Posts
2461Following
661Followers
1486Project Gutenberg
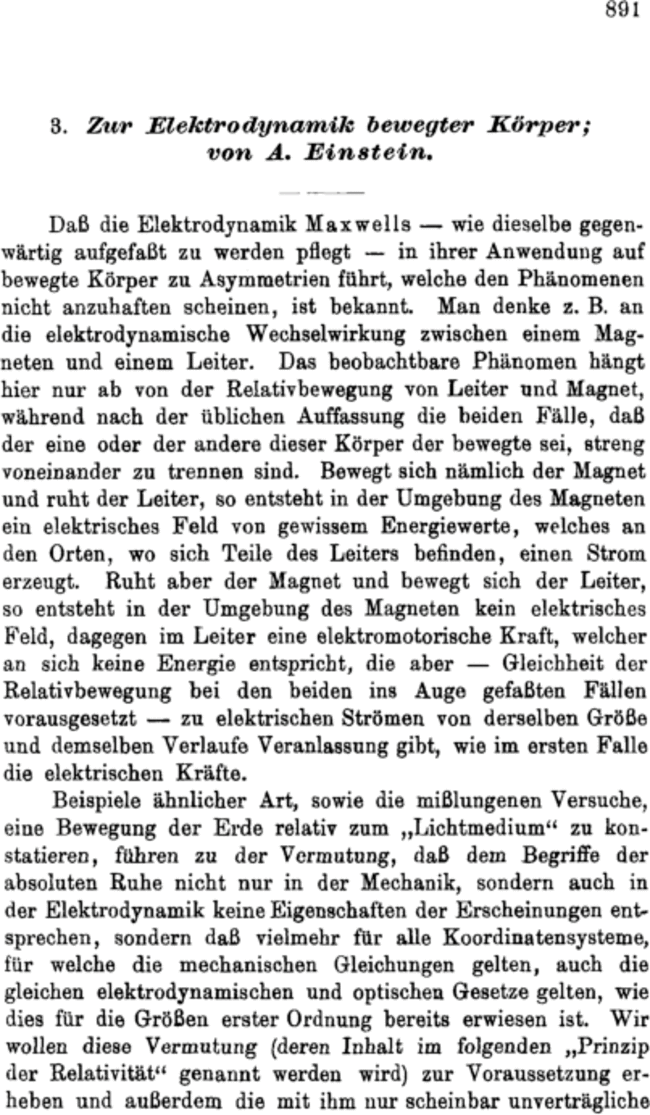
gutenberg_org@mastodon.social#OTD in 1905.
Albert Einstein publishes the third of his Annus Mirabilis papers, introducing the special theory of relativity, which used the universal constant speed of light c to derive the Lorentz transformations.
There are some controversies on the question of the extent to which Mileva Marić contributed to the insights of Einstein's annus mirabilis publications
https://en.wikipedia.org/wiki/Annus_mirabilis_papers#
On the Electrodynamics of Moving Bodies at PG:
https://www.gutenberg.org/ebooks/66944
buherator
buheratorI still have to dig into the works referenced by the recent Google post, but the data is obviously based on known vulns.
https://security.googleblog.com/2024/09/eliminating-memory-safety-vulnerabilities-Android.html
Because of this I think the conclusion shouldn't be that bugs naturally die out ("half-life"). Rather, if we have a fixed set of methods to discover vulns, we will eventually find everything _we currently can_ in a fixed code base, and we will again find some in new code.
I think Orange Tsai's latest work on Apache modules is a great demonstration of how a new approach can result in a bunch of CVE's. But the "realization" about format strings also comes to mind. How much "old" code had to be fixed because of that?
What I'd like to see is some data on memory-safe languages blocking otherwise vulnerable code paths, or vulns getting discovered during integration with safe languages.
Talos Vulnerability Reports
talosvulnsMicrosoft Pragmatic General Multicast Server PgmCloseConnection stale memory dereference
https://talosintelligence.com/vulnerability_reports/TALOS-2024-2062
CVE-2024-38140
jeffvanderstoep
jeffvanderstoep@infosec.exchangeI’m super excited about this blogpost. The approach is so counterintuitive, and yet the results are so much better than anything else that we’ve tried for memory safety. We finally understand why.
https://security.googleblog.com/2024/09/eliminating-memory-safety-vulnerabilities-Android.html
Jonathan Yu
jawnsy@mastodon.social"By turning off your lights all day every day for a month, you conserved about 1 percent of the energy needed for AI to generate a picture of a duck wearing sunglasses. Isn’t he cute? Aside from the fact that he has the feet of a human man, of course."
