Posts
4015Following
731Followers
1614buherator
buheratorhttps://blog.includesecurity.com/2024/11/spelunking-in-comments-and-documentation-for-security-footguns/
#elixir #python #go
buherator
buheratorhttps://www.synacktiv.com/en/publications/relaying-kerberos-over-smb-using-krbrelayx
David Weston (DWIZZZLE)
dwizzzlemsft@bird.makeupMy team just released a paper detailing all the security capabilites in Windows Server 2025
https://techcommunity.microsoft.com/blog/microsoftsecurityandcompliance/windows-server-2025-security-book/4283981
@mikko
mikko@bird.makeupThank You to the guests who joined the opening of the Museum of Malware Art! The museum is now open to the public. For hours and more information, see https://MuseumofMalware.Art
Kim Scheinberg
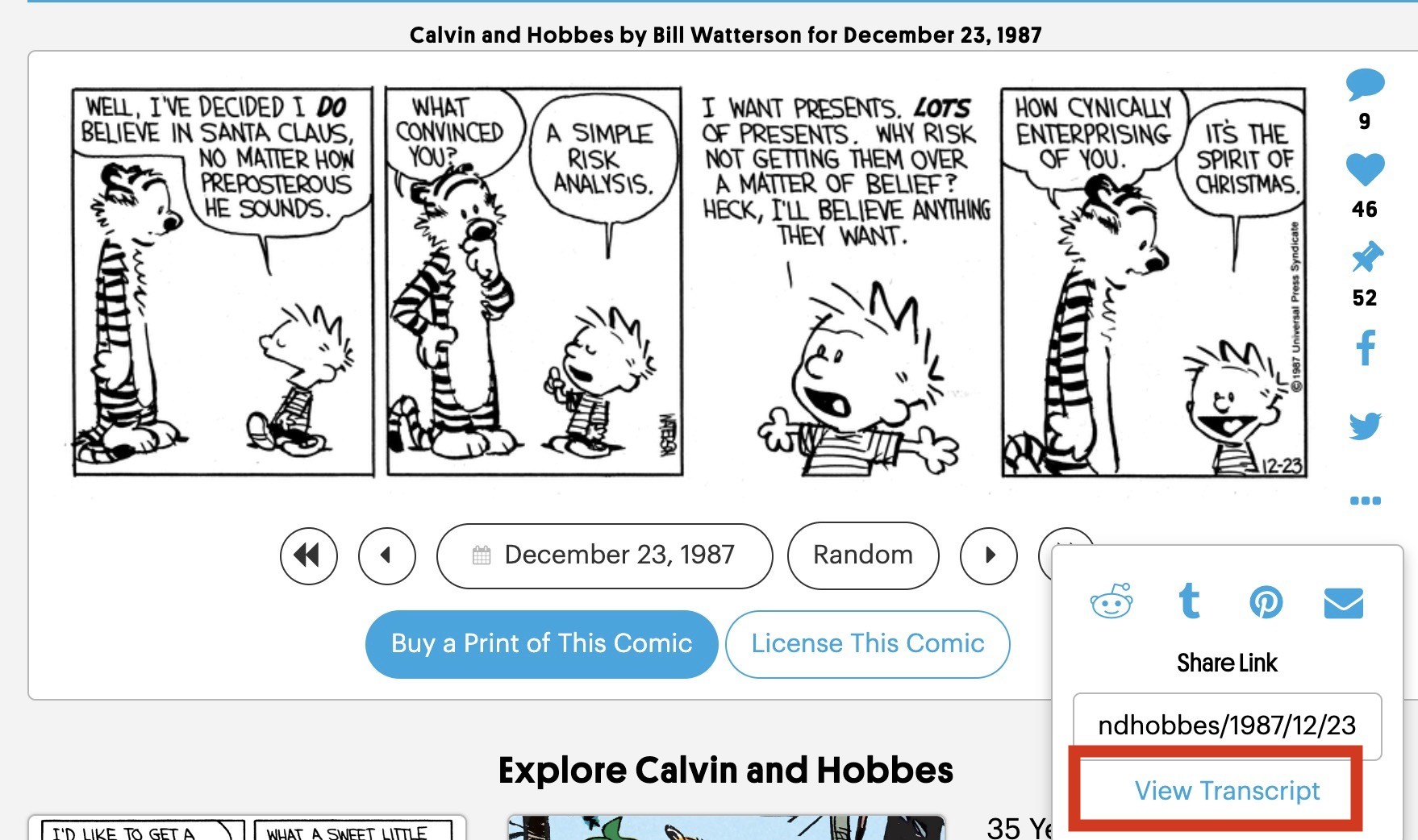
kims@mas.toSince Calvin and Hobbes are popular right now, please know that the entire archive is available online, searchable, for free. This includes ALL the strips, including some that didn't make it into the various anthologies:
https://www.gocomics.com/calvinandhobbes
And if you are insistent on using alt text but are (like me) sometimes not motivated to type out the dialogue, there's even a 'transcript' button in the three-dot submenu. It's short on describing images, but it's thorough on the text.
Alex Plaskett
alexjplaskett@bird.makeup✍️ A Ghidra nanoMIPS ISA module by @jamchamb_
https://www.nccgroup.com/us/research-blog/ghidra-nanomips-isa-module/
/r/netsec
_r_netsec@infosec.exchangeWormable XSS www.bing.com https://medium.com/@pedbap/wormable-xss-www-bing-com-7d7cb52e7a12
dragosr
dragosr@chaos.socialD-Link tells users to trash old VPN routers over bug too dangerous to identify.
