Posts
3686Following
724Followers
1595buherator
buheratorhttps://video.infosec.exchange/w/jtR1V9N5ghHES5oayeBrrd
Did I miss anything?
#NoCVE
buherator
buheratorShow content
https://blog.mollywhite.net/binance-script/
buherator
buheratorhttps://www.youtube.com/watch?v=dnHdqPBrtH8
Again, it's all about incentives...
Christopher
kharosx0@bird.makeupKASAN is now available for your own Windows Drivers: https://learn.microsoft.com/en-us/windows-hardware/drivers/devtest/kasan
Oh God, yes! When starting a qemu instance, you can pass it an fd on the command line for its listening socket for that chardev.
You can also tell it to listen on a TCP or UNIX socket, but as the starting process, you now need to try and connect multiple times until qemu is finally started and opened its listening socket. It also might never connect in case qemu fails to start. This is really annoying to handle properly in your code.
With the fd-passing, the parent process can create the listening socket, clear CLOEXEC on the socket, pass it to qemu and then connect to it. At that time it will either be open already or if qemu fails to start, the listening socket will be gone and the connect() fails.
I haven't tried it yet, but I need it for work and it sounds like a proper solution to a really annoying problem.
https://patchwork.kernel.org/project/qemu-devel/patch/20180205152455.12088-10-berrange@redhat.com/
leyrer
leyrer@chaos.socialUnattended children get an IBM System/370 and a Cobol starter lecture.
buherator
buheratorhttps://www.youtube.com/watch?v=piJkuavhV50
#Math
Ivan Ožić Bebek
