Posts
3752Following
723Followers
1596petersuber
petersuber@fediscience.orgKudos to #Mozilla for defying #Russia's ban on #Firefox extensions that help Russian users bypass Russian #censorship.
https://www.theregister.com/2024/06/14/mozilla_firefox_russia/
Nina Kalinina
nina_kali_nina@tech.lgbt~ Let's make RAM at home, thread #1 ~
In this thread: successful experiment with factory-made ferrite core memory (1 bit for now!), a brief explanation of the experiment, and failed attempts at making a core (so you wouldn't have to try it)
🧵 go~
Nina Kalinina
nina_kali_nina@tech.lgbtI became into toy computers after I got my hands on a wonderful Sumikko Gurashi computer (and started to believe that similarly designed machines can be an answer to our cold heartless world).
I have a few vintage vTech precomputers that run BASIC and have decent IO capabilities (a serial or a parallel port at the very least), but I was curious whether newer toy computers has anything similar.
The exhibit we have here is vTech Media Desktop, a toy computer from around 2010. Its original RPP was about $100, but after a short while slashed to $25. The computer has a non-backlit ~64x48 pixel LCD, two mid-sized speakers to play high-quality digital samples and polyphonic MIDI, a membrane keyboard and a ball mouse.
There is a mini-USB port on the back that switches computer into "Sync" mode. The device presents itself as a 16MB USB stick with 512KB free, and mirrors there the contents of 512KB SPI Flash it has on board.
With the right software (which has vanished from the Internet), new apps can be added.
🧵
BleepingComputer
BleepingComputer@infosec.exchangeA proof-of-concept (PoC) exploit for a critical Veeam Recovery Orchestrator authentication bypass vulnerability tracked as CVE-2024-29855 has been released, elevating the risk of being exploited in attacks.
testssl.sh 
testssl@infosec.exchange
Release of the old stable (bug-fixed only) version of testssl.sh was overdue but now happened ;-)
You can get it at https://testssl.sh/ or at https://github.com/drwetter/testssl.sh/releases .
You should better use 3.2rc3 though. It is at least as stable and has wayyy more features.
Project Gutenberg
gutenberg_org@mastodon.socialScottish physicist James Clerk Maxwell was born #OTD in 1831.
His most significant contribution is his formulation of the classical theory of electromagnetic radiation. In 1861-1862, he published a series of papers culminating in "A Dynamical Theory of the Electromagnetic Field," in which he presented Maxwell's equations. He made substantial contributions to the kinetic theory of gases as well as to the Maxwell-Boltzmann distribution
Tony Finch
fanf@mendeddrum.org2021 retro-link! https://berthub.eu/articles/posts/reed-solomon-for-programmers/ - Practical Reed-Solomon for programmers.
screaminggoat
screaminggoat@infosec.exchangeHappy Patch Tuesday (er, Wednesday) from Palo Alto Networks:
- CVE-2024-5905 (CVSSv4: 2.0 low) Cortex XDR Agent: Local Windows User Can Disrupt Functionality of the Agent
- CVE-2024-5906 (CVSSv4: 4.8 medium) Prisma Cloud Compute: Stored Cross-Site Scripting (XSS) Vulnerability in the Web Interface
- CVE-2024-5907 (CVSSv4: 5.2 medium) Cortex XDR Agent: Local Privilege Escalation (PE) Vulnerability
- CVE-2024-5908 (CVSSv4: 5.5 medium) GlobalProtect App: Encrypted Credential Exposure via Log Files
- CVE-2024-5909 (CVSSv4: 6.8 medium) Cortex XDR Agent: Local Windows User Can Disable the Agent
Palo Alto Networks is not aware of any malicious exploitation of this issue.
SponsorBlock (and DeArrow)
sponsorblock@fosstodon.orgYouTube is currently experimenting with server-side ad injection. This means that the ad is being added directly into the video stream.
This breaks sponsorblock since now all timestamps are offset by the ad times.
For now, I set up the server to detect when someone is submitting from a browser with this happening and rejecting the submission to prevent the database from getting filled with incorrect submissions.
/r/netsec
_r_netsec@infosec.exchangeCVE-2024-29824 Deep Dive: Ivanti EPM SQL Injection Remote Code Execution Vulnerability, IOCs, and POC https://www.horizon3.ai/attack-research/attack-blogs/cve-2024-29824-deep-dive-ivanti-epm-sql-injection-remote-code-execution-vulnerability/
Clément Labro
itm4n@infosec.exchange🆕 PrivescCheck update!
I realize that I haven't communicated about PrivescCheck in a while, although I implemented a bunch of new cool features recently. A few of them below:
➡️ Check for listing Attack Surface Reduction (ASR) rules enabled in Defender Exploit Guard.
➡️ SCCM cache folder paths are now enumerated using the registry, and browsed to identify potentially hardcoded credentials.
➡️ New "-Audit" option to enable configuration audit checks.
➡️ New "-Risky" option to manually enable checks that are likely to trigger EDR.
