Posts
3663Following
724Followers
1593Rebane
rebane2001@infosec.exchangein linux you can use the evil bird emoticon (:>) to destroy files, eg `:> important_document.txt`
the bird will eat the file and leave it completely empty!
linuzifer
linuzifer@23.socialFun stuff from my team mates Rene Rehme @renereh1, Nina Piontek and @kantorkel:
"Via a large enterprise's AI assistant, we obtained access to several million Entra identities and all chat logs including attachments — no prompt injection or model tricks required.”
CravateRouge
CravateRouge@infosec.exchangeDuring my previous research, I identified a "Won't Fix" DoS vulnerability affecting the latest versions of Windows, including 25H2 and Server 2025.
pauloba - DECT 7841
chmod644@mastodon.socialShall we stop calling them "social networks" and give them a more descriptive and accurate naming, like "Advertisment agregators and political view manipulative instruments".
I know, is not catchy, but at least it doesn't give the impression that you are interacting socially in a posstive and human way.
buherator
buheratorRE: https://infosec.place/objects/3c67cba4-e40f-42c2-8c4b-284816d64d00
buherator
buheratorhttps://blog.barrack.ai/qihoo-360-ssl-key-leak-wotrus-ca-fraud/
https://crt.sh/?id=24937759962
https://crt.sh/?id=24937755996
Ouch...
Decoder Loop
decoderloop@infosec.exchange🦀 Looking for Rust malware samples to practice analyzing? Our Rust Malware Sample Gallery just received a major update, with 20 new families added! https://github.com/decoderloop/rust-malware-gallery
The Sample Gallery collects links to articles about malware written in Rust, organizes them by malware family, and includes a download link to a publicly available sample for every malware family. This is a resource for any malware analyst who wants to get hands-on with real Rust malware.
The last time the Sample Gallery was updated was almost 2 years ago, in January 2024. Since then, there's been an explosive growth in new Rust malware, including all of the following families that are now in the Sample Gallery:
SPICA, KrustyLoader, RustDoor, SSLoad, Fickle Stealer, Cicada3301 Ransomware, RustyClaw, Embargo Ransomware, RustyAttr, Akira Ransomware (both the Akira_v2 and Megazord variants), Banshee (Rust variant), RALord Ransomware, RustoBot, Tetra Loader, EDDIESTEALER, Myth Stealer, Rustonotto, RustyPages, ChaosBot
This is nearly one new Rust malware family observed in the wild, every month. Rust as a programming language for malware is here to stay!
#rust #rustlang #malware #infosec #ReverseEngineering #MalwareAnalysis #reversing
buherator
buheratorSmartScreen windows got increasingly hard to unblock over time "and for a while, it was good". Then I went to a client where the sysadmin unblocked the freshly downloaded executable from the properties window so fast I had to ask him to show me once more what he just did because I couldn't follow.
Life finds a way.
@decryption @jpm @da_667 @sassdawe @Viss
buherator
buheratorhttps://labs.taszk.io/blog/post/114_mi_heap_bof/
https://labs.taszk.io/blog/post/113_mi_rng_predict/
https://labs.taszk.io/blog/post/112_mi_hshake_bypass/
It seems there is some exceptionally dump vendor policy in the works so #NoCVE
buherator
buheratorIn essence users are expected to make critical decisions about a system that is hidden from them in every other aspect of working with computers.
@sassdawe @da_667 @jpm @decryption
Joe Grand
joegrand@chaos.socialTom Lyon ✅
aka_pugs@mastodon.socialFresh scan: "The UNIX System - a Sun Microsystems Technical Report" (1985)
https://drive.google.com/file/d/1dW6l6cFAiqTKj3bmTulynKQuOHeHMx0u/view?usp=sharing
Nspace
nspace@infosec.exchangeI reported a bug in RenderDoc and it got fixed within 45 minutes (!!!) 