obivan@infosec.exchangeWindows DWM Core Library Elevation of Privilege Vulnerability (CVE-2024-30051) https://www.coresecurity.com/core-labs/articles/windows-dwm-core-library-elevation-privilege-vulnerability-cve-2024-30051
Binary Ninja
binaryninja@infosec.exchangeWant to know more about the reverse engineering community? Šárka and Brent break down the 2024 results from our annual Reverse Engineering Survey in our latest blog post:
jiska 🦄
jiska@chaos.social
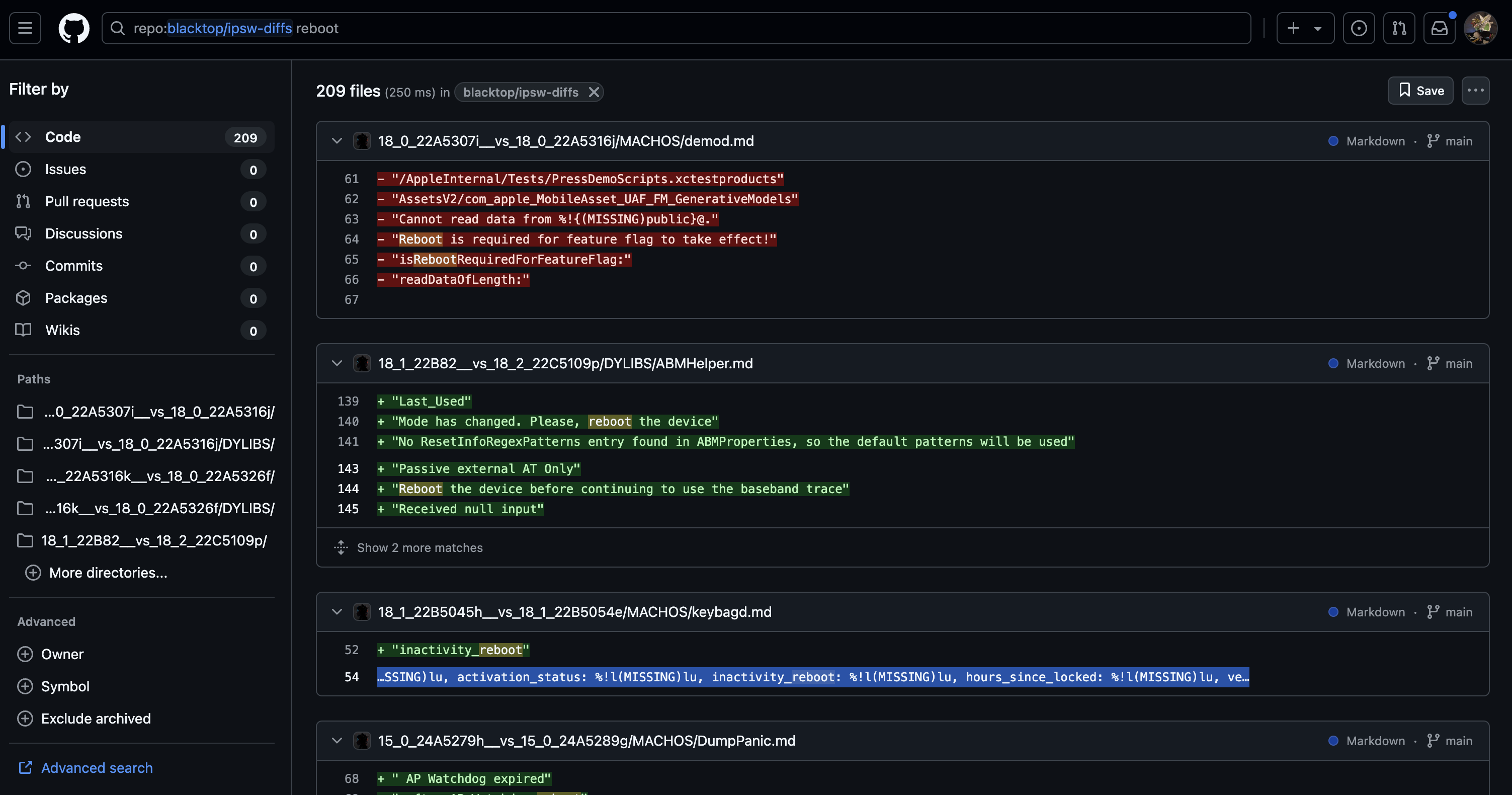
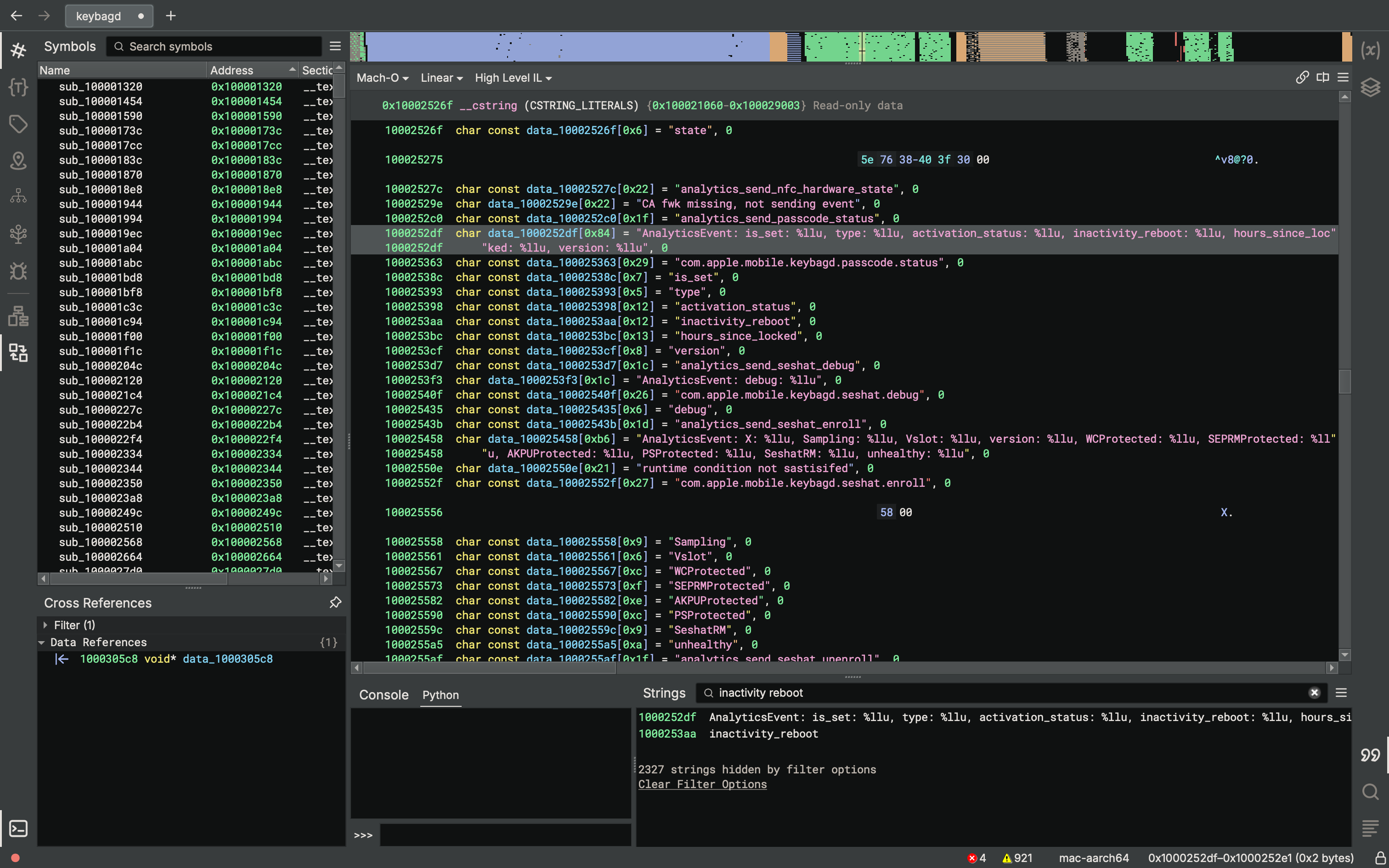
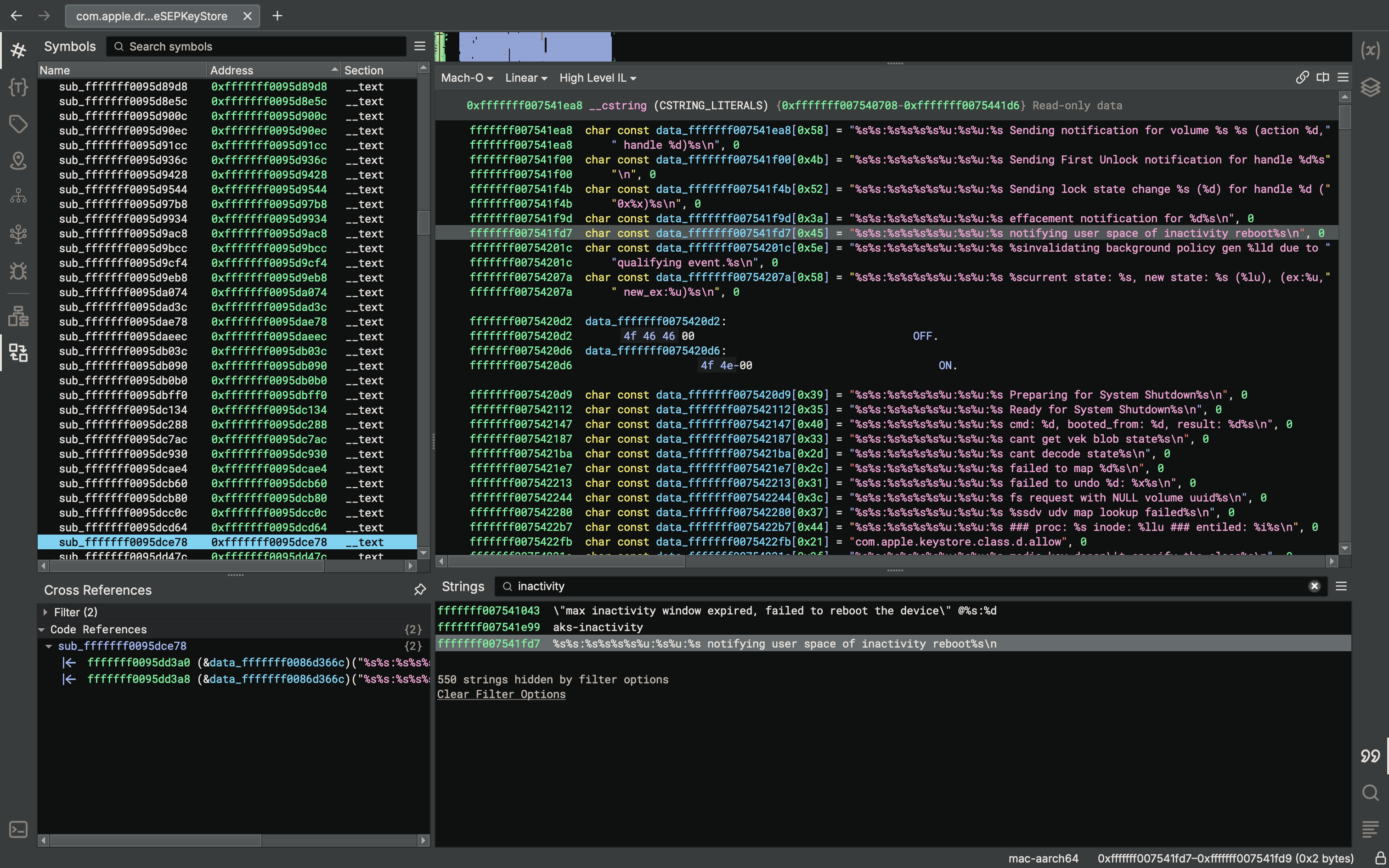
Apple added a feature called "inactivity reboot" in iOS 18.1. This is implemented in keybagd and the AppleSEPKeyStore kernel extension. It seems to have nothing to do with phone/wireless network state. Keystore is used when unlocking the device. So if you don't unlock your iPhone for a while... it will reboot!
