Posts
2983Following
697Followers
1545buherator
buherator- Copying .vscode/ template directory to the original (Eclipse-based) repo
- Fill in the path of my Ghidra installation in build.gradle (this can be pbbly done more elegantly by setting the env)
- Renaming the .classpath file produced by Eclipse, as it confuses VSCode
- Manually loading the plugin from Code Browser's File/Configure menu
The debugging experince is unfortunately shit so far, I can't even see which breakpoint is hit - I'll keep on reading VSCode tutorials...
buherator
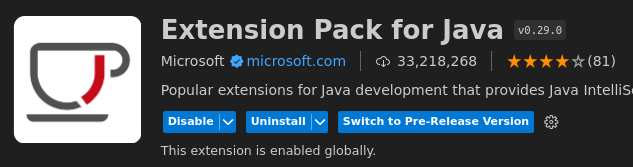
buherator1) You'll need the Extension Pack for Java (from MS, not Oracle's crap!)
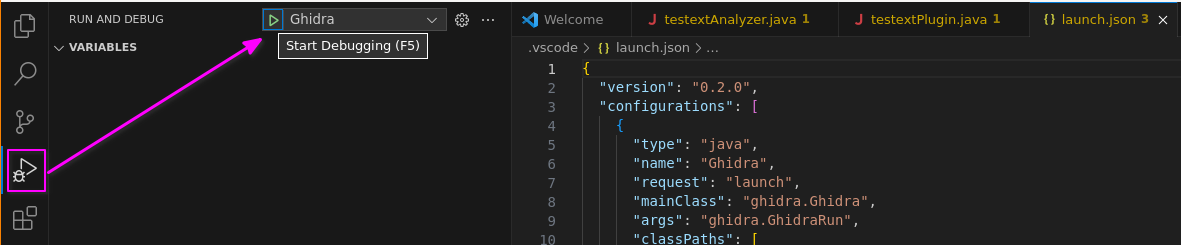
2) Ghidra launch configurations are available under the "bug with play button" sidebar icon
+1) Directory/workspace names are not necessarily valid Java package names, but Ghidra generates the code and the fs structure anyway
Now I'm trying to figure out why the sample code is not actually loaded to Ghidra when debugging...
buherator
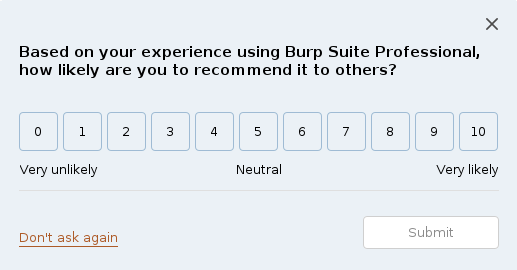
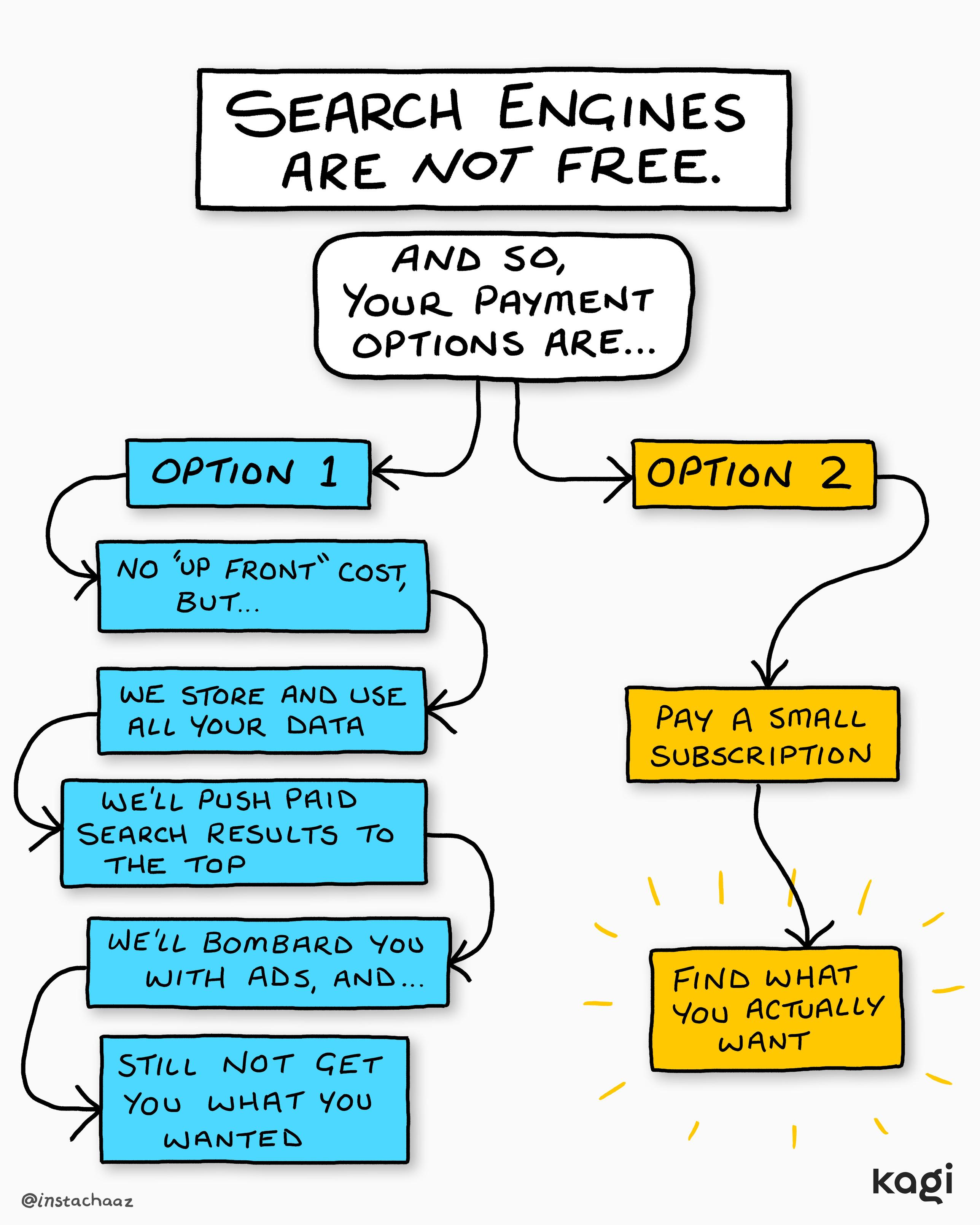
buheratorThis supposed to be a professional tool (that users pay for btw) not a fucking marketing platform.
