Posts
3178Following
705Followers
1561buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20241001-22/?p=110330
buherator
buheratorhttps://hackaday.com/2024/10/01/java-ring-one-wearable-to-rule-all-authentications/
buherator
buheratorhttps://cyberscoop.com/nso-group-court-filing-apple-lawsuit/
adam_cyber
adam_cyber@bird.makeupThis was a fun podcast with @aionescu discussing all things kernel: https://podcasts.apple.com/us/podcast/adversary-universe-podcast/id1694819239?i=1000671431945
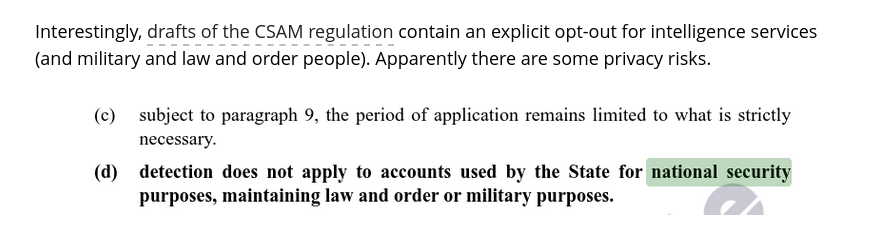
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgI love this part also. The #CSAM regulation proposal is full of how it is all great for privacy, and then it hits you with this. Apparently this is scanning of all OUR photos, not of theirs: https://www.patrick-breyer.de/wp-content/uploads/2024/10/2024-10-01-conseil-hu-csam-proposition-approche-generale-24-septembre.pdf
HN Security
hnsec@infosec.exchangeThe second article in our new series on #Windows #kernel #driver #vulnerability research and #exploitation is out!
Exploiting #AMD atdcm64a.sys arbitrary pointer dereference - Part 2:
https://security.humanativaspa.it/exploiting-amd-atdcm64a-sys-arbitrary-pointer-dereference-part-2/
This time, @ale98 covers how to craft PoCs for the arbitrary MSR read and arbitrary pointer dereference vulnerabilities described in his previous article, with step-by-step advice for debugging with #IDAPro.
Enjoy... and stay tuned for the third and last article next week.
Andrea Barisani
lcars@infosec.exchangeMy TamaGo talk at the recent @osfc_io is now online, if you are interested check it out!
https://www.osfc.io/2024/talks/tamago-bare-metal-go-for-arm-risc-v-socs/
Ivan Kwiatkowski
justicerage@infosec.exchangeIf you're using @zimbra, mass-exploitation of CVE-2024-45519 has begun. Patch yesterday.
Malicious emails are coming from 79.124.49[.]86 and attempting to curl a file from that IP.
buherator
buheratorhttps://github.com/google/security-research/security/advisories/GHSA-q9wq-xc9h-xrw9
buherator
buheratorhttps://blog.projectdiscovery.io/zimbra-remote-code-execution/
buherator
buheratorhttps://binary.ninja/2024/10/01/plugin-spotlight-coolsigmaker.html
Joxean Koret (@matalaz)
joxean@mastodon.socialA friend of mine (@GabrielGonzalez) has written a book about "Attacking and Securing U-Boot".
https://www.amazon.com/Attacking-Securing-U-Boot-Gabriel-Gonzalez/dp/B0DJ7M2JNN
Ange
Ange@mastodon.socialAn awesome video of live coding 6502 asm directly in Basic to produce music, with all the explanations on the way.
https://www.youtube.com/watch?v=ly5BhGOt2vE
/r/netsec
_r_netsec@infosec.exchangeVesta Admin Takeover: Exploiting Reduced Seed Entropy in bash $RANDOM https://fortbridge.co.uk/research/vesta-admin-takeover-exploiting-reduced-seed-entropy-in-bash-random/
bert hubert 🇺🇦🇪🇺🇺🇦
bert_hubert@fosstodon.orgPro-tip if you are searching for anything HTML, CSS or JavaScript related: add "mdn" to your query. This Mozilla project really is a work of love, maintained by hundreds of volunteers @openwebdocs and @MDN staff and contractors. https://developer.mozilla.org/en-US/docs/Learn
buherator
buheratorhttps://www.talospace.com/2024/09/music-production-on-power-adventure-in.html
:O
buherator
buheratorhttps://blog.convisoappsec.com/en/finding-classes-to-exploit-insecure-unchecked-vulnerabilities-in-java-with-joern/