Posts
3395Following
713Followers
1581buherator
buheratorhttps://en.wikipedia.org/wiki/Rubber_duck_debugging
buherator
buheratorhttps://blog.convisoappsec.com/en/introduction-to-fuzzing-android-native-components-strategies-for-harness-creation/
#fuzzing
Georgiana Brummell
dandylover1@friendica.worldAs someone who is totally blind, the Fediverse is the only place where I have ever been able to follow people such as photographers, artists, or even those who post pictures of their cats or the food they ate. The reason is that most of them use alt text. They take the time to describe the images that my screen reader can't recognise. Some write the descriptions themselves, and others use tools such as altbot. Some worry that their descriptions aren't good enough, especially when they are new at this. Let me assure you, not only are they good enough, they are extremely appreciated! If the rest of the world thought as you did, it would be a much better place. Don't hesitate to ask if you're unsure of something, but never think that we don't notice your effort.
#appreciation #accessibility #altbot #alttext #blind #blindness #fediverse #gratitude #images #inclusivity #peoplewhocare #pictures #technology
Zack Whittaker
zackwhittaker@mastodon.socialBREAKING: UnitedHealth has confirmed the ransomware attack and data breach on its Change Healthcare subsidiary in February 2024 now affects around 190 million people — almost double the previous estimate.
