Posts
3539Following
721Followers
1583Paul Cantrell
inthehands@hachyderm.ioI’m a software developer with a bunch of industry experience. I’m also a comp sci professor, and whenever a CS alum working in industry comes to talk to the students, I always like to ask, “What do you wish you’d taken more of in college?”
Almost without exception, they answer, “Writing.”
One of them said, “I do more writing at Google now than I did when I was in college.”
I am therefore begging, begging you to listen to @stephstephking: https://mstdn.social/@stephstephking/113336270193370876
buherator
buheratorrat (determined empirically)
rolenthedeep@rattodon.nexusIt's interesting to think that "my browser doesn't work with this website" used to mean "my browser is out of date". Now it means "someone intentionally broke this website for my browser because it supports ad blocking"
Extinction Rebellion Global
ExtinctionR@social.rebellion.globalgrsecurity
grsecurity@infosec.exchangeIn combination with the research published yesterday by ETHZ into IBPB implementation vulnerabilities on some Intel and AMD CPUs (https://comsec.ethz.ch/research/microarch/breaking-the-barrier/), Johannes Wikner has published a detailed walkthrough of the first cross-process Spectre exploit against a real target, an attack he developed in part during his internship with us last year.
Check it out here: https://grsecurity.net/cross_process_spectre_exploitation
johannes
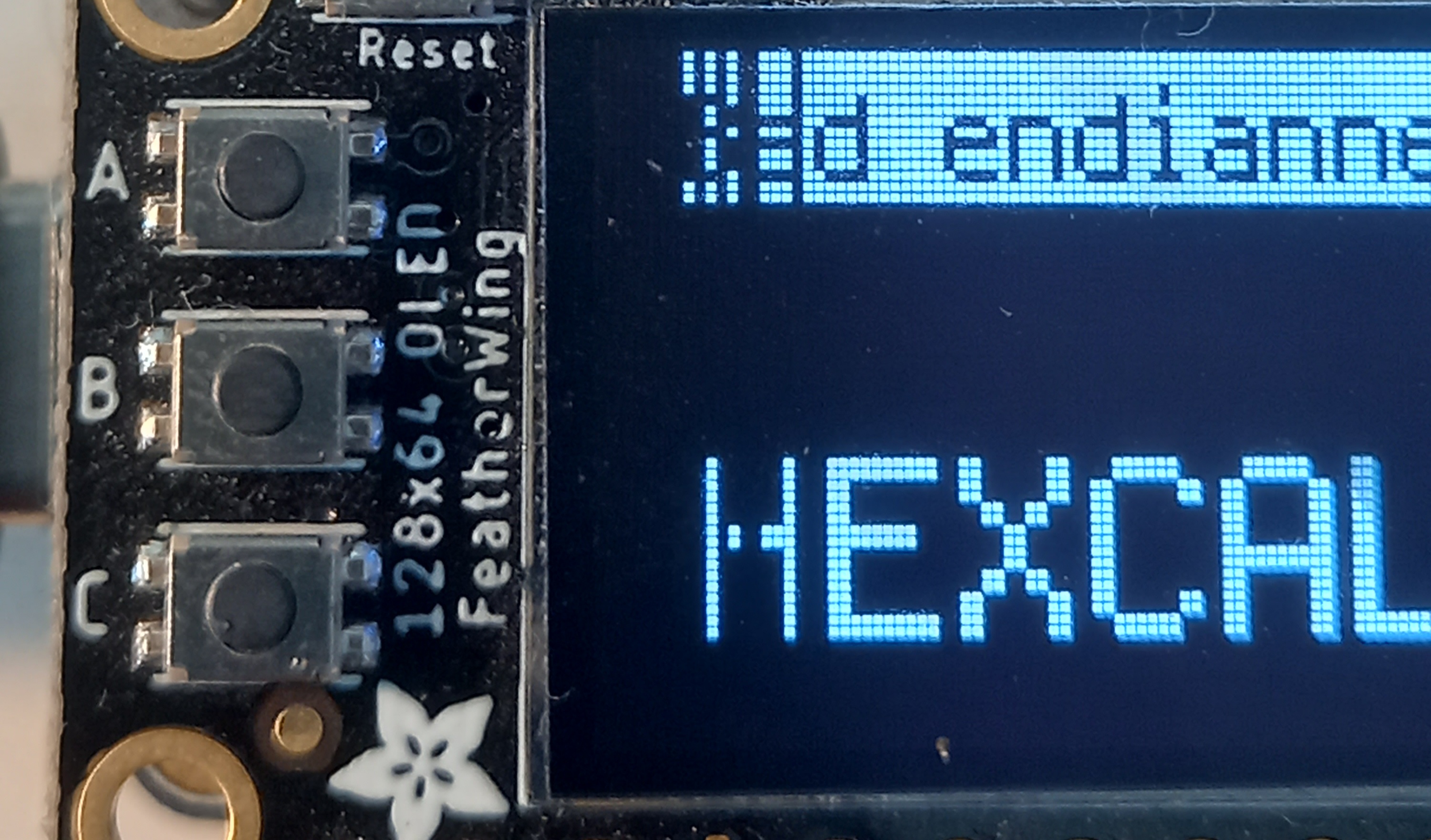
wiknerj@bird.makeupThe first ever end-to-end cross-process Spectre exploit? I worked on this during an internship with @grsecurity! An in-depth write-up here:
https://grsecurity.net/cross_process_spectre_exploitation
Oxide Computer Company
oxidecomputer@hachyderm.ioWe're excited to announce dtrace.conf(24), the premier unconference for all things DTrace! 🎉
📅 Date: December 11th, 2024
📍 Location: Emeryville, CA
As an unconference, the agenda is driven by attendees. Come ready to actively participate!
