Posts
3900Following
728Followers
1601Miloš
ynwarcs@infosec.exchangeI just released pdbconv, a program to convert PDB files between the plain old MSF format and the new MSFZ format that MS hasn't officially released yet.
It's available on github: https://github.com/ynwarcs/pdbconv
I also made a blog post describing the new format and what lead me to write the converter: https://ynwarcs.github.io/pdbconv-pdb-compression
WHY2025 Productiehuis
productiehuis@chaos.social1 #million views! Today is a momentous day for the #WHY2025 #MCH2022 #SHA2017 Youtube account.
The video of a talk called "Non-Euclidean Doom: what happens to a game when pi is not 3.14159…" reached 1 million views on Youtube a few minutes ago.
The video is of course also on media.ccc.de and has reached almost a hundred thousand views there.
The recommended way to watch the video is https://media.ccc.de/v/mch2022-236-non-euclidean-doom-what-happens-to-a-game-when-pi-is-not-3-14159-, but if you want proof of the milestone, check out https://youtu.be/_ZSFRWJCUY4
/r/netsec
_r_netsec@infosec.exchangeCVE-2024-41660: A Critical Vulnerability in OpenBMC https://tetrelsec.com/posts/cve-2024-41660-slpd-lite/
/r/netsec
_r_netsec@infosec.exchangeMIFARE Classic: exposing the static encrypted nonce variant https://eprint.iacr.org/2024/1275.pdf
GrapheneOS
GrapheneOS@grapheneos.socialWired was manipulated into spreading misinformation to market Palantir and iVerify by misrepresenting a vulnerability in a disabled demo app as being a serious problem which could be exploited in the real world. They should retract the article but won't.
https://wired.com/story/google-android-pixel-showcase-vulnerability/
Trammell Hudson
th@v.stFor #CircuitPythonDay2024 I'm porting Micropython to the SensorWatch SAML22J18 that fits in the classic Casio FT-91W. https://www.sensorwatch.net/
It's the Freya's day today so let's run another #nakeddiefriday why don't we.
Today I got a #French classic form 1983, one of the very first chip cards. The micromodule is a very characteristic shape of those designed by Bull.
On the die itself, the EEPROM array is in the very center, with the address counter to the right, drivers above and the data multiplexer below.
Note the designer initials, C.B. and Y.G.
Hi-res: https://siliconpr0n.org/archive/doku.php?id=infosecdj:bull:et1001
Linuxiac
linuxiac@mastodon.socialClamAV Antivirus 1.4 ends 32-bit Linux support, introduces ARM64 packages for Windows, improves ALZ and LHA archive handling, and more.
https://linuxiac.com/clamav-antivirus-1-4-ends-32-bit-linux-support/
CERT-EU
cert_eu@infosec.exchangeZabbix Server Critical Arbitrary Code Execution Vulnerability (CERT-EU Security Advisory 2024-082)
On August 13, 2024, a critical vulnerability, CVE-2024-22116, was disclosed in Zabbix Server, allowing attackers with restricted administrative permissions to execute arbitrary code. The flaw, identified in the Ping script execution within the Monitoring Hosts section, can compromise the entire infrastructure. The vulnerability carries a CVSS score of 9.9.
https://www.cert.europa.eu/publications/security-advisories/2024-082/
