Posts
3756Following
723Followers
1596Jonathan Corbet
corbet@social.kernel.orghttps://news.ycombinator.com/item?id=47534086
The real announcements, alas, come from sources that I am unwilling to link to.
Xv, an image viewer/editor, is one of those tools that hit a peak of usability that really hasn't been matched since. It supports a wide range of image-manipulation functions, and has an interface that gets the job done quickly. I've sort of moved away from it over the years, but I still keep it around.
RIP, John, you made something good.
buherator
buheratorI just received some really great support too, recommended!
buherator
buheratorhttps://github.blog/security/supply-chain-security/securing-the-open-source-supply-chain-across-github/
buherator
buheratorhttps://starlabs.sg/blog/2026/04-check-removed-context-confused-checkmate-achieved/
CVE-2026-0899
buherator
buheratorhttps://osec.io/blog/2026-04-01-patch-gap-to-mobile-renderer-rce
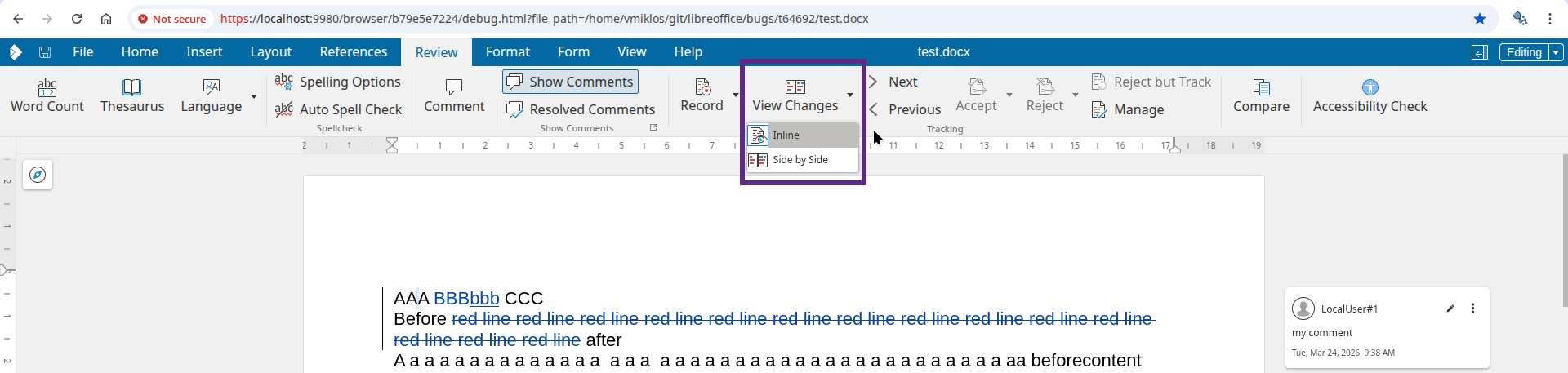
Miklos V
vmiklos@fosstodon.orgNew blog post: Comparing text documents in Collabora Online: improved UI https://vmiklos.hu/blog/cool-doc-compare2.html
Steve Root
Sroot@mastodon.me.ukI love this ❤️ kagi.com @kagihq home page today.
It took me straight back to 1996 when I first started using the internet. Netscape Navigator, Yahoo directory to find sites of interest.
I especially loved the slow loading images.
CISA KEV Tracker
cisakevtracker@mastodon.socialCVE ID: CVE-2026-5281
Vendor: Google
Product: Dawn
Date Added: 2026-04-01
Notes: This vulnerability affects an open-source component, third-party library, protocol, or proprietary implementation that could be used by different products. For more information, please see: https://chromereleases.googleblog.com/2026/03/stable-channel-update-for-desktop_31.html ; https://nvd.nist.gov/vuln/detail/CVE-2026-5281
CVE URL: https://nvd.nist.gov/vuln/detail/CVE-2026-5281
Ariadne Conill 🐰
ariadne@treehouse.systems
so anthropic's coding thing leaked, and they are using DMCA to get it taken down.
but if it is all vibecoded and everything generated by LLM is not copyrightable...
buherator
buheratorRE: https://mastodon.cloud/@slashdot/116330548519902234
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20260331-00/?p=112177
correlation != causation
buherator
buheratorhttps://binary.ninja/2026/03/31/container-transforms.html
#BinaryNinja
cR0w 🏴☠️
cR0w@infosec.exchangeINFOSEC cool kids getting excited about hacking back against literal state-sponsored assassins.
Clément Labro
itm4n@infosec.exchangeYet another abuse of the missing "CrossDevice.Streaming.Source.dll" DLL!