/cc @albinowax
Jeff Moss
thedarktangent@defcon.socialToday was my last day at ONCD. I turned in my White House pass, laptop and phone.
I was explaining why I was resigning, while they were explaining the Special Governmental Employee (SGE) program was being eliminated. We both got to the same result. No hard feelings, I wish the best for ONCD and Cyber, there are a lot of important and pressing challenges ahead.
On the way out I watched movers empty out the Pandemic Readiness office. 😦 I went for drinks with friends.
You remember #Apple scanning all images on your #mobile device?
If you have an #Android #phone, a new app that doesn't appear in your menu has been automatically and silently installed (or soon will be) by #Google. It is called #AndroidSystemSafetyCore and does exactly the same - scan all images on your device as well as all incoming ones (via messaging). The new spin is that it does so "to protect your #privacy".
You can uninstall this app safely via System -> Apps.
https://developers.google.com/android/binary_transparency/google1p/overview
If you are using Signal, and you are doing something the government considers illegal, the way they are going to read your messages about it is they will arrest the person you sent the messages *to*, and make your counterparty show them the logs. We know this because this technique came up again and again in, for example, the Jan. 6 court filings.
There may, hypothetically, be other Signal exploits available to a government, but this is the one they will use, because it works.
Valentin Gosu
valenting@fosstodon.orgI just published a blog post about getaddrinfo and all the other weird DNS APIs that we use in Firefox to resolve HTTPS records.
https://valentin.gosu.se/blog/2025/02/getaddrinfo-sucks-everything-else-is-much-worse
All this was part of the talk I gave at FOSDEM last weekend.
modzero
modzero@infosec.exchangeROPing our way to “Yay, RCE” - and a lesson in the importance of a good nights sleep!
From vulnerability to exploit - follow our Colleague Michaels journey of developing an ARM ROP chain to exploit a buffer overflow in uc-http
Via Return-Oriented Programming chain small code snippets, or gadgets, already present in a program’s memory can be leveraged
By chaining these gadgets together, they can execute arbitrary code without injecting anything new
Dive into the process of reverse engineering, gadget hunting, and crafting a working exploit.
Learn all about it in Michaels full report.
buherator
buheratorhttps://blog.0patch.com/2025/02/micropatches-released-for-windows-ole.html
daniel:// stenberg://
bagder@mastodon.socialDaniel weekly February 7, 2025
https://lists.haxx.se/pipermail/daniel/2025-February/000099.html
old security, ssh security, BBC, URLs from file, you can help, curl up CVE-2024-7264, EOSAwards, Workshop, FOSDEM, 1337, release, regressions, release candidates, codeql, no goods
Enfys J. Book [they/them]
EnfysBook@kind.socialIf you use Signal, Discord, or any other messaging app and you DON'T want Google or Apple monitoring/reading/learning from your messages, follow these steps.
Android:
1. Open Google app
2. Tap your profile photo
3. Settings
4. Google Assistant
5. "Your Apps"
6. Choose the app (e.g., Signal)
7. Toggle "Let your assistant learn from this app" off
iPhone:
1. Settings
2. Apps
3. Choose the app (e.g., Signal)
4. Toggle Apple intelligence or Siri settings to off (“learn from this app”)
/r/netsec
_r_netsec@infosec.exchangeWindows Telephony Services: 2025 Patch Diffing & Analysis https://blog.securelayer7.net/windows-telephony-services-2025-patch-diffing-and-analysis-pt-1/
Mr. Bitterness
wdormann@infosec.exchangeUK orders Apple to put backdoor in iCloud encryption (Advanced Data Protection, which is end-to-end encrypted):
https://www.theverge.com/news/608145/apple-uk-icloud-encrypted-backups-spying-snoopers-charter
The way this plays out is that UK iPhones lose the Advanced Data Protection feature, right?
Right??
qwertyoruiopz
qwertyoruiop@nso.groupBig news in Italy around the government misusing Paragon, and Paragon ended up cutting the contract citing misuse/ethical violations.
I commend Paragon on this one, the misuse was pretty blatant and as Italian sad to see. This is how the industry should react to misuse!
offensivecon
offensive_con@bird.makeup****For students and private individuals (not paid by a company) ONLY***
We are releasing a very limited amount of tickets for students and private individuals.
These tickets will be discounted in price and are separate from the waiting list.
Please email us with your story and background on why you want the ticket to info(at)offensivecon(dot)org
Students will have to bring a valid student ID to the conference.