In the news: "Police Freak Out at iPhones Mysteriously Rebooting Themselves, Locking Cops Out"
https://www.404media.co/police-freak-out-at-iphones-mysteriously-rebooting-themselves-locking-cops-out/
iOS version diffs to see yourself:
https://github.com/search?q=repo%3Ablacktop%2Fipsw-diffs%20inactivity_reboot&type=code
Csaba Fitzl
theevilbit@mastodon.social🍎🐛🎙️Following my #poc2024 talk we are releasing a blogpost series at Kandji, detailing the vulnerabilities of diskarbitrationd and storagekitd I discussed in my "Apple Disk-O Party" talk.
First part is out, and covers CVE-2024-44175.
screaminggoat
screaminggoat@infosec.exchangeVeeam security advisory from 06 November 2024 Veeam Backup Enterprise Manager Vulnerability (CVE-2024-40715)
CVE-2024-40715 (7.7 high) Veeam Backup & Replication Enterprise Manager authentication bypass. No mention of exploitation.
#cybersecurity #infosec #vulnerability #CVE #veeam #cve_2024_40715
The contrast between two CUPS vulns is amazing. This one, CVE-2024-35235, seems to have flown completely under the radar - in total contrast to CVE-2024-47176. It was an LPE with an exploit chain that sounds very reliable. I only heard about it for the first time today.
Sonar Research
SonarResearch@infosec.exchangeIn case you missed it, here's the recording of our #HEXACON2024 talk "Exploiting File Writes in Hardened Environments"!
It's a short and sweet 30-minute talk, so grab a coffee and sit back while @scryh goes from HTTP request to ROP chain in Node.js ☕
screaminggoat
screaminggoat@infosec.exchangePalo Alto Networks Security Advisory: PAN-SA-2024-0015 Important Informational Bulletin: Ensure Access to Management Interface is Secured
Palo Alto Networks is aware of a claim of a remote code execution vulnerability via the PAN-OS management interface. They do not know the specifics of the claimed vulnerability.
We strongly recommend customers to ensure access to your management interface is configured correctly in accordance with our recommended best practice deployment guidelines. In particular, we recommend that you ensure that access to the management interface is possible only from trusted internal IPs and not from the Internet. The vast majority of firewalls already follow this Palo Alto Networks and industry best practice.
#vulnerability #paloaltonetworks #paloalto #pan #panos #cybersecurity #infosec
Yarden Shafir
yarden_shafir@bird.makeupPlease make this happen. I would love nothing more than to have an image parser run during a bugcheck
buherator
buheratorhttps://jericho.blog/2024/11/07/was-it-really-gpac-no-getting-a-cve-removed-from-cisa-kev/
buherator
buheratorhttps://www.usenix.org/conference/woot24/presentation/brossard
%27In this article, we introduce the notions of "libification" and "procedural debugging" to facilitate partial debugging of binaries at the procedural level. These techniques allow the transformation of arbitrary dynamically linked ELF binaries into shared libraries, and the study of memory corruption bugs by directly calling the vulnerable functions, hence separating the memory corruption intraprocedural analysis from the reachability problem. %27
buherator
buheratorhttps://github.com/kagisearch/bangs/pull/125