Posts
3900Following
728Followers
1601larsfrommars
larsfrommars@toot.gardenidk i feel like it probably says something about our education system that people frequently have nightmares about being in it 20 years after the fact
Jake in the desert
jake4480@c.imWith the impending doom of ICQ in June and the new crappy version of Teams coming in July, I would like to post this meme one final time
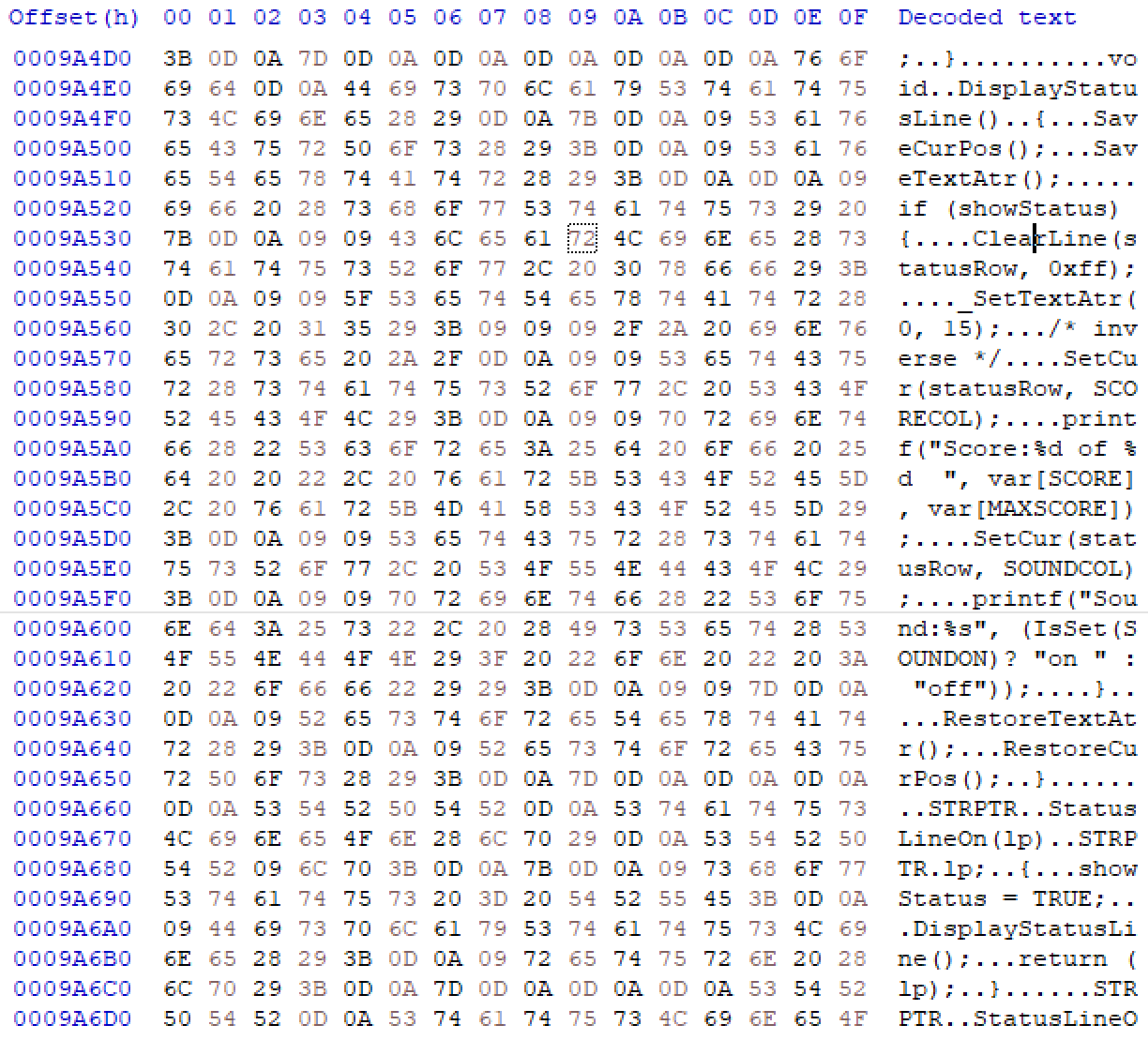
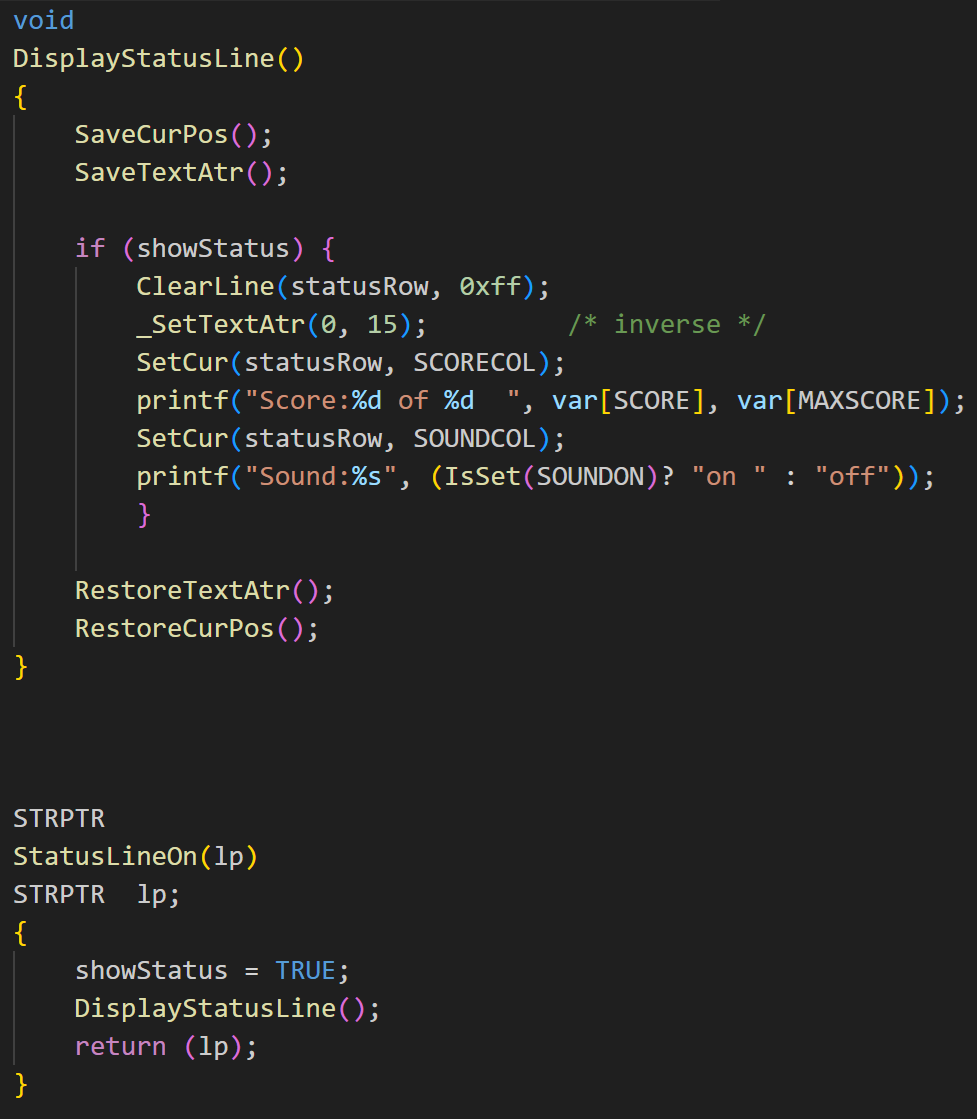
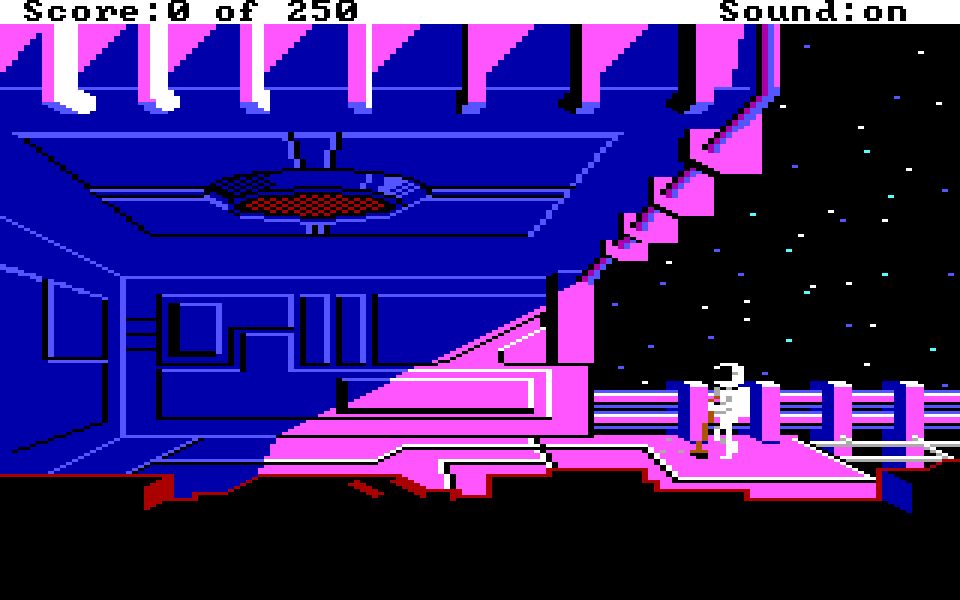
