Posts
3742Following
723Followers
1596Veronica
veronica@xoxo.zoneHere, I made you a Slack emoji for when you're talking about GenAI
Matt Blaze
mattblaze@federate.socialToday is the 30th anniversary of the announcement of the Clipper Chip, an ultimately failed proposal for "key escrow" cryptography that ignited the "crypto wars" of the 1990's.
jiska 🦄
jiska@chaos.social
Want to get into reversing or learn new advanced topics? Here are my favorite tutorials, talks, blog posts and podcasts! #reverseengineering #reversingshorts
https://youtu.be/6N0mk9s0ylU
alcinnz
alcinnz@floss.socialI finished reading World Wide Waste by Gerry McGovern. I'd consider it essential reading for anyone working with computers!
https://gerrymcgovern.com/books/world-wide-waste/
It's well cited (though I still need to check those citations) & uses maths effectively to make it's point.
That computers + (surveillance) capitalism is actually worse for the environment than the predigital era. That we can and must move slow and fix things, and fund that vital work directly.
OpenBSD Now!
openbsdnow@bsd.networkSomewhere, someone finally made this and I think it's beautiful
Zack Whittaker
zackwhittaker@mastodon.socialNew: Online alcohol recovery startups Monument and Tempest have confirmed they were sharing the personal information and health data of their patients, without their consent, with advertising giants for *years*.
More: https://techcrunch.com/2023/04/04/monument-tempest-alcohol-data-breach/
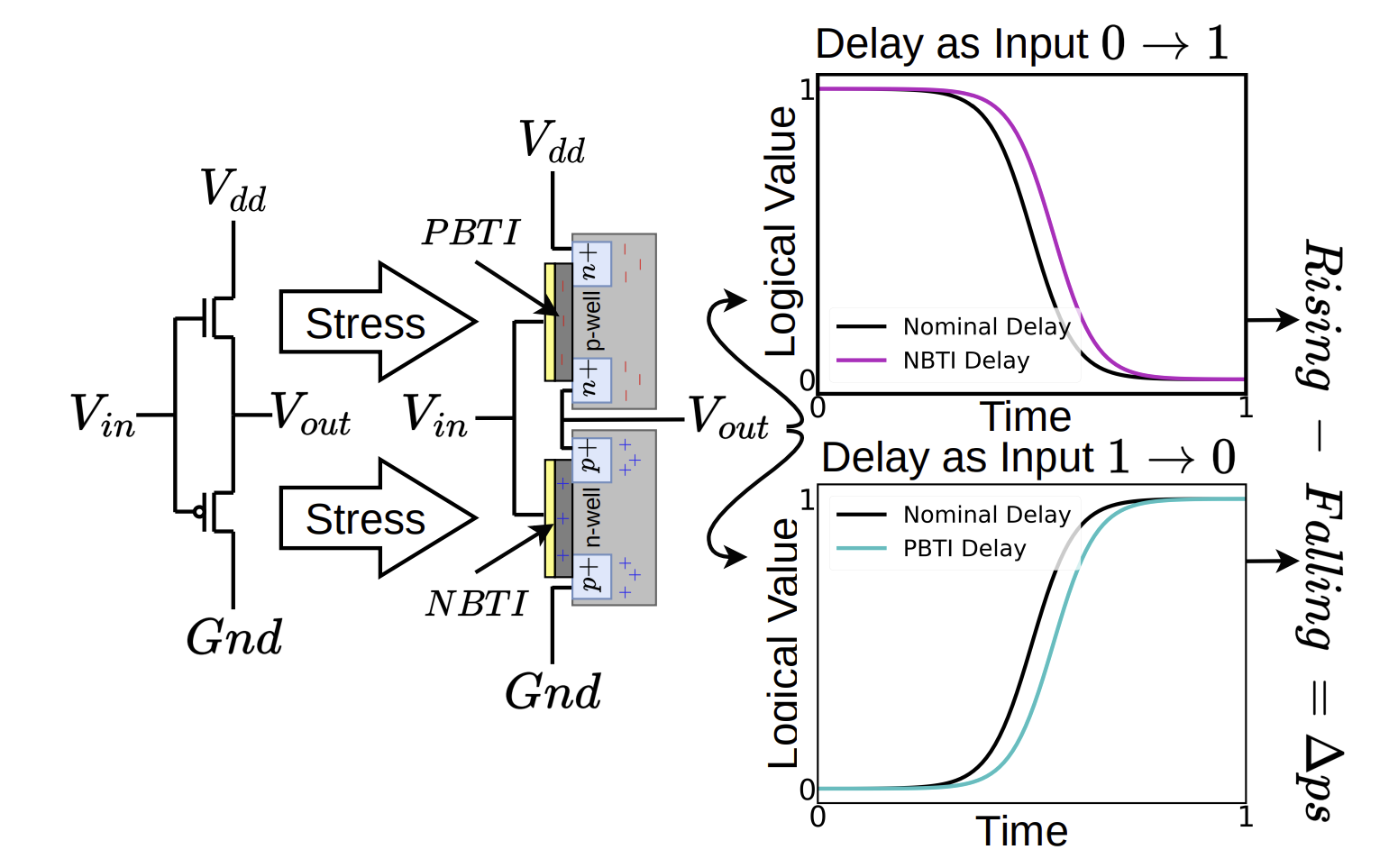
Hovav Shacham
hovav@infosec.exchangeI guarantee that this is the wildest paper you’ll read all year. Drewes et al., “Pentimento: Data Remanence in Cloud FPGAs,” https://arxiv.org/abs/2303.17881