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.org@HalvarFlake - I promised to take a better look at the #EuroStack but initially I could find no detail. Now there is a new (brief) document that looks very urgent but I haven't yet studied it: https://euro-stack.eu/a-pitch-paper/
CFG Bot 🤖
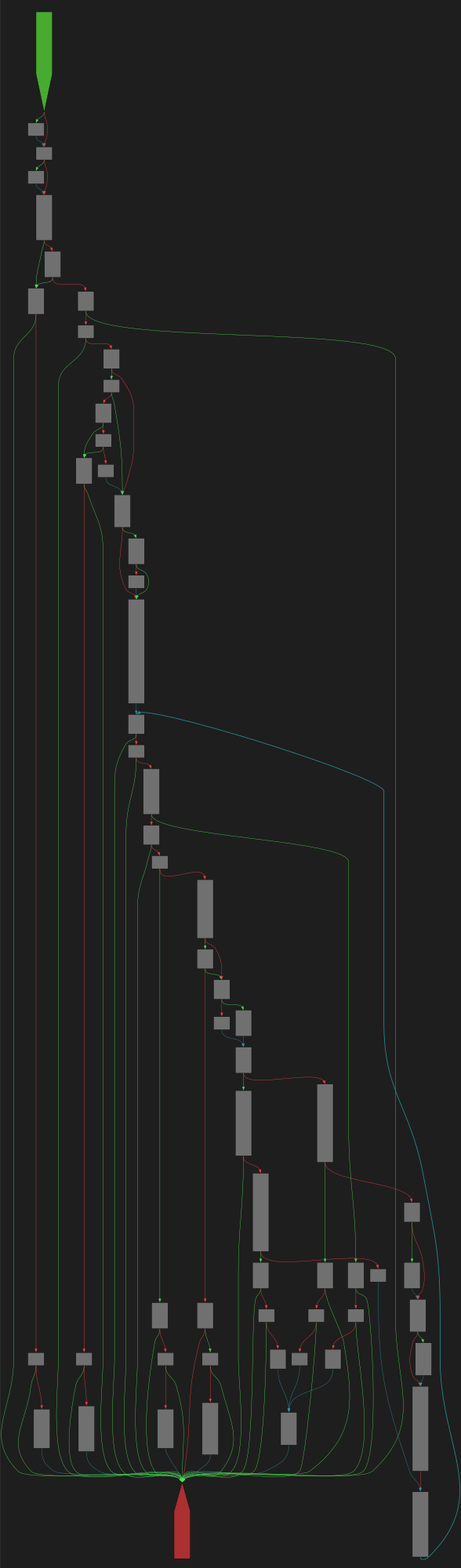
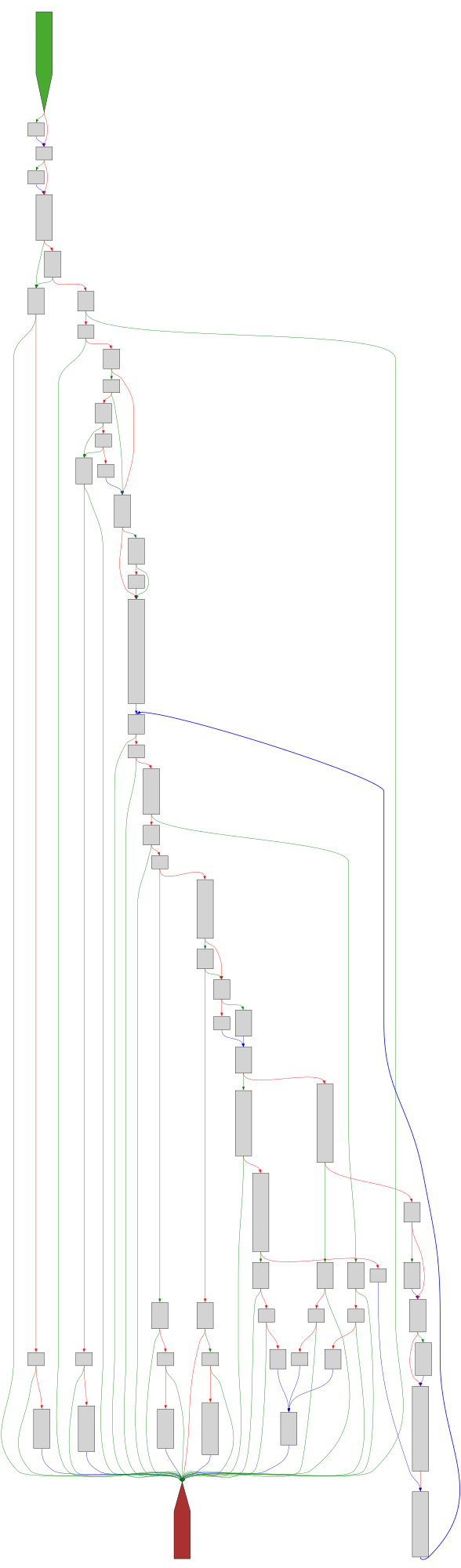
cfgbot@mastodon.socialProject: mpengine-x64-pdb 1.1.24090.11
File: mpengine.dll
Address: 75a20b610
Read
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fmpengine-x64-pdb%2F75a20b610.json&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fmpengine-x64-pdb%2F75a20b610.json&colors=light
Pavel A. Samsonov
PavelASamsonov@mastodon.socialMe clicking on a restaurant website: I wonder when they're open and what they serve
Restaurant website: O U R M I S S I O N
CFG Bot 🤖
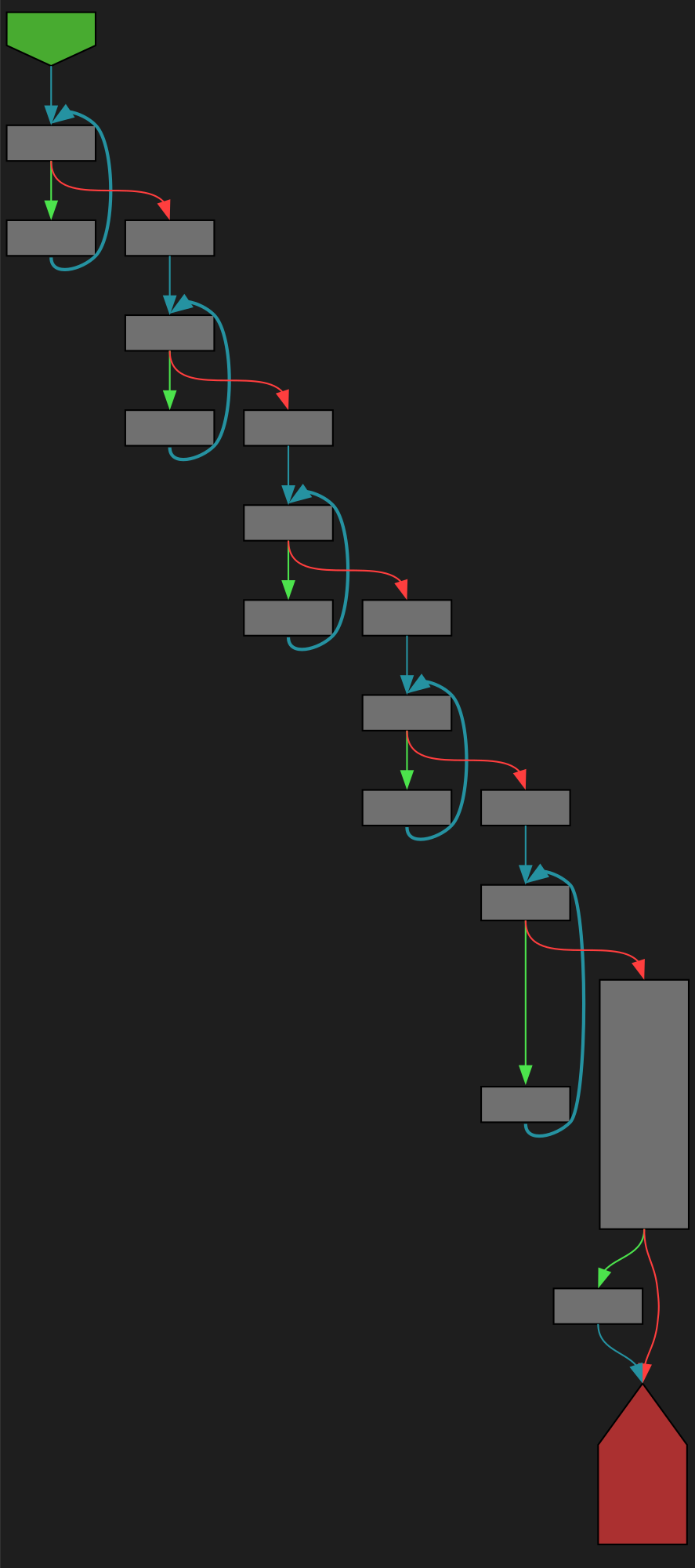
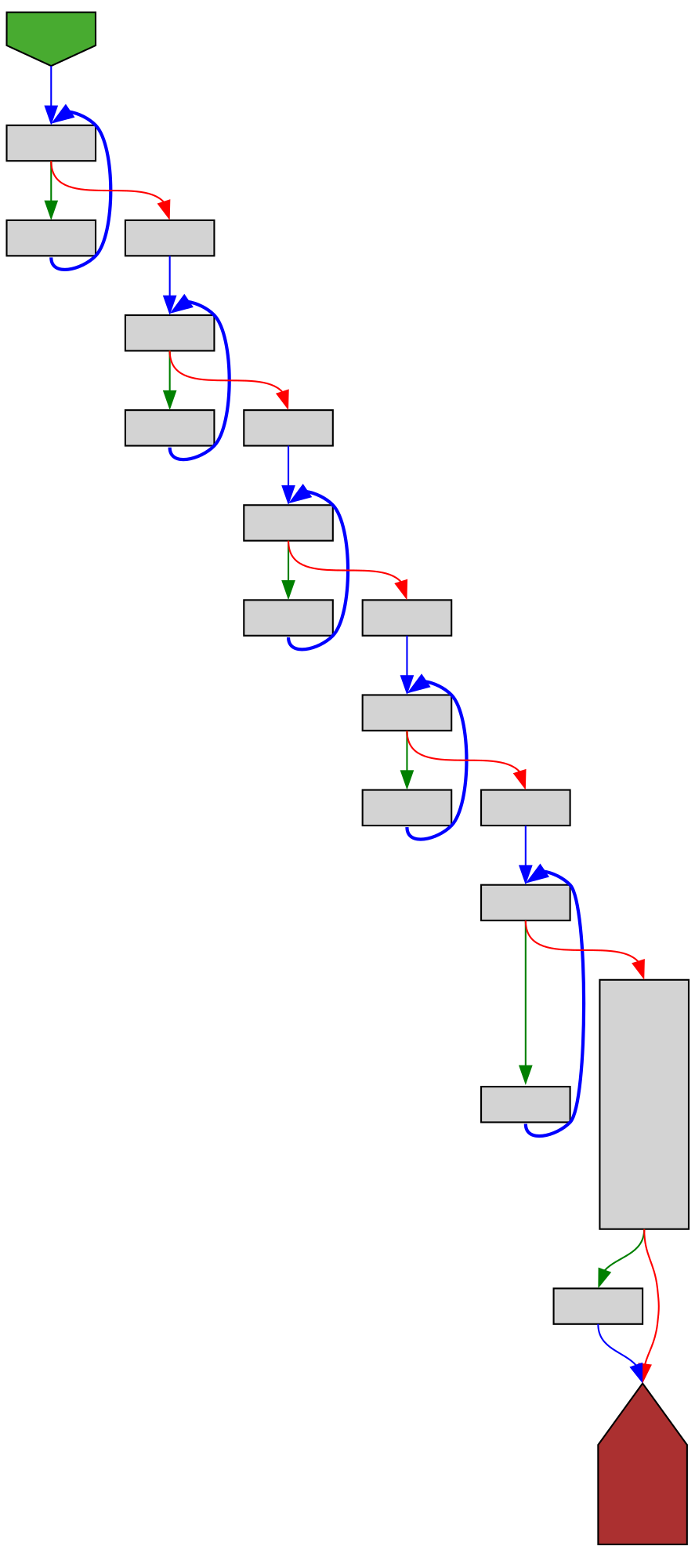
cfgbot@mastodon.socialProject: golang/go https://github.com/golang/go
File: src/cmd/vendor/github.com/google/pprof/profile/encode.go:132 https://github.com/golang/go/blob/refs/tags/go1.23.4/src/cmd/vendor/github.com/google/pprof/profile/encode.go#L132
func (p *Profile) encode(b *buffer)
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgithub.com%2Fgoogle%2Fpprof%2Fprofile%2Fencode.go%23L132&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgithub.com%2Fgoogle%2Fpprof%2Fprofile%2Fencode.go%23L132&colors=light
buherator
buheratorhttps://starlabs.sg/blog/2025/cve-2024-26230-windows-telephony-service-its-got-some-call-ing-issues/
lcamtuf 


