Posts
3804Following
723Followers
1598buherator
buheratorShow content
Working search!
Talos Vulnerability Reports
talosvulnsLibRaw HuffTable::initval heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2330
CVE-2026-20911
Talos Vulnerability Reports
talosvulnsLibRaw lossless_jpeg_load_raw heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2331
CVE-2026-21413
Talos Vulnerability Reports
talosvulnsLibRaw x3f_thumb_loader heap-based buffer overflow vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2026-2358
CVE-2026-20889
Bastard Operator from Mousey Hell
algernon@come-from.mad-scientist.clubA few weeks ago, someone reported an obsrvation on the iocaine bug tracker: ClaudeBot appeared to have figured out how to remove the poison ID from poisoned URLs.
That was a worrying development, so I set out to do some experiments in The Lab. I wasn't unprepared for this development, and had a few tricks lined up to address it. I wanted to test which one works.
After two and half weeks of experiments, I'm happy to report that Claude has not started to remove iocaine's poison IDs from URLs. The bot merely fails at the basic task of resolving relative URLs.
Both the built-in script and Nam-Shub of Enki generate relative URLs, and only include the poison ID if the entry URL didn't have one. Thus, whenever ClaudeBot hit a poisoned URL, it failed to resolve the poison-ID less relative URL, and constructed an URL that did not have one.
The straightforward fix for this is to not trust the crawlers to be able to resolve relative URLs.
Will Dormann
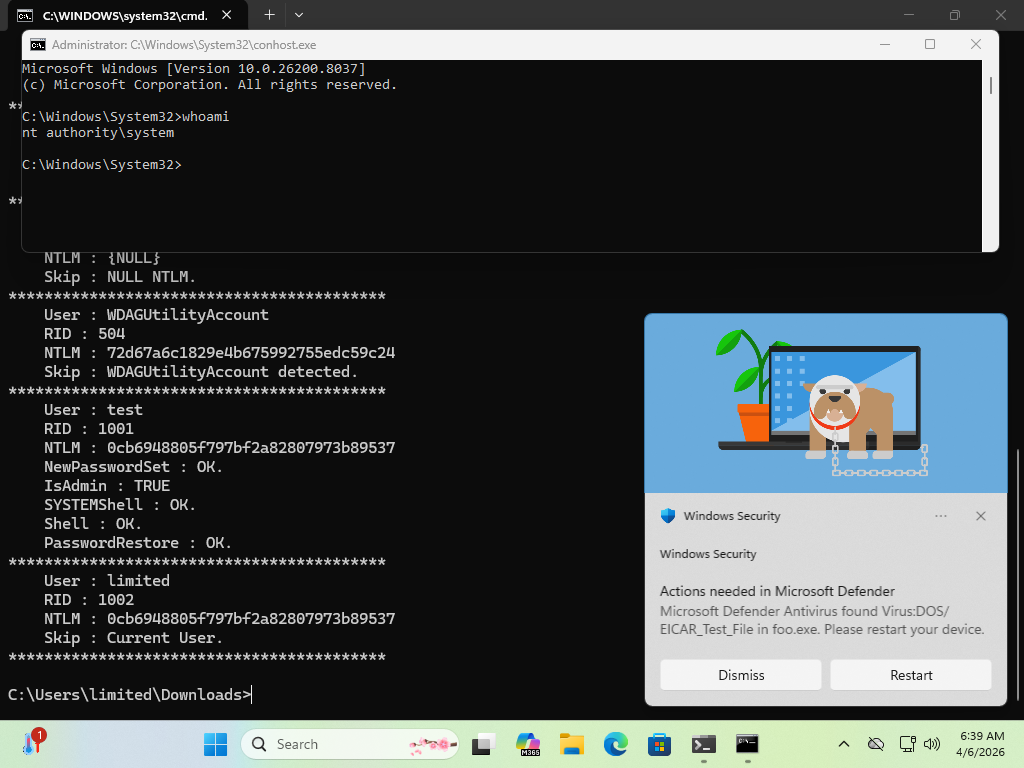
wdormann@infosec.exchangeThere's a new Windows 0day LPE that has been disclosed called BlueHammer. The reporter suggests that it's being disclosed due to how MSRC operates these days.
MSRC used to be quite excellent to work with.
But to save money Microsoft fired the skilled people, leaving flowchart followers.
I wouldn't be surprised if Microsoft closed the case after the reporter refused to submit a video of the exploit, since that's apparently an MSRC requirement now. 😂
Anyway, yeah, it works. Maybe not 100% reliably, but well enough...
Trail of Bits
trailofbits@infosec.exchangeThousands of CEOs said AI had no impact on productivity. We use AI to catch 200 bugs/week where we used to find 15, and generate $8M per sales rep.
95% of the company pushed back when we started. At unprompted, Dan Guido explains how our 140-person team went AI-native.
https://www.youtube.com/watch?v=kgwvAyF7qsA
Trail of Bits
trailofbits@infosec.exchangeBefore its launch, we audited WhatsApp's Private Processing TEEs and found 8 high-severity issues (patched). The enclaves yielded to injected config files, unmeasured ACPI tables, spoofed firmware levels, and stale attestation reports.
TEE security is only as good as the implementation details. Four lessons and the full report: https://blog.trailofbits.com/2026/04/07/what-we-learned-about-tee-security-from-auditing-whatsapps-private-inference/
Frederik Braun �
freddy@security.plumbing@buherator I think your configuration might be borked. We do not force a restart. You should only get this error if the binary file on disk changed while browsing. In that case, Firefox is unable to create a new process due to API incompatibility. Do you use multiple Firefoxes in parallel?
buherator
buheratorShow content
https://www.bloomberg.com/news/articles/2026-04-07/viktor-orban-offered-to-help-vladimir-putin-call-transcript-shows
Leaking intercepted Orban-Putin comms is an especially nice touch right when J.D.Vance is visiting Budapest...
buherator
buherator[1] https://www.reddit.com/r/firefox/comments/16ug51m/is_there_any_way_to_stop_firefox_from_forcing_a/
James Forshaw 
tiraniddo@infosec.exchange
I've put up the slides from my Zer0Con 2026 presentation on Administrator Protection. https://github.com/tyranid/infosec-presentations/blob/master/Zer0Con/2026/Protecting%20your%20Administrator.pdf
daniel:// stenberg://
bagder@mastodon.socialIf your Open Source project sees a steep increase in number of high quality security reports (mostly done with AI) right now (#curl, Linux kernel, glibc confirmed) please tell me the name of this project.
(I'd like to make a little list for my coming talk on this.)