Posts
3733Following
723Followers
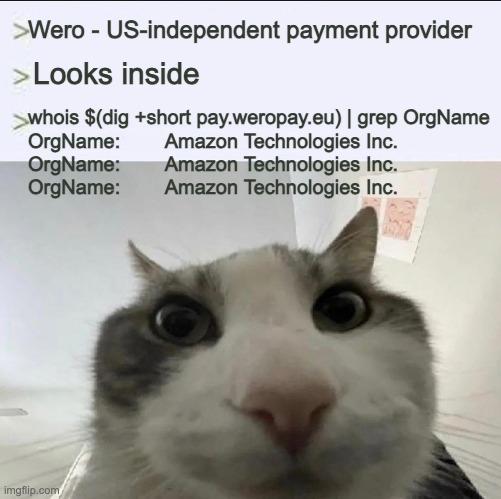
1598Did anyone got that alleged Vim RCE PoC working? MacOS doesn't seem vulnerable, Ubuntu 22/24, Debian 13, the same... Advisory says <9.2.0272 but doesn't seem like it?
Smells like AI slop hype? Yeah, kinda because most distros don't seem to ship vim with +tabpanel feature. HYPEEEEEEEEEEEEEEEEE
buherator
buheratorAlso note that gaining understanding of lib capabilities/limitations/general design *is* valuable (but also can be a prohibiting barrier of entry for small projects).
@david_chisnall
buherator
buheratorSource: I also tend to write frameworks for everything.
⠠⠵ avuko
avuko@infosec.exchangeInstead of using an LLM to write me some boilerplate and basic functionality, frontend etc, why isn’t there a library where I can find all of these?
You know, something structured and shared, again, like a library, for specific purposes, and specific languages, with educational hints from development pros on the best way to do things and maybe some constructive feedback and improvements from other people?
And why were we left to deal with stackexchange instead?
Could this have been, dare I say it: gatekeeping?
Graham Sutherland / Polynomial
gsuberland@chaos.sociali blogged about the memcmp thing
Alexandre Dulaunoy
adulau@infosec.exchangeIf someone comes to me today preaching about “post-quantum” security issues, I’ll remind them of the current state of security: the npm ecosystem gets abused daily, CI pipelines run left and right with full access to cloud services, so-called security devices like F5 and Ivanti are exposed (and compromised) to the internet, mailboxes get compromised just to change an IBAN in a PDF, and a simple phone call is still enough to get someone to hand over an MFA code.
But yes, by all means, let’s focus on post-quantum threats while handing AI tools SSH access like it’s a feature, not a confession.
Taggart
mttaggart@infosec.exchangeThis is a big deal. Already seeing evidence of this by way of OpenClaw installations.
buherator
buheratorHD Moore
hdm@infosec.exchangeTom Ptacek posted a great writeup titled "Vulnerability Research Is Cooked", covering the state of vulndev and its rapidly accelerating future:
https://sockpuppet.org/blog/2026/03/30/vulnerability-research-is-cooked/
buherator
buheratorhttps://martinvol.pe/blog/2026/03/30/how-the-ai-bubble-bursts/
buherator
buheratorbuherator
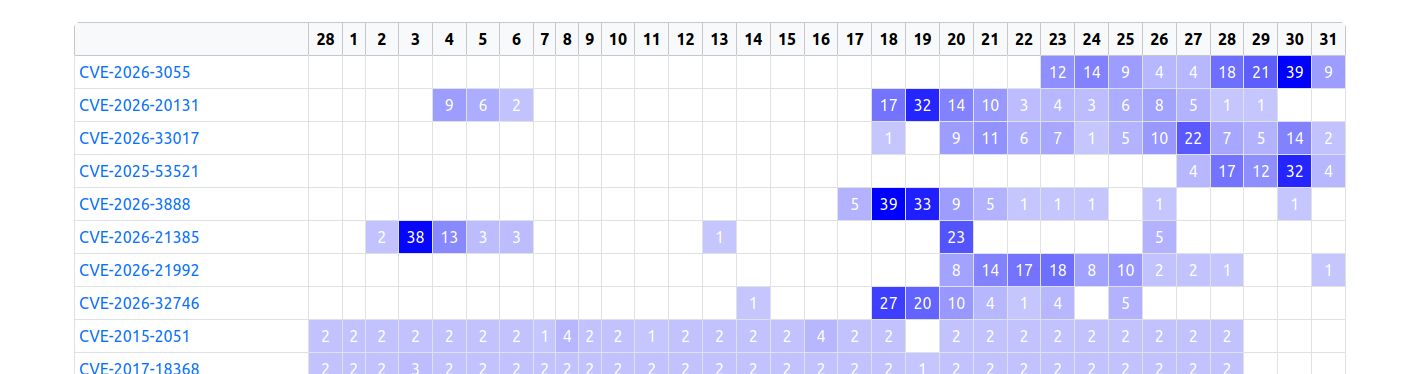
buheratorhttps://www.zerodayinitiative.com/advisories/upcoming/
Since that vuln was reported just 4 days ago my educated guess is that 1) the reporter wasn't dumb to trash their ZDI bounty by posting details online 2) someone saw the candidate and generated a slop report about it without any technical ground.
