Posts
2476Following
656Followers
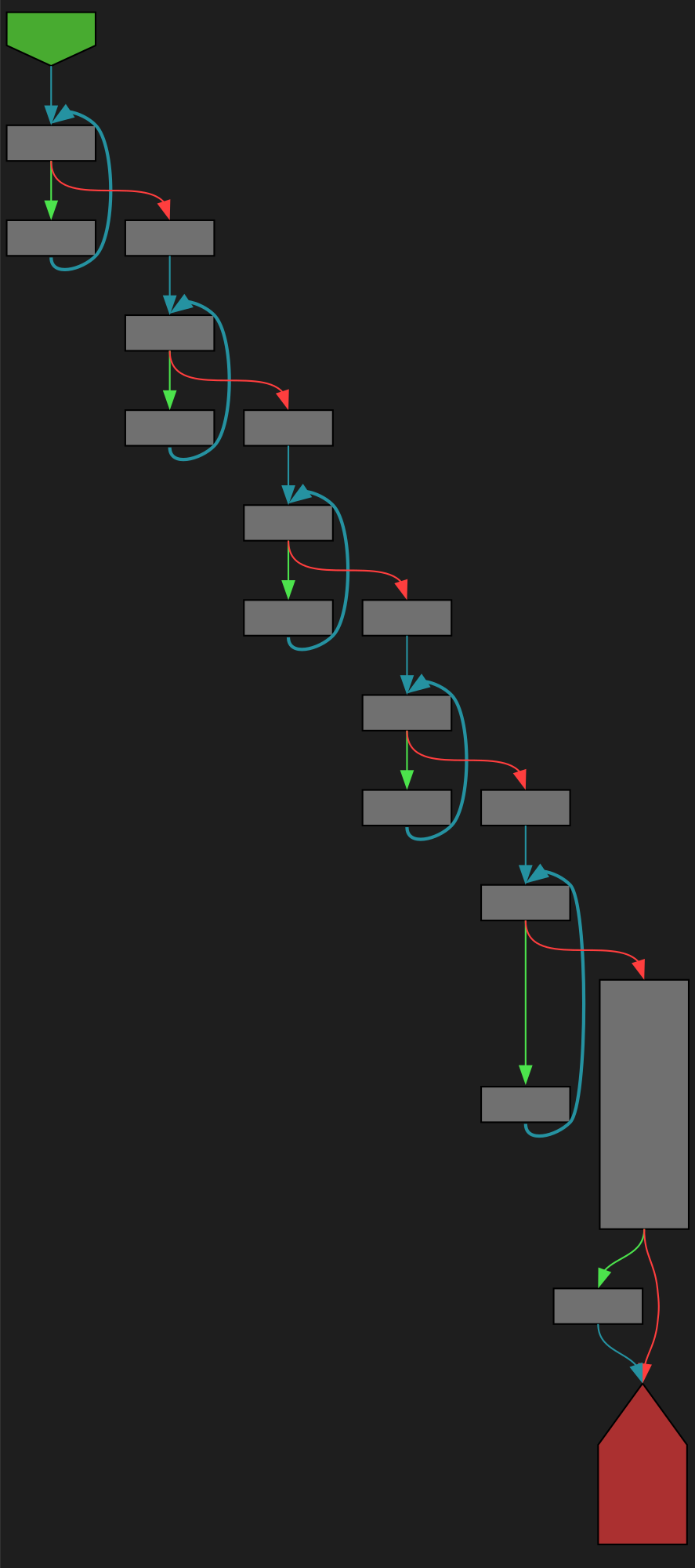
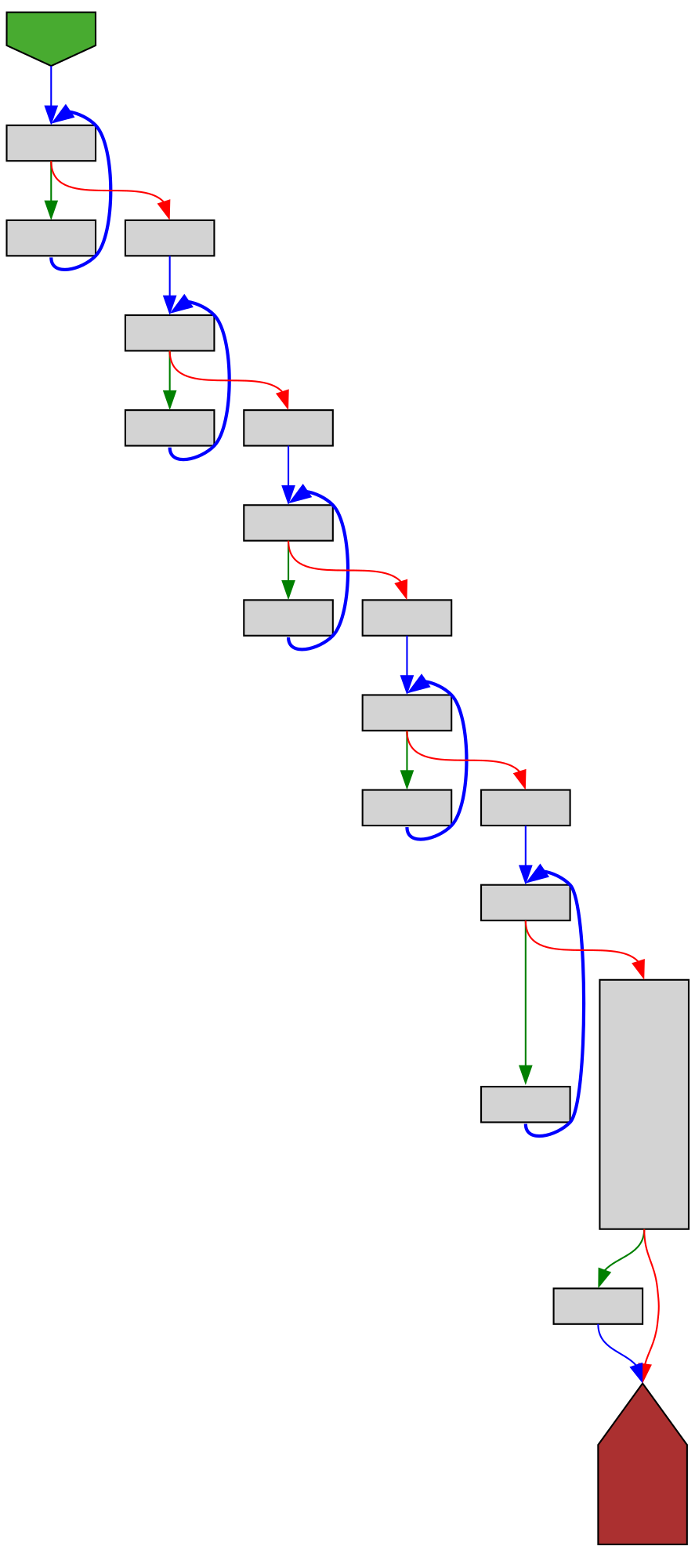
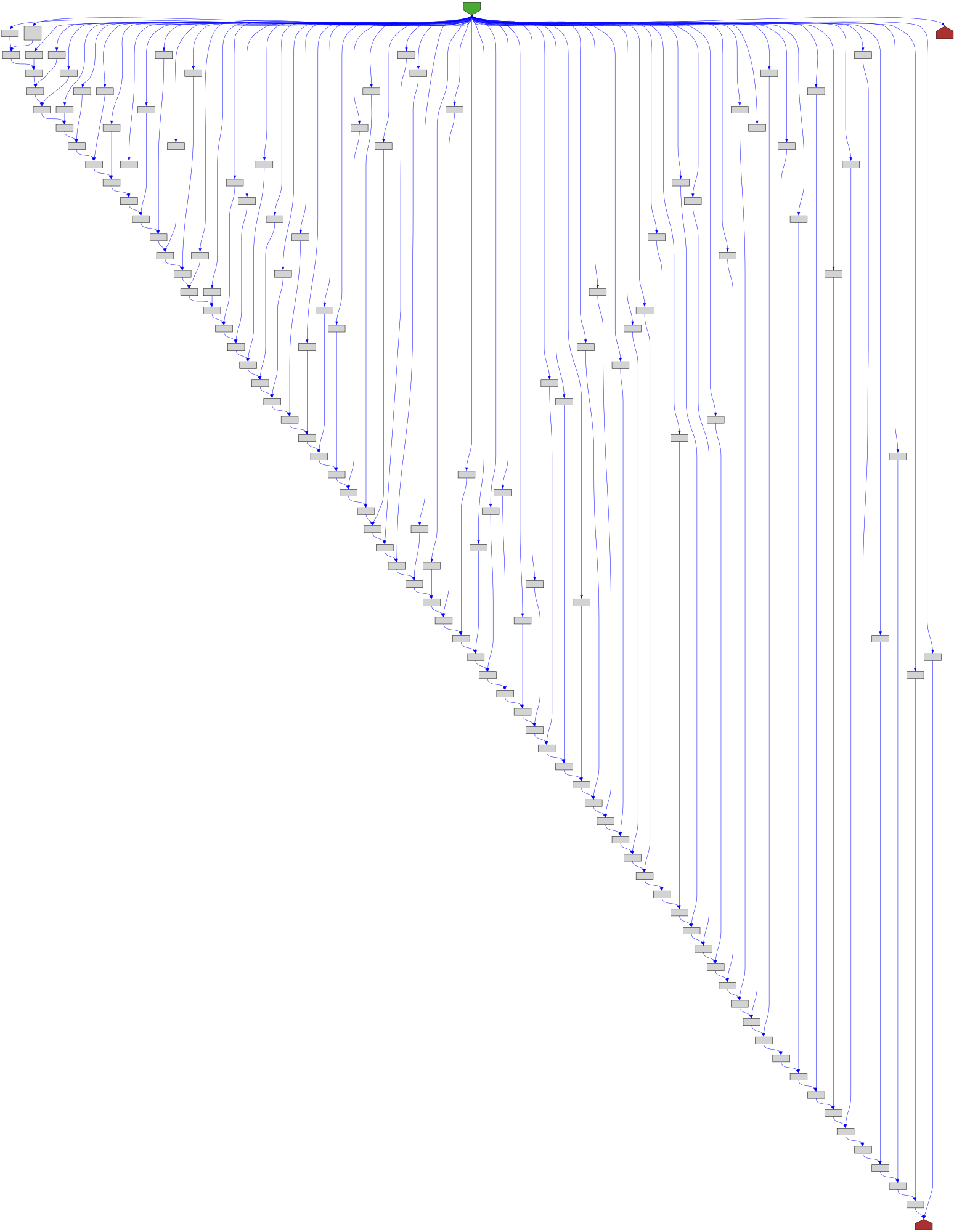
1478CFG Bot 🤖
cfgbot@mastodon.socialProject: golang/go https://github.com/golang/go
File: src/cmd/vendor/github.com/google/pprof/profile/encode.go:132 https://github.com/golang/go/blob/refs/tags/go1.23.4/src/cmd/vendor/github.com/google/pprof/profile/encode.go#L132
func (p *Profile) encode(b *buffer)
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgithub.com%2Fgoogle%2Fpprof%2Fprofile%2Fencode.go%23L132&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fvendor%2Fgithub.com%2Fgoogle%2Fpprof%2Fprofile%2Fencode.go%23L132&colors=light
buherator
