Posts
2297Following
461Followers
1105Heretek of Silent Signal
bert hubert 🇺🇦🇪🇺
bert_hubert@fosstodon.orgWill quantum be big in war? After reading this NATO chart, I'm not sure what they really think. Source: https://www.mscoe.org/document/quantum-information-and-modelling-simulation-integration-initial-concept/
Hamid Kashfi
Hamid@infosec.exchangeThe InfoSec Weekly is out! https://paper.li/hkashfi/1447346035?share_id=0d9958c0-c581-11ed-890c-fa163ed80008 #infosec #cybersecurity
Ravi Nayyar
ravirockks@infosec.exchange'In late 2022 and early 2023, Project Zero reported eighteen 0-day vulnerabilities in Exynos Modems produced by Samsung Semiconductor. The four most severe of these eighteen vulnerabilities... allowed for Internet-to-baseband remote code execution. Tests conducted by Project Zero confirm that those four vulnerabilities allow an attacker to remotely compromise a phone at the baseband level with no user interaction [YIKES!], and require only that the attacker know the victim's phone number. With limited additional research and development, we believe that skilled attackers would be able to quickly create an operational exploit to compromise affected devices silently and remotely. [UM, WOT?!]
'Due to a very rare combination of level of access these vulnerabilities provide and the speed with which we believe a reliable operational exploit could be crafted, we have decided to make a policy exception to delay disclosure for the four vulnerabilities that allow for Internet-to-baseband remote code execution'. [Yeah, not surprising - these are BAD bugs.]
https://googleprojectzero.blogspot.com/2023/03/multiple-internet-to-baseband-remote-rce.html
Molly White
molly0xfff@hachyderm.io"it's not like we can put the genie back in the bottle! 🤷" – VC who stands to profit massively from the release of the genie, and who has worked tirelessly to release said genie
Saagar Jha
saagar@saagarjha.com* several thousand engineers working in a 100% memory safe language on the world’s most widely deployed smartphone os
* one missing character boi
https://twitter.com/ItsSimonTime/status/1636857478263750656
Tim (Wadhwa-)Brown 
timb_machine@infosec.exchange
Questions to ask your UNIX engineering teams:
1) Do we track users and their process execution and termination?
3) How do we secure and monitor world writable locations on our boxes?
3) Do we do anything to monitor the integrity of our log generator configs (be that syslogd, auditd, applications etc)?
4) Do we collect .bash_history or equivalent?
5) Do we have any way of knowing if a system or process is generating raw packets or using the packet capture (BPF) APIs?
Fabian Yamaguchi
fabs@home.social"Microsoft tries to justify AI’s tendency to give wrong answers by saying they’re ‘usefully wrong’" - https://www.cnbc.com/2023/03/16/microsoft-justifies-ais-usefully-wrong-answers.html - cool, yeah, that about sums up the state of the industry.
Mara
Mara@hachyderm.io"programming is serious and not a game [..] stop with the outfits and princess programmer stuff"
I think we should all start writing software and giving talks while wearing princess dresses. 👸👗👩💻
Justin Schuh
jschuh@infosec.exchangeI was barely recovered from the covid that the kids brought home before they brought home yet another cold. My point here is that children are always trying to kill you, typically with biological warfare, and in clear violation of United Nations Biological Weapons Convention.
Hex-Rays SA
HexRaysSA@infosec.exchangeDid you know that IDA Free has been updated to 8.2 and gained some new features 👇 Give it a try today 🌐 https://hex-rays.com/ida-free/?utm_source=Social-Media-Post&utm_medium=Mastodon&utm_campaign=ida-free-updated-8-2
Damien Miller
djm@cybervillains.comOpenSSH 9.3 has been released.
