Posts
3724Following
724Followers
1598Carly Page
carlypage@mastodon.socialZyxel says it has no plans to release patches for two zero-days under active attack and is advising customers to replace vulnerable routers.
The company says these devices have been “end of life for years” - but the devices are not listed on Zyxel’s EOL page, and some are still available to buy on Amazon https://techcrunch.com/2025/02/05/router-maker-zyxel-tells-customers-to-replace-vulnerable-hardware-exploited-by-hackers/
daniel:// stenberg://
bagder@mastodon.socialEmbrace. This is the new #curl CVE I expect I will get a fair amount of... "traffic" about: https://curl.se/docs/CVE-2025-0725.html
buherator
buheratorhttps://blog.0patch.com/2025/02/micropatches-released-for-windows-task.html
Scott Williams 🐧
vwbusguy@mastodon.onlineWe've been collecting and mirroring what we can find of public data scrapes of data that has recently gone missing from federal sites or is likely to in the near future. The repos here include public data from CDC, NIH, and NOAA. Be warned that some of these repos are quite large!
buherator
buheratorhttps://bughunters.google.com/blog/6644316274294784/secure-by-design-google-s-blueprint-for-a-high-assurance-web-framework
screaminggoat
screaminggoat@infosec.exchangeUnofficial #PatchTuesday continues with Google Chrome: Stable Channel Update for Desktop
Chrome 133.0.6943.53 (Linux) and 133.0.6943.53/54( Windows, Mac) includes 12 security fixes, 3 are externally reported:
- CVE-2025-0444 (high) Use after free in Skia
- CVE-2025-0445 (high) Use after free in V8
- CVE-2025-0451 (medium) Inappropriate implementation in Extensions API
No mention of exploitation.
James Kettle
albinowax@infosec.exchangeThe results are in! We're proud to announce the Top 10 Web Hacking Techniques of 2024! https://portswigger.net/research/top-10-web-hacking-techniques-of-2024
screaminggoat
screaminggoat@infosec.exchangeNETGEAR did this earlier than #PatchTuesday on 01 February 2025 but here you go:
- Security Advisory for Unauthenticated RCE on Some WiFi Routers, PSV-2023-0039An unassigned (no CVE) unauthenticated remote code execution vulnerability (CVSSv3.0: 9.8 critical) has been patched in NETGEAR XR1000, XR1000v2, and XR500 WiFi routers.
- Security Advisory for Authentication Bypass on Some Wireless Access Points, PSV-2021-0117An unassigned (no CVE) authentication bypass security vulnerability (9.6 critical) was patched on NETGEAR WAX206, WAX220 and WAX214c2 wireless access points.
Ivan Ožić Bebek
obivan@infosec.exchangeTop 10 web hacking techniques of 2024 https://portswigger.net/research/top-10-web-hacking-techniques-of-2024
screaminggoat
screaminggoat@infosec.exchange#PatchTuesday continues with Zyxel: Zyxel security advisory for command injection and insecure default credentials vulnerabilities in certain legacy DSL CPE
Zyxel's security advisory confirms the existence of CVE-2024-40890, CVE-2024-40891, and CVE-2025-0890 affecting end-of-life DSL CPE products. While they link to GreyNoise's blog post, Zyxel does not acknowledge the fact that CVE-2024-40891 (8.8 high) post-auth command injection is a zero-day being exploited in the wild by a Mirai botnet variant. They reiterate that EoL products don’t receive further support and:
"we strongly recommend that users replace them with newer-generation products for optimal protection."
Note: DSL CPE likely stands for Digital Subscriber Line Customer-Premises Equipment cc: @fellows for more Patch Tuesday Madness.