There are also other privilege escalation attack vectors I want to cover in the near future. Stay tuned! :)
chompie
chompie1337@haunted.computermicrosoft: Exploit Code Unporoven
me: i literally gave you a compiled PoC and also exploit code
m$: No exploit code is available, or an exploit is theoretical.
me:
stf
stf@chaos.socialscreaminggoat
screaminggoat@infosec.exchangeJetBrains security advisory: Updates for security issue affecting IntelliJ-based IDEs 2023.1+ and JetBrains GitHub Plugin
A new security issue was discovered that affects the JetBrains GitHub plugin on the IntelliJ Platform, which could lead to disclosure of access tokens to third-party sites. CVE-2024-37051 (CVSSv3: 9.3 CRITICAL) GitHub access token could be exposed to third-party sites in JetBrains IDEs. No mention of exploitation.
h/t: @serghei See related Bleeping Computer reporting: JetBrains warns of IntelliJ IDE bug exposing GitHub access tokens
screaminggoat
screaminggoat@infosec.exchangeHappy Patch Tuesday from Adobe:
- APSB24-27 : Security update available for Adobe Photoshop (1)
- APSB24-28 : Security update available for Adobe Experience Manager (144 CVEs!! Someone's EXPERIENCING a lot of vulnerabilities if you know what I mean)
- APSB24-32 : Security update available for Adobe Audition (2)
- APSB24-34 : Security update available for Adobe Media Encoder (1)
- APSB24-38 : Security update available for Adobe FrameMaker Publishing Server (2, and CVE-2024-30299 is a perfect 10.0 🥳)
- APSB24-40 : Security update available for Adobe Commerce (10)
- APSB24-41 : Security update available for Adobe ColdFusion (2)
- APSB24-43 : Security update available for Adobe Substance 3D Stager (1)
- APSB24-44 : Security update available for Adobe Creative Cloud Desktop (1)
- APSB24-50 : Security update available for Adobe Acrobat Android (2)
No mention of exploitation.
#PatchTuesday #Adobe #CVE #vulnerability #Acrobat #Photoshop #ColdFusion
Corey Quinn
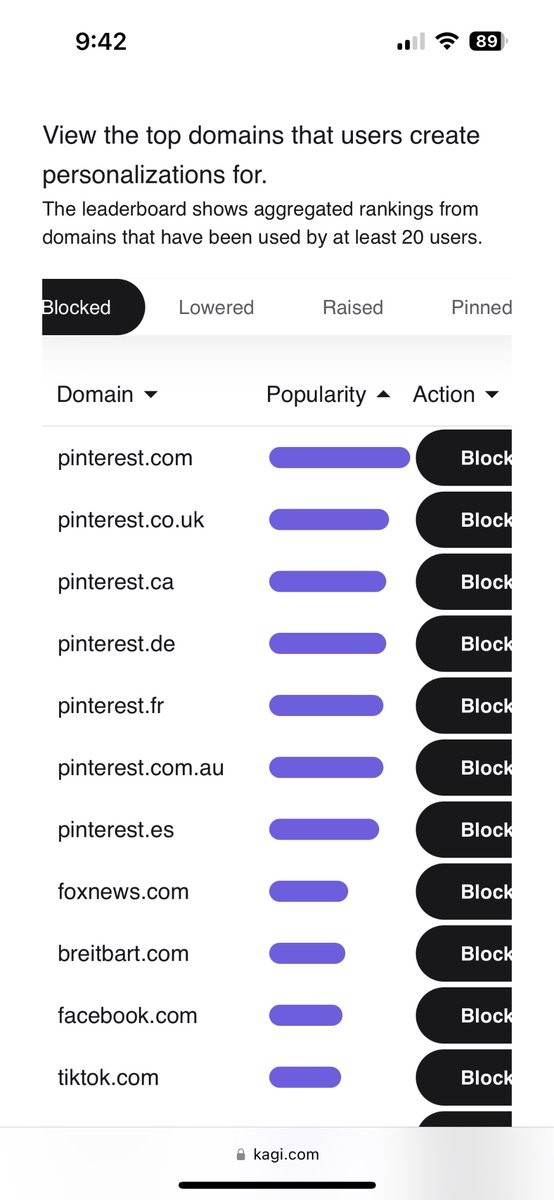
Quinnypig@awscommunity.socialYou’d really think that the top seven blocked domains on @KagiHQ being @Pinterest indicate that a functional Google would have deboosted them years ago.
(I’m loving Kagi)
TrendAI Zero Day Initiative
thezdi@infosec.exchangeSchool's out, and so are the latest patches from #Microsoft. We're still waiting on the updates from #Adobe. Check out the analysis from @TheDustinChilds as he breaks down the small release from Redmond. https://www.zerodayinitiative.com/blog/2024/6/11/the-june-2024-security-update-review
The Dustin Childs
TheDustinChilds@infosec.exchange#Microsoft patches are out. Another small release. Still waiting on #Adobe :-[ Let them patches out! I'll have my full analysis out soon. #PatchTuesday