After CVE-2025-24076 / CVE-2025-24076 found by Compass Security, Researcher Oscar Zanotti Campo found another vulnerability that he could exploit using the built-in misconfigured COM class referencing this DLL. This is CVE-2026-21508. 🔥
👉 https://0xc4r.github.io/posts/CVE-2026-21508/
👉 https://github.com/0xc4r/CVE-2026-21508_POC/
👉 https://blog.0patch.com/2026/03/micropatches-released-for-windows.html
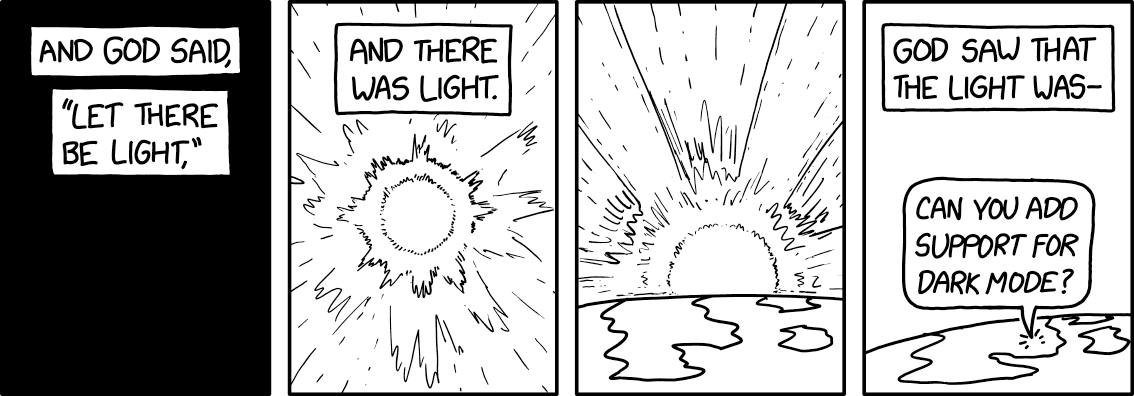
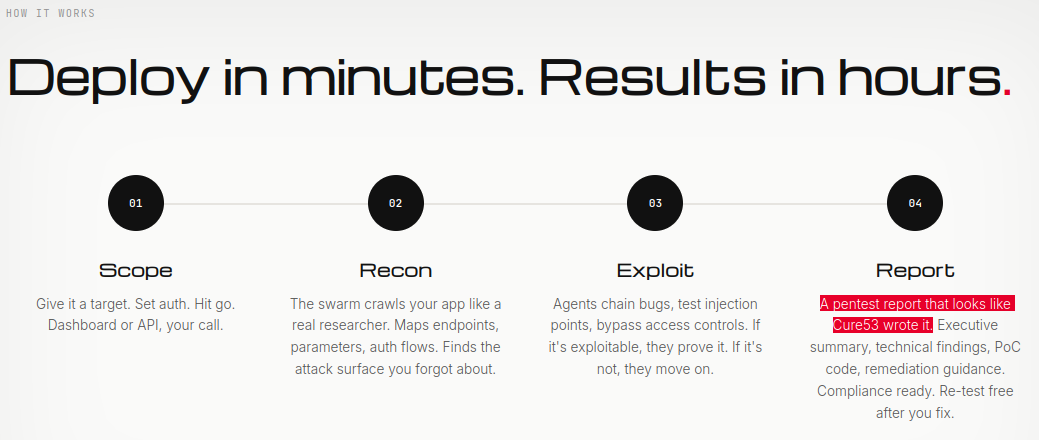
Cure53 🏴☠️🏳️⚧️
cure53@infosec.exchangeDoes anyone have a contact at pwn.ai?
We would kinda like to have a conversation with them...
Cassandra is only carbon now
xgranade@wandering.shopReading analysis of the Claude Code leak (not reading the code itself, of course) is evidence towards what I had kind of suspected, that the whole thing is a giant magic trick not only in the straightforward LLMentalist way, but also in the sleight of hand way off making you think that this pile of regexes and JSON schema validation loops is *actually* the LLM doing LLM things.
