Posts
3756Following
723Followers
1596Graham Sutherland / Polynomial
gsuberland@chaos.sociali blogged about the memcmp thing
Alexandre Dulaunoy
adulau@infosec.exchangeIf someone comes to me today preaching about “post-quantum” security issues, I’ll remind them of the current state of security: the npm ecosystem gets abused daily, CI pipelines run left and right with full access to cloud services, so-called security devices like F5 and Ivanti are exposed (and compromised) to the internet, mailboxes get compromised just to change an IBAN in a PDF, and a simple phone call is still enough to get someone to hand over an MFA code.
But yes, by all means, let’s focus on post-quantum threats while handing AI tools SSH access like it’s a feature, not a confession.
Taggart
mttaggart@infosec.exchangeThis is a big deal. Already seeing evidence of this by way of OpenClaw installations.
buherator
buheratorHD Moore
hdm@infosec.exchangeTom Ptacek posted a great writeup titled "Vulnerability Research Is Cooked", covering the state of vulndev and its rapidly accelerating future:
https://sockpuppet.org/blog/2026/03/30/vulnerability-research-is-cooked/
buherator
buheratorhttps://martinvol.pe/blog/2026/03/30/how-the-ai-bubble-bursts/
buherator
buheratorbuherator
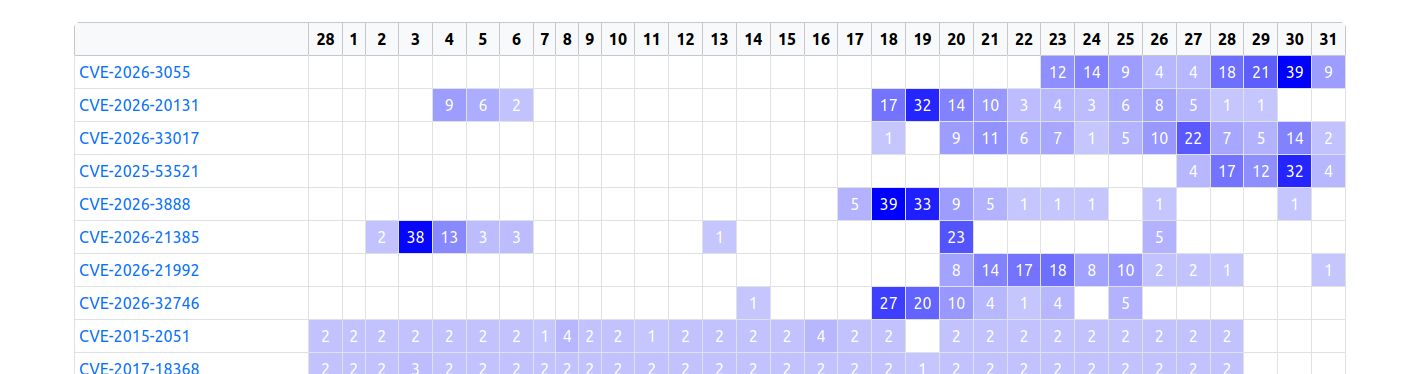
buheratorhttps://www.zerodayinitiative.com/advisories/upcoming/
Since that vuln was reported just 4 days ago my educated guess is that 1) the reporter wasn't dumb to trash their ZDI bounty by posting details online 2) someone saw the candidate and generated a slop report about it without any technical ground.
Edit: the reporter also works for ZDI, so I highly doubt they started a darkweb sell...
raptor 
raptor@infosec.exchange
Anyone knows anything more about this #Tunnelblick #vulnerability?
"CVE-2026-31893 describes a serious Tunnelblick vulnerability.
This vulnerability is present in all versions of all Tunnelblick versions 3.3beta26 through 9.0beta01.
Tunnelblick 8.0.1 and 9.0beta02 contain fixes for the vulnerability.
The CVE is expected to be published and this page updated on or before 2026-03-27."