Hopefully folks realize they should replace it with another vendor.
This vuln was covered at DEF CON 32 by Sam Curry. TR-069 is an admin access protocol that lets DLink work with your router remotely (reset device, etc.). Bad actors use spoofed requests to change config data, read the MAC address, monitor traffic, and use them as botnets. TR-069 is industry standard
https://www.theregister.com/2024/11/20/dlink_rip_replace_router/
Wade Baker
wade@infosec.exchangeI'm fascinated by the concept of measuring attacker-defender advantage in software, devices, and even entire IT environments. What do I mean by "attacker-defender advantage?" Lemme sum up and then share a chart.
Let's say you could measure the speed at which defenders remediate various types of security vulnerabilities across all relevant assets. Then say you could detect and measure the speed at which attackers find/exploit those vulnerable assets across the target population of organizations using them. Finally, plot those curves (across time and assets) to see the delta between them and derive a measure of relative advantage for attackers and defenders. That relative value is what I mean by attacker-defender advantage.
Since a picture is worth a thousand words, here's a visual example of the concept. The blue line represents defenders, measuring the speed of remediation. Red measures how attacker exploitation activity spreads across the target population. When the blue line is on top, defenders have a relative advantage (remediating faster than attackers are attempting to exploit new targets). When red's on top, the opposite is true. The delta between the lines corresponds to the relative degree of advantage (also expressed by the number in the upper left).
This chart comes from prior Cyentia Institute research in which we were able to combine datasets from two different partners (with their permission). Unfortunately, those datasets/partners are no longer available to further explore this concept - but maybe this post will inspire new partnerships and opportunities!
Any surprises in the attacker-defender advantage results depicted in the chart? Has anyone measured this or something similar?
#cybersecurity #vulnerabilities #cyberattacks #infosec #exploitation
XBOW bypasses a MIME-type filter, abusing an OTP icon preview feature in 2FAuth to exploit an SSRF and discover CVE 2024-52598. Affected users should apply the patch and read about all the details in our blog post this Friday.
screaminggoat
screaminggoat@infosec.exchangeCISA: CISA Adds Two Known Exploited Vulnerabilities to Catalog
- CVE-2024-38812 (9.8 critical) VMware vCenter Server heap-overflow vulnerability
- CVE-2024-38813 (7.5 high) VMware vCenter privilege escalation vulnerability
#cisa #kev #cisakev #knownexploitedvulnerabilitiescatalog #vmware #vcenter #vulnerability #eitw #activeexploitation #infosec #cybersecurity
MITRE ATT&CK
mitreattack@infosec.exchangeWe’re excited to introduce our new TAXII server and the latest addition to the ATT&CK Workbench software suite: the MITRE ATT&CK Workbench TAXII 2.1 Server:
https://medium.com/mitre-attack/introducing-taxii-2-1-and-a-fond-farewell-to-taxii-2-0-d9fca6ce4c58
Joseph Cox
josephcox@infosec.exchangeNew from 404 Media: we've obtained and published the list of iPhone and Android devices secretive phone unlocking tech Graykey was able, or unable, to get data from recently. Unprecedented leak, we've never seen this granularity from Graykey before https://www.404media.co/leaked-documents-show-what-phones-secretive-tech-graykey-can-unlock-2/
Jerry 🦙💝🦙
jerry@infosec.exchangeI’ve been getting a number of phishing emails purporting to be from Hetzner saying my payment into needs to be updated. It’s interesting excuse they targeting email addresses that are plausibly associated with my various fediverse service domains. The from addresses are nonsensical, and the link to login Hetzner are easy give away that it’s a scam.
Anyhow, please be on alert if you use Hetzner. I am guessing the play here is to steal your Hetzner login credentials, and (probably) payment information. Hetzner does have an alert in their portal about phishing attacks purporting to be from them so I think they are aware, though I found the targeting to be a bit novel.
Stay safe out there.
buherator
buheratorhttps://community.ibm.com/community/user/power/blogs/val-besong/2024/11/12/ibm-power-modernizes-infrastructure-and-accelerate
buherator
buheratorhttps://blog.securelayer7.net/coldfusion-path-traversal-and-weblogic-unauthenticated-rce-remediation/
AttackerKB
attackerkbTopic description: "An authentication bypass in Palo Alto Networks PAN-OS software enables an unauthenticated attacker with network access to the management web interface to gain PAN-OS administrator privileges to perform administrative actions, tamper with the configuration, or exploit other authenticated privilege escalation vulnerabilities like CVE-2024-9474 https://security.paloaltonetworks.com/CVE-2024-9474 . ..."
"Based upon writing a [Metasploit exploit module](https://github.com/rapid7/metasploit-framework/pull/19663) for this exploit chain, I have rated the exploitability of this as very easy, as a target PAN-OS management interface is vulnerable in a default configuration. ..."
Link: https://attackerkb.com/assessments/a360309b-1a6e-424c-961a-f7dfb48113d7
TROOPERS Conference
WEareTROOPERS@infosec.exchangeHello #TROOPERS, we have opened the cfp (https://troopers.de/troopers25/contribute/) and ticket shop for next year's #TROOPERS25! Get your early bird until January 31st. Hope to see you in Heidelberg next near in June and looking forward to all your submissions!