Posts
3792Following
723Followers
1598abadidea
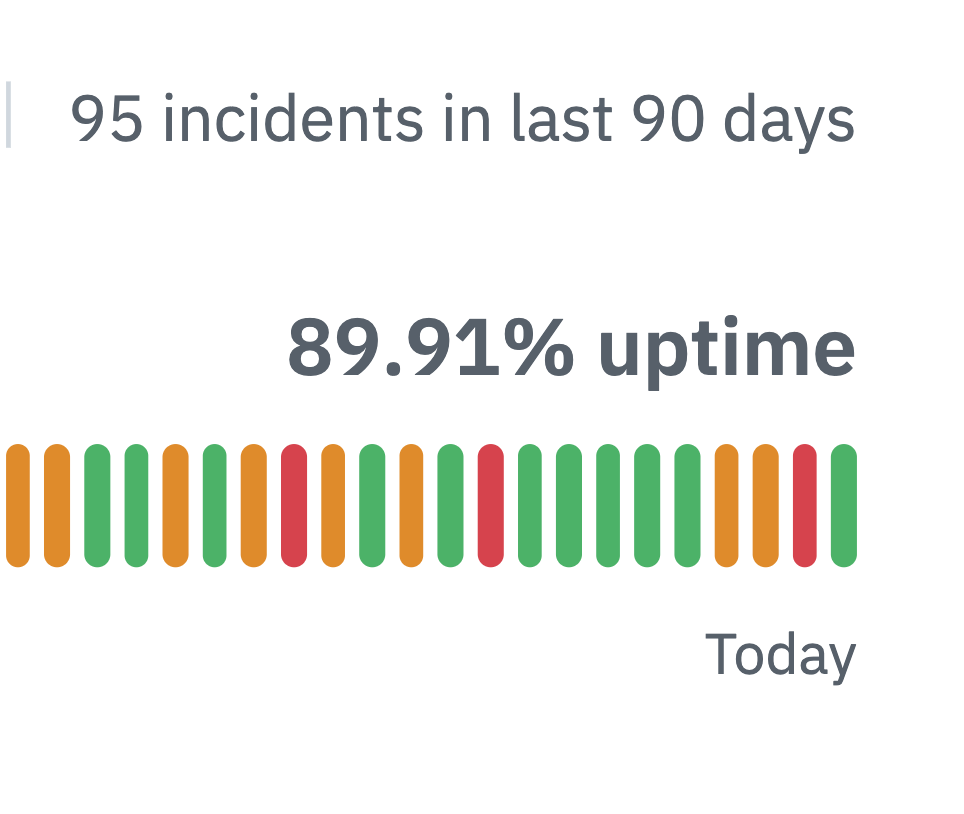
0xabad1dea@infosec.exchangeIT'S HAPPENING
GITHUB, THE FIRST ENTERPRISE CLOUD SOLUTION TO REACH ZERO NINES RELIABILITY
Rebane
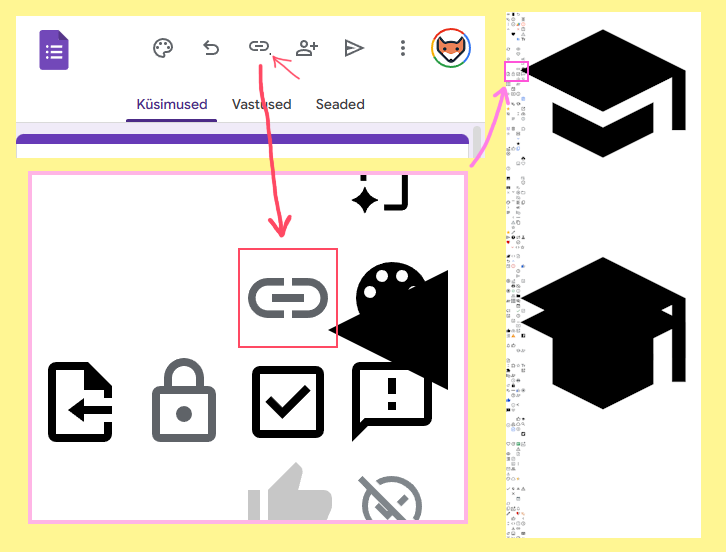
rebane2001@infosec.exchangedid you know? the google forms share icon has a stray pixel in its corner
why? because the icon spritesheet has a massive black triangle overlapping the icons
what is that triangle? it's a giant out-of-bounds hat!
