Posts
2923Following
695Followers
1529buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/04/18/2
Zhuowei Zhang
zhuowei@notnow.devI spent all morning trying to decode the Apple Positional Audio Codec (APAC)’s GlobalConfig from its MPEG4 Sample Description Box (stsd).
If you want to follow along:
- the codec is in
/System/Library/Frameworks/AudioToolbox.framework/AudioCodecs - See
apac::GlobalConfig::Serializeandapac::GlobalConfig::Deserialize - If you need a sample file:
afconvert -o sound.m4a -d apac -f mp4f sound.wav - Or grab a sample file from https://trac.ffmpeg.org/ticket/11480
- Pull the
stsdfrom the m4a withmp4extract --payload-only moov/trak[0]/mdia/minf/stbl/stsd/apac sound.m4a sound_config.bin - The config starts after
dapathen 4 0x00 bytes - First two bytes of the apac bitstream are 0x08 0x00 (see
IsAPACBitstreamVersionValid/ACAPACBaseEncoder::GetMagicCookie) - followed by the
GlobalConfig
Disconnect3d
disconnect3d@infosec.exchangeReleased new Pwndbg: 2025.04.18
It adds display of breakpoints in the disasm view, new libcinfo command, improves attachp & hexdump commands, UI, TUI and more. Also, command names use "-" istead of "_" now for consistency.
Read more and download it on https://github.com/pwndbg/pwndbg/releases/tag/2025.04.18 !
Filippo Valsorda
filippo@abyssdomain.expertOof. Reportedly, if you got a certificate from SSL.com by putting “example[@]gmail.com” at _validation-contactemail.example.com, they would add gmail.com (!!!) to your verified domains.
A good reminder to use the CAA record, and to sign up for CT monitoring (e.g. Cert Spotter).
Graham Sutherland / Polynomial
gsuberland@chaos.socialTIC80 jam just kicked off, with a DJ set from Commander Homer!
Washi
washi@infosec.exchangeAfter #flareon11 challenge 7, I got inspired to build tooling for #dotnet Native AOT reverse engineering.
As such, I built a #Ghidra Analyzer that can automatically recover most .NET types, methods and frozen objects (e.g., strings).
👉https://blog.washi.dev/posts/recovering-nativeaot-metadata/
/r/netsec
_r_netsec@infosec.exchangeCVE-2025-25364: Speedify VPN MacOS privilege Escalation https://blog.securelayer7.net/cve-2025-25364-speedify-vpn-macos-escalation/
Glyn Moody
glynmoody@mastodon.socialTake Action: Defend the @internetarchive - https://blog.archive.org/2025/04/17/take-action-defend-the-internet-archive/ "This lawsuit is an existential threat to the Internet Archive and everything we preserve—including the Wayback Machine, a cornerstone of memory and preservation on the internet." please sign the open letter if you can
Tim Carstens Ⓥ✨ is hacking zk
intoverflow@bird.makeupFun fact:
💁 The oldest known buffer overflow vuln dates back to UNIX V6 login
💁♀️ It appeared in a 1981 post by Truscott & Ellis (better known for inventing Usenet)
💁♂️ The next overflow vuln was fingerd, 1988
Bonus fact:
🙅 The login vuln isn’t real:
https://www.tuhs.org/cgi-bin/utree.pl?file=V6/usr/source/s1/login.c
Open Source Security mailing list
oss_security@bird.makeupMultiple vulnerabilities in libxml2 https://www.openwall.com/lists/oss-security/2025/04/17/3
CVE-2025-32414: Buffer overflow when parsing text streams with Python API
Python Package Index contains outdated and unsanctioned vulnerable upload
CVE-2025-32415: Heap-based Buffer Overflow in xmlSchemaIDCFillNodeTables
Jason Scott
textfiles@mastodon.archive.orgIt was only a matter of time - a contracted, approved grant to the Internet Archive was cut with no warning.
David Chisnall (*Now with 50% more sarcasm!*)
david_chisnall@infosec.exchangeThe first edition of the #CHERIoT book has been published!
The eBook editions are available for purchase now from a few retailers, print editions will take a bit longer to appear (up to two weeks). And, of course, the drafts of the second edition remain free (HTML, ePub, PDF) from the CHERIoT site
Thanks to Discribe Hub for funding a lot of the work on this edition!