Hacker News
hkrn@mstdn.socialCartoon Network's Website Was Deleted. That Should Scare You All
L: https://slate.com/technology/2024/08/david-zaslav-warner-bros-discovery-culture-deleting-movies-tv-shows.html
C: https://news.ycombinator.com/item?id=41262878
posted on 2024.08.15 at 23:25:16 (c=0, p=5)
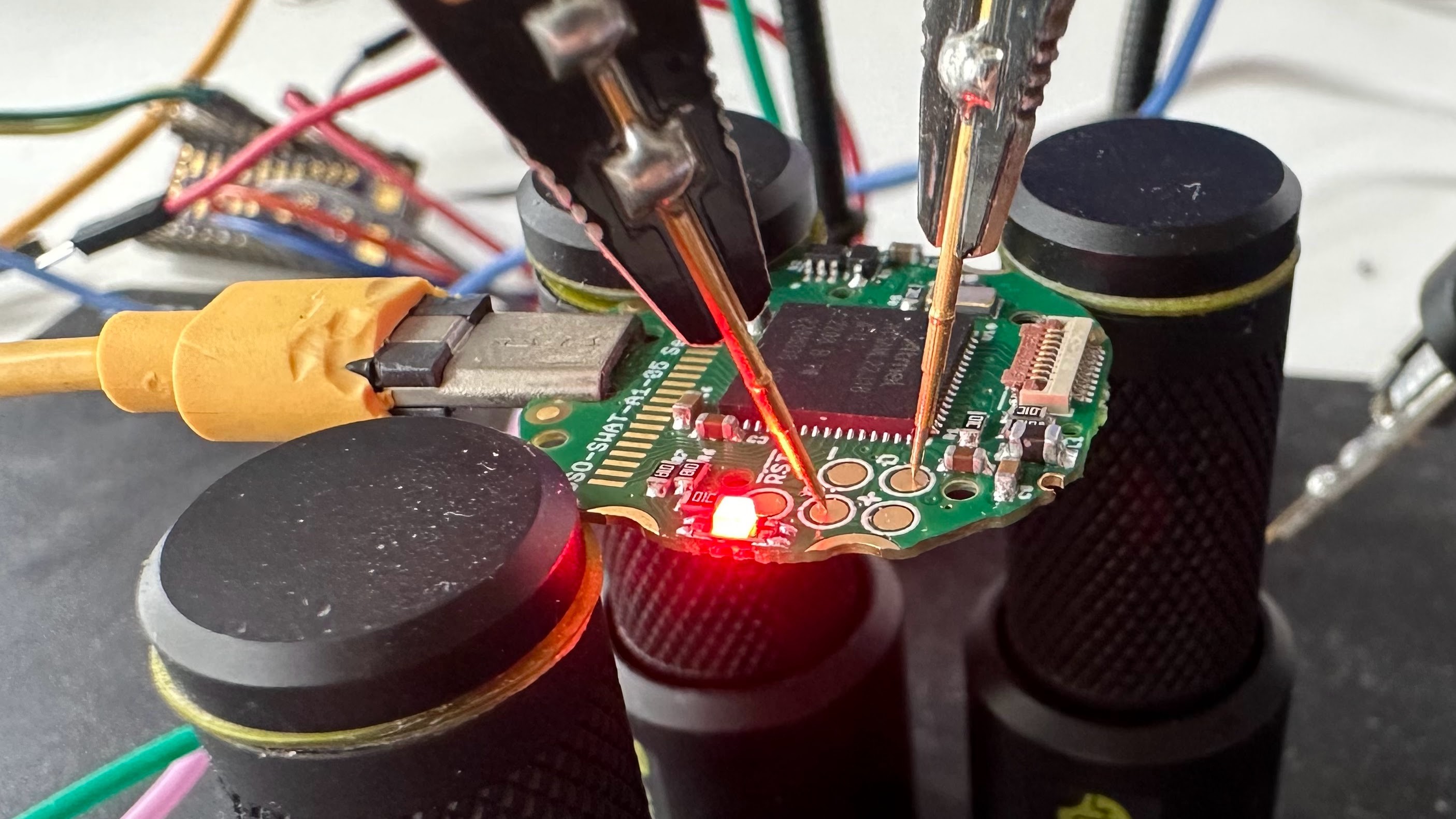
stacksmashing
stacksmashing@infosec.exchangeWhen I got started with hardware hacking etc @travisgoodspeed was (and is) one of my heroes.
Now there’s a chapter in his new (awesome) book on a vuln I found. Feels awesome.
Thanks Travis for all your contributions to our community.
Also, you should buy his book!
kaoudis
kaoudis@infosec.exchangehttps://www.usenix.org/conference/usenixsecurity24/presentation/qi System-level emulation and instrumentation is generally slow, but there’s a neat insight into when instrumentation *isn’t* necessary and what basic blocks to not instrument for QEMU-based system-level concolic execution in this work!
Guy Dupont
gvy_dvpont@mastodon.socialTired of using your own tongue to test 9V batteries???
👅👅👅🔋🔋🔋 ouch!
Honored and humbled to announce my latest product:
/r/netsec
_r_netsec@infosec.exchangeMSI motherboards susceptible to code execution & firmware implant - analysis of CVE-2024-36877 https://jjensn.com/at-home-in-your-firmware
Enjoy the old sch00l lulz:
Fuck You Ilfak - A IDA Pro 9.0 Beta 2 macOS x86 Fix Loader
TrendAI Zero Day Initiative
thezdi@infosec.exchangeMicrosoft fixed CVE-2024-38213 last Tuesday. It was discovered in the wild by ZDI threat hunter @gothburz. Today, he makes the details of the vulnerability and how it's being used by threat actors. https://www.zerodayinitiative.com/blog/2024/8/14/cve-2024-38213-copy2pwn-exploit-evades-windows-web-protections
Trail of Bits
trailofbits@infosec.exchangeTwo days ago, NIST finalized three post-quantum cryptography standards. Today, we are announcing an open-source Rust implementation of one of these standards, SLH-DSA, now available in RustCrypto! https://blog.trailofbits.com/2024/08/15/we-wrote-the-code-and-the-code-won/
Andrew Couts
couts@mastodon.socialNEW: Every Pixel phone released since 2017 has a hidden Verizon app, "Showcase.apk," with deep system access that has an unpatched flaw. Google's response to the vulnerability caused Palantir to ditch Android altogether. @lhn has the scoop: https://www.wired.com/story/google-android-pixel-showcase-vulnerability/
daniel:// stenberg://
bagder@mastodon.socialthe most recent hackerone issue was filed because the user googled "[another project] bug bounty program", clicked the first link (to #curl's bug-bounty) and entered an issue about a completely different project...
Joxean Koret (@matalaz)
joxean@mastodon.socialLong thread ahead about training a classifier of "good/batch matches" for #Diaphora.
So, the whole idea that I have been working on for quite some time already to try to, somehow, improve matching in Diaphora is the following: Train a model to better determine if a pair of functions in two binaries (ie, a match between a function A in binary X, and function B in binary Y) is correct or not.