buheratorhttps://starlabs.sg/blog/2025/cve-2024-26230-windows-telephony-service-its-got-some-call-ing-issues/
lcamtuf 


lcamtuf@infosec.exchange
UI is hell, or why you can't design a four-function calculator: https://lcamtuf.substack.com/p/ui-is-hell-four-function-calculators
buherator
buheratorhttps://www.cisa.gov/news-events/alerts/2025/01/23/cisa-adds-one-known-exploited-vulnerability-catalog
The KEV page quotes (emphasis mine): "JQuery contains a *persistent* cross-site scripting (XSS) vulnerability" so this still doesn't seem to meet the bar for my XSS Reflections list:
https://github.com/v-p-b/xss-reflections
If anybody has more info about the related incident please lmk!
Trend Zero Day Initiative
thezdi@infosec.exchangeAnd that’s a wrap! #Pwn2Own Automotive 2025 is complete. In total, we awarded $886,250 for 49 0-days over the three day competition. With 30.5 points and $222,250 awarded, Sina Kheirkhah (@SinSinology) of Summoning Team (@SummoningTeam) is our Master of Pwn. #P2OAuto
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250123-00/?p=110800
Full system instrumentation ftw :)
Soatok Dreamseeker
soatok@furry.engineerEvery once in a while I have a really stupid idea, and then I sit down to write out what it would look like, and immediately spot a flaw in it that renders the whole thing insecure.
One of these days, one of my bad ideas is going to look back at me as someone else's implementation, deployed to production.