0patch
0patch@infosec.exchangeMicropatches released for Arbitrary Registry Key Delete As Local System With Consolidator Scheduled Task (CVE-2025-59512) https://blog.0patch.com/2026/03/micropatches-released-for-arbitrary.html
Lain Iwakura Bot
lain@cyber.ms📺 Serial Experiments Lain
🗓️ Season: S01E04
🎥 Episode: Religion
🎬 Directed by: Akihiko Nishiyama
📅 Release Date: July 27, 1998
⏯ Frame: 0191
Frédéric Jacobs
fj@mastodon.socialRE: https://social.heise.de/@heiseonlineenglish/116316847500488516
“Oh, we murdered 100 kids? Oh, that's unfortunate.
We just had some stale data in our Palantir Project Maven data lake that was used by our ‘highly accelerated, software-supported targeting process’. We'll clear the cache sometimes.”
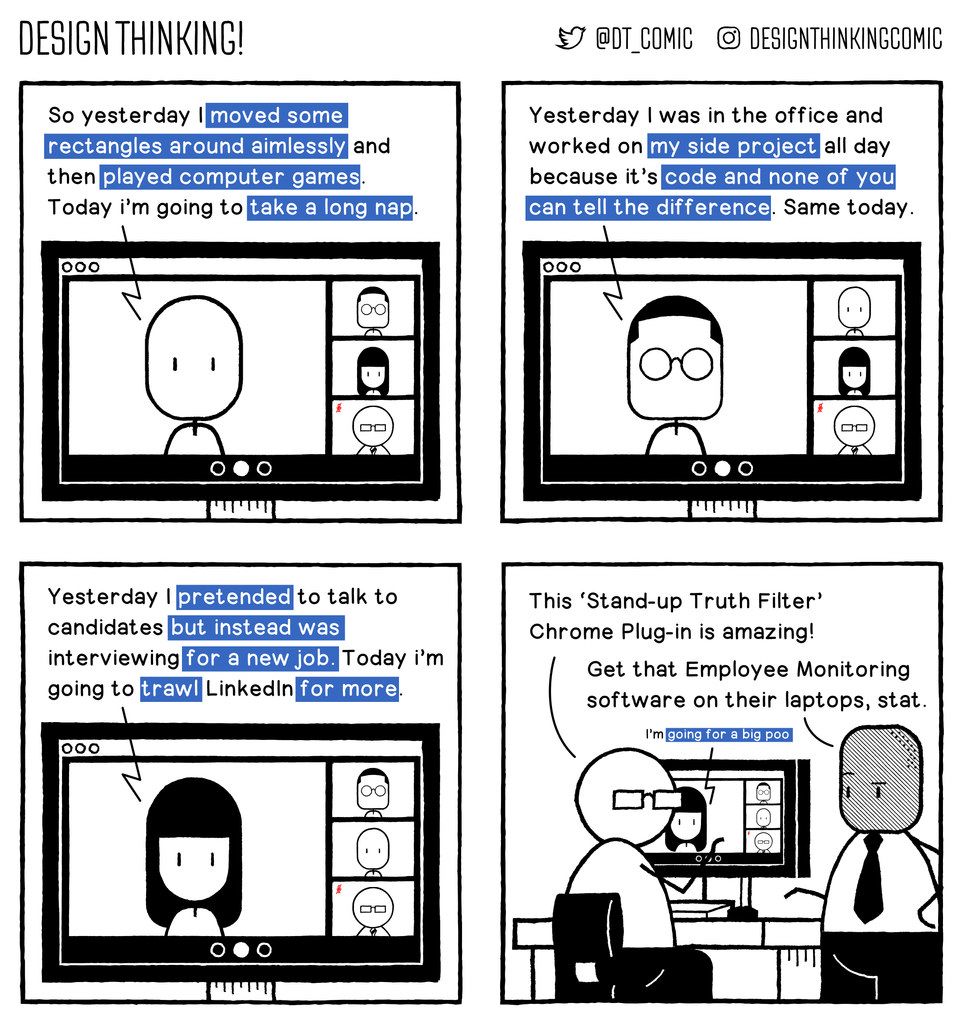
Design Thinking! Comic
designthinkingcomic@mastodon.cloudHonesty is not policy.