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/04/18/1
Exploit published ^
note to self unreal tournament
mothcompute@vixen.zonemicrosoft word, the predecessor to microsoft dword,
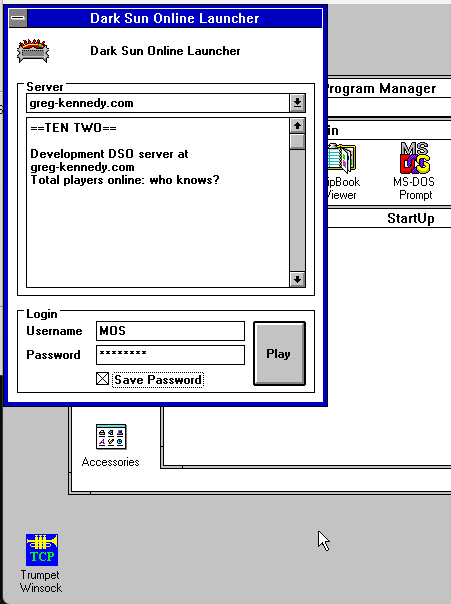
Quite proud of myself for successfully building a Windows 16-bit application that runs on Windows 3.1 - all dialog-based, and it makes network connections, too! Compiled with Visual C++ 1.52 on XP, it works on this old system. Consumes 14kb disk space and does everything in even less RAM :)
Andrea Allievi
aall86@bird.makeuphttps://techcommunity.microsoft.com/blog/windows-itpro-blog/hotpatch-for-windows-client-now-available/4399808 Finally! I personally worked on Hotpatch, together with my team 3 years ago... and now is finally approaching client versions of Windows... Yuuuyuuu!
hasherezade
hasherezade@bird.makeupMy new blog for Check Point Research - check it out! 💙 // #ProcessInjection : #WaitingThreadHijacking
Satoshi Tanda
standa_t@bird.makeupI am thrilled to be back and offer the in-person training once again at Hexacon, the fabulous conf. in Paris
https://hexacon.fr/trainer/tanda/
Get hands-on experience with virtualization and learn real-world applications and bugs of them!
The tickets will be available for purchase soon.
Tim (Wadhwa-)Brown 
timb_machine@infosec.exchange
Interesting links of the week:
Strategy:
* https://en.wikipedia.org/wiki/SIPOC - modelling systems with SIPOC
* https://www.thecvefoundation.org/ - the CVE foundation
* https://euvd.enisa.europa.eu/ - EU bug jail
* https://xntrik.wtf/aisa2024/ - @xntrik maps threats with https://threatcl.github.io/
* https://threatspec.org/ - the ThreatSpec
Threats:
* https://cloud.google.com/blog/topics/threat-intelligence/windows-rogue-remote-desktop-protocol - a novel phishing attack involving RDP
Detection:
* https://rulehound.com/rules - a single place to find interesting detection engineering ideas
Bugs:
* https://bugs.chromium.org/p/chromium/issues/detail?id=584535 - an 11 year old bug in every browser, still not dead!
Exploitation:
* https://silentsignal.github.io/BelowMI/ - memory management on System i courtesy of @buherator
* https://github.com/N1ckDunn/SOSLInjection/blob/main/SOSLInjection.pdf - Sal''esforce \o/
* https://github.com/N1ckDunn/DoubleFetch/blob/main/Double-FetchVulnerabilitiesInC.pdf - exploiting double fetch
Hard hacks:
* https://xairy.io/articles/thinkpad-xdci - emulating USB on a ThinkPad
* https://www.rtl-sdr.com/dragonos-lte-imsi-sniffing-using-the-lte-sniffer-tool-and-an-ettus-x310-sdr/ - build your own LTE sniffer
* https://blog.sesse.net/blog/tech/2025-04-05-10-57_cisco_2504_password_extraction.html - extracting passwords from Cisco WLC
* https://www.prizmlabs.io/post/remote-rootkits-uncovering-a-0-click-rce-in-the-supernote-nomad-e-ink-tablet - exploiting the Nomad e-ink tablet
Nerd:
* https://ukparliament.github.io/ontologies/meta/bots/ - UK parliamentary bots
* https://mwl.io/fiction/crime - Git drives people to murder
* https://changelog.complete.org/archives/10768-announcing-the-nncpnet-email-network - building a new mail protocol