This release contains fixes for a security problem relating to destination-restricted smartcard keys in ssh-agent, a memory safety fault (out-of-bound stack read) in some DNS-related code used by VerifyHostKeyDNS as well as a number of small bugfixes and minor features
Robert McNees
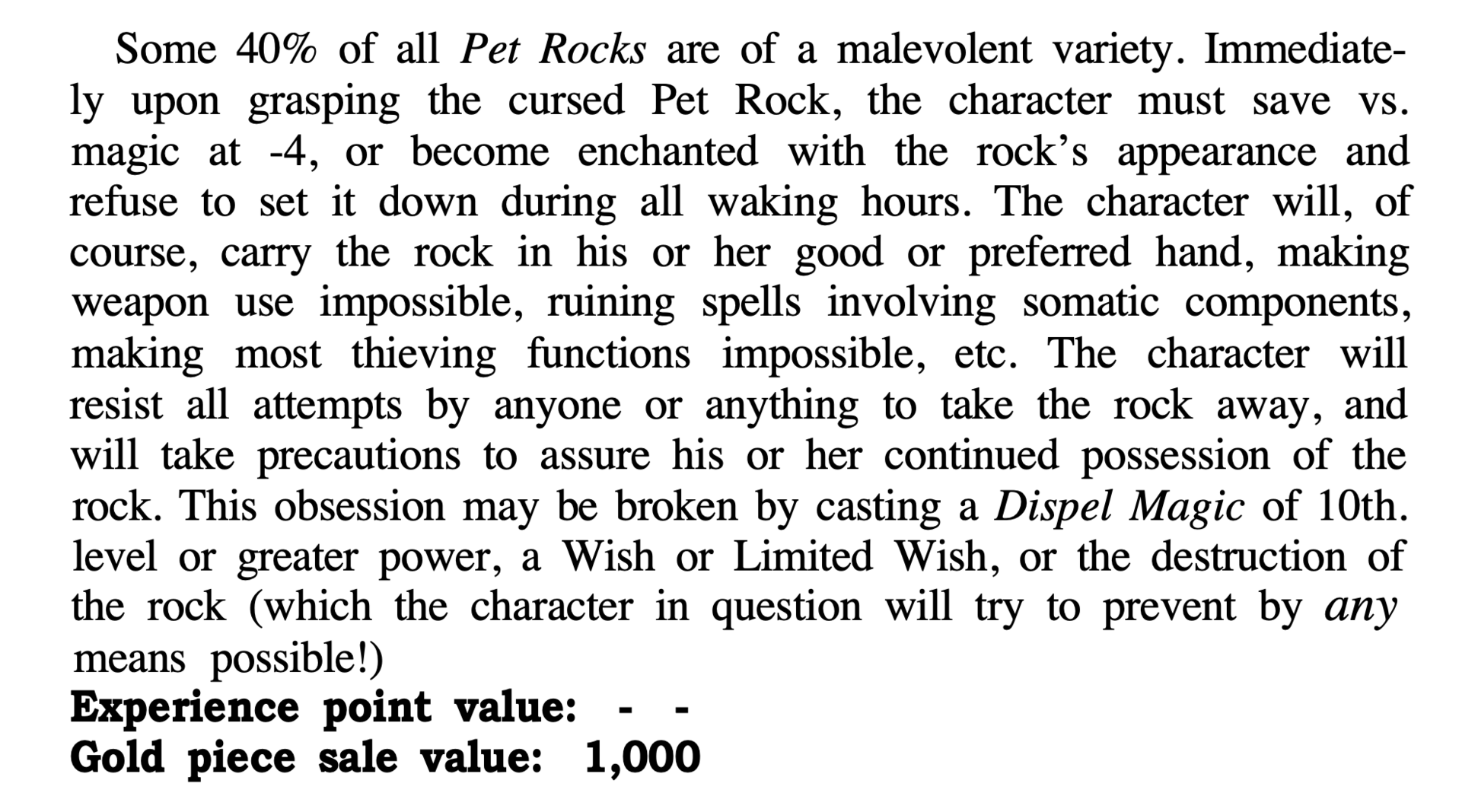
mcnees@mastodon.socialThis description of a cursed magic rock from an old issue of Dragon Magazine is basically just a cell phone.
Marco Ivaldi
raptor@infosec.exchangeExamining #OpenSSH Sandboxing and Privilege Separation – Attack Surface Analysis
// by jfrog
Linus Torvalds
torvalds@social.kernel.orgRandom first trial post: today, March 14th, is the 29th anniversary of the Linux 1.0 announcement.
Of course, there are other arguably more important dates in Linux history, but this is one of them.
Jonni Passki 🏳️⚧️ 
jpasski@infosec.exchange
Lol looks like JFrog finally disclosed CVE-2022-0668 [1]. @matthias_kaiser and I found that around a year ago, along with CVE-2022-0573 [2]. Coupled together we could unauth RCE Artifactory 🔥
Funny how they marked the RCE as being as severe as a blind SQLi, a “High”🤪
In neither case were we told the issues were fixed… 🙈🙉🙊
1. https://www.jfrog.com/confluence/display/JFROG/CVE-2022-0668%3A+Artifactory+Authentication+Bypass
2. https://www.jfrog.com/confluence/display/JFROG/CVE-2022-0573%3A+Artifactory+Vulnerable+to+Deserialization+of+Untrusted+Data
buherator
buheratorOr that allowing sign-ins with multiple accounts (which this thing is supposed to handle) to the same service would result in an acceptable user experience??
+ notice how the title says nothing about what action you are performing (logout), and that while you already chose to log out, your session is still active until you click though this dialog.
#UX #microsoft #idiots
jomo
jomo@mstdn.ioThanks Docker Hub for finally killing yourself 👍👍👍
https://blog.alexellis.io/docker-is-deleting-open-source-images/ #Docker #Dockerhub