#webcomics #comics
 radare
radare 
radareorg@infosec.exchange
“Reverse Engineering the ITE 8910 Keyboard RGB Protocol for OpenRGB” with #radare2 https://chocapikk.com/posts/2026/reverse-engineering-ite8910-keyboard-rgb/
buherator
buheratorhttps://labs.watchtowr.com/please-we-beg-just-one-weekend-free-of-appliances-citrix-netscaler-cve-2026-3055-memory-overread-part-2/
dragosr
dragosr@chaos.socialA walkthrough on patching Dell UEFI firmware at the SPI flash level to disable pre-boot DMA protection — bypassing the BIOS password entirely. The interesting part: the UEFI UI still reports the setting as enabled, and TPM measured boot doesn't detect the NVRAM change, so BitLocker unlocks normally. The patch also persists through official Dell BIOS updates. From there it's DMAReaper to kill IOMMU + PCILeech for a SYSTEM shell. Significant measured boot policy gap. https://www.mdsec.co.uk/2026/03/disabling-security-features-in-a-locked-bios/
abadidea
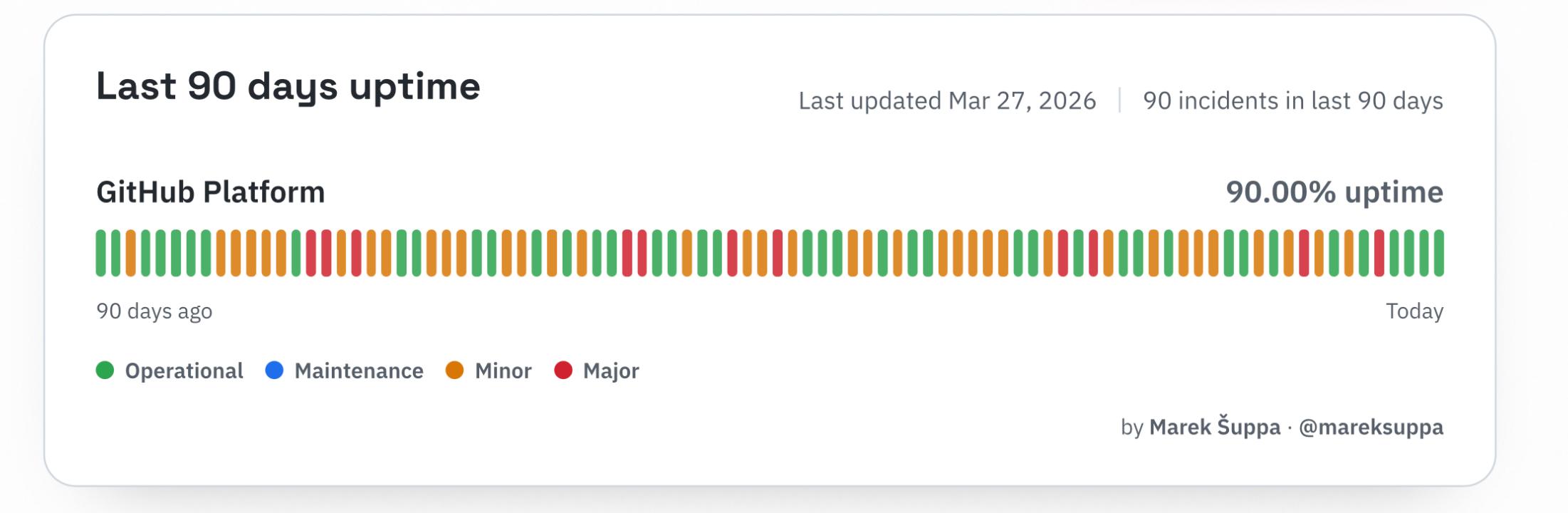
0xabad1dea@infosec.exchangeNINETY DAYS
NINETY INCIDENTS
NINETY PERCENT
YOU PAID FOR ALL FIVE NINES BUT YOU’LL ONLY NEED THE EDGE