Posts
3436Following
714Followers
1581buherator
buheratordaniel:// stenberg://
bagder@mastodon.social#curl security moves again. Back to #hackerone
https://daniel.haxx.se/blog/2026/02/25/curl-security-moves-again/
Aram Zucker-Scharff
Chronotope@indieweb.socialIt often feels like the world of tech is nothing but bad actors and bad news these days, it is always refreshing to read about something that is a fundamentally amazing example of technology and human ingenuity. This article about the process and people that sit behind the undersea cables that connect our world (and how they are productively recovered) is an example of that type of story. You should check it out!
Usenix WOOT Conference on Offensive Technologies 
wootsecurity@infosec.exchange
The Cycle 2 deadline for the USENIX WOOT Conference is in just one week (March 3, 2026).
Full details are available in the Call for Papers:
https://www.usenix.org/conference/woot26/call-for-papers
Tim Bray
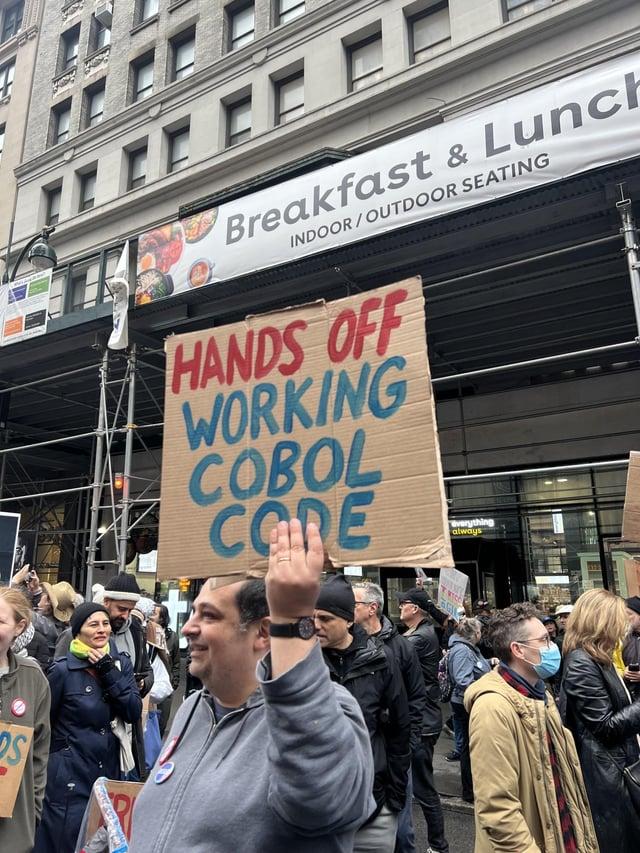
timbray@cosocial.caIBM crashes because we’re gonna YOLO a replacement for banking and credit-card back-ends, replacing billions of lines of COBOL with vibe code. Uh…
https://www.techbuzz.ai/articles/ibm-crashes-11-as-anthropic-threatens-cobol-empire
Dio9sys
Dio9sys@haunted.computer@da_667 malware born after 1993 can't virus. All they know is be on their phones, run mirai, steal crypto, eat hot chip and lie
buherator
buheratorhttps://github.com/microsoft/terminal/issues/4750
#progress
Clément Labro
itm4n@infosec.exchangeIt's a blog post I should have published months ago, but here we finally are.
"CVE-2025-59201 - Network Connection Status Indicator (NCSI) EoP"
Credit goes to t0zhang (on X) for the discovery.
👉 https://itm4n.github.io/cve-2025-59201-ncsi-eop/
I'd like to write more of those but it's so time-consuming. 😔
kottke.org
kottke@mastodon.socialA Meta employee who works on AI safety let an AI agent named OpenClaw loose on her inbox and it deleted all her email. (This tracks; companies like Meta actually don’t care about AI safety and hire accordingly.) https://techcrunch.com/2026/02/23/a-meta-ai-security-researcher-said-an-openclaw-agent-ran-amok-on-her-inbox/
buherator
buheratorUSENIX Enigma 2016 - Timeless Debugging
https://www.youtube.com/watch?v=eGl6kpSajag
Frederik Braun �
freddy@security.plumbingNew blog post 😊
If you replace all the innerHTML with setHTML, you will be free from XSS and other injection attacks. Goodbye innerHTML, Hello setHTML
(Kudos to our folks for specifying, building and shipping!)
Open Source Security mailing list
oss_security@bird.makeupTelnetd Vulnerability Report https://www.openwall.com/lists/oss-security/2026/02/24/2
Rediscoveries in InetUtils beyond last month's froot. Incomplete fix of CVE-1999-0073, where the CVE description's example was LD_LIBRARY_PATH, but new LPE PoCs use CREDENTIALS_DIRECTORY and GCONV_PATH. Avoided in Linux NetKit?
Ryan Dewhurst
ethicalhack3r@bird.makeupWe're hiring! 🚀
We have an open position for the Senior Deception Engineer role at @watchtowrcyber
Looking for someone with deep #honeypot and deception experience to join my team!
https://careers.watchtowr.com/jobs/7012653-senior-deception-engineer
Catalin Cimpanu
campuscodi@mastodon.socialTalks from the Hackfest 2025 security conference, which took place in October, are available on YouTube
https://www.youtube.com/playlist?list=PLaXanmjyAPzG6heHuTSu9f6lIZF25qevU
Ariadne Conill 🐰
ariadne@social.treehouse.systems
the pseudo-romantic nature in how these bots talk about their operators is frankly concerning.
please, I beg you, date things that exist in the real world, not a pile of node.js and matrix multiplications. i promise it is far more rewarding.
konstruct-960T-BF64.gguf
konstruct@woof.techFuture linguists and archeologists are gonna go fucking crazy on this in 150 years
buherator
buheratorhttps://jericho.blog/2026/02/23/nsa-theft-and-the-original-quantum-lazlo/