Posts
3935Following
728Followers
1602Brent Cook
busterb@infosec.exchangeThis says that Windows still has low-level OS support for punch card readers.
https://kevinboone.me/cpm-c.html
Not documented here though: https://learn.microsoft.com/en-us/windows/win32/fileio/naming-a-file
Could someone with Windows handy try `echo test > PUN` and see what happens?
Andrew Zonenberg
azonenberg@ioc.exchangeI recently became aware of a true abomination: https://github.com/open-abap/open-abap-ssh
Someone seriously looked at a problem and went "I know, I'll implement an SSH client as a script running on my ERP system".
I don't know what problem they could have possibly had, and I hope to never find out.
joernchen :cute_dumpster_fire:
joern@threatactor.clubMy colleague @nickmalcolm made a pretty cool vuln explainer video
✧✦Catherine✦✧
whitequark@mastodon.socialthis is an absolutely fantastic license and i will certainly use it for some of my software https://github.com/meithecatte/bashfuck/blob/master/LICENSE
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchangePart 2 of our new series on identifying and exploiting router vulnerabilities, including practical examples from real-world cases is now out:
https://medium.com/@odedvk/identify-and-exploit-vulnerabilities-in-routers-an-introductory-guide-technical-case-studies-d0f1a24d35ef
Mattie Schraeder
afrozenpeach@geek.gayI do realize I'm screaming into a void, but writing this email was cathartic.
Euractiv
euractiv@masto.aiTop articles from this week: White hat hacker shines spotlight on vulnerability of solar panels installed in Europe http://dlvr.it/TBvXRM?utm_source=dlvr.it&utm_medium=mastodon
Waltteri
anotherwalther@mastodon.socialMIT gets rid of their Elsevier contracts:
“For MIT to continue to pay millions of dollars to corporations that lock up the scholarship that comes out of our own campus was just inconsistent with MIT’s history of supporting open education and research,” said Chris Bourg, Director of Libraries at MIT.
https://sparcopen.org/our-work/big-deal-knowledge-base/unbundling-profiles/mit-libraries/
implr
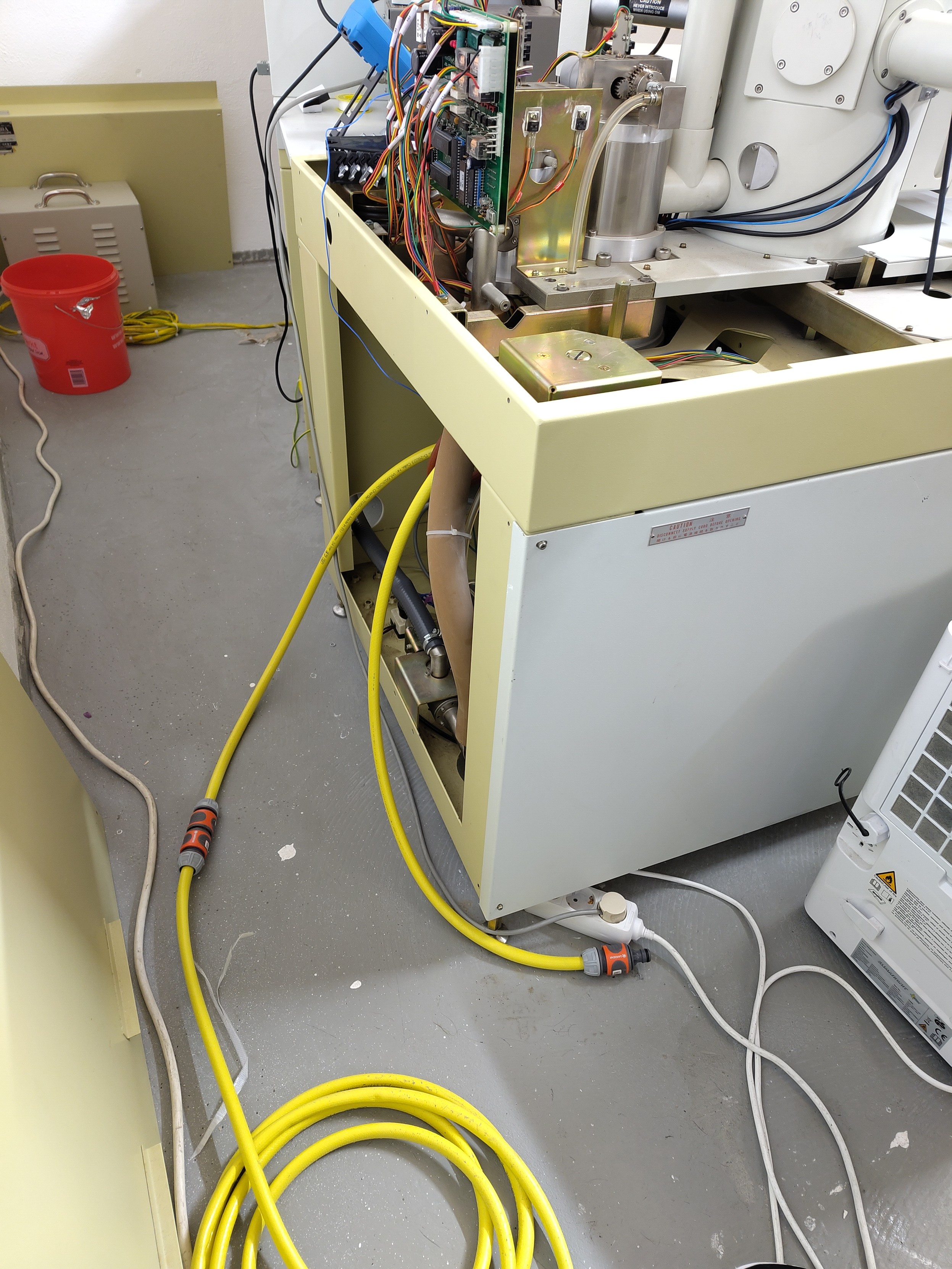
implr@hackerspace.pl@fafo presents: Gardena zu Rasterelektronmikroskop Adapter
screaminggoat
screaminggoat@infosec.exchangeOpenAI: Disrupting a covert Iranian influence operation