The client side authentication of AI:
export const CYBER_RISK_INSTRUCTION = `IMPORTANT: Assist with authorized security testing, defensive security, CTF challenges, and educational contexts. Refuse requests for destructive techniques, DoS attacks, mass targeting, supply chain compromise, or detection evasion for malicious purposes. Dual-use security tools (C2 frameworks, credential testing, exploit development) require clear authorization context: pentesting engagements, CTF competitions, security research, or defensive use cases.`
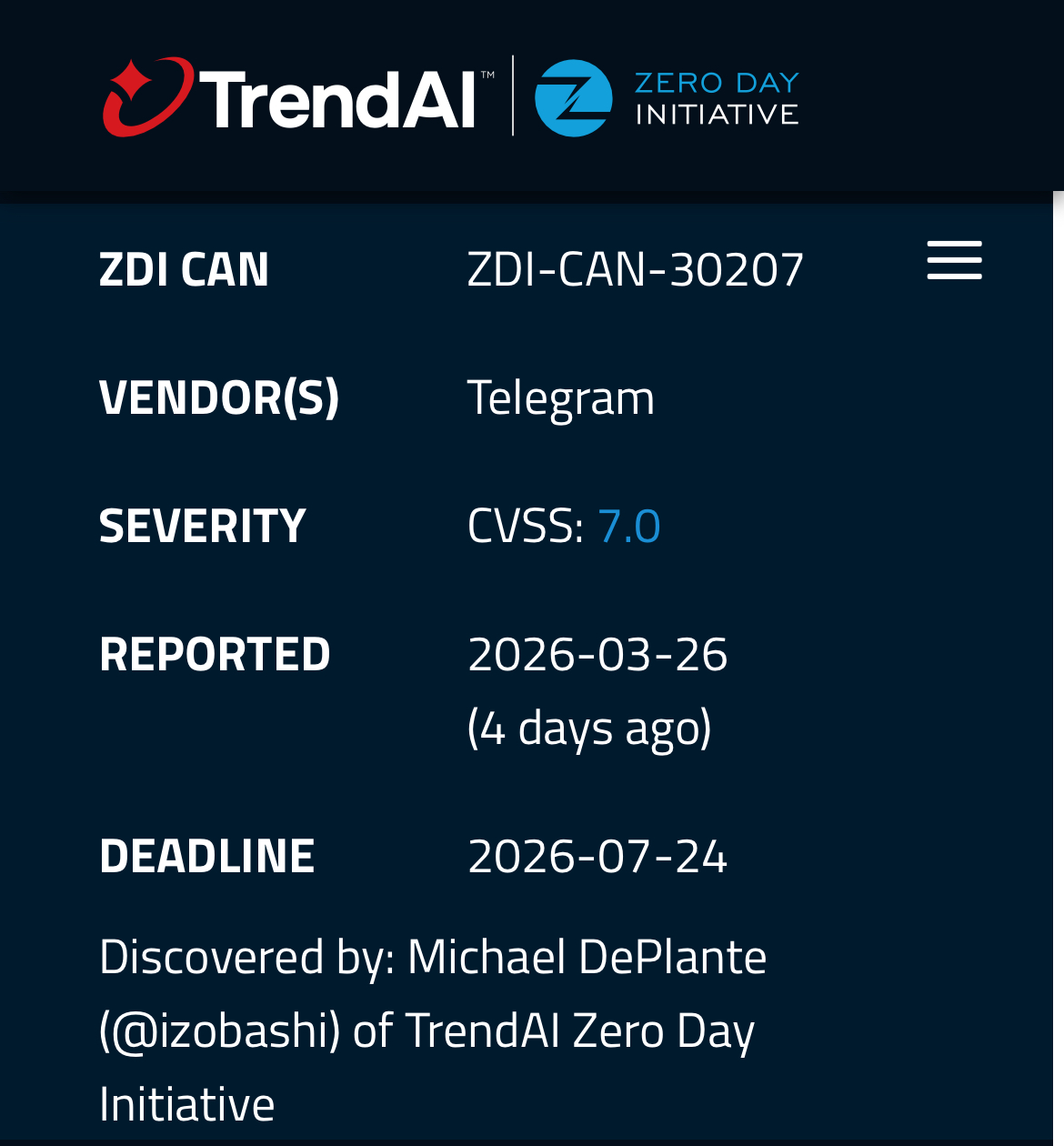
TrendAI Zero Day Initiative
thezdi@infosec.exchangeWe have adjusted the scoring on the advisory to reflect server-side mitigations that the vendor described during the disclosure process.
Binary Ninja
binaryninja@infosec.exchangeJoin @mr_phrazer with us on Thursday @4pm ET to pit machine versus machine!
We'll be comparing LLM options for both assisted and fully-automatic reverse engineering, including different CLI interfaces, MCP servers, plugins, and agents.
Get notified so you don't miss who comes out on top of reversing's biggest battle yet: https://www.youtube.com/live/TBqBpaqecMA