We find that a remote attacker can recover “FPGA pentimentos” — long-removed secret data belonging to a prior user or proprietary design image on a cloud FPGA. Just as a pentimento of a painting can be exposed via infrared imaging, FPGA pentimentos can be exposed via signal
timing sensors instantiated on a remote cloud FPGA. The sensitive data constituting an FPGA pentimento is imprinted to the device through bias temperature instability effects on the underlying transistors. We demonstrate how this slight degradation can be measured using a time-to-digital converter when an adversary programs one into the target cloud FPGA. This technique allows an attacker to ascertain previously safe information, after it is no longer explicitly present, on cloud FPGAs. Notably, it can allow an attacker to (1) extract proprietary details or keys from an encrypted FPGA design image available on the AWS marketplace and (2) recover information from a previous user of a cloud-FPGA. Both threat models are experimentally validated on the AWS F1 platform.
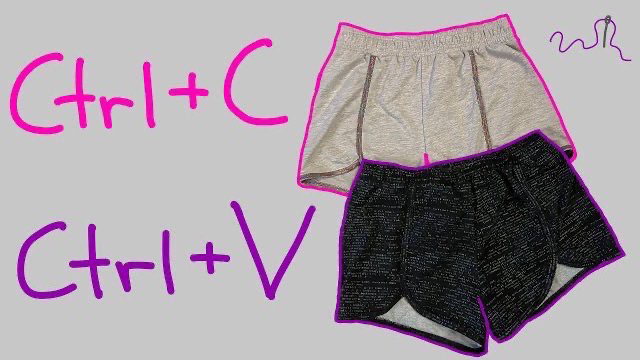
jiska 🦄
jiska@chaos.social
The Reversing Shorts video you've been waiting for: How to actually reverse engineer shorts? 🩳🧵🪡
Follow along this sewing tutorial and get to know how to copy your favorite clothes! #reverseengineering #sewing @sewing
qwertyoruiopz
qwertyoruiop@nso.groupDISCLAIMER: me and the ‘nso.group’ domain are not affiliated with NSO Group, and the domain is just a meme domain I owned for 5+ years
Keith D Johnson
KeithDJohnson@sfba.social'Encouraging creative theft'.
Would this work in USAnian cities? Certainly in some neighborhoods.
Photo text excerpt from #BillMollison's autobiography, Travels In Dreams.