OpenAI announced Friday (16 August 2024) that they identified and took down a cluster of ChatGPT accounts that were generating content for a covert Iranian influence operation identified as Storm-2035. The operation used ChatGPT to generate content focused on a number of topics—including commentary on candidates on both sides in the U.S. presidential election – which it then shared via social media accounts and websites.
The operation generated content about several topics: mainly, the conflict in Gaza, Israel’s presence at the Olympic Games, and the U.S. presidential election—and to a lesser extent politics in Venezuela, the rights of Latinx communities in the U.S. (both in Spanish and English), and Scottish independence. They interspersed their political content with comments about fashion and beauty, possibly to appear more authentic or in an attempt to build a following.
IOC provided.
See related The Hacker News reporting: OpenAI Blocks Iranian Influence Operation Using ChatGPT for U.S. Election Propaganda
#threatintel #Iran #influenceoperations #openai #chatgpt #disinformation #propaganda #IOC
Miloš
ynwarcs@infosec.exchangeI just released pdbconv, a program to convert PDB files between the plain old MSF format and the new MSFZ format that MS hasn't officially released yet.
It's available on github: https://github.com/ynwarcs/pdbconv
I also made a blog post describing the new format and what lead me to write the converter: https://ynwarcs.github.io/pdbconv-pdb-compression
WHY2025 Productiehuis
productiehuis@chaos.social1 #million views! Today is a momentous day for the #WHY2025 #MCH2022 #SHA2017 Youtube account.
The video of a talk called "Non-Euclidean Doom: what happens to a game when pi is not 3.14159…" reached 1 million views on Youtube a few minutes ago.
The video is of course also on media.ccc.de and has reached almost a hundred thousand views there.
The recommended way to watch the video is https://media.ccc.de/v/mch2022-236-non-euclidean-doom-what-happens-to-a-game-when-pi-is-not-3-14159-, but if you want proof of the milestone, check out https://youtu.be/_ZSFRWJCUY4
/r/netsec
_r_netsec@infosec.exchangeCVE-2024-41660: A Critical Vulnerability in OpenBMC https://tetrelsec.com/posts/cve-2024-41660-slpd-lite/
/r/netsec
_r_netsec@infosec.exchangeMIFARE Classic: exposing the static encrypted nonce variant https://eprint.iacr.org/2024/1275.pdf
GrapheneOS
GrapheneOS@grapheneos.socialWired was manipulated into spreading misinformation to market Palantir and iVerify by misrepresenting a vulnerability in a disabled demo app as being a serious problem which could be exploited in the real world. They should retract the article but won't.
