Posts
3664Following
724Followers
1593jcoglan
jcoglan@mastodon.socialgot a fun reply yesterday that was like "yeah I can't believe people are taking such a lax approach to verifying the behaviour of software especially if they use LLMs. we never would have done this when I worked at <well known arms manufacturer>"
buherator
buheratorSource:
https://superuser.com/questions/462443/what-are-reasons-for-local-windows-named-pipes-to-fail
buherator
buheratorbuherator
buherator* You have to let Zed proxy through the Windows firewall (I just disabled it as usual, since this is a lab network)
* The default cmd.exe shell doesn't seem to work with remote tasks (I suspect character escaping error), you have to explicitly set powershell.exe
I was initially concerned about usual Windows SSH shenanigans, but surprisingly my config (with jumphost and an agent) worked flawlessly from Linux.
h/t @raptor for the tip!
Frida
fridadotre@fosstodon.orgFrida 17.8.0 dropped with frida-strace syscall tracing on Android & iOS, no jailbreak required 🙌 https://github.com/frida/frida/releases/tag/17.8.2
Jeff Atwood
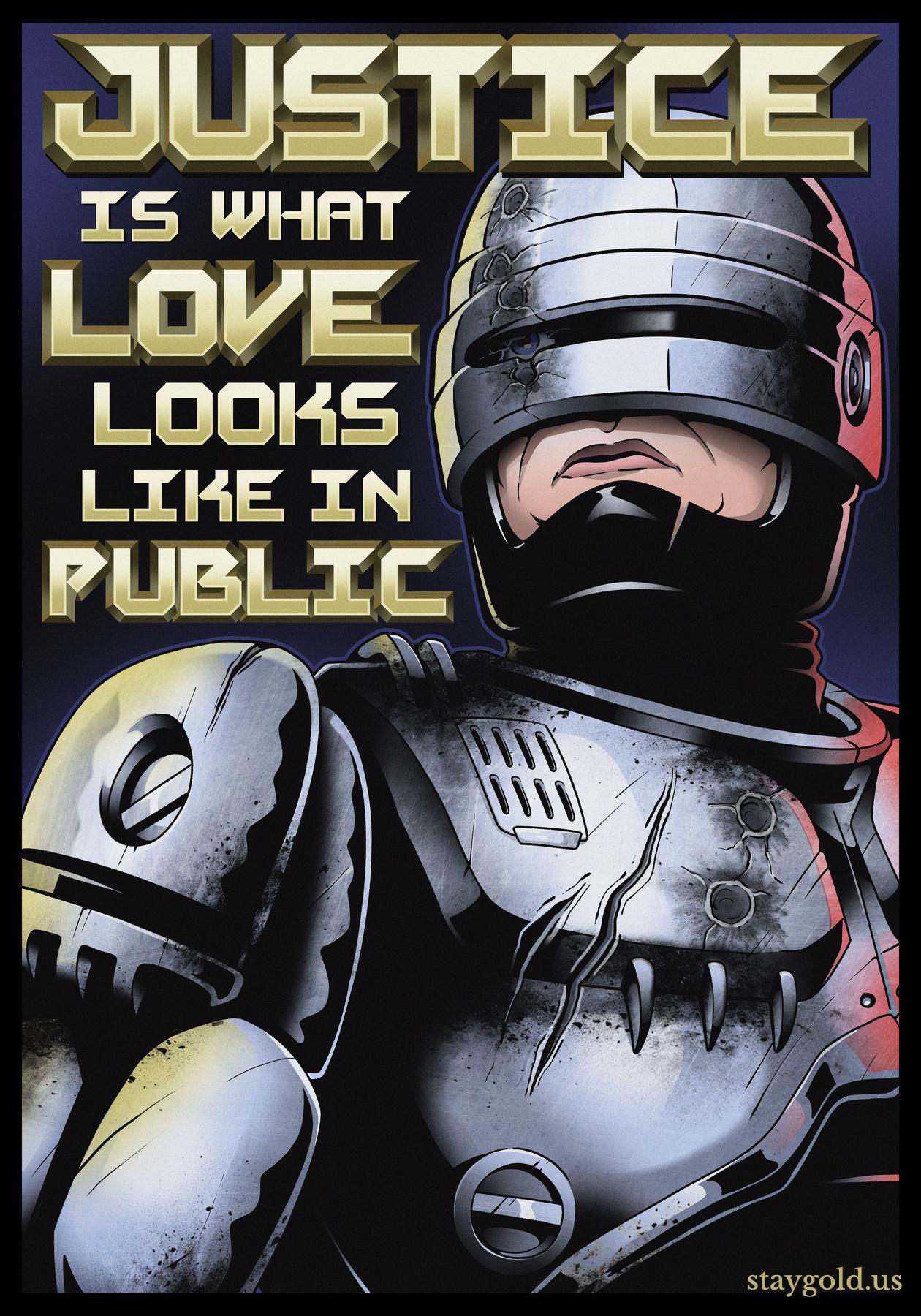
codinghorror@infosec.exchange"Justice is what love looks like in public." Via Natalie Foster and Cornel West, commissioned by me through Clay Graham Art https://www.claygrahamart.com/products/robo-justice-battle-damage-variant-matte-poster
Blue DeviL // SCT
bluedevil@infosec.exchangeA very detailed tutorial from "Joaquin Pinillos"
Walk x86-64 page tables by hand in qemu and gdb. Decompose a virtual address, follow cr3 through all levels of physical memory, and extract a flag from raw bytes.
buherator
buheratorbuherator
buheratorbuherator
buheratorhttps://eurazsiaijegyzetek.substack.com/p/battlefield-budapest-an-unprecedented
Juanma Fernandez
XC3LL@mastodon.socialRegPwn was a Windows 0-day that we were using for LPE in our Red Team for a year (discovered by Filip D. In January 2025). Unfortunately it got fixed 🥲
Good bye RegPwn 🫡
Attack and Defense
attackanddefense@infosec.exchangeAn update to our bug bounty policy: https://attackanddefense.dev/2026/03/13/bug-bounty-program-updates-2026.html
/r/netsec
_r_netsec@infosec.exchangeRegPwn - Windows LPE vulnerability (now fixed) https://www.mdsec.co.uk/2026/03/rip-regpwn/
buherator
buheratorThere is an ongoing case in front of the #EU Curia to test #copyright laws vs LLMs:
https://infocuria.curia.europa.eu/tabs/document?source=document&text=&docid=301042&pageIndex=0&doclang=en&mode=doc&dir=&occ=first&cid=489283
This would be pretty boring, BUT the case is based on a story of this guy who became a singer celebrity in the '90s in #Hungary, then a few years ago he gave an interview sky-high on cocaine talking about the awesome dolphins in lake Balaton:
https://www.youtube.com/watch?v=kxkiM635LMk
(there are no dolphins in Balaton)
Being the self-promotion genius he is, he actually kept on promoting the deployment of dolphins to Balaton, and (copyrighted) reports of this activity are now part of the court case! Naturally, he also wrote a song about the topic:
https://www.youtube.com/watch?v=mUJXhAjZQ7A
#Kozsó
buherator
buheratorhttps://geohot.github.io/blog/jekyll/update/2026/02/19/ai-art.html
(See also: photography vs painting)