lcamtuf@infosec.exchange
UI is hell, or why you can't design a four-function calculator: https://lcamtuf.substack.com/p/ui-is-hell-four-function-calculators
buherator
buheratorhttps://www.cisa.gov/news-events/alerts/2025/01/23/cisa-adds-one-known-exploited-vulnerability-catalog
The KEV page quotes (emphasis mine): "JQuery contains a *persistent* cross-site scripting (XSS) vulnerability" so this still doesn't seem to meet the bar for my XSS Reflections list:
https://github.com/v-p-b/xss-reflections
If anybody has more info about the related incident please lmk!
TrendAI Zero Day Initiative
thezdi@infosec.exchangeAnd that’s a wrap! #Pwn2Own Automotive 2025 is complete. In total, we awarded $886,250 for 49 0-days over the three day competition. With 30.5 points and $222,250 awarded, Sina Kheirkhah (@SinSinology) of Summoning Team (@SummoningTeam) is our Master of Pwn. #P2OAuto
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250123-00/?p=110800
Full system instrumentation ftw :)
Soatok Dreamseeker
soatok@furry.engineerEvery once in a while I have a really stupid idea, and then I sit down to write out what it would look like, and immediately spot a flaw in it that renders the whole thing insecure.
One of these days, one of my bad ideas is going to look back at me as someone else's implementation, deployed to production.
/r/netsec
_r_netsec@infosec.exchangeWinVisor: A proof-of-concept hypervisor-based emulator for Windows x64 binaries https://www.elastic.co/security-labs/winvisor-hypervisor-based-emulator