/r/netsec
_r_netsec@infosec.exchangeWinVisor: A proof-of-concept hypervisor-based emulator for Windows x64 binaries https://www.elastic.co/security-labs/winvisor-hypervisor-based-emulator
The Shadowserver Foundation
shadowserver@infosec.exchangeWe are sharing backdoored Ivanti Connect Secure devices that *may* have been compromised as part of a CVE-2025-0282 exploitation campaign (but also we believe may include older or other activity).
379 new backdoored instances found on 2025-01-22:
https://dashboard.shadowserver.org/statistics/combined/tree/?day=2025-01-22&source=compromised_website&source=compromised_website6&tag=cve-2025-0282%2B&geo=all&data_set=count&scale=log
Data shared daily in our Compromised Website report https://www.shadowserver.org/what-we-do/network-reporting/compromised-website-report/ tagged 'backdoor;ivanti-connect-secure'
Make sure to investigate your Ivanti Connect Secure instance if you receive an alert from us! @cisacyber mitigation advice is a good start https://www.cisa.gov/cisa-mitigation-instructions-cve-2025-0282
Thank you to @certfi for the insights and detection methods!
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgYesterday a user told me they couldn't log in to my parliamentary monitoring site. On investigating, I found that Microsoft email security was logging in on behalf of my user by executing a POST. This broke the single-use sign-on link. Executing POSTs is usually considered unacceptable, and in this way Microsoft again transgresses an important norm. Here's how to deal with the specific POST problem & what might be done about these transgressions in general:
https://berthub.eu/articles/posts/shifting-cyber-norms-microsoft-post/
Daniel Chateau  (シャトー・ダニエル)
(シャトー・ダニエル)
djchateau@infosec.exchange
Shitposting is valid pentesting apparently.
https://www.reddit.com/r/csMajors/comments/1i7v7hg/my_teams_intern_just_found_a_critical_bug_by/
hackaday
hackaday@hackaday.socialShellcode over MIDI? Bad Apple on a PSR-E433, Kinda
https://hackaday.com/2025/01/23/shellcode-over-midi-bad-apple-on-a-psr-e433-kinda/
Dr. Christopher Kunz
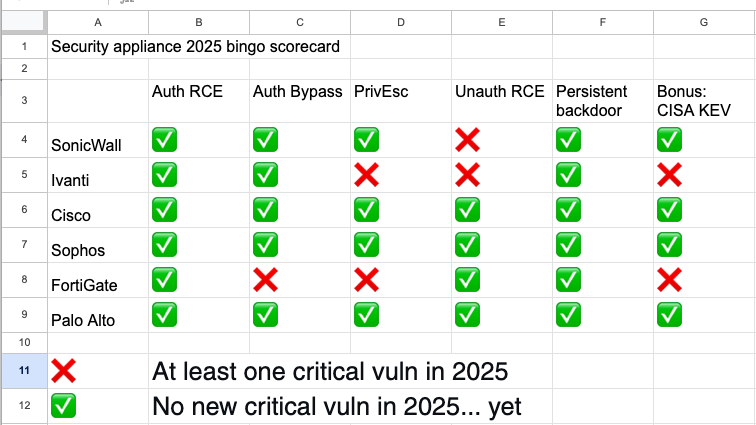
christopherkunz@chaos.social...and here we go: Next entry in our bingo card is CVE-2025-23006 in SonicWall SMA1000.