Project Zero Bot
p0botWindows: OSK Shared Session Key EoP
https://project-zero.issues.chromium.org/issues/466303419
CVE-2026-24291
Project Zero Bot
p0botWindows: ATBroker CopySettingsToLockedDesktop Information Disclosure
https://project-zero.issues.chromium.org/issues/466301558
CVE-2026-25186
Project Zero Bot
p0botWindows: WinLogon WlAccessabilitypDeleteSATKey Registry Deletion EoP
https://project-zero.issues.chromium.org/issues/466300525
CVE-2026-25187
cynicalsecurity 
cynicalsecurity@bsd.network
Lessons learned from the Artemis 2 mission:
1. some genius thought sending Outlook to space was a good idea,
2. some other genius thought that Bluetooth in space was a good idea,
3. plumbers are in demand, even in space.

buherator
buheratorhttps://www.ibm.com/support/pages/node/7268448?myns=swgother&mynp=OCSSTS2D&mynp=OCSWG60&mynp=OCSSKWKM&mynp=OCSSB23CE&mynp=OCSS9QQS&mynp=OCSSC5L9&mync=A&cm_sp=swgother-_-OCSSTS2D-OCSWG60-OCSSKWKM-OCSSB23CE-OCSS9QQS-OCSSC5L9-_-A
That hard-coded key shouldn%27t be hard to find...
buherator
buheratorhttps://nootnooot.codeberg.page/segway-ninebot-ble
Open Source Security mailing list
oss_security@bird.makeupOVE-20260330-0003: Linux: KVM shadow EPT stale rmap use-after-free https://www.openwall.com/lists/oss-security/2026/03/30/5
Found through fuzzing, exploitable from any x86 guest with nested virtualization enabled or using shadow paging. Guest-to-host DoS and kernel heap corruption, potentially aiding VM escape.
Chad 
chad@mstdn.ca
My therapist said I need to find things to keep me busy, so I created the @cdnspace Artemis II dashboard.
I reverse-engineered the Unity Engine powering the NASA AROW visualization and found an absolute treasure trove of data to display.
Little did I expect that it's now being seen by anywhere from 200 to 600 people at any given time with 130,000 people having looked at it in the last 24 hours. People are even building projects around my API.
Yesterday, I received a message on LinkedIn from someone working in Mission Control in Houston... and they're using my dashboard! He even sent me a photo, but I can't share it until after the crew has splashed down.
Mind blown, and an absolute pick-me-up. The best part? It's being served from my basement.
Jon Snow
jonsnow@mastodon.onlineGerman digital ID will require an Apple/Google Account
Rooted/jailbroken phone? Custom ROM? Latest updates not applied? Authentication denied, Mutterficker!
Apple & Google become gatekeepers. "Your" device will be constantly monitored - for "compliance". "And you will be happy".
#DigitalID #IDVerification #Google #Apple #Android #iOS #technology #privacy #surveillance #enshittification #dystopia #BigTech #Germany #EU
buherator
buheratorhttps://androidoffsec.withgoogle.com/posts/a-technical-deep-dive-into-cve-2024-23380-exploiting-gpu-memory-corruption-to-android-root/
Samantaz Fox
SamantazFox@infosec.exchangeHello fedi!
I have an .MVAX #firmware #update file for an MV Silicon chip (unknown model).
Has someone already encountered those? And if yes, is there some documentation, tooling or existing #ReverseEngineering work done of that format?
For the record, the file magic (first 8 bytes) is as follow:4D 56 B5 58 05 01 13 00
And the end of the file contains the following (no spaces, wrapping is mine):
MVSKeyFileMVBP10<0x90>0xBE>SIMPLEs
<0xD3><0x9A>.<0x90><0xD9>
MVSILICONKEYFL<0x00><0x00>
<0xFF><0xBD><0x00>0x00>
Thanks in advance for your help!!
#embedded #mcu #blob #fileformat #FileFormatAnalysis #binary #extraction