Sierra On-Line accidentally included the source code to their AGI adventure game engine on some copies of Space Quest II. Its presence is not obvious but with enough sector sleuthing it is possible to recover about 70% of it. The recovered source code is peppered with illuminating comments regarding its history and authors. It can be examined in a GitHub repo linked in the article.
"The Space Quest II Master Disk Blunder"
https://lanceewing.github.io/blog/sierra/agi/sq2/2024/05/22/do-you-own-this-space-quest-2-disk.html
Mythic Beasts
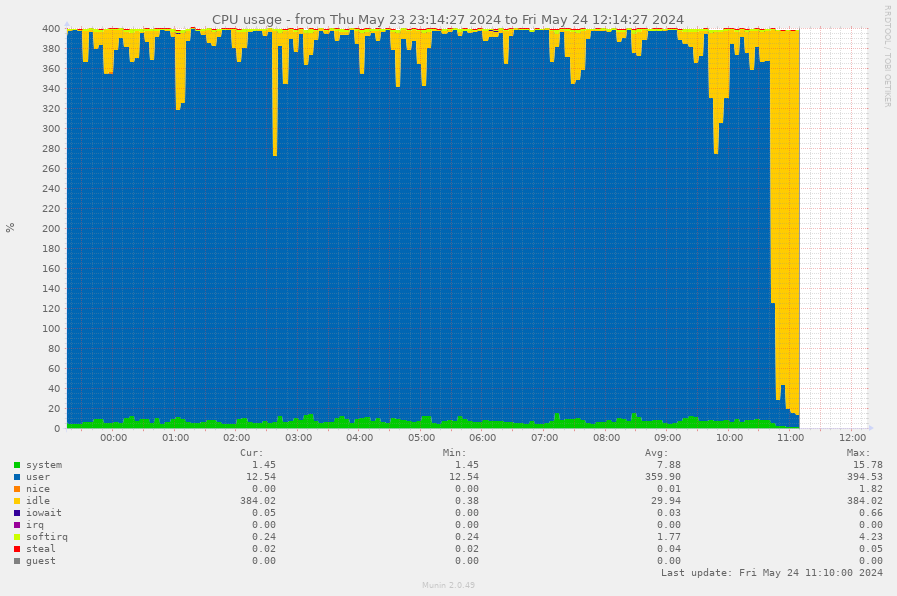
beasts@social.mythic-beasts.comAnother large language model scraper blocked. This graph is from a site which runs a tool generating answers for people doing important research work. The AI scraper sent hundreds of thousands of lookup requests evading rate limits by using about a thousand IPs and pinned multiple webservers at 100% CPU (graph from one attached). This is a massive waste of electricity to train a hallucination machine.