The Shadowserver Foundation
shadowserver@infosec.exchangeWe are sharing backdoored Ivanti Connect Secure devices that *may* have been compromised as part of a CVE-2025-0282 exploitation campaign (but also we believe may include older or other activity).
379 new backdoored instances found on 2025-01-22:
https://dashboard.shadowserver.org/statistics/combined/tree/?day=2025-01-22&source=compromised_website&source=compromised_website6&tag=cve-2025-0282%2B&geo=all&data_set=count&scale=log
Data shared daily in our Compromised Website report https://www.shadowserver.org/what-we-do/network-reporting/compromised-website-report/ tagged 'backdoor;ivanti-connect-secure'
Make sure to investigate your Ivanti Connect Secure instance if you receive an alert from us! @cisacyber mitigation advice is a good start https://www.cisa.gov/cisa-mitigation-instructions-cve-2025-0282
Thank you to @certfi for the insights and detection methods!
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgYesterday a user told me they couldn't log in to my parliamentary monitoring site. On investigating, I found that Microsoft email security was logging in on behalf of my user by executing a POST. This broke the single-use sign-on link. Executing POSTs is usually considered unacceptable, and in this way Microsoft again transgresses an important norm. Here's how to deal with the specific POST problem & what might be done about these transgressions in general:
https://berthub.eu/articles/posts/shifting-cyber-norms-microsoft-post/