"By dropping $7K on better, energy-efficient insulation for your home, Google AI was able to tell someone how to prepare chicken incorrectly, and they got, like, super sick—thanks to you!"
Ange
Ange@mastodon.socialOur paper "Magika: AI-powered content-type detection" is up on Arxiv:
https://arxiv.org/abs/2409.13768
c3voc releases
c3voc_releases@chaos.socialEnhancing Security with Systemd: Secure Web Tokens and TPM 2.0 has been released on media.ccc.de and YouTube #asg2024 #MainHall https://media.ccc.de/v/all-systems-go-2024-265-enhancing-security-with-systemd-secure-web-tokens-and-tpm-2-0 https://www.youtube.com/watch?v=NrO-Q_x36U8
buherator
buheratorhttps://www.horizon3.ai/attack-research/cve-2024-28987-solarwinds-web-help-desk-hardcoded-credential-vulnerability-deep-dive/
/r/netsec
_r_netsec@infosec.exchangeCritical Vulnerabilities in WatchGuard SSO Agent https://www.redteam-pentesting.de/advisories/rt-sa-2024-006/
RE//verse Conference
REverseConf@infosec.exchangeThe conference website is live!
https://re-verse.io/
CFP is now open and training tickets are open as well. General ticket sales live in three weeks!
Patrick Gray
riskybusiness@infosec.exchangeThis week's show is up, featuring @metlstorm and special guest co-host @RGB_Lights. Available on YouTube or through your regular podcatcher...
 radare
radare 
radareorg@infosec.exchange
. 🔥 🔥 🔥 🎟️ 🎟️ 🎟️ 🔥 🔥 🔥
#r2con2024 tickets are finally available!
🔥 🔥 🔥 🎟️ 🎟️ 🎟️ 🔥 🔥 🔥
PD: All presentations will be recorded and published online for free. Tickets are only required to physically attend the event.
HN Security
hnsec@infosec.exchangeAfter his popular series on customizing the Sliver C2, our very own @ale98 is back with another series of three articles. This time, the topic is #Windows #kernel #driver #vulnerability #research and #exploitation, inspired by @saidelike’s @OpenSecurityTraining2 courses.
Part 1 is already out:
https://security.humanativaspa.it/exploiting-amd-atdcm64a-sys-arbitrary-pointer-dereference-part-1/
The others will follow shortly in the next weeks.
Amber
Saren42@infosec.exchangeHoly fuck folks. Like Kapersky and their ties to the Russian government suck, yes. Them being banned from doing business in the US probably needed to be done. But folks, them installing UltraAV and uninstalling Kapersky was announced weeks ago. Paying customers got emailed about it weeks ago. Just because people don't pay attention doesn't mean it's time to engage in low effort journalism (like so many outlets are doing.)
My citation for reference. https://www.zdnet.com/article/one-million-us-kaspersky-customers-to-be-migrated-to-this-lesser-known-alternative/
#antivirus #kapersky #security #infosec #cybersecurity #malware
Trail of Bits
trailofbits@infosec.exchangeAWS Nitro Enclaves offer strong isolation for sensitive workloads but require careful security implementation. We cover key areas to help developers avoid common pitfalls and harden their enclave deployments. https://blog.trailofbits.com/2024/09/24/notes-on-aws-nitro-enclaves-attack-surface/
Cedric Halbronn
saidelike@infosec.exchangeToday is your last chance to register to my Windows Kernel Exploitation training delivered at #hexacon in Paris/France https://www.hexacon.fr/trainer/halbronn/
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20240923-00/?p=110297
Viss
Viss@mastodon.socialnobody should "want to switch careers to security".
security shouldnt be "its own career".
it should be "becoming so good at the thing you are already good at, that you can perform security on that thing - like develoment, or SRE, or networking, or intelligence work". Eventually you get so good, you 'become security'.
which is why security has never, and will never be a 'starter career'. folks should get promoted into a security role from another role, like sysadmin/dev/network/etc.
eversinc33 🤍🔪⋆。˚ ⋆
eversinc33@bird.makeupYesterday I finally finished part II of my anti rootkit evasion series, where I showcase some detections for driver "stomping", attack flawed implementations of my anti-rootkit, hide system threads via the PspCidTable and detect that as well. Enjoy!
esjay
esj4y@bird.makeupFinally, the second part of the blog post where we go from Windows Paged Pool Overflow to SYSTEM shell starting from Low Integrity https://3sjay.github.io/2024/09/20/Windows-Kernel-Pool-Exploitation-CVE-2021-31956-Part2.html have a great weekend everyone ;)