Edit: the reporter also works for ZDI, so I highly doubt they started a darkweb sell...
raptor 
raptor@infosec.exchange
Anyone knows anything more about this #Tunnelblick #vulnerability?
"CVE-2026-31893 describes a serious Tunnelblick vulnerability.
This vulnerability is present in all versions of all Tunnelblick versions 3.3beta26 through 9.0beta01.
Tunnelblick 8.0.1 and 9.0beta02 contain fixes for the vulnerability.
The CVE is expected to be published and this page updated on or before 2026-03-27."
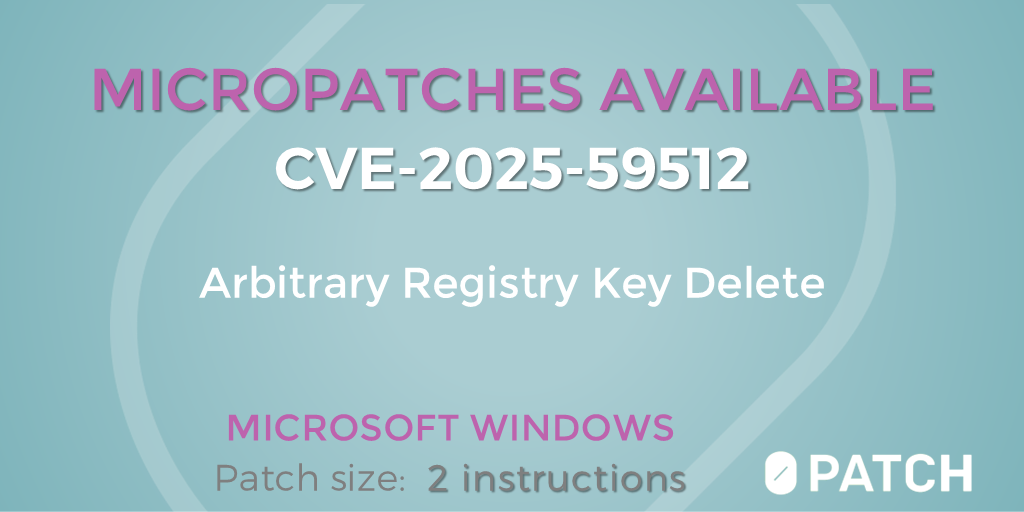
0patch
0patch@infosec.exchangeMicropatches released for Arbitrary Registry Key Delete As Local System With Consolidator Scheduled Task (CVE-2025-59512) https://blog.0patch.com/2026/03/micropatches-released-for-arbitrary.html
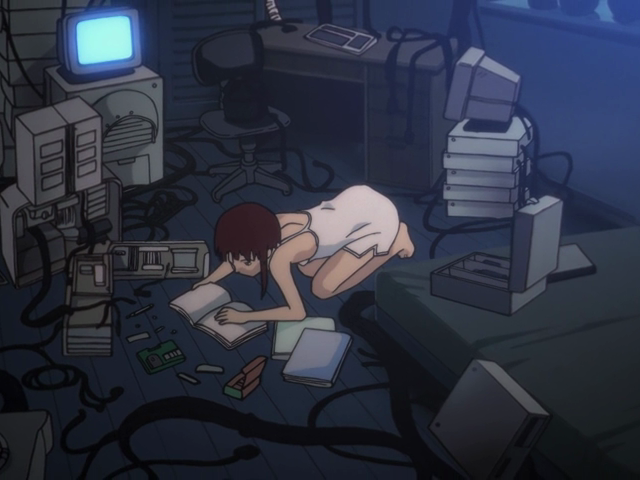
Lain Iwakura Bot
lain@cyber.ms📺 Serial Experiments Lain
🗓️ Season: S01E04
🎥 Episode: Religion
🎬 Directed by: Akihiko Nishiyama
📅 Release Date: July 27, 1998
⏯ Frame: 0191
Frédéric Jacobs
fj@mastodon.socialRE: https://social.heise.de/@heiseonlineenglish/116316847500488516
“Oh, we murdered 100 kids? Oh, that's unfortunate.
We just had some stale data in our Palantir Project Maven data lake that was used by our ‘highly accelerated, software-supported targeting process’. We'll clear the cache sometimes.”