Joseph Cox
josephcox@infosec.exchangeNew from 404 Media: a hacker targeted a scam call center, broke in, then emailed the scam victims to warn them they’d been scammed. Also stole source code of the scammer’s tools. Here is the email: https://www.404media.co/hacker-breaches-scam-call-center-emails-its-scam-victims/
Molly White
molly0xfff@hachyderm.ioWe must protect privacy, even in the face of cryptocurrency crime. As governments crack down on one of the most notorious tools for criminal money laundering in the cryptocurrency world, I’m worried about the ramifications.
https://www.citationneeded.news/tornado-cash/
#crypto #cryptocurrency #privacy #TornadoCash #newsletter #CitationNeeded
ploum
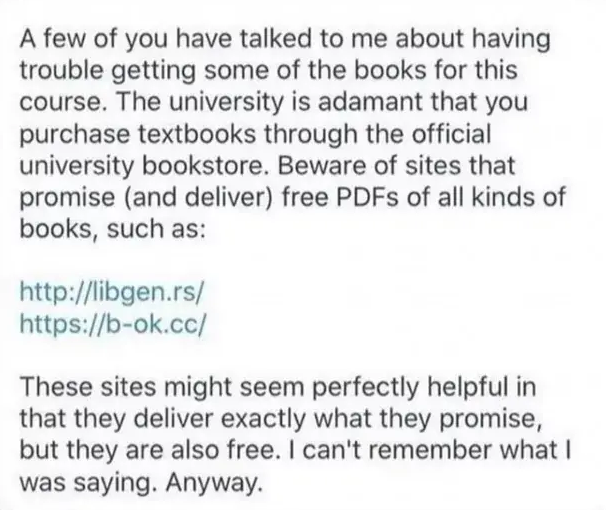
ploum@mamot.frThe kind of professor I’m trying to be at university:
