Posts
2520Following
646Followers
1461VictorV
vv474172261@bird.makeuphttps://v-v.space/2024/08/19/CVE-2024-38148/
Check my blog about Windows secure channel RCE analysis, though MSRC thought it's a DOS. By the way, I'm not the finder. Share for studying
vuln research is the act of downloading trials and encountering errors while installing them
Lin Tan
lin0tan@bird.makeupIntroducing ReSym (CCS'24): our binary analysis technique, an LLM+static analysis solution that recovers names, types, and layouts of variables and data structures from binaries https://tinyurl.com/resym24 @danning_x, @i2huer, @nanjiang719, @xiangzhex XiangyuZhang #LLM4code #CCS #LLM
Alex Plaskett
alexjplaskett@bird.makeupexploit developers reading yet another RFC to see how IPv6 option processing works
DEF CON
defcon@defcon.socialThe #defcon 32 Video Team videos are now up on https://media.defcon.org Enjoy!
screaminggoat
screaminggoat@infosec.exchangeGoogle Chrome Zero Day: Stable Channel Update for Desktop
This update includes 38 security fixes. (20 externally reported). CVE-2024-7971 (high severity) Type confusion in V8
Reported by Microsoft Threat Intelligence Center (MSTIC), Microsoft Security Response Center (MSRC) on 2024-08-19
Google is aware that an exploit for CVE-2024-7971 exists in the wild.
cc: @campuscodi @briankrebs @mttaggart @deepthoughts10 @cR0w @regnil @bschwifty @arinc629 @Cali @wvu @hrbrmstr @avoidthehack @bieberium @AAKL (make sure to remove all the mentions to avoid ReplyAll madness)
#Google #Chrome #zeroday #vulnerability #eitw #activeexploitation #CVE #CVE_2024_7971
charles aylward
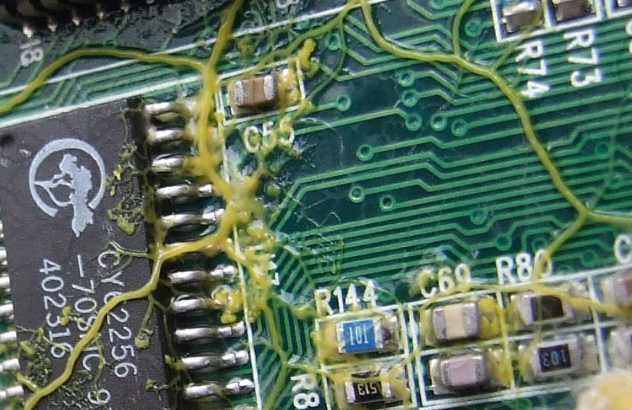
cda@malt.socialPhysarum wires: Self-growing self-repairing smart wires made from slime mould: https://arxiv.org/abs/1309.3583 a.k.a. super super gross wires. This is for sure how you end up with the backstory for the Borg.
Stefan Bohacek
stefan@stefanbohacek.onlineThis won't likely surprise anyone, but "a prompt injection vulnerability in Slack AI makes it possible to fetch data from private Slack channels".
https://www.theregister.com/2024/08/21/slack_ai_prompt_injection/
buherator
buheratorhttps://gergelykalman.com/the-missing-guide-to-the-security-of-filesystems-and-file-apis.html
Binary Ninja
binaryninja@infosec.exchangeBinji's teaching in Europe! By popular demand and for the first time ever, Novice to Ninja is online in GMT! Uncover the truth behind today's most pressing cybersecurity issues, and what might be done to mitigate them. No reversing experience required! https://binary.ninja/training/n2n-syllabus.html
buherator
buheratorhttps://www.youtube.com/watch?v=tBy1j9cTYKc
#Debugging #ReverseEngineering
rev.ng
revng@infosec.exchangeThe SAILR paper is being presented at @USENIXSecurity
.
It's a nice piece of work. If you're interested in what we think, take a look at the in-depth review we did on Feb!
Amethyst Basilisk
amethyst@haunted.computerIt's here! #Phrack officially released online, and with it my article! http://phrack.org/issues/71/9.html#article It's about writing a good virus, using oldschool techniques to show you how effective old stuff can still be! #infosec #malware
Foone🏳️⚧️
foone@digipres.clubugh. I picked up a shitty NUC from ewaste and it had a label on it for an AI company.
ahh, another startup that burnt out trying to build some silly AI project on crap hardware. I wonder what they did? I check their URL:
ahh. healthcare. great, great.
Mark McCaughrean
markmccaughrean@mastodon.socialThat’s no moon – it’s the Moon 🌗
The first colour images from ESA JUICE’s close lunar encounter last night are out.
Taken by the monitoring cameras, both show sunlit craters & shadows on the surface with parts of the spacecraft in the foreground.
At the top of the second image, you can just make out Earth as a small dark circle, surrounded by the ring of its backlit atmosphere.
We arrive (t)here tonight 🛰️🌏
Kudos to @stim3on for the magical processing 🙇♂️
buherator
buheratorAlternatively, what is the easiest way to generate a function call graph for packages of any package manager?
#Programming #StaticAnalysis
CERT-EU
cert_eu@infosec.exchangeUPDATE: Palo Alto Cortex XSOAR CommonScripts Critical Vulnerability (CERT-EU Security Advisory 2024-083)
On August 14, 2024, Palo Alto Networks released a security advisory for a critical command injection vulnerability, CVE-2024-5914, in Cortex XSOAR. This flaw allows unauthenticated attackers to execute arbitrary commands within the context of an integration container, potentially compromising the system. The vulnerability affects the product's CommonScripts Pack and is rated as high severity with a CVSS score of 9.0.
https://www.cert.europa.eu/publications/security-advisories/2024-083/