#zyxel #vulnerability #cve #CVE_2024_40891 #zeroday #eitw #activeexploitation #mirai #botnet #infosec #cybersecurity
screaminggoat
screaminggoat@infosec.exchangeCISA: CISA Adds Four Known Exploited Vulnerabilities to Catalog
Hot off the press!:
- CVE-2018-19410 (9.8 critical) Paessler PRTG Network Monitor Local File Inclusion Vulnerability
- CVE-2018-9276 (7.2 high) Paessler PRTG Network Monitor OS Command Injection Vulnerability
- CVE-2024-29059 (7.5 high) Microsoft .NET Framework Information Disclosure Vulnerability
- CVE-2024-45195 (9.8 critical) Apache OFBiz Forced Browsing Vulnerability
#cisa #cisakev #kev #vulnerability #eitw #activeexploitation #infosec #cybersecurity #knownexploitedvulnerabilitiescatalog
Gynvael Coldwind 🐈
gynvael@infosec.exchangeThere is still a couple more days to submit your 1-page article to Paged Out! #6!
We're at 41 pages of content out of 50 required. We'll start finalizing the issue when we reach 50. Not much time left, but you can still make it! 🙂
Details: https://pagedout.institute/?page=cfp.php
buherator
buheratorI mean, their last exploit writeup is estimated a 15mins read, the latest thing is 41 and there isn't even code to explain.
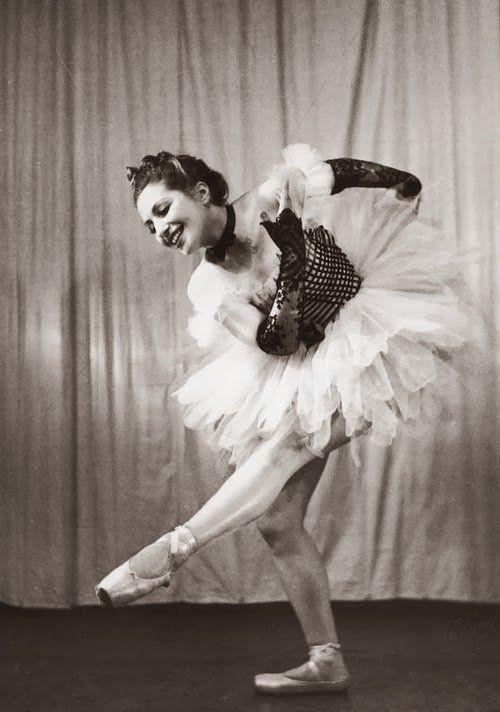
Auschwitz Memorial
auschwitzmuseum@mastodon.world4 February 1917 | A Polish Jewish dancer Franciszka Mann was born. She was most probably the woman who on 23 October 1943, inside the undressing room of gas chamber II at Auschwitz II-Birkenau, seized SS man Josef Schillinger’s pistol, shot him & wounded SS man Wilhelm Emmerich.
buherator
buheratorCVE-2024-27137: Unrestricted deserialization of JMX authentication credentials
https://seclists.org/oss-sec/2025/q1/92
CVE-2025-24860: Network region AUTHZ bypass
https://seclists.org/oss-sec/2025/q1/94
CVE-2025-23015: Privilege escalation with ALL KEYSPACES permission
https://seclists.org/oss-sec/2025/q1/93
buherator
buheratorhttps://github.com/xkiian/cloudflare-jsd
buherator
buheratorhttps://blog.0patch.com/2025/02/micropatches-released-for-ntlm-hash.html
Erik Moeller
eloquence@social.coopDo you want to introduce the fediverse and/or Bluesky to your organization -- in addition to, or instead of, X & Meta?
Through Feb, Mar and Apr, I'll be offering free one-hour sessions on Fridays to talk to your org. For-profit, non-profit, gov, edu, etc. This is not a consultancy; this is volunteer advocacy and support for building our collective independence from X & Meta.
If you are interested, book a slot through this link (starting Feb 7). Time is not movable. :)
Paragon Initiative Enterprises
paragon@phpc.socialNew from our team: A PHP implementation of RFC 9180 (HPKE - Hybrid Public-Key Encryption):
https://github.com/paragonie/hpke-php
This should serve as building block for more secure protocols (i.e., RFC 9420 a.k.a. Messaging Layer Security)/
This would, in turn, enable PHP developers to write software that communicates with MLS-compatible end-to-end encrypted messaging services.