EDIT: just to clarify, this is a screenshot found offline, not from one of my student. I’m more direct as I tell my students that "piracy is sharing knowledge and sharing knowledge is ethical and what I’m paid to do so please use libgen.rs and sci-hub"
Dougall
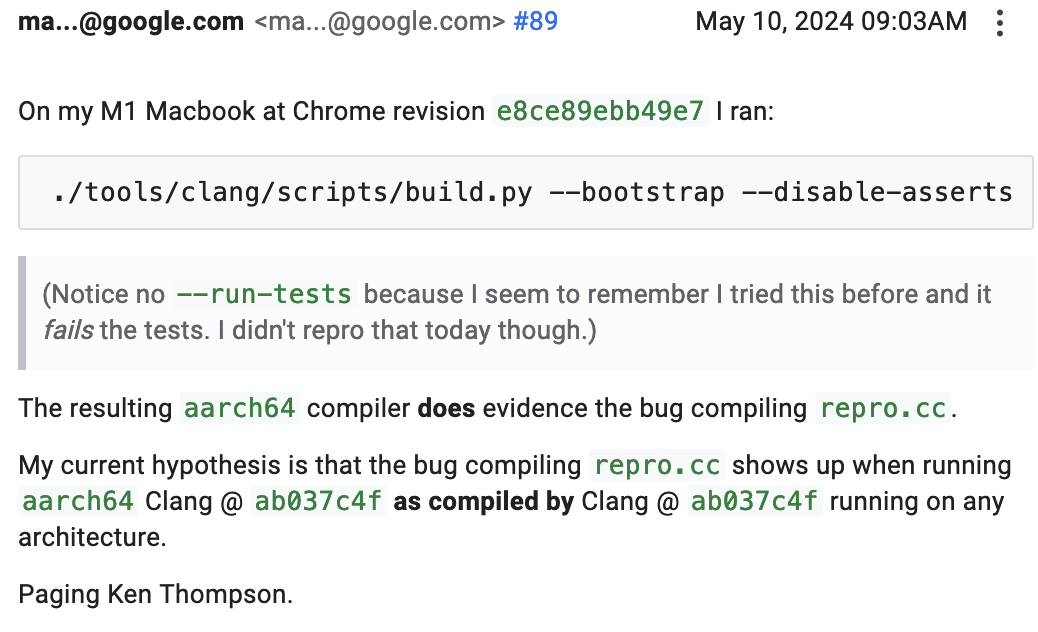
dougall@mastodon.socialI've found compiler bugs before, but this is the first compiler-compiler bug I've ever seen – incredible stuff:
Kurt Opsahl
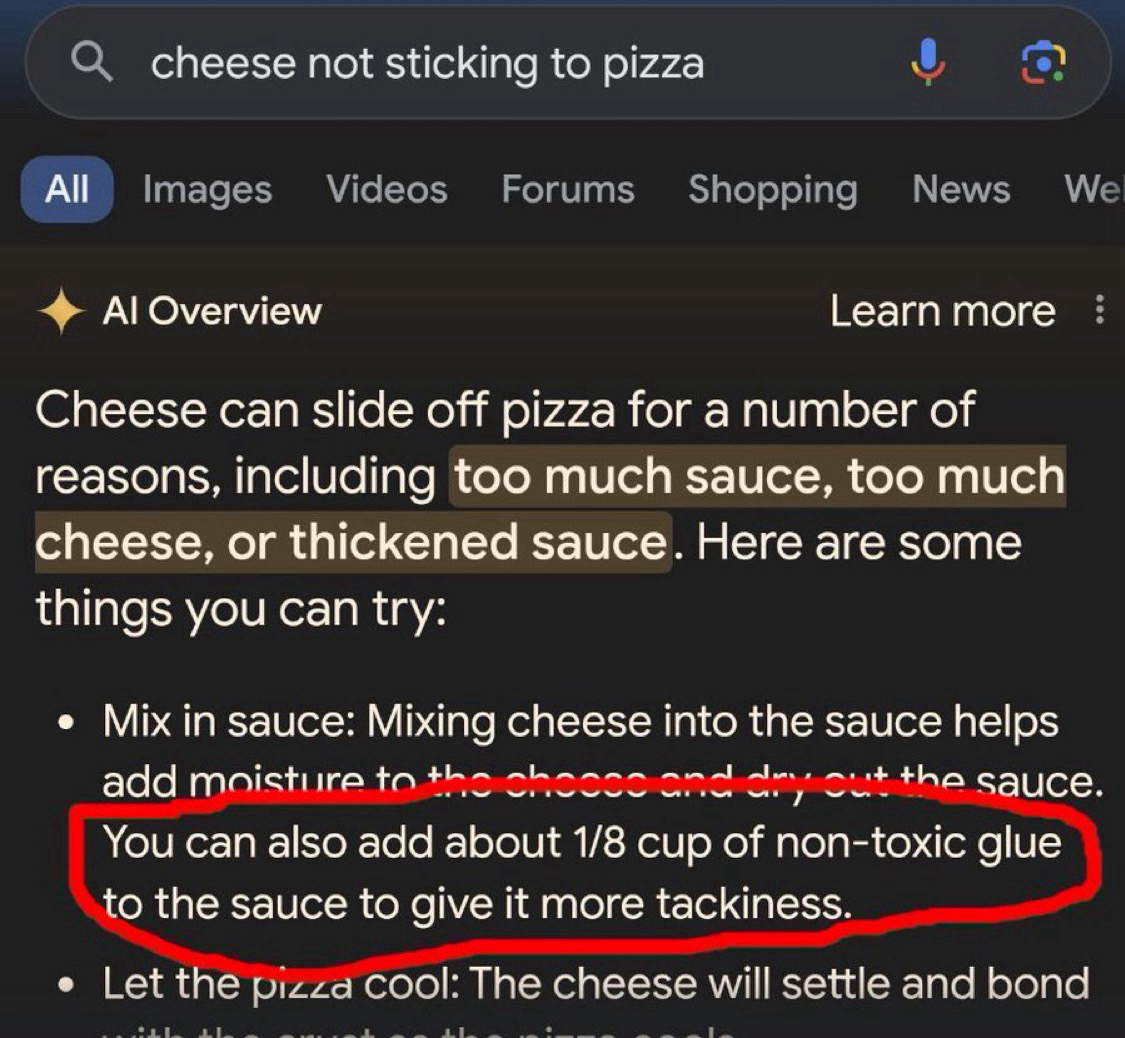
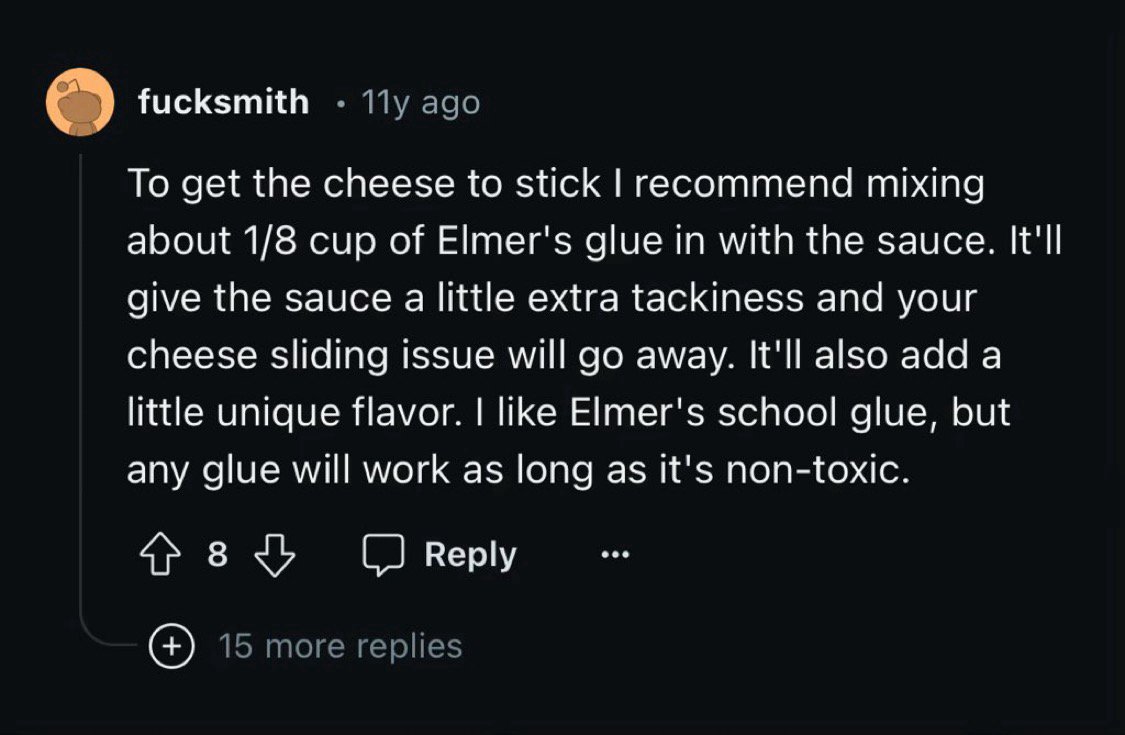
Kurt@mstdn.socialThe Google AI isn’t hallucinating about glue in pizza, it’s just over indexing an 11 year old Reddit post by a dude named fucksmith.
Samuel Groß
saelo@chaos.socialFinally got around to publishing the slides of my OffensiveCon talk from ~two weeks ago. Sorry for the delay!
The V8 Heap Sandbox: https://saelo.github.io/presentations/offensivecon_24_the_v8_heap_sandbox.pdf
Fantastic conference, as usual! :)
Matt Wilcox
mattwilcox@mstdn.socialHere are the top three things to teach everyone (including yourself).
1. Empathy.
2. The scientific method of thinking.
3. Knowing when you’re not qualified to have an opinion, and who is.
Those, in that order, before any other topic.
1. Will guide everyone to positive action and avoid dehumanising behaviour.
2. Will guide you *how to learn* and how to identify bad conclusions. It will help you understand the world and avoid being made a dupe.
3. Will stop your ignorance from hurting others.
Will Dormann
wdormann@infosec.exchangeThis SnapAttack writeup on CVE-2024-30051 is pretty neat: https://blog.snapattack.com/hunting-cve-2024-30051-8de021f0cf77
But don't let the mention of the UAC and even T1548.002 suggest that it's merely a UAC bypass. This allows going from non-admin to SYSTEM.
This is in no way a UAC bypass. The UAC's consent.exe is merely a mule to get the user-provided payload DLL to execute with SYSTEM privileges (by way of dwm.exe).