QCATOPR 
timjclevenger@infosec.exchange
Free System/36 in SoCal. Today only. Please repost. #retrocomputing
HackSys Team
hacksysteam@bird.makeup🚨 We're hiring! 🚨
HackSys Inc. is looking for a full-time Vulnerability Researcher (Windows/Android/Browser) based in India! 🛡️
🔍 Skills:
- Vulnerability classes, C/C++/ASM
- Exploited n-day on Windows/Android/Browser
- Reverse Engineering (WinDbg, IDA, Ghidra)
- Passionate about VR 🔥
Interested? DM @hacksysteam on Discord or Twitter for more details! #Hiring #VulnerabilityResearch #CyberSecurity
abadidea
0xabad1dea@infosec.exchangeAs much as I've been inconvenienced by the Internet Archive being offline this long, I'm proud of them for making up their minds to just keep it down for as long as it takes to make sure everything's fixed and safe before exposing it again. I hope everyone involved is putting in reasonable hours and getting enough sleep.
jeffvanderstoep
jeffvanderstoep@infosec.exchangeI joined @durumcrustulum and @tqbf on the Security Cryptography Whatever podcast to talk about our latest blogpost:
https://securitycryptographywhatever.com/2024/10/15/a-little-bit-of-rust-goes-a-long-way/
https://security.googleblog.com/2024/09/eliminating-memory-safety-vulnerabilities-Android.html
Something that Thomas said in the podcast really stood out to me. He said “the blog post undersells it. …. This is a lot more interesting than it looks like on the tin.”
I agree with this. It feels like we discovered a game-changer not just in memory safety, but in security more generally - that doing something very practical results in major security improvements for non-obvious reasons. Focusing on new code is disproportionately effective, exponentially.
Thomas also said “And that observation about the half life of vulnerabilities, if that’s true, says something pretty profound about what the work looks like to shift to a memory safe future.”
Or as Deidre said: “You can get really big bang for your buck, which is if you have something new, just write it in the Rust or another memory safe language and make it interop with the rest of your project and you will in fact, get really good returns on mitigating your memory safe vulnerabilities, which is the majority of your vulnerabilities, period.”
Agreed. We’re already prioritizing differently based on this data. It was a fun conversation, and we believe that it applies to a lot more than just memory safety.
CISA is looking for feedback on its "Secure by design" initiative draft doc.
https://www.infosecurity-magazine.com/news/cisa-product-security-flaws/
Elizabeth Laraki
elizlaraki@bird.makeupI'm talking at a conference later this year (on UX+AI).
I just saw an ad for the conference with my photo and was like, wait, that doesn't look right.
Is my bra showing in my profile pic and I've never noticed...? That's weird.
I open my original photo.
No bra showing.
I put the two photos side by side and I'm like WTF...
Someone edited my photo to unbutton my blouse and reveal a made-up hint of a bra or something else underneath. 🤨
Immediately, I email the conference host.
(FYI he is a great, respectable guy with 5 kids at home.)
He is super apologetic and immediately looks into the issue.
He quickly reports back that the woman running their social media used a cropped square image from their website.
She needed it to be more vertical, so she used an AI expand image tool to make the photo taller.
AI invented the bottom part of the image (in which it believed that women's shirts should be unbuttoned further, with some tension around the buttons, and revealing a little hint of something underneath). 🤯
—
FYI the conference organizers were super apologetic and took down all of the content with that photo.
Anderson Nascimento
andersonc0d3@infosec.exchangeUndefinedBehaviorSanitizer’s unexpected behavior
https://daniel.haxx.se/blog/2024/10/17/undefinedbehaviorsanitizers-unexpected-behavior/
buherator
buheratorhttps://hackaday.com/2024/10/16/linus-live-codes-music-on-the-commodore-64/
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20241016-00/?p=110378