.0
buherator
buheratorShow content
https://vulgardisplayofpurring.bandcamp.com/album/vulgar-display-of-purring-presents-new-york
This is a fun compilation!
Dr. Zalka Csenge Virág
TarkabarkaHolgy@ohai.socialI cannot stress this enough:
In a lot of traditions what we call fairy tales (or wonder tales) were for adults. Often told by grown men at the barracks or during work.
Which means uncensored fairy tale texts often include a whole lot of cussing. Because you'd yell "Sh**!" too if a devil chased you.
And this is how we get the scene where an evil king offers a hero money for his services and the hero flat out says "Your majesty, suck my d***"
The DFIR Report
TheDFIRReport@infosec.exchange🌟New report out today!🌟
Navigating Through The Fog
In December 2024, The DFIR Report's Threat Intel Group uncovered an open directory linked to a Fog ransomware affiliate, revealing their operational toolkit.
Key takeaways from our analysis:
➡️ Initial Access: Compromised SonicWall VPN credentials were used.
➡️ Toolkit: Included tools for reconnaissance, exploitation (Certipy, Zer0dump), credential theft (DonPAPI), persistence (AnyDesk automated via PowerShell), and C2 (Sliver, Proxychains tunneling).
➡️ Targets: Victims spanned technology, education, and logistics sectors across Europe, North America, and South America.
➡️ Persistence: AnyDesk RMM tool was leveraged for maintaining access.
➡️ Command & Control: Sliver C2 executables were hosted alongside Proxychains for traffic tunneling.
Read the full analysis here: https://thedfirreport.com/2025/04/28/navigating-through-the-fog/
Caitlin Condon
catc0n@infosec.exchangeLike others, Rapid7 MDR has observed in-the-wild exploitation of SAP NetWeaver Visual Composer CVE-2025-31324 in customer environments. Webshells being dropped with random 8-character names. Earliest confirmed EITW on our side currently is late March, but I'd expect that may change (i.e., move earlier). Manufacturing is overwhelmingly the most affected vertical, mostly in the U.S.
Romain THOMAS
rh0main@infosec.exchangeFuzzing Windows ARM64 binaries with a DBI and LLVM?
Here we go: https://www.romainthomas.fr/post/25-04-windows-arm64-qbdi-fuzzing/