#UrbanPermaculture #fruit #UrbanFarming #Rewilding #GuerillaHorticulture
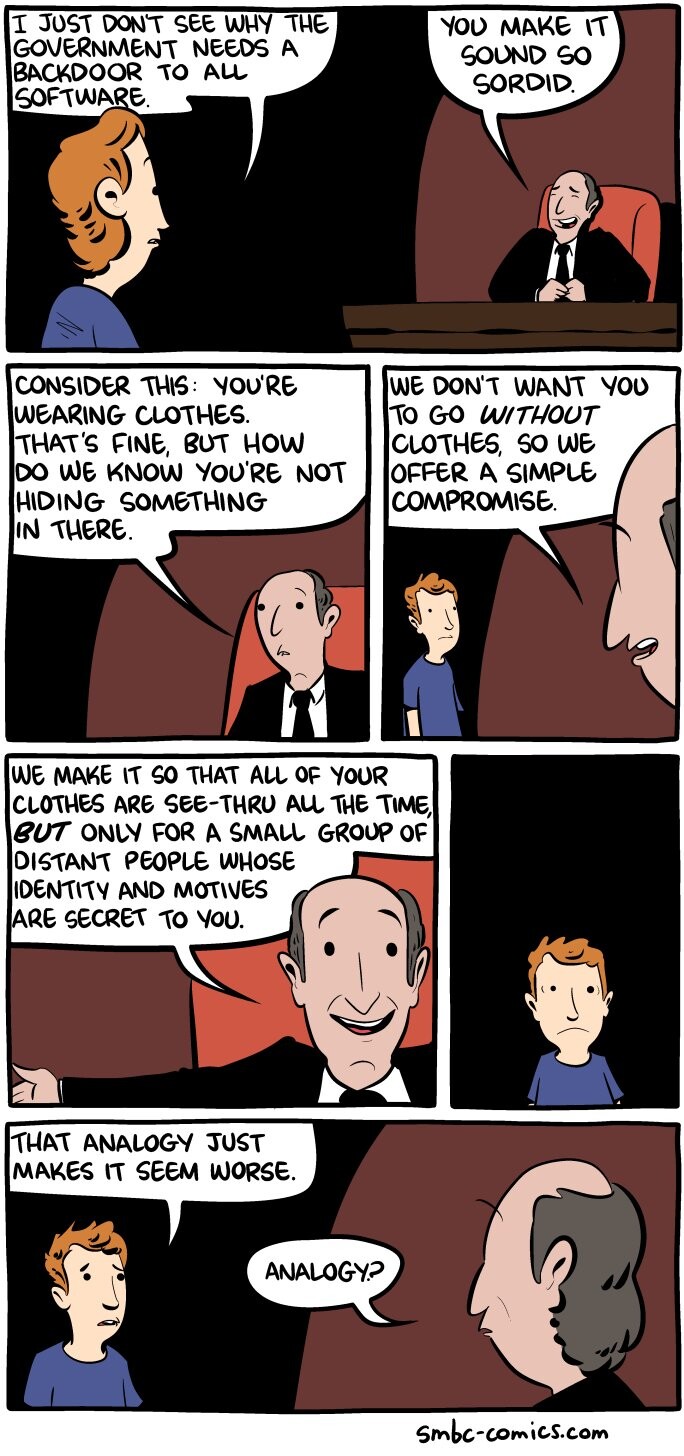
While the #CryptoWars continue, we would like to remind everyone of two very convincing facts for the pro #encryption side:
✅ 1. Encryption can't be outlawed
✅ 2. Backdoors for the good guys only are impossible
Read our position on the ongoing crypto wars: https://tutanota.com/crypto-wars/
David Buchanan
retr0id@retr0.idMy writeup on exploiting CVE-2023-21036 (un-cropping Android screenshots!)
https://www.da.vidbuchanan.co.uk/blog/exploiting-acropalypse.html
Molly White
molly0xfff@hachyderm.io"it's not like we can put the genie back in the bottle! 🤷" – VC who stands to profit massively from the release of the genie, and who has worked tirelessly to release said genie
Linus Torvalds
torvalds@social.kernel.orgRandom first trial post: today, March 14th, is the 29th anniversary of the Linux 1.0 announcement.
Of course, there are other arguably more important dates in Linux history, but this is one of them.
Mx. Moriarty 🏳️⚧️ 
jpasski@infosec.exchange
Lol looks like JFrog finally disclosed CVE-2022-0668 [1]. @matthias_kaiser and I found that around a year ago, along with CVE-2022-0573 [2]. Coupled together we could unauth RCE Artifactory 🔥
Funny how they marked the RCE as being as severe as a blind SQLi, a “High”🤪
In neither case were we told the issues were fixed… 🙈🙉🙊
1. https://www.jfrog.com/confluence/display/JFROG/CVE-2022-0668%3A+Artifactory+Authentication+Bypass
2. https://www.jfrog.com/confluence/display/JFROG/CVE-2022-0573%3A+Artifactory+Vulnerable+to+Deserialization+of+Untrusted+Data
Kevin Beaumont
GossiTheDog@cyberplace.socialI wonder if Microsoft should meaningfully strengthen HTA files (not with SmartApps)… (yes, they definitely should) HT @campuscodi
hexnomad
hexnomad@infosec.exchangeTwo vulnerabilities I disclosed to @msftsecresponse got patched today. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-23415 and https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-23416. Both are are RCE and given critical severity. The first is a pre-auth vuln in ICMP.
From the bulletin:
How could an attacker exploit this vulnerability?
An attacker could send a low-level protocol error containing a fragmented IP packet inside another ICMP packet in its header to the target machine. To trigger the vulnerable code path, an application on the target must be bound to a raw socket.