Alex
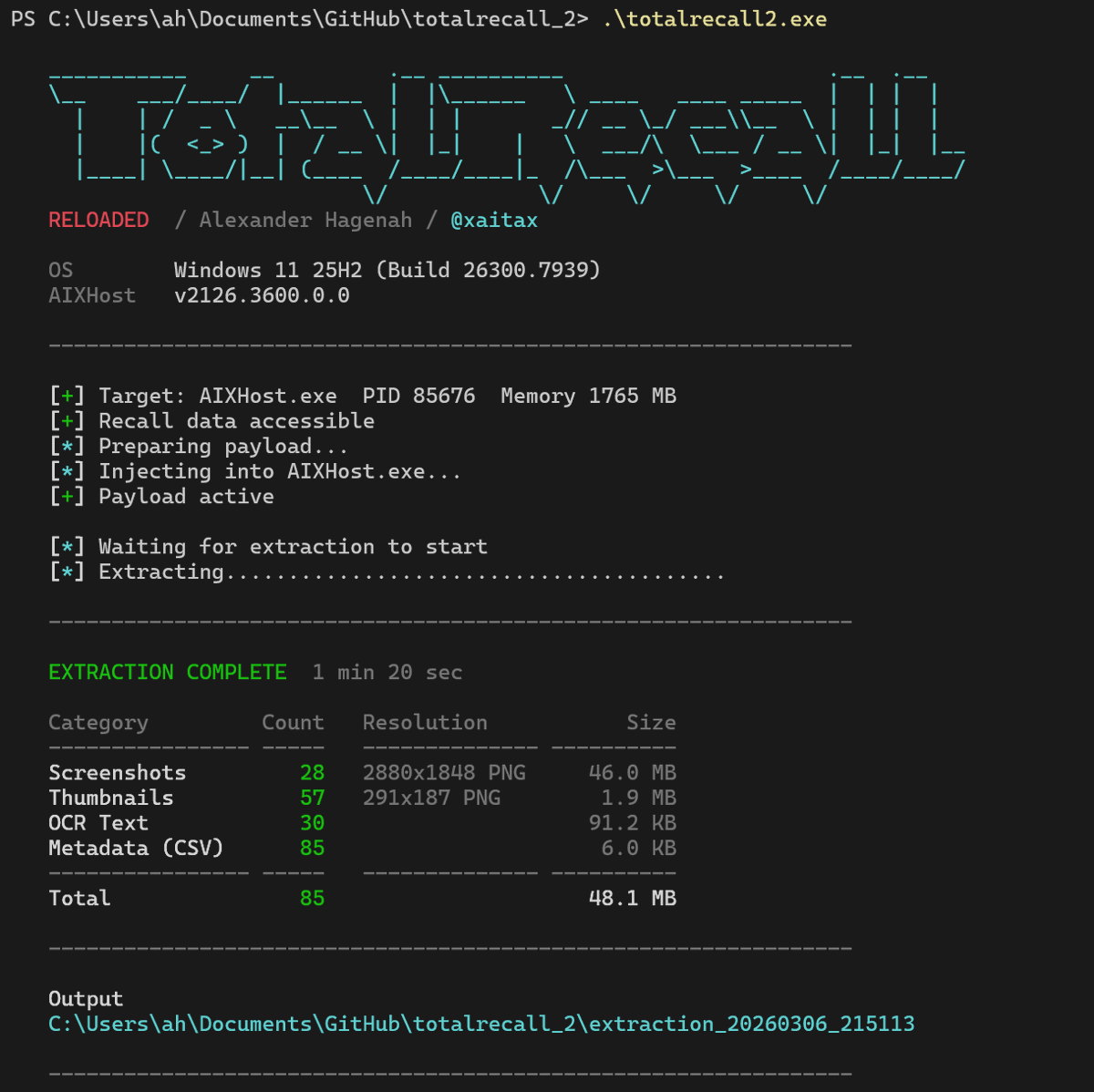
xaitax@bird.makeupTotalRecall - Reloaded.
Invested some time again into Windows Recall. Microsoft redesigned the entire architecture with VBS enclaves after the original TotalRecall. Took a closer look at the new defenses. This time going through MSRC.
Alex Matrosov
matrosov@bird.makeupThe dream of a fast and reliable binary analysis framework is now a reality.
Today, we’re open sourcing http://VulHunt.RE 🎉
code: https://github.com/vulhunt-re/vulhunt
docs: https://vulhunt.re/docs
A huge kudos to the entire REsearch team!
https://bird.makeup/users/matrosov/statuses/2025997688437874893