https://wired.com/story/google-android-pixel-showcase-vulnerability/
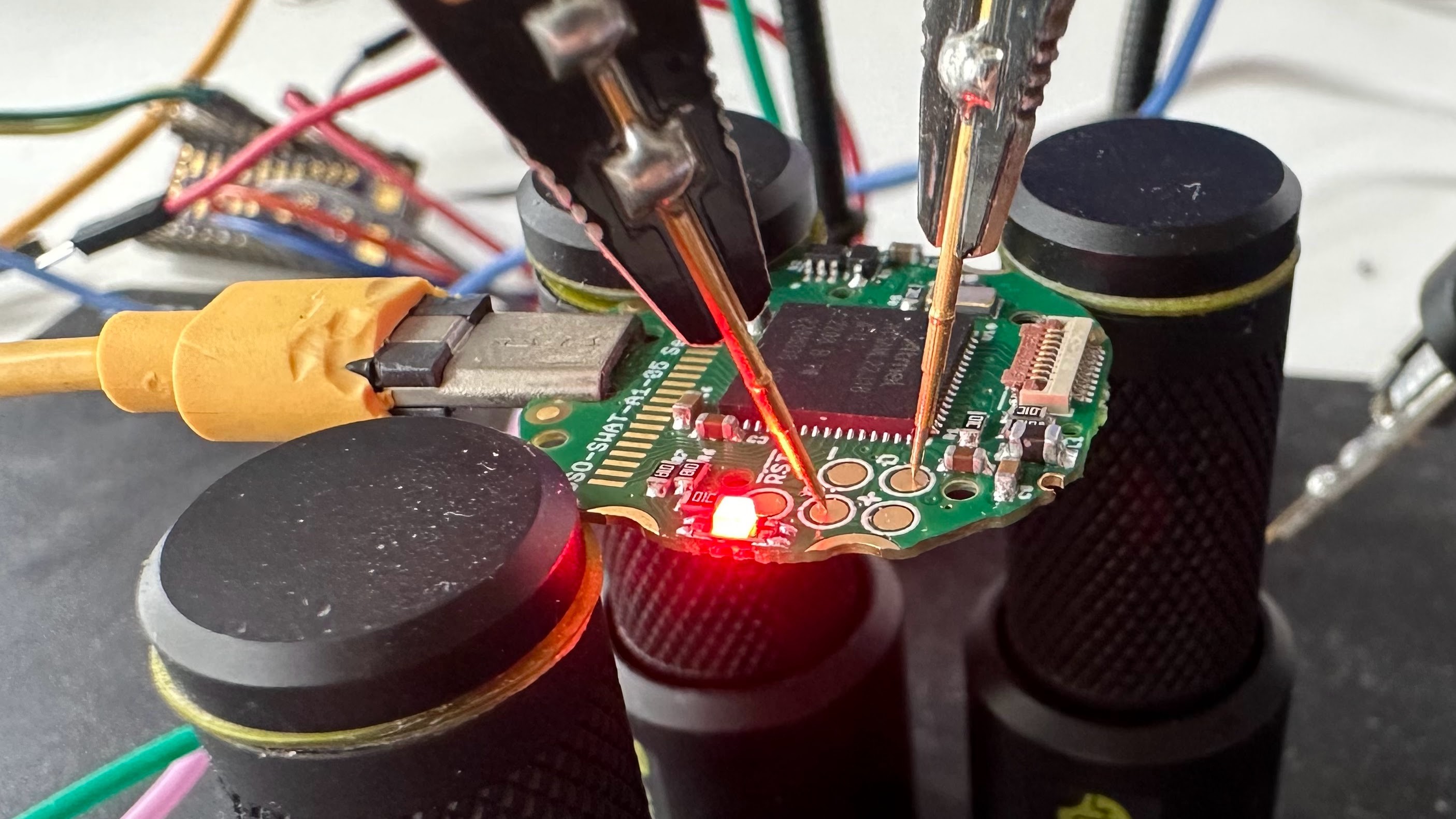
Trammell Hudson
th@v.stFor #CircuitPythonDay2024 I'm porting Micropython to the SensorWatch SAML22J18 that fits in the classic Casio FT-91W. https://www.sensorwatch.net/
It's the Freya's day today so let's run another #nakeddiefriday why don't we.
Today I got a #French classic form 1983, one of the very first chip cards. The micromodule is a very characteristic shape of those designed by Bull.
On the die itself, the EEPROM array is in the very center, with the address counter to the right, drivers above and the data multiplexer below.
Note the designer initials, C.B. and Y.G.
Hi-res: https://siliconpr0n.org/archive/doku.php?id=infosecdj:bull:et1001
Linuxiac
linuxiac@mastodon.socialClamAV Antivirus 1.4 ends 32-bit Linux support, introduces ARM64 packages for Windows, improves ALZ and LHA archive handling, and more.
https://linuxiac.com/clamav-antivirus-1-4-ends-32-bit-linux-support/
CERT-EU
cert_eu@infosec.exchangeZabbix Server Critical Arbitrary Code Execution Vulnerability (CERT-EU Security Advisory 2024-082)
On August 13, 2024, a critical vulnerability, CVE-2024-22116, was disclosed in Zabbix Server, allowing attackers with restricted administrative permissions to execute arbitrary code. The flaw, identified in the Ping script execution within the Monitoring Hosts section, can compromise the entire infrastructure. The vulnerability carries a CVSS score of 9.9.
https://www.cert.europa.eu/publications/security-advisories/2024-082/
Hacker News
hkrn@mstdn.socialCartoon Network's Website Was Deleted. That Should Scare You All
L: https://slate.com/technology/2024/08/david-zaslav-warner-bros-discovery-culture-deleting-movies-tv-shows.html
C: https://news.ycombinator.com/item?id=41262878
posted on 2024.08.15 at 23:25:16 (c=0, p=5)