Thanks, everyone, and remember: Current version lives at https://cku.gt/appbingo25
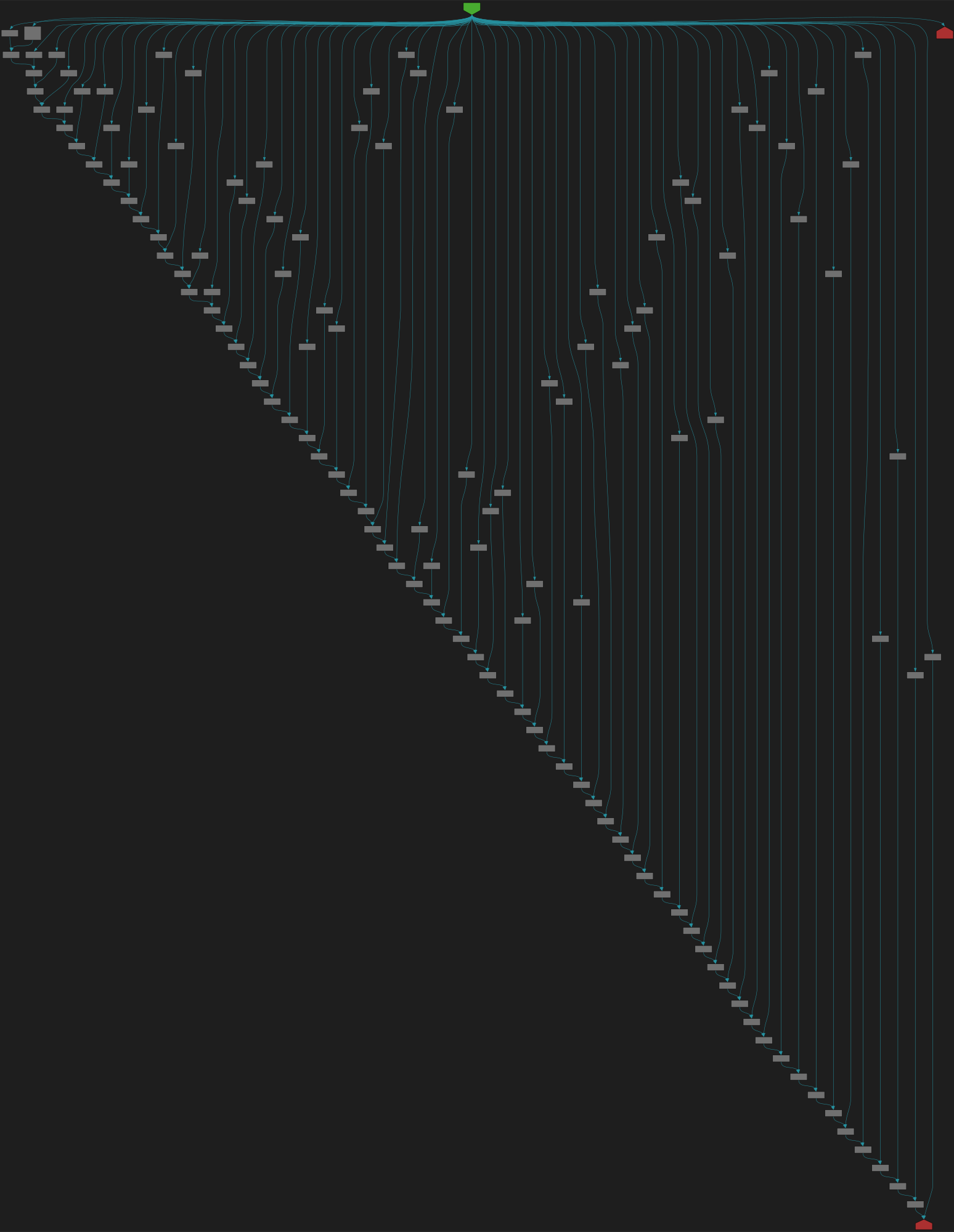
CFG Bot 🤖
cfgbot@mastodon.socialProject: microsoft/TypeScript https://github.com/microsoft/TypeScript
File: src/compiler/utilities.ts:4463 https://github.com/microsoft/TypeScript/blob/cbac1ddfc73ca3b9d8741c1b51b74663a0f24695/src/compiler/utilities.ts#L4463
function canHaveJSDoc(node: Node): node is HasJSDoc
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fmicrosoft%2FTypeScript%2Fblob%2Fcbac1ddfc73ca3b9d8741c1b51b74663a0f24695%2Fsrc%2Fcompiler%2Futilities.ts%23L4463&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fmicrosoft%2FTypeScript%2Fblob%2Fcbac1ddfc73ca3b9d8741c1b51b74663a0f24695%2Fsrc%2Fcompiler%2Futilities.ts%23L4463&colors=light
screaminggoat
screaminggoat@infosec.exchangeSonicWall exploited zero-day: SMA1000 Pre-Authentication Remote Command Execution Vulnerability
CVE-2025-23006 (9.8 critical) Pre-authentication deserialization of untrusted data vulnerability has been identified in the SMA1000 Appliance Management Console (AMC) and Central Management Console (CMC), which in specific conditions could potentially enable a remote unauthenticated attacker to execute arbitrary OS commands.
IMPORTANT: SonicWall PSIRT has been notified of possible active exploitation of the referenced vulnerability by threat actors
cc: @goatyell @cR0w @GossiTheDog @briankrebs
#zeroday #CVE_2025_23006 #sonicwall #vulnerability #CVE #infosec #cybersecurity #eitw #activeexploitation