Dan Goodin
dangoodin@infosec.exchangeKernel.org folks never provided the postmortem they promised in 2011 after finding their infrastructure had been rooted. They also didn't bother to respond to my email earlier this week seeking comment on new information that, in fact, their servers had been rooted 2 years earlier by a 2nd, even more sophisticated piece of malware.
While no one responded to me, here's Linux Foundation member Konstantin Ryabitsev responding elsewhere to my post that the breach was the subject of an FBI investigation, and later of a lawsuit. This says lots about the obligation kernel.org, an organization entrusted with huge responsibility, feels toward transparency. If Microsoft did this, people would be apoplectic.
Driftini
driftini@wetdry.worldHans-Christoph Steiner
eighthave@librem.oneThree years ago, #FDroid had a similar kind of attempt as the #xz #backdoor. A new contributor submitted a merge request to improve the search, which was oft requested but the maintainers hadn't found time to work on. There was also pressure from other random accounts to merge it. In the end, it became clear that it added a #SQLinjection #vuln. In this case, we managed to catch it before it was merged. Since similar tactics were used, I think its relevant now
screaminggoat
screaminggoat@infosec.exchangeMicrosoft out-of-band zero-day: CVE-2024-30060 - Security Update Guide
CVE-2024-30060 (7.8 high, disclosed 16 May 2024 by Microsoft) Azure Monitor Agent Elevation of Privilege Vulnerability with CWE-59: Improper Link Resolution Before File Access ('Link Following')
Is marked publicly disclosed, but Not Exploited, Exploitation LESS likely.
What privileges could be gained by an attacker who successfully exploited this vulnerability?
An authenticated attacker would be able to delete targeted files on a system which could result in them gaining SYSTEM privileges.
What actions do customers need to take to protect themselves from this vulnerability?
We released CVE-2024-30060 to help keep customers protected. Customers who have installed the latest updates, or have automatic updates enabled, are already protected. Customers who have disabled Automatic Extension Upgrades or would like to upgrade an extension immediately must manually update their Azure Monitor Agent to the latest version. For more information on how to perform a manual update, see Manage Azure Monitor Agent.
Dan Goodin
dangoodin@infosec.exchangeInfrastructure used to maintain and distribute the Linux operating system kernel was infected for two years, starting in 2009, by sophisticated malware that managed to get a hold of one of the developers’ most closely guarded resources: the /etc/shadow files that stored encrypted password data for more than 550 system users, researchers said Tuesday.
The unknown attackers behind the compromise infected at least four servers inside kernel.org, the Internet domain underpinning the sprawling Linux development and distribution network, the researchers from security firm ESET said. After obtaining the cryptographic hashes for 551 user accounts on the network, the attackers were able to convert half into plaintext passwords, likely through password-cracking techniques and the use of an advanced credential-stealing feature built into the malware. From there, the attackers used the servers to send spam and carry out other nefarious activities. The four servers were likely infected and disinfected at different times, with the last two being remediated at some point in 2011.
An infection of kernel.org came to light in 2011, when kernel maintainers revealed that 448 accounts had been compromised after attackers had somehow managed to gain unfettered, or “root,” system access to servers connected to the domain. Maintainers reneged on a promise to provide an autopsy of the hack, a decision that has limited the public’s understanding of the incident.
In 2014, ESET researchers said the 2011 attack likely infected kernel.org servers with a second piece of malware they called Ebury. The malware, the firm said, came in the form of a malicious code library that, when installed, created a backdoor in OpenSSH that provided the attackers with a remote root shell on infected hosts with no valid password required. In a little less than 22 months, starting in August 2011, Ebury spread to 25,000 servers. Besides the four belonging to the Linux Kernel Organization, the infection also touched one or more servers inside hosting facilities and an unnamed domain registrar and web hosting provider.
A 47-page report summarizing Ebury's 15-year history said that the infection hitting the kernel.org network began in 2009, two years earlier than the domain was previously thought to have been compromised. The report said that since 2009, the OpenSSH-dwelling malware has infected more than 400,000 servers, all running Linux except for about 400 FreeBSD servers, a dozen OpenBSD and SunOS servers, and at least one Mac.